How can you secure your Magento Store
Today all websites face serious risks. But, it is the e-commerce industry that faces the most risks online. And, as it turns out, Magento is the leader of the e-commerce space, thus a coveted target.
However, you can reduce these risks systematically by following a set of Magento security best practices. In this comprehensive and extensive guide, I have listed primitive actionable measures to strengthen Magento.
If you read this guide throughout and followed it with utmost priority, you can be sure of your website’s reduced susceptibilities.
Go through the below URLs if you are looking for –
The Magento CMS, currently, powers 25% of all e-commerce websites all over the world. Clearly, it is one of the most admired CMSes for eCommerce. To add to that, it also stores a sea of personal & financial data, which makes it even more lustrous in the eyes of hackers. The following hacking statistics on Magento backs this.
Magento Hacking Statistics
- Magento powers 1.2% of the internet.
- And, 12% of all eCommerce sites.
- In pure numbers, 250,00 active sites use Magento.
- However, only 11,000 of those sites run on Magento 2, which is around 44% of all Magento websites.
Magento is also, the most hacked CMS after WordPress. The CVE details of Magento CMS show that XSS is the biggest threat to Magento. Other threats to Magento include Code Execution, SQL Injection, Directory Traversal, Magento store redirecting, CSRF, etc. The following graph makes it better to understand.
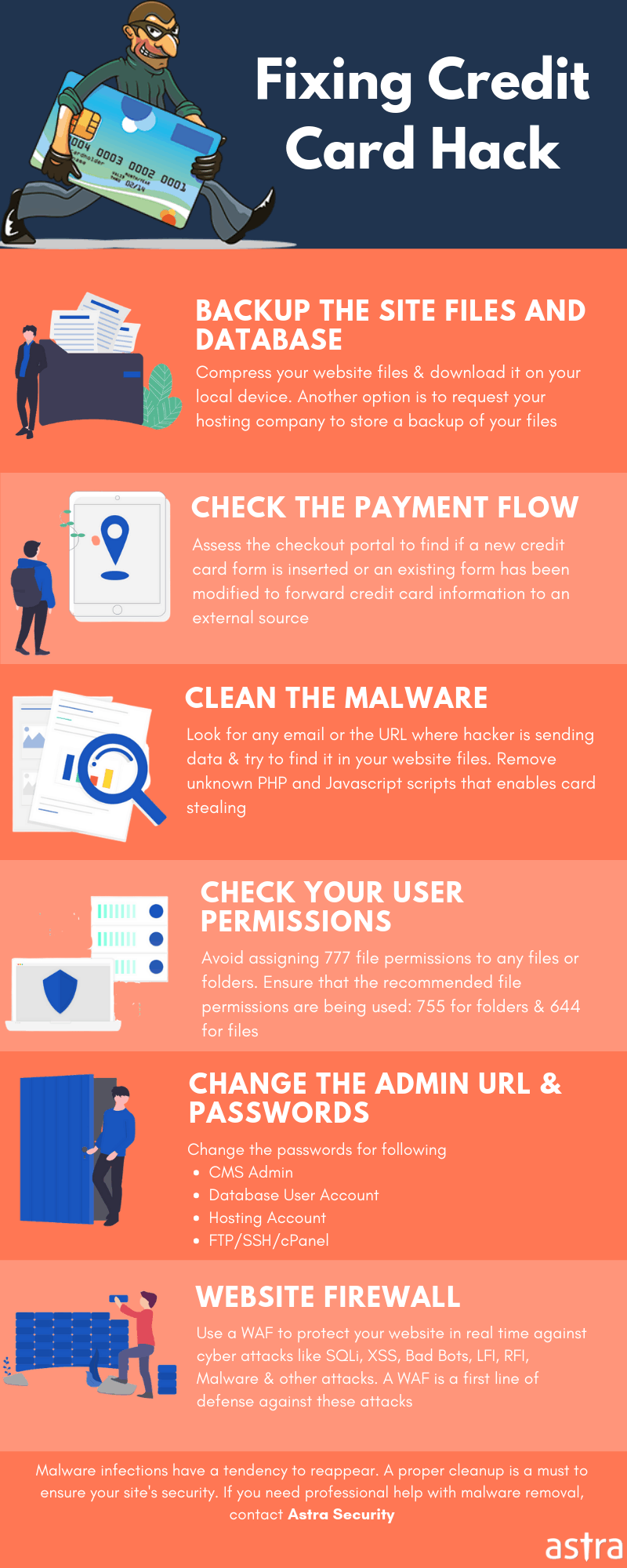
Moreover, Magento card skimming and Credit card hacks are some examples of how data compromisation on Magento take place. Further, the Magecart attacks make for the most persistent attack on Magento as of now. As a result of these attacks, customers encounter identity theft, data theft, fake transactions, and so on. Here are more extensive data on hacking for your reading.
Top 16 Steps To Securing Magento 1 & Magento 2 Stores
Securing & maintaining your website is crucial in this era of increased cybercrimes, more so when it is e-commerce. The aftereffects of an attack on Magento or any e-commerce for that matter reverberates to a larger number of people. In cases like these, it is the common people and their data that are at stake. Bill Gates, aptly conveys the apprehension for e-commerce websites as,
Oh, I think there are a lot of people who would be buying and selling online today that go up there and they get the information, but then when it comes time to type in their credit card they think twice because they’re not sure about how that might get out and what that might mean for them.
It all comes down to one thing – securing your website for people to feel confident enough to swipe their cards right in and not being faced with consequences. As for the owners of websites, there are cold & harsh penalties for condoning Magento security.
However, you can avoid being at the face of the storm just by following the below security measures depicted in this guide. Honestly, if you implemented these measures carefully, you will reduce the risks by the maximum.
Get the ultimate Magento Security checklist with 300+ test parameters
Related Guide – Ecommerce Security
1. PCI-DSS (Payment Card Industry – Data Security Standard)
Since e-commerce websites deal in sensitive payment data of customers, it requires vigilant monitoring. Therefore, the PCI (Payment Card Industry), an association of top credit card companies, invigilates Magento store security of these sites.
As a web business owner, it is of utmost importance that customers get a guaranteed safe checkout. Hence, the PCI-DSS requires all Magento websites to use standard & secure credit card handling. In case of non-compliance, hefty fines and severe penalties can be charged.
What PCI compliance include?
The security requirements under the PCI compliance include policies and procedures, software design, and network architecture. In laymen’s language
- Build and Maintain a Secure Network and Systems
Requirement 1: Install and maintain a firewall configuration to protect cardholder data
Requirement 2: Do not use vendor-supplied defaults for system passwords and other security parameters - Protect Cardholder Data
Requirement 3: Protect stored cardholder data
Requirement 4: Encrypt transmission of cardholder data across open, public networks - Maintain a Vulnerability Management Program
Requirement 5: Protect all systems against malware and regularly update antivirus software or programs
Requirement 6: Develop and maintain secure systems and applications - Implement Strong Access Control Measures
Requirement 7: Restrict access to cardholder data by business need to know
Requirement 8: Identify and authenticate access to system components
Requirement 9: Restrict physical access to cardholder data - Regularly Monitor and Test Networks
Requirement 10: Track and monitor all access to network resources and cardholder data
Requirement 11: Regularly test security systems and processes - Maintain an Information Security Policy
Requirement 12: Maintain a policy that addresses information security for all personnel
Not adhering to the set guidelines by PCI-SSC can open doors for credit card hacks in your store.
2. Change Admin Username for Magento Store
After you have ensured the PCI compliance of your site, change the default admin username. Always refrain from using the obvious as your username. For instance, the word ‘admin’, your own name, your website’s name are too easy a guess for a hacker and thus dangerous. A newly installed Magento website has the project owner’s email as the username. Change the default hard code email address of the project owner as follows:
- Log into your Magento admin panel
- Go to system >> My account
- Type in the new and unique username in the ‘Username’ field’.
- Click “Save Account.”
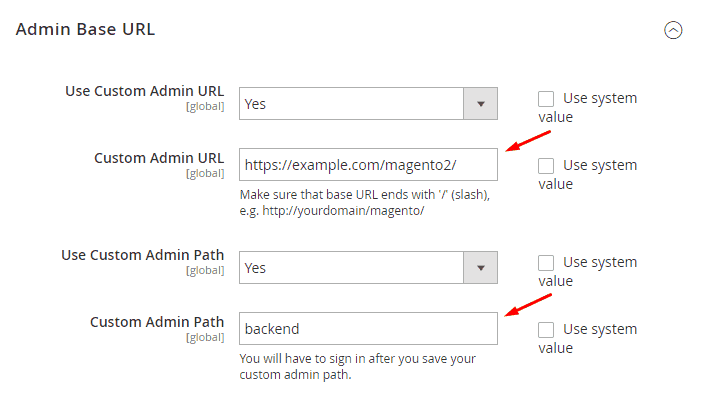
3. Change Admin URL in Magento
Almost all websites have /admin as the default URL for their admin pages. Not changing this default admin URL in Magento makes for a serious vulnerability. On the other hand, changing the default URL would hide your website’s admin page thus improve Magento security. Further, we recommend you choose a value other than `admin` or `backend` or another term that isn’t easy to guess.
You can change the default admin URL by following a few steps as below:
- On the Admin Panel, select System > Configuration.
- Select Admin in the left-most column.
- Navigate to the Admin Base URL section, and do the following:
a) Set Use Custom Admin URL to “Yes.” Then, enter the Custom Admin URL in a format like this:
http://yourdomain.com/magento/
b) Set Custom Admin Path to “Yes.” Then, enter the name of the Custom Admin Path. Choose something that is not easily guessable by attackers. - At last, hit the Save Config button, and log in with the newly created URL.
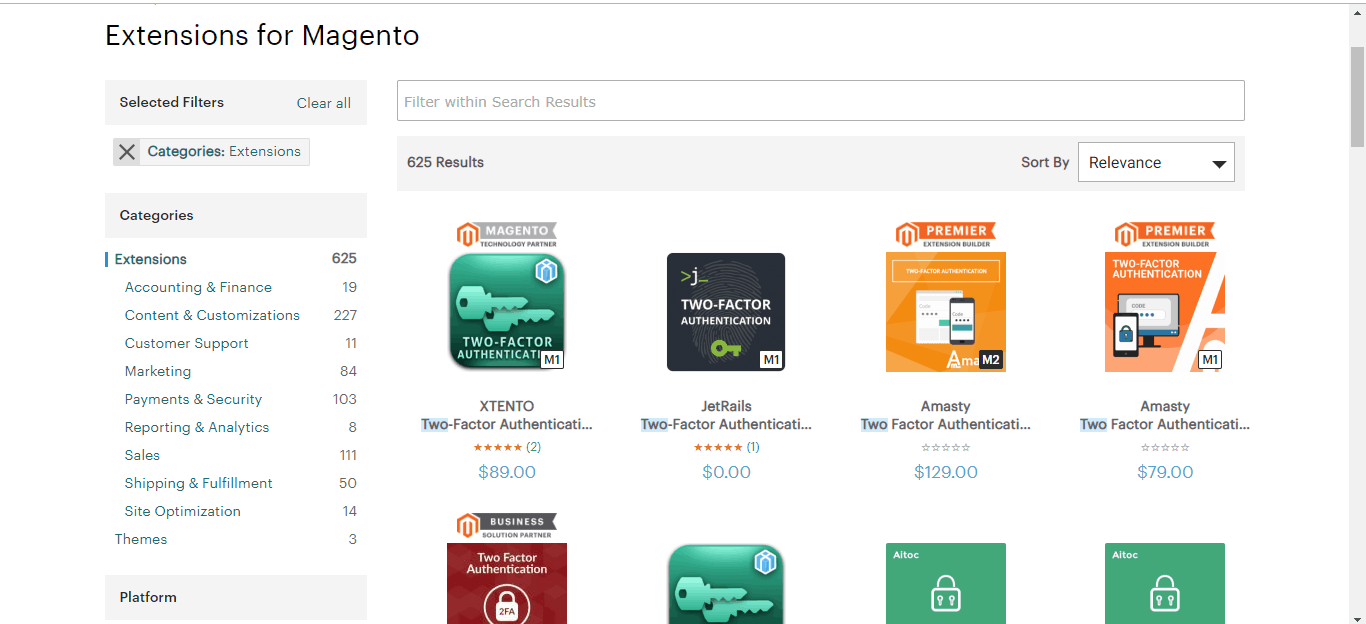
4. Use Two-Step Verification for Magento Login
The two-step verification considerably reduces the security risks related to your Magento passwords. Even if a hacker has access to stolen credentials, he just can’t log into your admin panel due to an added security. Additionally, two-factor authentication also checks brute-forcing. You can install TFA for your login page too for authentic access to user accounts.
There are loads of extensions that provide the utility of two-step verification, choose the best based on the ratings.
5. Use IP Whitelisting and .htaccess in Magento
Next up is the IP whitelisting and .htaccess. Whitelisting only select IPs to reach Magento’s admin panel is a smart way you can secure your site. Thus, use IP whitelisting and .htaccess password protection to block access to any development, staging, or testing systems. Since these are highly sensitive systems and any compromisation to these would lead to an ugly data leak or brutal attack.
Here is how you can modify your .htaccess file to protect certain URLs from lurking attackers
For a single-store view Magento installation
#####Secure adminRewriteCond %{REQUEST_URI} ^/(index.php/)?admin/ [NC,OR]RewriteCond %{REQUEST_URI} ^/downloader/ [NC]RewriteCond %{REMOTE_ADDR} !^my.ip.add.ressRewriteRule ^(.*)$ http://%{HTTP_HOST}/ [R=302,L]
For a Store View in a Subdirectory
If you have Magneto installed in a sub-directory or a store view as a virtual sub-directory of the main domain name,
Eg. https://www.getastra.com/features/
Eg. https://www.getastra.com/en/
Eg. https://www.getastra.fr/
#####Secure adminRewriteCond %{REQUEST_URI} ^/(downloader shop/ en fr/)?(index.php/)?admin/ [NC,OR]RewriteCond %{REQUEST_URI} ^/downloader/ [NC]RewriteCond %{REMOTE_ADDR} !^my.ip.add.ressRewriteRule ^(.*)$ http://%{HTTP_HOST}/ [R=302,L]
Another easy way to whitelist IP addresses is to use an extension like GeoIP Ultimate Lock that grants store access to specific IP addresses. With this extension, you can easily block traffic from unwanted countries, regions & IP addresses. Moreover, you can also block access to the entire store, specific products & web pages.
6. Use Strong Passwords
If you are still using a password that is easy to guess kindly reconsider. Using a strong password helps you to:
- Keep your personal information safe
- Protect your emails, files, and other content
- Prevent someone from breaking into your account
A strong password stands in a crisis like a brute-force attack. Now, what qualifies as a strong password and what doesn’t? Combination of letters, numbers & symbols as passwords makes for a strong password. Since, passwords are case sensitive, using both uppercase and lowercase letters make it even stronger. The ideal password length is between 8-14 characters. On the other hand, a weak password is that which uses easy to guess words, phrases & combinations. For example, password, 12345678, 9874561, etc. categorizes as weak passwords.
You can create passwords either on your own or use an online password generator for the purpose. If you are planning on creating passwords yourself, we suggest you take a look at this guide on – “How to create safe and secure passwords.”
Here is an example of how you can convert a simple password to a strong password:
Replace letters with numbers & symbols
Example-“Spooky Halloween” becomes “sPo0kyH@ll0w3En”
7. Limit Login Attempts for Magento Admin
Another secure way to lock your admin panel from attackers is to limit the number of failed login attempts. You can also go on and limit the maximum number of password reset requests. This will protect your website from unauthenticated login attempts.
To configure your website, you can follow the below steps:
For Magento 1.x:
- Log into your admin panel.
- Navigate to System.
- Next, go to Configuration.
- Click on Advanced > Admin.
- Click to expand the Security option there. And change respective settings
For Magento 2.x:
- Log into your admin panel.
- Navigate to Stores >Settings
- Next, go to Configuration.
- Click on Advanced > Admin.
- Click to expand the Security option there. And change respective settings
Related Blog – Magento Login Protection
8. Enable Captcha in Magento Login & Forms
CAPTCHA is an abbreviation for Completely Automated Public Turing test to tell Computers and Humans Apart. It is rather self-explanatory. So, CAPTCHA is the best bet to discourage bot attacks on your Magento’s admin panel. You can enable CAPTCHA on your site by following these simple steps:
For Magento 1.x:
- Navigate to System
- Click on Configuration
- Go to Advanced>> Admin in the left-most panel
- Expand the CAPTCHA section; Select ‘Yes’ to enable CAPTCHA.
For Magento 2.x:
Navigate to Stores > Settings>Configuration > Advanced > Admin > CAPTCHA
- Navigate to Stores>>Settings
- Click on Configuration
- Go to Advanced>> Admin in the left-most panel
- Expand the CAPTCHA section; Select ‘Yes’ to enable CAPTCHA.
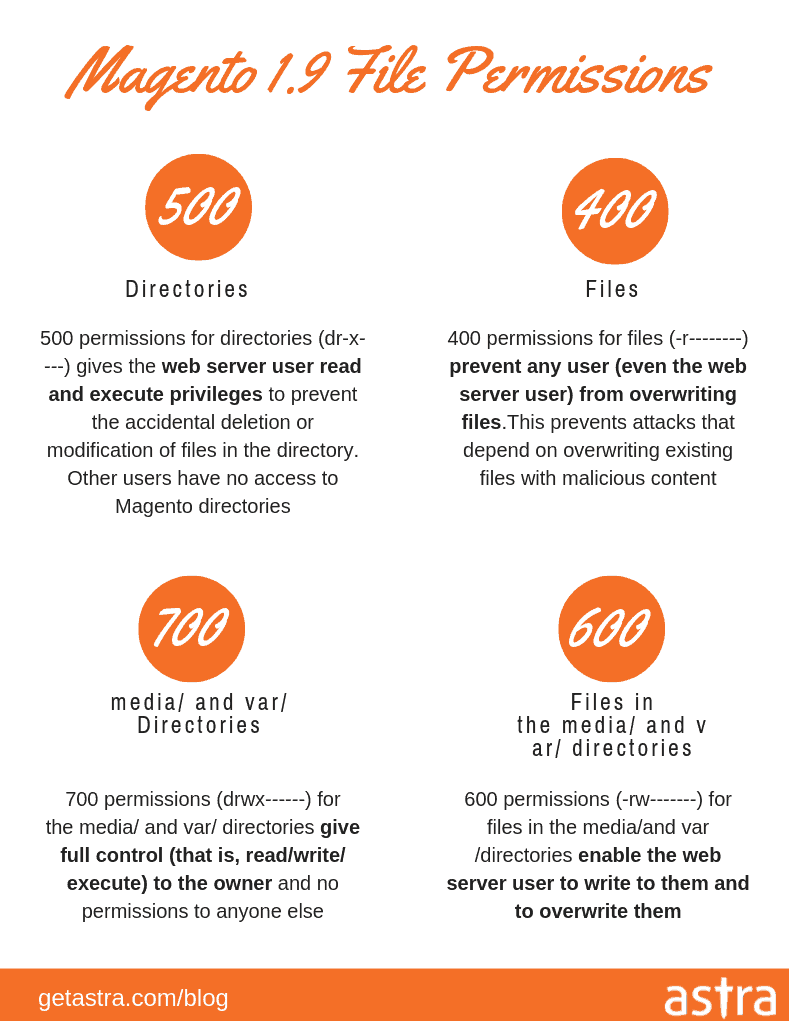
9. Set Recommended File & Directory Permissions in Magento Store
To suit Magento for your specific business needs, you may need to customize the platform. Files and folders and their respective permissions play an important part in this. However, it is also complex.
As a security person, I recommend having the permission of 755 for directories and 644 for files. That being said, there are files in your Magento website that might require different permission than what we just mentioned. Listing all those files and their correct permissions will make this guide unnecessarily lengthy, but, we do have a guide on “How to set correct Magento file permissions” that shall help.
Also read: PHP web shell
Set Folder permissions as:
- Access your website through FTP.
- Navigate to your Magento installation folder. Ex: (/path/to/your/Magento/install/)
- Right-click on the folder and select the File Permissions option
- Once you click on the option, a new window will open. Insert “700” in the Numeric value field.
- Then enable the “Recurse into subdirectories” option. In the list seen below, select the checkbox titled “Apply to directories only”.
- Hit the OK button.
- The process may take several minutes for a large number of files.
Set File permissions as:
- Access your website through FTP.
- Navigate to the where Magento is installed. Ex: (/path/to/your/Magento/install/)
- Right-click on the file and select the File Permissions option
- Once you click on the option, a new window will open. In the Numeric value field input the value “600”.
- Then enable the “Recurse into subdirectories” option. In the list seen below, select the checkbox titled “Apply to files only”.
- Hit the OK button.
- The process may take several minutes for a large number of files.
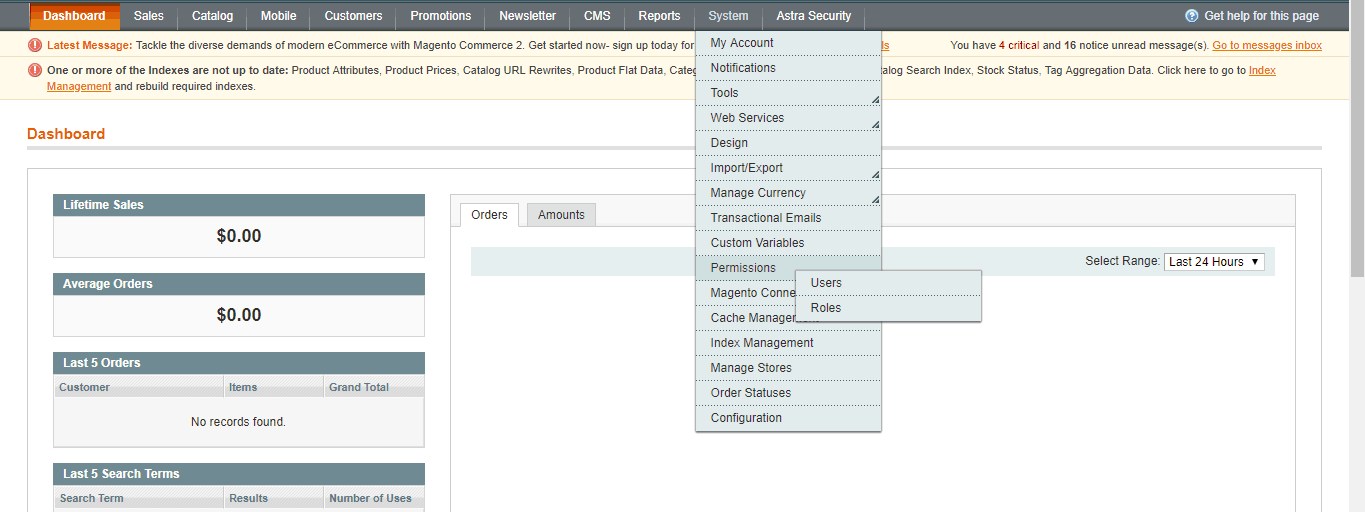
10. Set Recommended User Roles and Permissions in Magento Store
Defining correct user roles helps in segregating duties. It also enhances store security since every user does not enjoy all the permissions. There are different levels of permissions. You can assign a user a role based on their duty and your preference.
Here are the steps to set correct user permissions:
- Log into your website and navigate to ‘System’
- Click on ‘Permissions’, you will see two options ‘Users’ & ‘Roles’
- ‘Roles’ is the section where you can define roles, whereas ‘Users’ is where you assign them.
11. Backup Your Data Regularly
In the case of an unexpected attack, a backup can save your site. A good backup helps restore your hacked website in minutes. It is the best disaster management you’ve got. But, to make backups functional you need to take care of a few things, like-
- the files to include
- the frequency of the backup
- the functionality of the backup
Before you start backing up your site, understand the necessities correctly. A backup should include all the files necessary for your website’s configuration, look, and workings. A Magneto website allows you to take four kinds of backups such as:
- System Backup (includes source code+database+media),
- Database Backup (exclusively for the database),
- Database with media backup, and
- System without media Backup.
Note:
- Put your website on maintenance mode before taking a backup. The website automatically comes out of the Maintenance mode after the backup.
- Make sure that your server and database are backed up to an external location other than your server.
A system backup is the most functional backup as it includes both the source code and the database. However, you can shuffle the types according to your needs.
Coming to the frequency of the backups. Well, it can vary depending on how often you update the content of your website. You can opt for either daily, weekly, or monthly backups.
Now the methods of backup, you can opt either for a manual backup or automate the process.
The purpose of a backup is to restore your website back to its original & healthy position. Thus, always check backup rolls back to your website completely. In case of a large site, the restoration of a backup becomes too tedious & time-consuming. In such situations, it would be better to work with your hosting provider in order to deploy a professional database backup solution.
12. Update Missing Magento 2.0 Security Patches
Running websites on outdated and vulnerable versions remain the biggest cause of hacks in CMS. Always run your store on the latest version of Magento. This ensures that your installation doesn’t contain any vulnerability. Every update includes the latest security enhancements.
Check for security updates here – https://magento.com/security
If for any reason you cannot upgrade to the latest version, make sure to install all security patches as recommended by Magento. Although Magento releases security patches to fix major issues, new product releases also include additional improvements to help secure the site.
13. Install Extensions from a Trusted Source
Unupdated and vulnerable third-party extensions are again the root cause of many hacks. Make a point to install extensions only from trusted sources. You can check the statistics and reviews from Magento Marketplace and identify which extension developer has a credible profile. For example, extension developer such as FMEextenstions has a strong footprint on Magento Marketplace and offers a broad range of verified extensions.
Never use paid extensions that are published on torrent or other sites. Check for the support an extension provides. It is the second most important thing after checking if the extension is updated & maintained often. Always review the extensions for security issues before installing them.
Do not click on suspicious links, or open suspicious emails.
Do not disclose the password to your server or to the Magento Admin.
Check periodically for unauthorized Admin access.
Work with your hosting provider to review server logs for suspicious activity, and to implement an Intrusion Detection System (IDS) on your network.
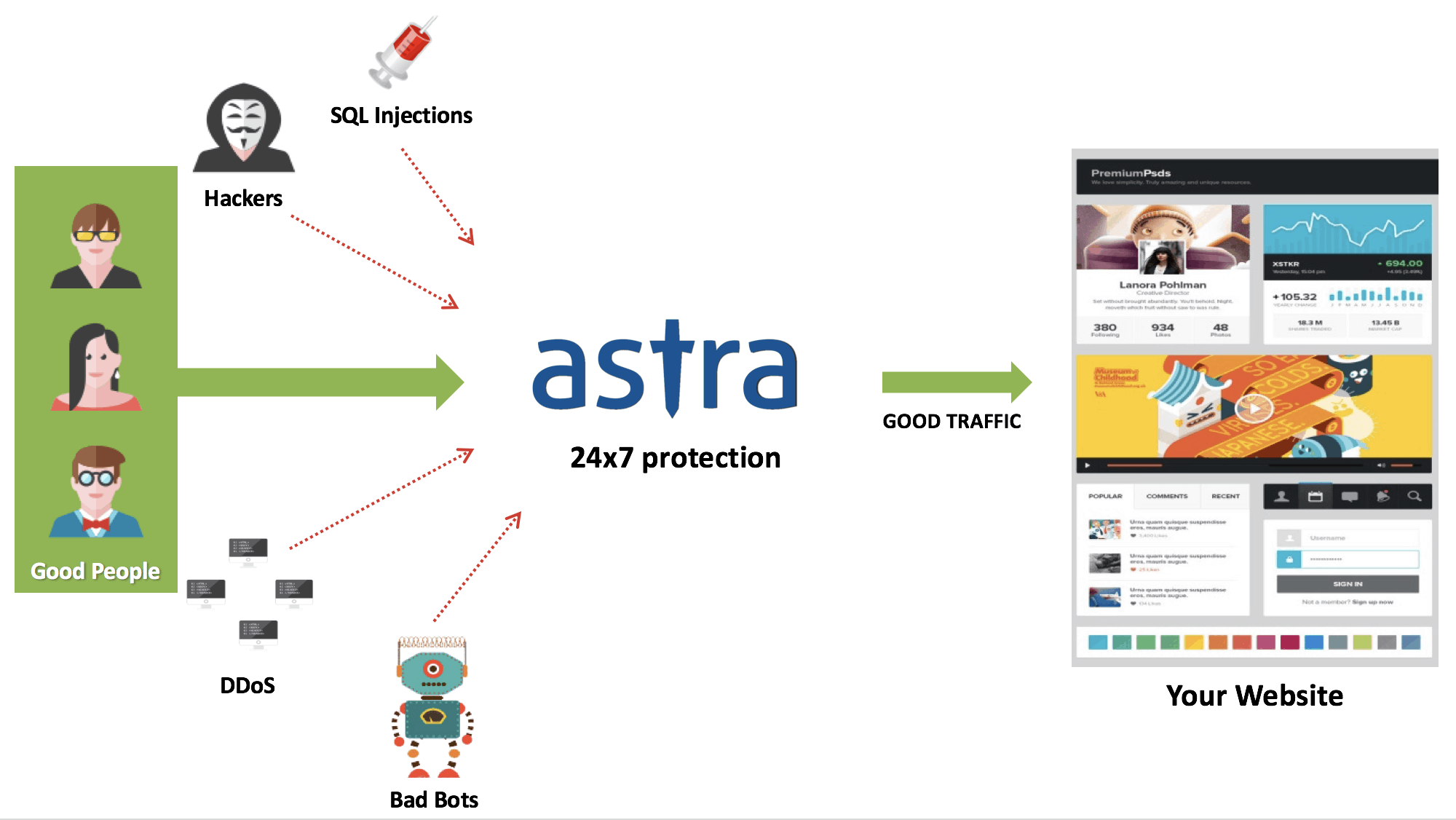
14. Secure Magento Store with a Web Application Firewall
E-commerce stores are a prime target of Hackers. Using a Web Application Firewall like Astra can help analyze the traffic and discover suspicious patterns. A firewall can block malicious traffic and IPs attempting hacks on your website. It safeguards your store from XSS, LFI, RFI, SQL injection and 100+ security threats.
Having a firewall on top of your website is like having a security shield. A firewall is the best way to deploy a real-time website monitoring mechanism. Here is how the Astra firewall protects your website:
15. Hardening Your Server
Securing your server is another pillar in the store security structure. Before you host your website, weigh the hosting provider well for its offerings, such as –
- Security
- Support
- Customization
- Loading time
If you can, ask the hosting provider what security measures it undertakes. Also, review the support it provides. A hosting without proper support can become really frustrating in case anything goes south with your website. A managed hosting solves this problem quite acutely. With managed hosting, you get a dedicated host, who looks after your website and is there to solve 911 emergencies with the site.
Other than managed hosting, hosting on a cloud is quite a rage at present. Cloud hosting reduces the loading time of your site as the information is coming from the closest cluster. Several companies like Amazon, Serverguy, etc. offer cloud hosting at reliable prices.
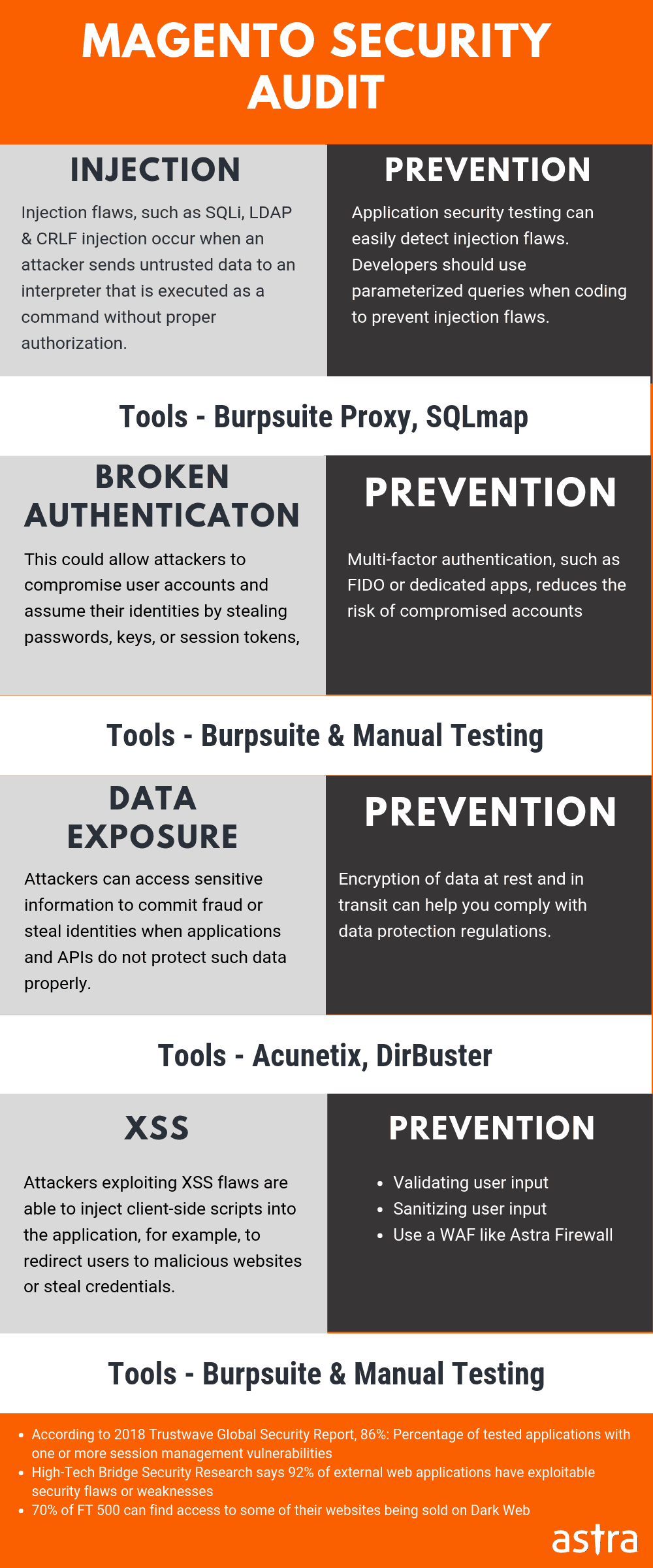
16. Magento Security Audit
Maintaining a website also includes auditing it regularly. A security audit helps you identify loopholes, backdoors, broken security structure before a hacker does. Now, thorough scanning such as an audit might not be feasible for a business owner. Still, you can opt for a professional security audit by Astra.
Astra security experts will do an in-depth security audit and pentesting for you, while you do business. This security audit will uncover each and every vulnerability, loophole & backdoor your site might contain. Our security engineers will also help you with the fixation steps and promises to be there till the time your developers fix it.
Magento Security: In The End…
I know, building a dashing web store requires enormous effort, maintaining it more so. But it is not impossible. To be honest, it is quite the contrary. And, I hope I made a successful attempt at putting across the essential Magento store security measures. Follow the mentioned fundamental practices and improve your online security ten-fold.
If you believe we missed some, just comment below. I will be happy to hear from you!

















Thanks for such an informative guide on Magento security. I was looking for an all in one guide to secure few of my Magento stores.
What is the pricing for your Magento firewall?
Thanks, Grbriel. You can check our pricing here – https://www.getastra.com/pricing
Thanks for such an informative guide on Magento security. I was looking for an all in one guide to secure few of my Magento stores.
What is the pricing for your Magento firewall?
Magento security is getting frequently targeted by hackers to steal card information. Your guide on Magento security is indeed helpful with all proper steps. Do you have any guide on Magento hack removal & what features you offer for Magento store on security front?
Thanks, Maximilian. We always try to make the things simpler so that even non tech people can follow them. You can check our Magento Hack removal guide here – https://www.getastra.com/blog/911/magento-hacked-fixing-magento-vulnerabilities/
& you can check our Magento security suite features here – https://www.getastra.com/features
One of the top class guide on Magento security. I was looking for resources to secure my store from brute force & landed on your Magento security guide.
Awesome work.
Thank you, Sean for your kind words
Hi, when will a website will be marked as dangerous by chrome? I am using magento as tech stack. If it happens how can I resolve this?
Thanks for responding to our article. In this case, you need to find malware, malicious links to reference to malicious links that could be causing this. Basically, a code review for malicious content is required in such cases. Followed by submitting to Google for a review. Ideally, a security firewall is recommended as the website will be on the radar of hackers. This article talks about various malware and fixes, please feel free to review them: https://www.getastra.com/blog/911/magento-hacked/
Hi there, I have a website using Magento CMS. How safe and secure is magento?
Thanks for responding to our post. It’s not Magento that makes your site safe and secure. Instead it’s how your programmer sets up your site with proper security features and does not compromise the code quality while setting it up. Magento being a Zend based CMS is pretty robust and secure in itself and does not encounter common security threats as often encountered with wordpress. In this case, we request you to use a security plugin and that is what we exactly offer.For more information: https://www.getastra.com/magento-firewall and You can follow our magento hack removal guide: https://www.getastra.com/blog/911/magento-hacked
Hello, for my website I can see a lot of Japanese gibberish URLs. Do you have any guide on how to remove this?
Thanks for responding to our post and sorry to hear about the japanese SEO spam. You can follow this article to remove the hack: https://www.getastra.com/blog/911/black-hat-seo-spam-magento-opencart-prestashop/. We recommend you to use a security plugin and that is what we offer where our experts will help you in securing your website. For pricing and details you can visit: https://www.getastra.com/pricing
Magento SQL injection is spreading all over and businesses are getting ruined and I don’t want to take the risk. Is there any guide on how to protect from this?
Yes, you are correct. SQL Command Injection is a technique where an attacker creates or alters existing SQL commands to expose hidden data, or to override valuable ones, or even to execute dangerous system level commands on the database host. It will cause many harmful things to your Magento Store, and your database. You can refer our article on how to protect: https://www.getastra.com/blog/cms/magento-security/magento-sql-injection/
This is really a great article. How can I avoid a Malware injection for my website? I am using Magento.
Thanks for responding to our post. Yes, Magento has witnessed a steep rise in malware attacks. E-commerce platforms are a goldmine for malicious actors to harvest lucrative credit card and personal information from online transactions. You can refer our guide to protect against it: https://www.getastra.com/blog/cms/magento-security/how-to-prevent-magento-code-injection/
So, I own a website and haven’t been using a security plugin or a firewall. How important is it to use a WAF?
Thanks for responding to our post. Precisely, a WAF (Web Application Firewall) is like a gatekeeper that filters all traffic coming to your portal. It protects you from hackers, bots, malware etc. A business can set up online rules for users by having a Web Application Firewall. For more info on the significance of WAF kindly refer this article: https://www.getastra.com/blog/astra-product/ecommerce-security-web-application-firewall/
Hi, I would like to secure my Magento 2 admin panel from hackers. Is there any way I can protect against the attacks?
Thanks for responding to our post. Magento is considered as the best e-commerce platform available today and it has numerous features, plugins, regular updates and a huge community of developers. As the technology and security measures improve, so do the capabilities of the hackers. Hackers usually target e-commerce websites to gain credit card information or just for some kicks. You can refer this article to guard your magento admin panel: https://www.getastra.com/blog/cms/magento-security/steps-secure-magento-admin-panel-hackers-bruteforcing-magento-1-magento-2/