What is Cloki Malware?
A new kind of malware has surfaced, dubbed as “Cloki” which has been slowing down (& also crashing) vulnerable Joomla & WordPress websites. The malware is able to execute core system commands without having access to cPanel or SSH. It is able to add a cron job so that the malware code is executed repeatedly in a very short time. This causes the server resources to be maxed out, making your WordPress and Joomla websites slow. We have seen cases where hosting accounts like like GoDaddy, Hostgator, and InMotion have suspended the Linux shared hosting accounts of website infected with Cloki.
How to check if you are hacked with Cloki
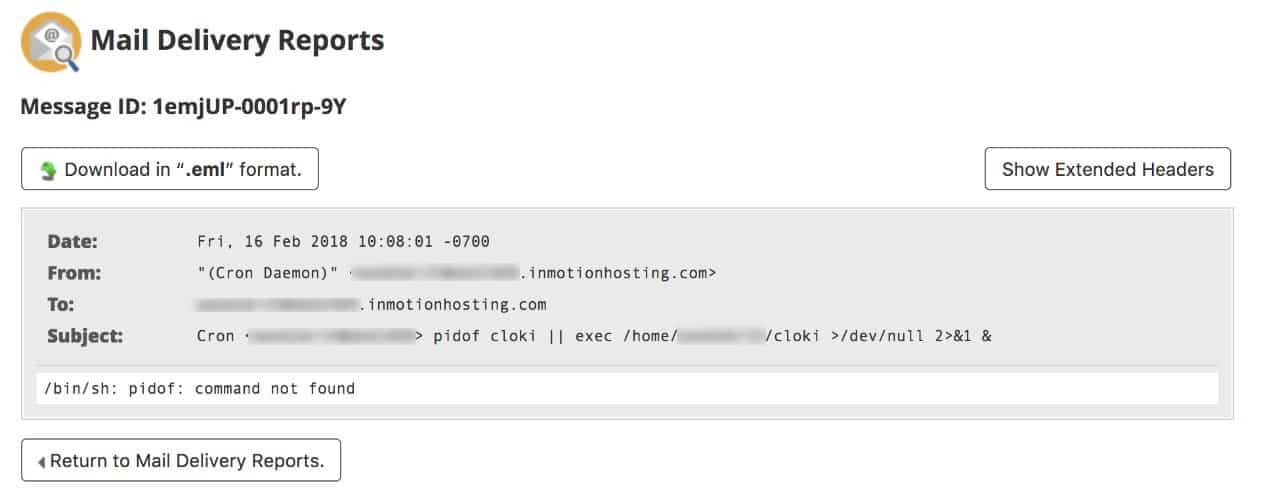
- Check the Cron Jobs/CronTabs running on your server (via cPanel): If you see a cron job you have not added, which looks like this:
root@<owner>:/home/<owner># crontab -l -u <owner> */4 * * * * pidof cloki || exec removed script”
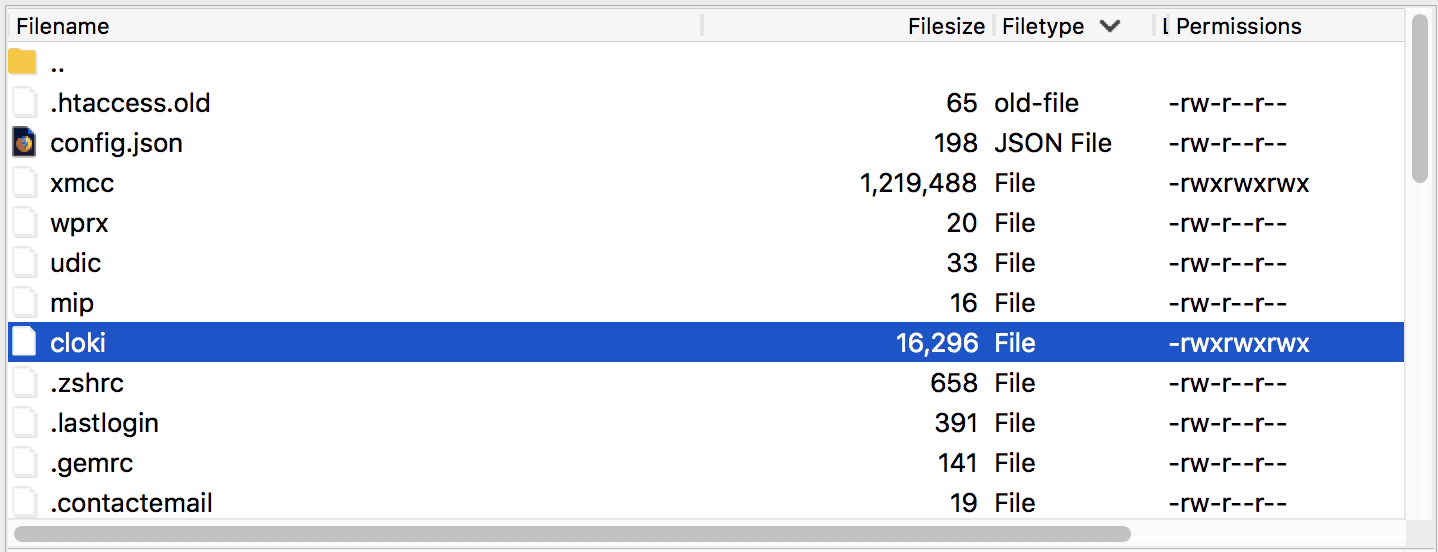
- Check for files with the following name on the server. They are usually located in the home directory of your user:
- cloki
- mip
- udic
- wprx
- xmcc
How to Fix Cloki Malware
- Temporarily disable/suspend your hosting account via the cPanel/WHM or by raising a ticket with your hosting company
- Create a custom php.ini fine in the public_html folder that has the following ‘disable_functions’ added:
show_source, system, shell_exec, passthru, phpinfo, popen, proc_open, allow_url_fopen, eval, exec, parse_ini_file, open_base, symlink. - Delete the Cloki cron job which you must have found in the earlier section.
- Delete all instances of the malicious files mentioned below:
- cloki
- mip
- udic
- wprx
- xmcc
- Re-enable your hosting account and monitor the website for a few minutes.
- Check the files or cron jobs if have been created again by the malware
How to Protect Joomla and WordPress from Cloki
- Protect the site with a Web Application Firewall (WAF)
- Disable dangerous PHP functions on the server using the the php.ini file as mentioned in the previous section.
- Update the CMS & plugins, i.e WordPress & Joomla core versions
- Check for vulnerable file upload areas in your website. Make sure
- Regularly monitor file & cron job changes on the server
Removing Cloki can get a little tricky. The malware has a tendency to reinfect very quickly. By the delete you one file/cron job, another gets created almost instantly. If you want help in cleaning this infection from your website, head over to our website cleanup & malware removal page.
















Excellent blog post. I used to be looking for something very different,
but stumbled on your blog. I am glad I did. Many thanks for sharing
useful information. Thank you and all the best.