How to Prevent Magento Malware Injection?
Magento, while being one of the most favored e-commerce platforms, has also witnessed a steep rise in malware attacks. E-commerce platforms are a goldmine for malicious actors to harvest lucrative credit card and personal information from online transactions. While Magento owes to its popularity to strict security practices, a timely update of system core and immediate fixes to security issues, attackers continue to take advantage of existing flaws like unpatched vulnerabilities, weak ownership, poor passwords and permission settings.
As a result, educating merchants to follow security best practices has become even more critical than before. While Astra advocates for Magento security practices and puts out its own checklist crafted by security experts with years of experience in Magento Security.
Related Guide – Complete Guide to Magento Security (Reduce the risk of Hacking by 90%)
However, it is paramount that admins understand that under what circumstances their Magento store is likely to be hacked, and what measures can help mitigate this in advance.
Reasons for Magento store hack
An analysis by Magento’s security team reveals that in most malware cases, attackers are not developing new ways to penetrate Magento sites. Instead, they are taking advantage of small existing flaws like weak passwords or improper file settings: all things that can be controlled!
- Missing Magento patches: While the Magento Security team periodically releases security patches whenever any vulnerability comes to light, store owners often do not install these patches immediately. While the vulnerability becomes common knowledge following the release of the patch, it provides the attacker with a window of opportunity to exploit such a store.
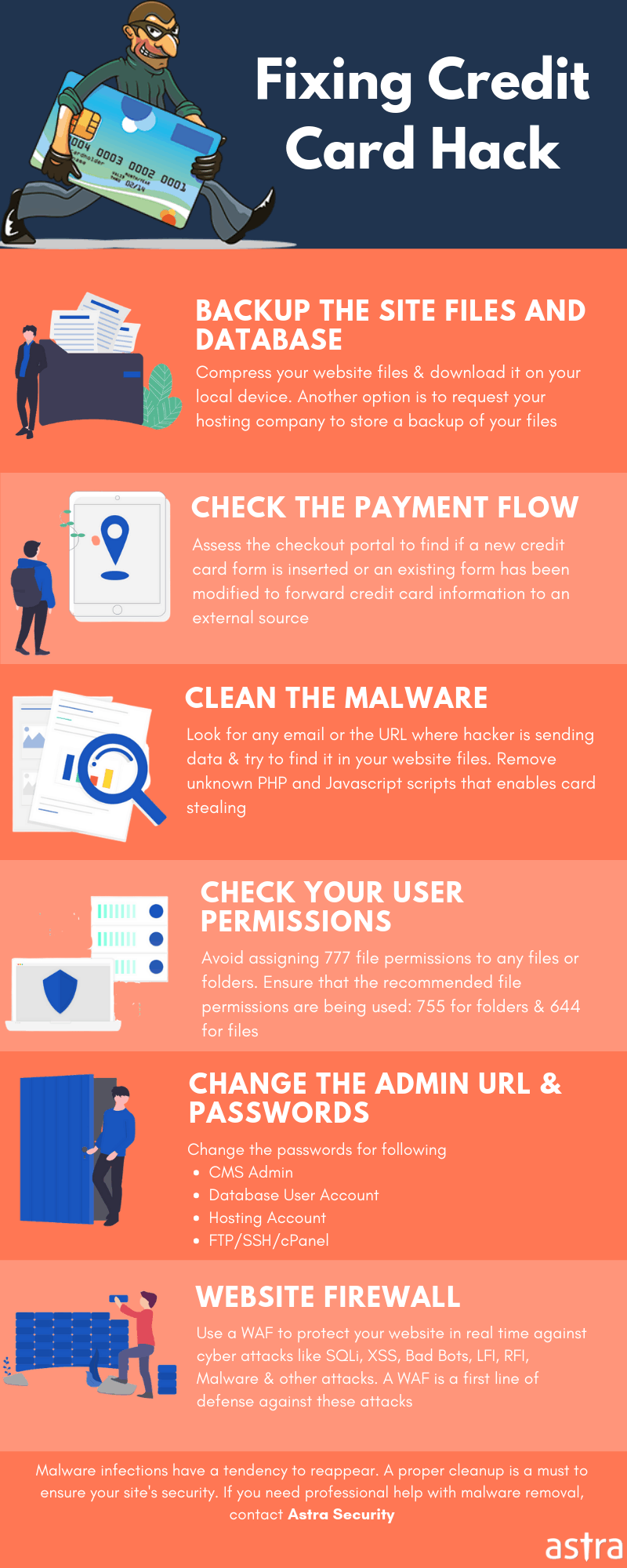
- The website is under-protected and is without a firewall: Lack of a Web Application Firewall for your Magento store is clearly a red flag. A Web Application Firewall is used to analyze traffic and discover suspicious patterns, such as credit card information being sent to an attacker.
- Running an older or outdated version of Magento: Running outdated versions of Magento can prove fatal to store owners as it’ll exempt them from any added security provided by newer versions. This makes them prone to malicious attacks
Consequences of Magento Malware
A compromised Magento site can have long-term consequences for both customers and merchants. While consumers might incur identity theft and financial loss, merchants may end up with a damaged reputation, loss of merchandise, higher processing fees, revoked privileges with financial institutions, and the threat of lawsuits.
In case a successful malware injection occurs in Magento, it can lead to dire consequences like:
- Theft of Customer Information: E-commerce portals often save customer information like e-mail IDs, names, addresses etc.
- Credit Card Hacking: Owing to the large scale of financial transactions occurring in e-commerce portals like Magento, hackers mostly look to create credit card clones or steal financial information
- Phishing pages can be hosted on the server: Once a hacker gains control of admin privileges, he can host phishing pages to bait users into clicking for further malicious prospects. Pishing is a type of social engineering.
- IP Address of server can be blacklisted:
How to prevent Magento Malware Injection
There is a multifaceted approach to improve the security of your Magento site. While there isn’t a single assured way to remove all security risks, there is a combination of things that can be done to make your site a less attractive target. Following some trivial steps, a Magento Malware injection can be avoided:
- Install latest Magento patches: Astra can’t help but advocate the importance of this step as a Magento owner’s top priority step. Newer versions encompass better secure coding practices and vulnerability fixes which is essential to keep your store running hack free.
- Use a tool to scan all file uploads for malware: Malware injections through form field is one of the most commonly used ways to inject a malicious script into an application. Therefore, it is important to sanitize user-supplied data and filter for malware using a scanner. Astra provides with a security scanner for malware detections in Magento stores.
- Regular Malware Scanning: Regular periodic malware scanning proves useful in fishing out any unprecedented flaws which can potentially lead to a fatal malware attack sooner or later. To know more, check out Astra’s Magento Malware Removal tool.
- Use a web application firewall: A Web Application Firewall allows you to analyze traffic and discover suspicious patterns, such as credit card information being sent to an attacker.
- Implement Magento Security Best Practices: Following expert suggested Magento Security best practices can go a long way in securing your Magento store from online attackers.
Implement the above steps beginning now!
Also, check our article on Web Application Firewall- A must needed security for your Ecommerce store.
Still worried about how to protect your Magento site from online threats? Visit Astra’s Magento Security Suite to secure your Magento site. To stay abreast with latest happenings on Magento threats and released updates, follow our blog on Magento Security.