If you are reading this, you are either looking to validate your current pentesting partner or shopping for one because your board, auditors, or enterprise clients are asking for independent security validation, risk assessments, or proof of compliance alignment across frameworks like SOC 2, PCI DSS, and ISO 27001.
So let’s break down the top 10 penetration testing companies, what they actually deliver, and how to pick the right one for your specific threat landscape, attack vectors, and compliance requirements.
This article was originally published in February 2024 and has been updated for freshness in 2026 and technically reviewed by Chris Kubecka, Cybersecurity Researcher and Cyber-Warfare Specialist, to ensure accuracy and methodological integrity.
List of the Top 10 Penetration Testing Companies
Best For Mid-Market/SMB Tier:
Best For Hybrid/PTaaS Tier:
Best For Enterprise/Consulting Tier:
Our Evaluation Criteria
Choosing a top penetration testing provider is a mix of proof, speed, and predictable outcomes. Here’s a concise checklist of the criteria we have considered while shortlisting these penetration testing companies.
| Criteria | What to look for |
|---|---|
| Testing Methodology & Depth | Go for manual exploitation + automated scanning and threat modeling. Tests mapped to PTES, OWASP, and NIST SP 800-115. Look for PoC exploits, exploit chaining, and white or grey box options for deeper coverage including privilege escalation and lateral movement scenarios. |
| Compliance Alignment & Certifications | Organizational accreditations and individual tester certs are vital. Seek CREST, ISO 27001, and PCI mapping when relevant. Verify tester credentials, such as OSCP or eWPTXv2, and clear audit evidence for SOC2/HIPAA needs and regulatory risk validation. |
| Reporting Quality & Remediation Support | Multi-audience reports that include executive summaries and developer-friendly findings hold importance. Prioritized remediation steps, CVSS scoring, PoC evidence, and integrations with Jira/CI pipelines supporting DevSecOps workflows. Retesting and remediation support should be included, too. |
| Delivery Speed & Engagement Flexibility | Look for PTaaS/hybrid models that fit sprint cycles. Fast onboarding, live dashboards, API access, and on-demand retesting enable continuous attack surface validation.. Ensure the vendor can scale windows for red team while offering continuous checks for frequent deploys. |
| Pricing Transparency & Service Quality | Clear tiers and SOWs with predictable SLAs. Pricing tied to scope and methodology, not hidden credits. Look for guaranteed retesting until critical issues are closed and explicit statements on turnaround and support. |
Bonus point: Scalability matters. Confirm the vendor can extend coverage via APIs, integrations, and custom engagements as your asset base grows.
Top Pentesting Vendors Comparison
Penetration Testing Companies (Comprehensive Review)
Though this is not an exhaustive list, here’s how the top 10 penetration testing companies compare against each other:
1. Astra Security [Get Started]
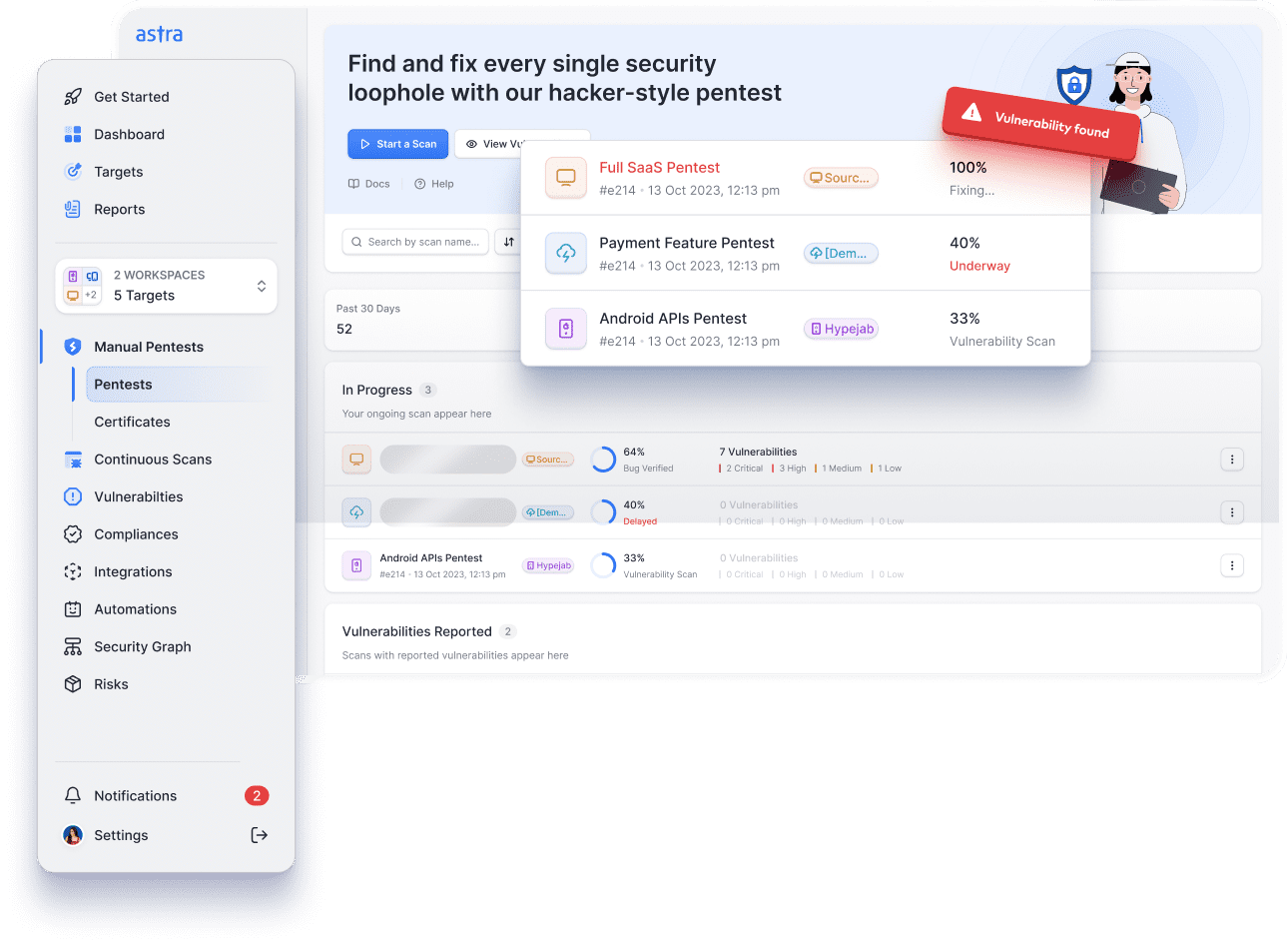
Astra Security is an AI-led, continuous penetration testing company with hybrid DAST and manual pentesting capabilities delivered by CREST-certified experts following structured offensive security testing methodologies.
The hybrid model suits SaaS, mid-market, and enterprise teams that need continuous security validation aligned with OWASP standards, NIST security guidance, and modern application security posture management practices.
The company holds CREST and ISO 27001 accreditation and issues verifiable certificates upon remediation.
Reports are developer-friendly and include PoC artifacts demonstrating real-world exploitability, such as authentication bypass, business logic abuse, and access control weaknesses to speed fixes and retesting.
Key Features:
- A hybrid delivery model that pairs automated coverage with human expert-led exploitation for realistic results.
- Compliance-oriented services that map findings to PCI DSS, SOC 2, HIPAA, and NIST SP 800-115.
- Developer-centric reports with PoC videos, CVSS ratings, and Jira Slack integrations to streamline remediation.
- Evidence issuance and board-ready reporting that supports procurement and vendor risk reviews.
Penetration testing services offered:
- Web, API, cloud, AI, mobile, and network pentesting covering attack surface enumeration, API authorization testing, cloud misconfiguration analysis, identity and access control validation, and real-world adversary simulation
- AI-assisted continuous checks + prioritized manual exploit work for real-world coverage
- Certified testers who publish research and hold OSCP, CEH, eWPTXv2, and other credentials
- Industry-tailored modules for fintech, healthcare, and regulated SaaS environments
- Deep DevOps integration with CI/CD connectors and automated retests for validated fixes
- Verifiable certificates and executive dashboards for procurement and board reporting.
Other services:
- Vulnerability management platform
- WAF and API security controls
- Threat monitoring and managed security
What do the customers say:
Customers feel that Astra’s platform is intuitive and developer-friendly, combining automated scans with expert manual validation to produce prioritized fixes.
G2 rating: 4.6/5 ⭐(180 reviews)
2. Invicti Security
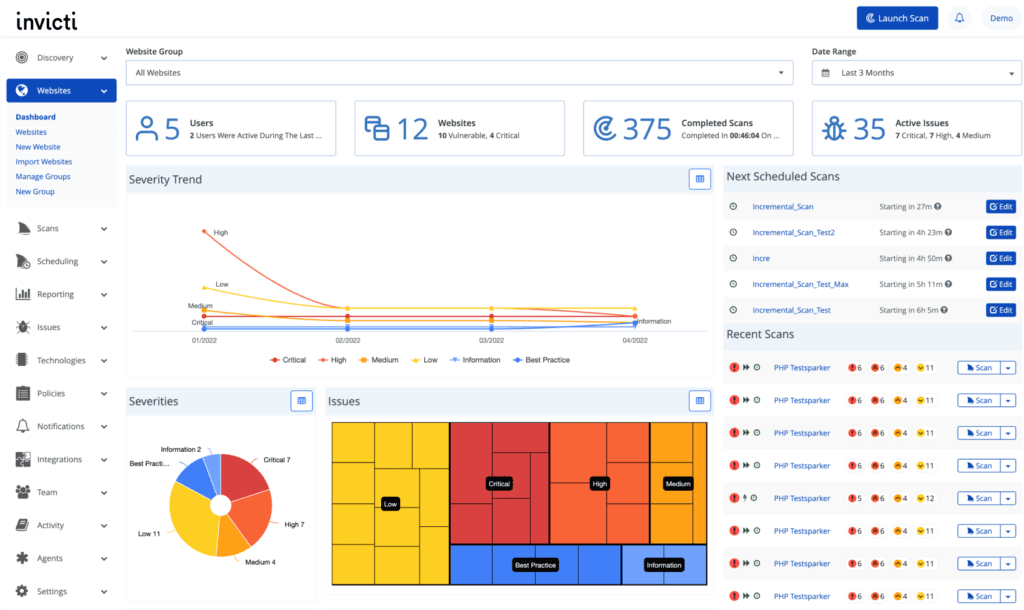
Invicti is known for scalable automated testing that supports DevOps and AppSec teams. The pentesting company focuses on accurate DAST scans with proof-based validation to reduce false positives and speed remediation.
Many engineering orgs rely on Invicti as a pen-testing provider to maintain steady coverage of web and API assets integrated into CI/CD pipelines.
Key Features:
- Proof-based scanning that reduces wasted engineering time
- Enterprise-scale automation that fits into DevOps for continuous testing
- Unified AppSec that combines DAST with API discovery and vulnerability management
- Strong reporting and remediation tracking
Penetration testing services offered by Invicti:
- Web application and API penetration testing
- Automated DAST
- Compliance scanning support and regulatory checks
Other services:
- Application security posture management and SCA capabilities
- AppSec consulting
What do the customers say:
Customers find Invicti’s web scanning to be pretty quick, intuitive, and highly accurate at detecting a broad range of vulnerabilities.
Users do warn about occasional slow performance, API/upgrade friction, and limited endpoint testing, which can undermine confidence for deeper manual pentests.
G2 rating: 4.6/5 ⭐ (68 reviews)
3. NetSPI
NetSPI is one of the top-rated offensive pentesting companies in the US, known for its BAS expertise and enterprise-scale PTaaS, simulating real-world adversary tactics aligned with the MITRE ATT&CK framework mapping.
NetSPI uses a platform approach, combining expert consulting with proprietary tech to manage engagements efficiently.
Their Resolve platform helps orchestrate complex engagements and track remediation across teams.
Key Features:
- Breach and attack simulation expertise combined with platform orchestration.
- High-end technical talent for complex multi-layer engagements.
- Conducting in-depth, human-led testing across modern infra, including APIs, web apps, and cloud environments.
Penetration testing services offered by NetSPI:
- Network, web, and mobile penetration testing
- Cloud penetration testing
- API penetration testing
- Red/Purple teaming
- Breach and attack simulation (BAS)
Other services:
- Attack surface management
- Adversary readiness consulting
What do the customers say:
Customers emphasize the abundant communication and support from the NetSPI team, which includes multiple kickoff calls and frequent check-ins to ensure a clear scope and expectations.
The testers and pentest consultants are described as “top-notch,” and the Resolve platform is praised as a one-stop portal for all pentest activities.
G2 rating: 4.9/5 ⭐ (11 reviews)
4. Cobalt
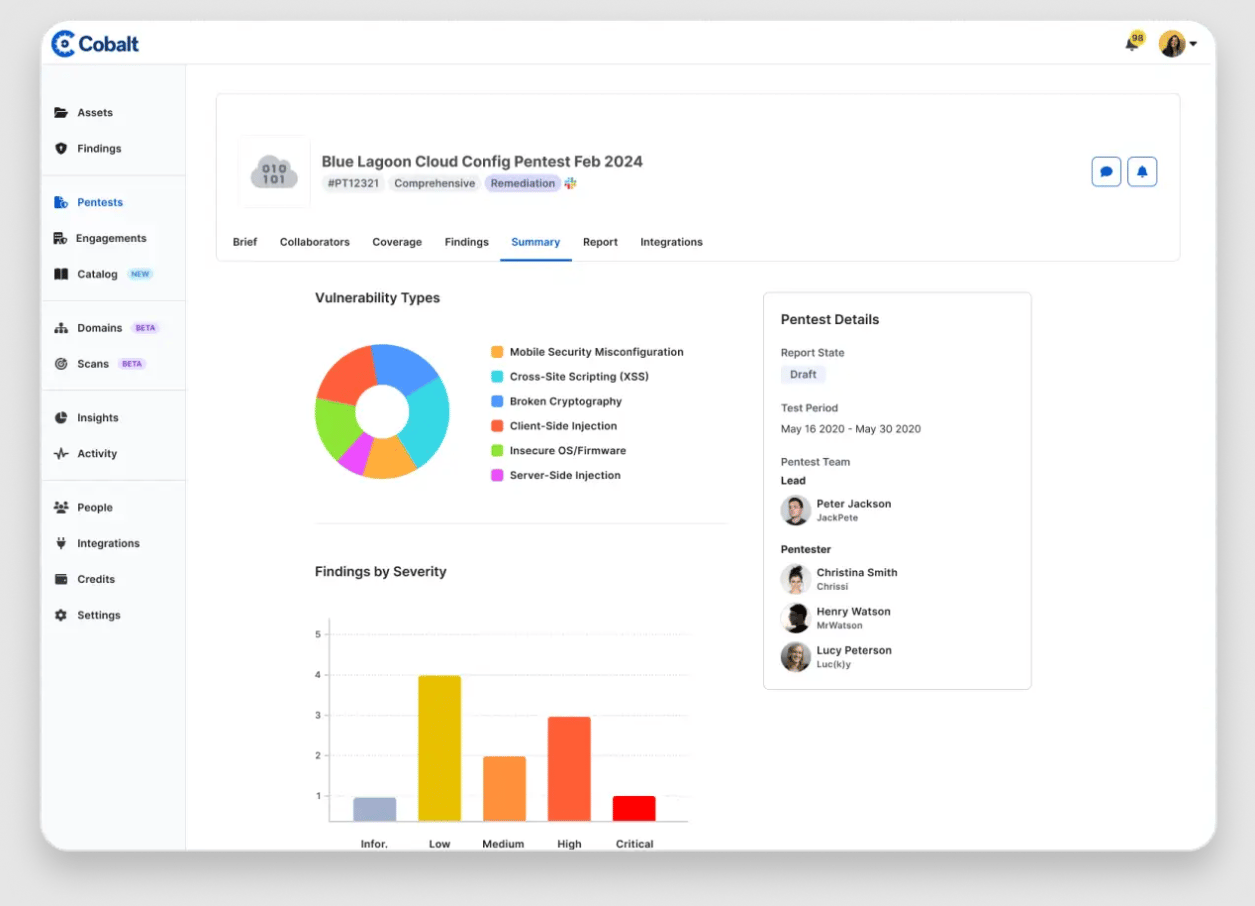
Cobalt is another pick from the long list of top penetration testing companies that delivers on-demand PTaaS through a managed service model and has a curated researcher network.
It works with DevOps teams to integrate security into deployment pipelines and offers predictable engagements for recurring assessments.
Cobalt focuses on delivery speed and collaboration with engineering teams.
Key Features:
- Managed PTaaS delivery with live results and scoped engagements
- Strong Jira and CI/CD integrations for developer handoffs
- Global vetted researcher pool enabling rapid scaling by skill and region
Penetration testing services offered by Cobalt:
- Web, API, mobile, and network testing
- Cloud configuration reviews
- Red team and specialized AI/LLM testing.
Other services:
- Attack surface management
- Vulnerability management integration.
What do the customers say:
Customers feel that Cobalt enables quick, flexible pentesting with strong collaboration tools and clear reporting.
G2 rating: 4.5/5 ⭐(172 reviews)
5. BreachLock
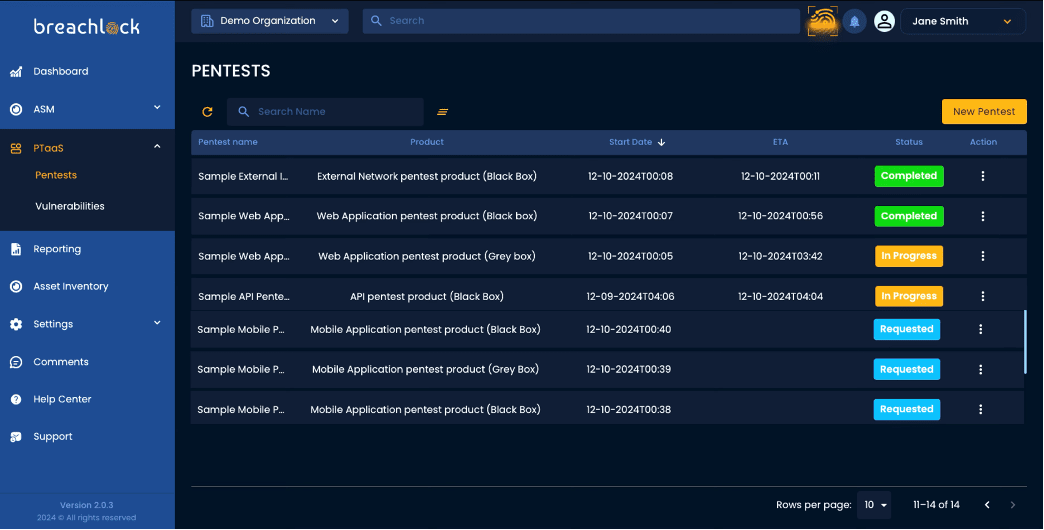
BreachLock, based in the US, is a pentesting provider that offers comprehensive, hybrid VAPT solutions focused on continuous security validation with cost efficiency and scalability.
It uses automation for baseline coverage and pairs it with manual validation to maintain accuracy and depth while keeping costs sensible.
The platform is aimed at teams that need frequent tests for variable digital targets, clear remediation workflows, and competitive pricing.
Key Features:
- A hybrid approach that balances automated scanning and manual verification
- Scalable plans optimized for repeatable checks
- Built-in ticketing and remediation workflows that ease developer handoffs
Penetration testing services offered by BreachLock:
- Web, API, mobile, cloud, and network pentesting
- IoT and embedded device assessments.
Other services:
- Dark web monitoring
- Phishing simulations
What do the customers say:
Customers feel BreachLock delivers thorough tests via an easy portal and detailed reports that help teams prioritize fixes.
G2 rating: 4.6/5 ⭐ (37 reviews)
6. Synack
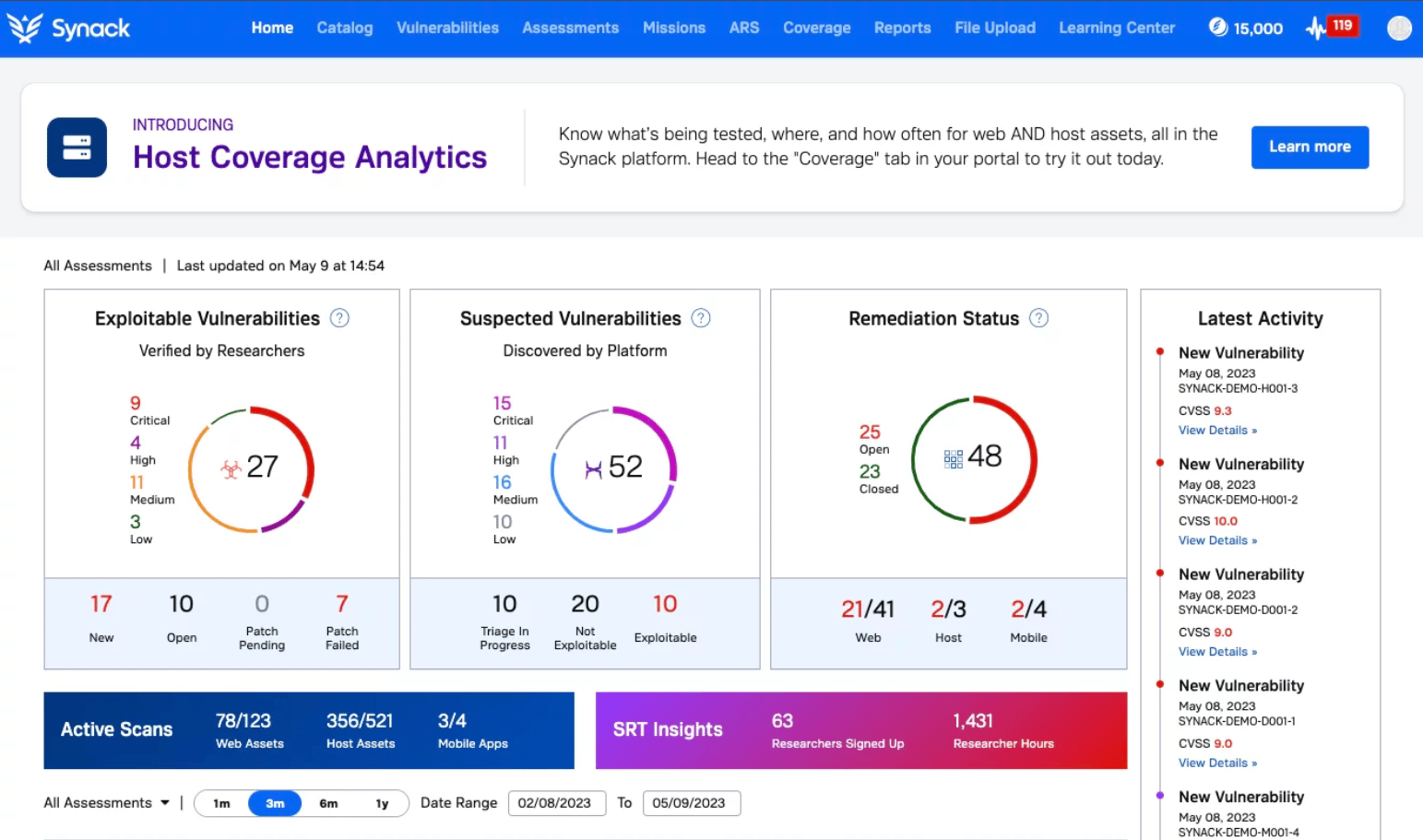
Synack is a penetration testing company that operates as a crowdsourced red team PTaaS platform, providing customers with on-demand access to a highly vetted, specialized network of global security researchers.
It blends human expertise with AI capabilities to deliver large-scale continuous testing. The crowd-based model is best for enterprises needing broad coverage across dynamic assets.
Key Features:
- Crowdsourced red team (Synack Red Team) with strict vetting and platform controls
- Agentic AI (named SARA) directed workflows that focus on augmenting researcher effort and facilitating continuous, highly targeted pentesting.
- Secure testing environment and on-demand capacity.
Penetration testing services offered by Synack:
- Web, mobile, API, network, and cloud pentesting
- Red team and third-party assessments.
Other services:
- Vulnerability triage
- Attack surface discovery
- Security research and bug bounty management.
G2 rating: 4.7/5 ⭐(14 reviews)
7. Redbot Security
Redbot Security is a specialized pentesting provider known for delivering customized penetration testing engagements, including assessments for niche, high-risk systems like Industrial Control Systems (ICS) and SCADA.
It focuses on OT, ICS, and industrial environments while also covering cloud and web layers.
They mostly cater to orgs requiring flexibility in scoping and budgeting, often working within specific constraints to deliver measurable ROI.
Key Features:
- OT and ICS expertise with scenario-based attack simulations
- Hands-on exploit chaining and impact-centric reporting
- Flexible scoping to fit constrained or high-risk industrial environments
- Capable of integrating continuous testing for evolving assets like APIs
Penetration testing services offered by Redbot Security:
- ICS/SCADA penetration testing
- Web and mobile penetration testing
- Cloud infra testing
- API penetration testing
- External and internal network penetration testing
- Red/Purple team exercises
Other services:
- Vulnerability management
- Security architecture reviews
- Compliance gap analysis
G2 rating: NA/5 ⭐(No reviews yet)
8. HackerOne
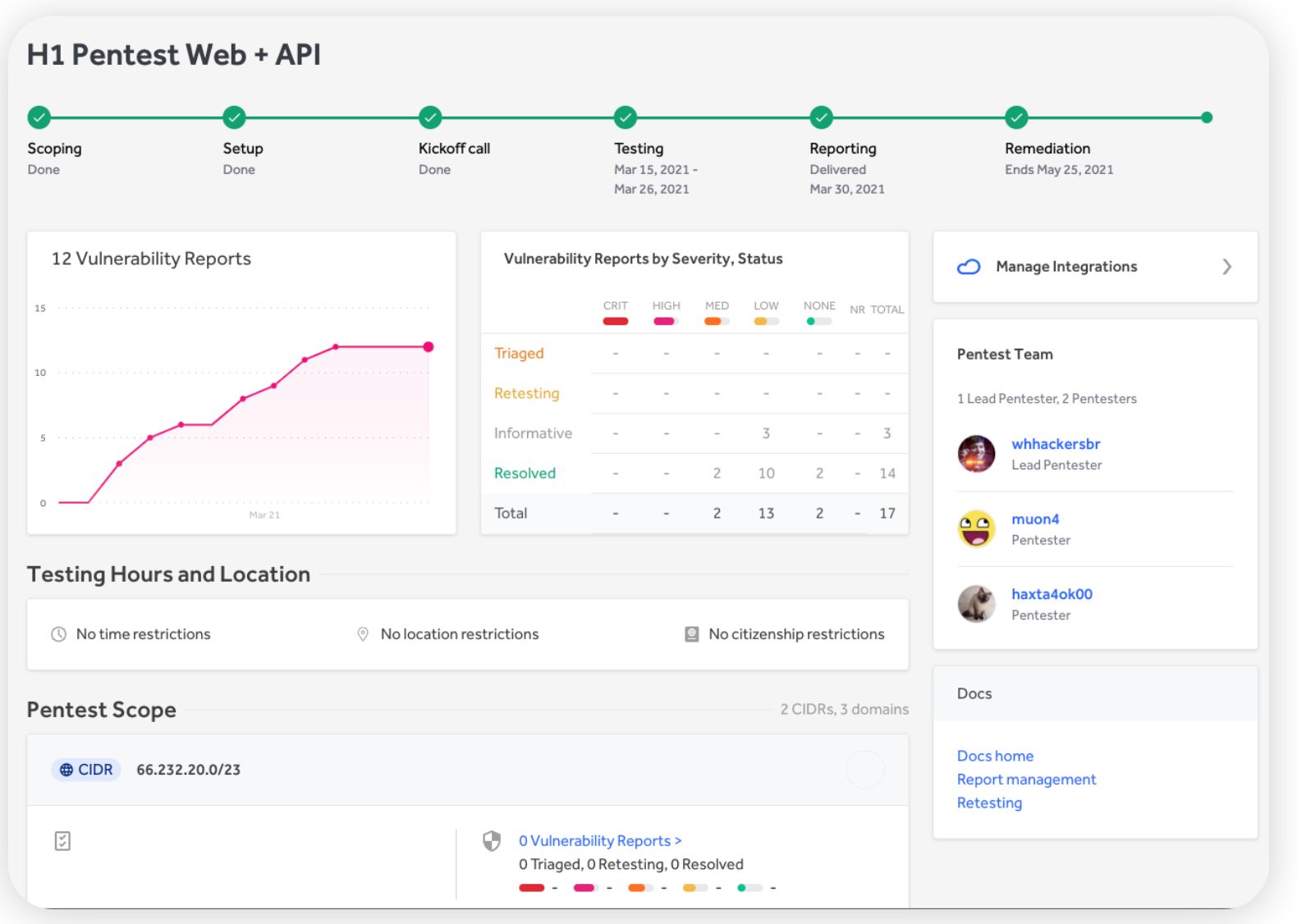
HackerOne is a pentesting company that connects organizations to a global community of vetted researchers for both bug bounty programs and PTaaS.
Many security teams use HackerOne as a flexible penetration testing vendor to gain fresh perspectives and continuous coverage across web, API, mobile, and infrastructure assets.
Key Features:
- Crowdsourced expert community providing diverse testing techniques and perspectives
- Real-time PTaaS delivery with dashboarded findings and workflow integrations
- Broad asset coverage, including web, APIs, mobile, cloud, and emerging AI systems
Penetration testing services offered by HackerOne:
- Web app and API pentesting
- Mobile security assessments and cloud infra reviews
- Network/desktop testing + targeted PTaaS engagements
Other services:
- Managed bug bounty programs
- Attack surface management
- Training resources and advice on secure SDLC practices
What do the customers say:
Customers value HackerOne for access to a large, skilled group of testers and for a platform that scales vulnerability discovery beyond traditional pentests.
That advantage comes with tradeoffs, though, since users report slow triage, inconsistent analyst performance, and a steep learning curve.
G2 rating: 4.5/5 ⭐ (64 reviews)
9. CrowdStrike
CrowdStrike is a recognized pentest provider in enterprise risk management and endpoint security.
It uses threat intelligence from its Falcon platform to run adversary emulation and red-team exercises based on real-world attacker TTPs (Tactics, Techniques, and Procedures) that tune detection and response.
It best suits large enterprises that want intel-driven testing tied to MDR.
Key Features:
- Intelligence-led adversary emulation using real-world TTPs
- Integration with EDR and cloud protection controls
- Strong red team capabilities and incident response alignment
Penetration testing services offered by CrowdStrike:
- External and internal network penetration testing
- Red team operations and adversary emulation
- Cloud penetration testing
- Web application pentesting (context-specific)
Other services:
- MDR and Cloud security posture management (CSPM)
- Identity protection (Identity Threat Detection and Response)
G2 rating: 4.6/5 ⭐(588 reviews)
10. Rapid7
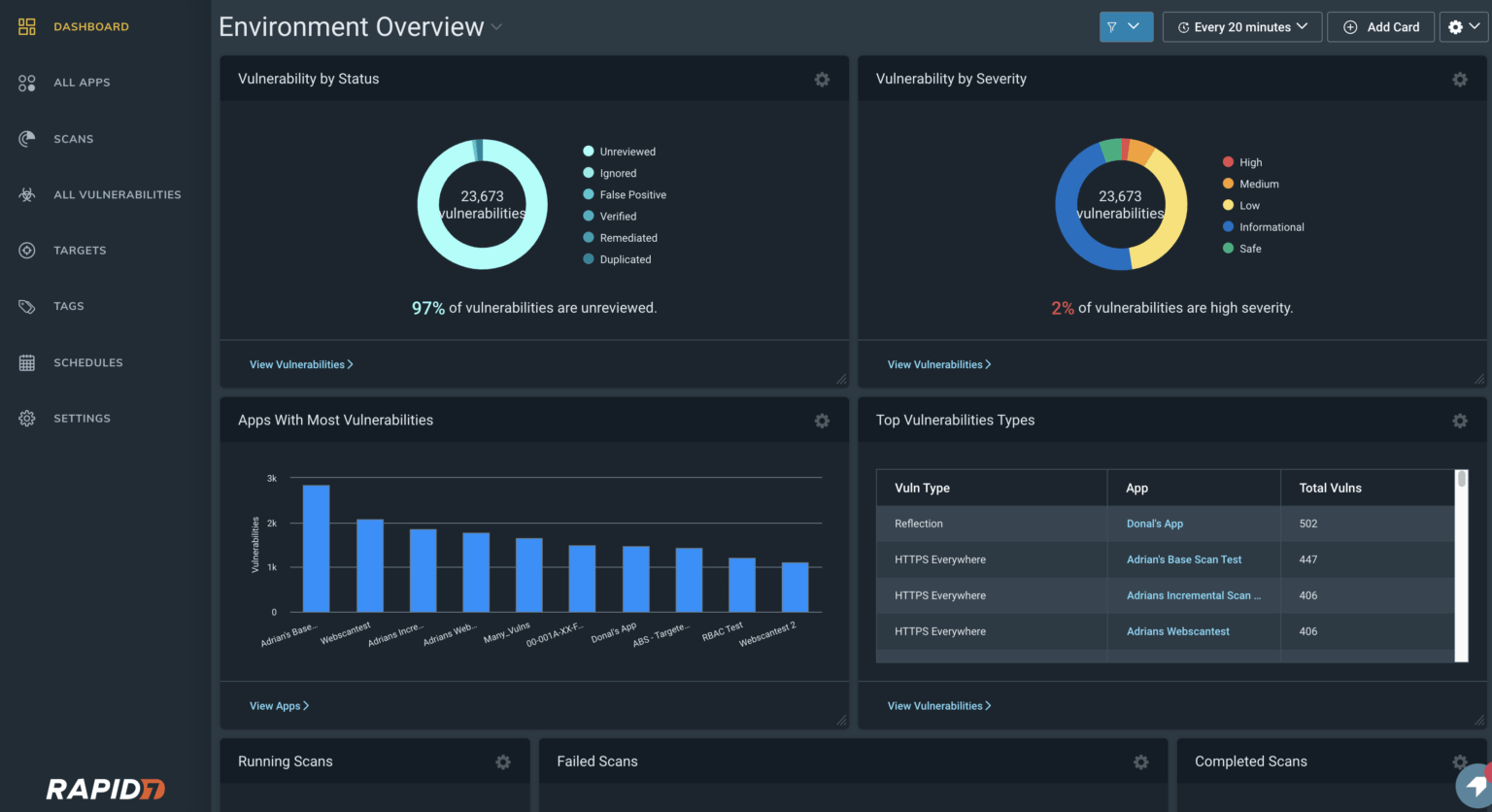
Rapid7 is one of the most reputable penetration testing companies in the USA that leverages its expertise in vulnerability management (InsightVM) to deliver platform-integrated penetration testing services.
It masters the PTaaS model by providing expert consultation via a cloud-based portal that delivers live results, enables direct communication with testers, and provides critical on-demand retesting functionality.
It works well for organizations that want a single view of risk across scans and manual tests.
Key Features:
- Platform-driven PTaaS + InsightVM integration
- Research-oriented team (20% research time) with Metasploit contribution
- Flexible engagement models from one-off audits to PTaaS subscriptions
Penetration testing services offered by Rapid7:
- Web and mobile application penetration testing
- External and internal network penetration testing
- Cloud security assessments
- Red team exercises
Other services:
- Vulnerability management (InsightVM)
- Application security testing (InsightAppSec)
- Security information and event management (SIEM)
What do the customers say:
Customers feel that Rapid7’s security services offer powerful, comprehensive vulnerability management.
Many cite the in-depth visibility it provides across networks, workloads, and the strong reporting capabilities, making it easier to prioritize and fix issues.
G2 rating: 4.3/5 ⭐ (256 reviews)
How to Choose the Right Penetration Testing Company?
How you pick from some of the top penetration testing companies in the USA should feel like procurement, not guesswork.
Here are some steps you can take to make that decision effective:
1. Define Objectives (Compliance vs Detection)
Be precise about why you are paying a pen test provider. If the goal is audit readiness, prioritize pentest vendors who deliver mapped evidence and certificates.
If you want adversary simulation, prioritize red team capabilities and exploit narratives that prove business impact.
Questions to ask yourself:
- Is the objective compliance, risk assessment, or simulation of a real-world attack?
- Are success criteria clearly defined and measurable?
- Are all internal stakeholders aligned on goals and expectations?
- Does the vendor offer executive-level summaries as well as technical depth in reporting?
Pro Tip: Treat objective-setting as a design decision, not a checklist. Ask your team to identify the specific question this test should answer, and then verify that your vendor can deliver on that exact outcome.
2. Scope Impact on Production
Decide how much risk to uptime you will accept and communicate that to penetration testing vendors.
A mature provider will give options for safe, authenticated checks and for deeper, controlled exploitation windows.
Ask about rollback plans and who owns kill switches so your business continuity is never compromised.
Questions to ask yourself:
- Is the provider experienced with your environment type, on-prem, cloud, hybrid, or containerized?
- Can they safely test production systems if needed?
- Can they assess APIs, microservices, mobile apps, and legacy components as part of the engagement?
- Do they have relevant industry or compliance experience, such as SOC 2, HIPAA, or PCI?
3. Stakeholder Alignment
Testing fails when findings land in inboxes and stall. Get product, infra, legal, and procurement in the room before scoping.
Define handoff points and retest SLAs so fixes do not linger. Insist on reports that serve both the board and the engineer.
Questions to ask yourself:
- Are internal stakeholders aligned on remediation ownership and timelines?
- Does the vendor provide both executive summaries and dev-friendly runbooks?
- Will the provider coordinate post-test retesting and evidence delivery?
Pro Tip: Bring stakeholders in early, frame the test around what matters to them (reputation, uptime, liability), and treat the post-test readout as a strategic moment, not a security report walkthrough.
4. Manual vs Automated Trade-Offs
Automation finds volume. Humans find nuance.
Choose pen test providers that mix both and can show time allocation per phase to balance coverage depth with attack realism.
High-risk apps require manual exploit time and code review, including business logic and authorization testing. For broad surface coverage, look for authenticated scans and API analysis.
Questions to ask yourself:
- Is their approach a blend of manual and automated methods?
- Do they support CI/CD and ticketing integrations for automated handoffs?
- Can they offer flexible testing frequency on demand or tied to release cycles?
5. Frequency and Provider Rotation
Treat testing as a frequency, not a calendar event within a continuous security validation strategy.
Use PTaaS for sprint pace and rotate providers periodically to avoid stale coverage and detection bias.
New teams bring new techniques and expose assumptions your current providers might miss.
Questions to ask yourself:
- Do they include remediation retesting, or is it a separate purchase?
- Have you planned periodic vendor rotation to avoid blind spots?
- Are additional services like IR or secure dev training available from the provider?
Final Thoughts
The right penetration testing company isn’t the one with the flashiest services. It’s the one that matches your actual security maturity and compliance pressure.
If you are a SaaS startup needing continuous validation for enterprise buyers, PTaaS models like Astra Security or Cobalt make sense.
If you are managing critical infra/OT environments, specialized consulting from Redbot or Mandiant is the way to go.
With an 83% surge in critical vulnerabilities, picking a provider based solely on price is strategic negligence.
Match methodology depth, certifications, and engagement flexibility to your risk profile and then shortlist accordingly.
FAQs
1. What assets generally get pentested by these pentesting companies?
Typical assets include external-facing networks, internal networks, web and mobile applications, APIs, cloud services, databases, and even IoT/embedded devices, depending on the scope.
2. What is the average cost of a penetration test?
A standard penetration test usually ranges between US $10,000-30,000, though simpler projects may start around $5,000, and complex engagements can exceed US $100,000.
This usually depends on factors such as scope, complexity, target assets, testing depth, and whether it’s a one-time assessment or part of a continuous engagement.
3. Do penetration testing firms also support compliance like HIPAA, ISO 27001, and PCI DSS?
Yes, leading penetration testing companies like Astra Security help you meet major compliance requirements by mapping your engagement to them.
Their services therefore provide the documented evidence needed for audits against standards like PCI DSS, HIPAA, ISO 27001, and more.
4. Why do I need a penetration testing company despite having an internal security team?
Yes, you need a penetration testing company even with an internal security team.
An external provider brings an independent “attacker’s” perspective, specialised expertise, and a fresh set of eyes to uncover blind spots your internal team may miss due to familiarity or bias.









Nice informative article. I was curious on how to get the most out of a penetration testing services?
To get the most out of penetration testing services you must stick with a reputable provider you can trust, establish a clear testing scope that prioritizes important assets, provide detailed information regarding your network and systems, and have a realistic expectation of the outcomes.