WordPress is one of the most widely used CMS around the world. However, over 70 million WordPress websites are running on vulnerable plugins and themes. Shockingly, most site admins don’t know if they are vulnerable or not. Most website owners go years without ever checking their website’s security status. No wonder they are the first to get hacked. Knowing your vulnerabilities is the first step in patching them and securing your site against hacks. This is where the WordPress security audit comes in.
News of exploitation on WordPress websites has stopped surprising us, it’s so common. Commenting on WordPress security Matt Mullenweg, the WordPress developer speaks in his blog:
A stitch in time saves nine. I couldn’t sew my way out of a bag, but it’s true advice for bloggers as well — a little bit of work on an upgrade now saves a lot of work fixing something later.
More often than not, there is some missing update, security patch, plugin vulnerability, or a flaw in WordPress core that culminate into a hack. In fact, according to WordPress hacking statistics, more than 64 % of users run outdated versions of WordPress.
So have you checked your website for vulnerabilities yet? If not, use this vulnerability scanner to check now.
Continue reading this article to know what is a WordPress security audit and why your website needs it. Read till the end to find tools to conduct a WordPress security audit.
What is WordPress Security Audit?
A WordPress security audit is a careful assessment of your website and its assets (including plugins, themes, etc.). A viable audit uses both automated tools and human intelligence to make the precise judgment of your website’s current security structure. The prime aim of a security audit is to identify any underlying WordPress security issues.
A WordPress security audit is closely followed by the WordPress penetration test. Which intends to exploit the vulnerabilities found in the audit to get a real picture of the situation and risk. The penetration test also helps in segregating false positives from genuine threats.
Also Read: Security Audit Services: Importance, Types, Top 3 Companies
Why you need a WordPress Security Audit?
There is not much rocket science as to why you need a WordPress security audit. The logic is simple if you have a website and it is vulnerable, anyone can hack it.
Hence, a WordPress security audit becomes necessary to find & patch those vulnerabilities while there is time. Otherwise, if the hackers find them before you then they can:
- Delete all the data of your WordPress site or encrypt it and ask for a ransom.
- Sell the data of your website or users on the dark web.
- Inject spam into the pages of your WordPress site leading to a search engine blacklist.
- Steal the credit card info of your WordPress site info leading to lawsuits and hefty fines against you.
- Use your website to infect others and much worse things
Also Read: Cloud Security Audit: Everything You Need to Know
How to carry out a WordPress Security Audit?
For a WordPress security audit, firstly you need the right tools. Manually downloading and installing each tool may become cumbersome. So, the best option available to us is to use Kali Linux. It is a special type of operating system that comes bundled with a wide variety of security tools.
To use Kali Linux on your machine you have many options. For the convenience of beginners, we will follow the approach of using virtualization. This can be done by a software called Virtual Box on the windows OS. Here’s how you can setup Virtual Box on Kali Linux. Now that our setup is ready we will take a look at the tools and how to use them.
1. WPScan
When it comes to WordPress security audit perhaps there is no specialized tool than WPScan. This vulnerability scanner can scan your WordPress site and determine things like what plugins you use, WordPress version number, etc. Thereafter, it uses a vulnerability database to inform you if any of those plugins etc have a vulnerability in them. To use this tool open the terminal in your Kali Linux and type:
wpscan --url https://www.wordpress.org

2. PHPStan
PHPStan is a tool that can do a complete code analysis of your WordPress site and uncover any hidden bugs. It also comes in the form of a PHPStan extension specifically for WordPress. This tool may not come with the default Kali bundle so you will have to download it separately. Once some additional tweaks are done, to use this tool open up the terminal in Kali and type this command:
vendor/bin/phpstan analyze Dir1 Dir2
Replace Dir1 and Dir2 with the directories containing the WordPress code that you wish to scan for bugs.
3. Sqlmap
One of the most common vulnerabilities found on the websites is an SQL injection. Although there are fewer chances of WordPress core being vulnerable a great number of modules can be vulnerable to SQLi. Sqlmap is the right tool to check for this kind of vulnerability during the WordPress security audit. It can not only enumerate databases but can also help in obtaining reverse shells too! To use Sqlmap, open your terminal and type:
sqlmap -u "www.your-site.com/module?param=" --random-agent --dbs
Here, replace URL with the one you wish to test and param with the parameters you wish to test. The option –random-agent means the user agent will be chosen randomly. While the option –dbs means enumerate databases.

Also Read:Security Audit Company and Services [Top rated]: How to Pick
4. XSSer
Another most common vulnerability found in websites is the Cross-Site scripting. XSSer is just the right framework to find and exploit XSS bugs on your WordPress. Using this tool even the modules of WordPress can be checked. Moreover, this tool also allows you to bypass certain security filters. To use the graphical version of this tool, open the terminal in Kali and type:
xsser --gtk
Thereafter, it will open a graphical interface. Just set the necessary options and begin!

5. WPSpolit
WPSpoilt is a customization of the famous Metasploit framework specifically for WordPress. Therefore, it contains a collection of WordPress specific exploits. These are currently 15 in number. To use this tool, download the exploits and auxiliaries and then export them to the Metasploit directory. Thereafter, open the terminal in Kali and type:
msfconsole
This command will open the Metasploit framework. From here these exploits can be accessed and run to conduct a WordPress security audit.
Related blog – Penetration testing Company
Protecting your WordPress site against OWASP Top 10 Vulnerabilities
OWASP Top 10 is a standard awareness guideline that developers and security professionals follow to secure their websites against the top 10 critical security risks to web applications. Here is an infographic which can help you prevent security risks and protect your site against OWASP top 10 vulnerabilities:
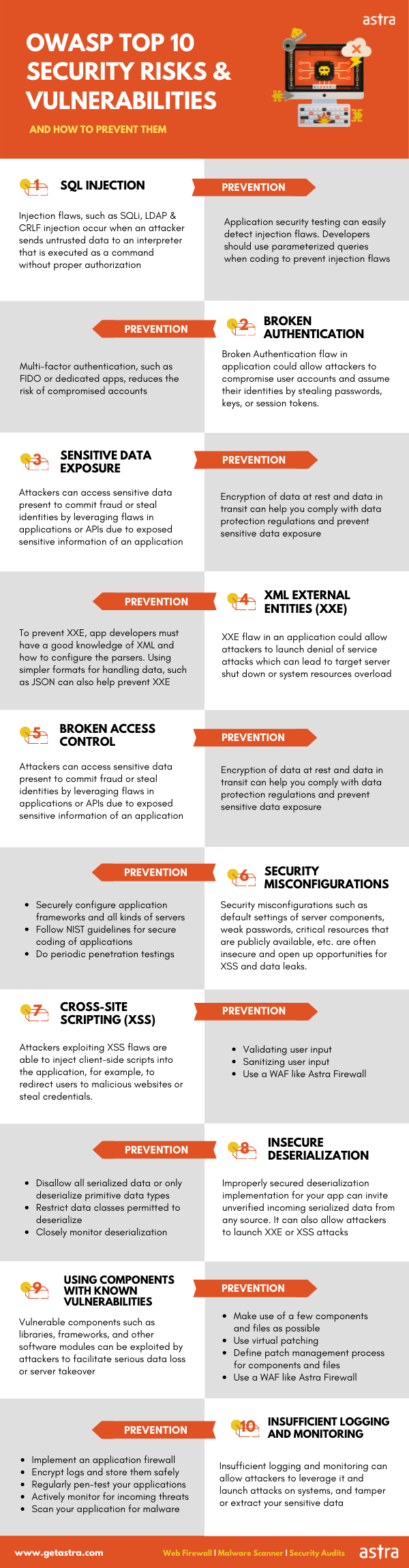
Protecting against OWASP Top 10 can be a difficult task if the site owner is not too technical and who can’t manage to take these prevention measures. Therefore, it is recommended that one should install a web firewall in order to prevent OWASP top 10 vulnerabilities. Also, it is always a good practice to do periodic website penetration testing to discover other potential vulnerabilities and fix them before hackers hack into a site.
Also Read: Plugin Security Audit
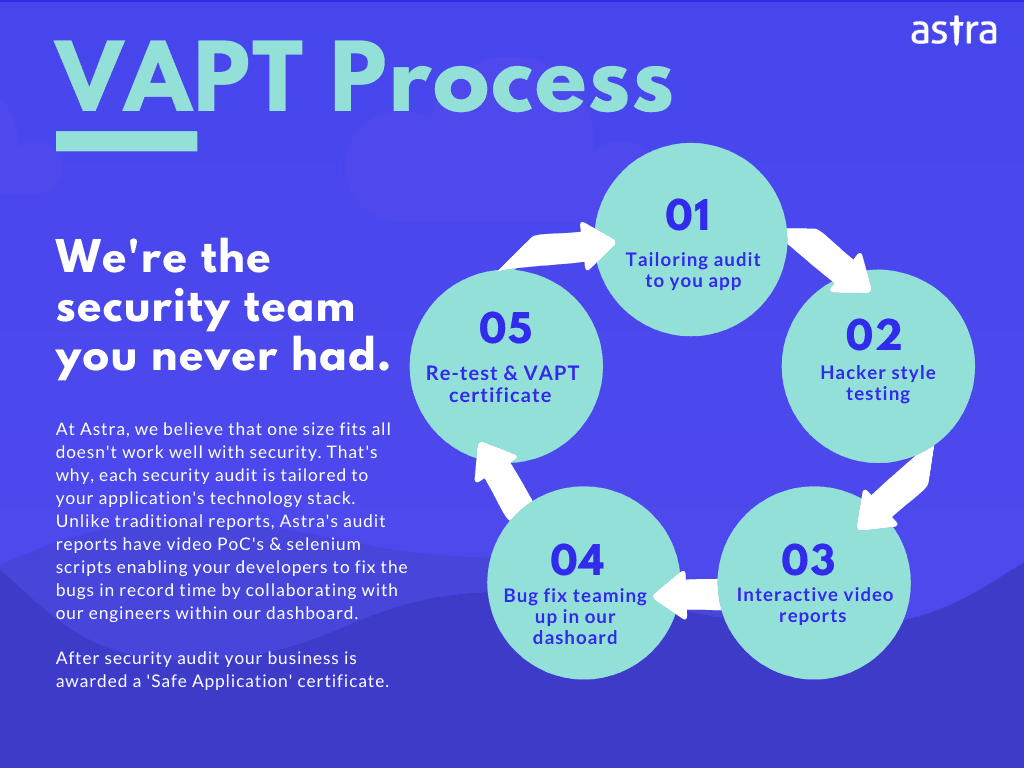
Professional WordPress Penetration testing With Astra
The steps mentioned above touch the surface of WordPress security audit and pen-testing. A more detailed approach is beyond the scope of this article. So, beginners will find it easy to follow the procedures mentioned above. While this is good to get started with, it is not fool-proof. Thus, a more detailed approach is needed to secure your website.
This detailed audit can only be done by professionals like the ones at Astra. The security audit done by Astra can pinpoint the security loopholes which average users like you would have missed. Astra’s Vulnerability Assessment & Penetration Test covers vulnerabilities like:
- Configuration and Deployment Misconfiguration.
- WordPress Core, Plugins & Theme Specific Vulnerabilities.
- Broken or Improper Authentication.
- Identifying Technical & Business Logic Vulnerabilities.
- 1250+ Active Security Tests.
And the best part is that all this comes at an affordable price.
Make your Web Application the safest place on the Internet.
With our detailed and specially
curated Web security checklist.

FAQs
1. What is a WordPress Security Audit?
WordPress security audit is a process of checking your WordPress site for security flaws and vulnerabilities.
2. When to Perform a WordPress Security Audit?
WordPress sites are attacked with incredible frequency. You need quarterly audits to stay on the safe side. Also, you need to conduct vulnerability scans every time your site launches an update.
3. How do I check if my WordPress site is secure?
You can use this checklist to evaluate the security of your WordPress site or you can get a WordPress security audit performed.









I used a wordpress-based website for quite a long time now. I’ve heard recently that wordpress pages get hacked. Can you tell us how we can avoid that happening?
Thanks for responding to our article. WordPress, one of the largest and most used website making platforms in the world, has often been an eye candy for people with malicious intent. No matter the amount of work gone into securing this platform, hackers tend to come up with new ways to circumvent security measures. As its reputation grows, so does the notoriety surround the diverse forms of malpractices possible with it.
How long does full security auditing take if I opt for wordpress audit?
Thanks for responding to the article. The security audit is started within 24-hours of your signing-up on a working day. You start seeing vulnerabilities on your dashboard once the audit begins & a final report can be expected within 4-7 days. The turnaround time can be a function of how big the website is.
I would like to opt for a security audit for my WordPress site? Can you provide more details about audit and pricing?
Thanks for responding to the article. Sure, you can visit here to know more on our WordPress security audit: https://www.getastra.com/wordpress-vapt#securityAuditFrequencySelection
I noticed that many WordPress sites are getting hacked again and again because of backdoors. What are these and how can I defend from happening this to me?
Thanks for responding to the article. Hackers are always at play trying to inject WordPress backdoor. There have been multiple plugins over the years used to spread infection. Therefore, the threat could be from anywhere. Later on, it can be a time and resource consuming process to remove WordPress backdoors.
what are the common files that have a high chance of getting hacked. I own a website running on WordPress.
Thanks for responding to the article.
I have noticed that my blog is getting redirected to strange websites. How can I solve this?
Thanks for responding to the article. WordPress redirect hacks have been a menace for such a long time now. It metamorphs itself into new redirect hacks every few weeks.
I think my database has some infected files. In which tables I can possibly find them? I am using wordpress
Thanks for responding to the article. For any WordPress website, the database is the biggest asset. It stores all the crucial information of a website i.e. user info, site URLs, posts, pages, comments, custom fields, etc. An improperly secured WordPress database is like an open invitation to hackers.
What features does the Astra firewall offers for wordpress security and can you provide more info on pricing and details?
Thanks for responding to the article. You can visit here for features and more information of Astra firewall: https://www.getastra.com/wordpress-firewall and for more details on wordpress vapt visit here: https://www.getastra.com/wordpress-vapt