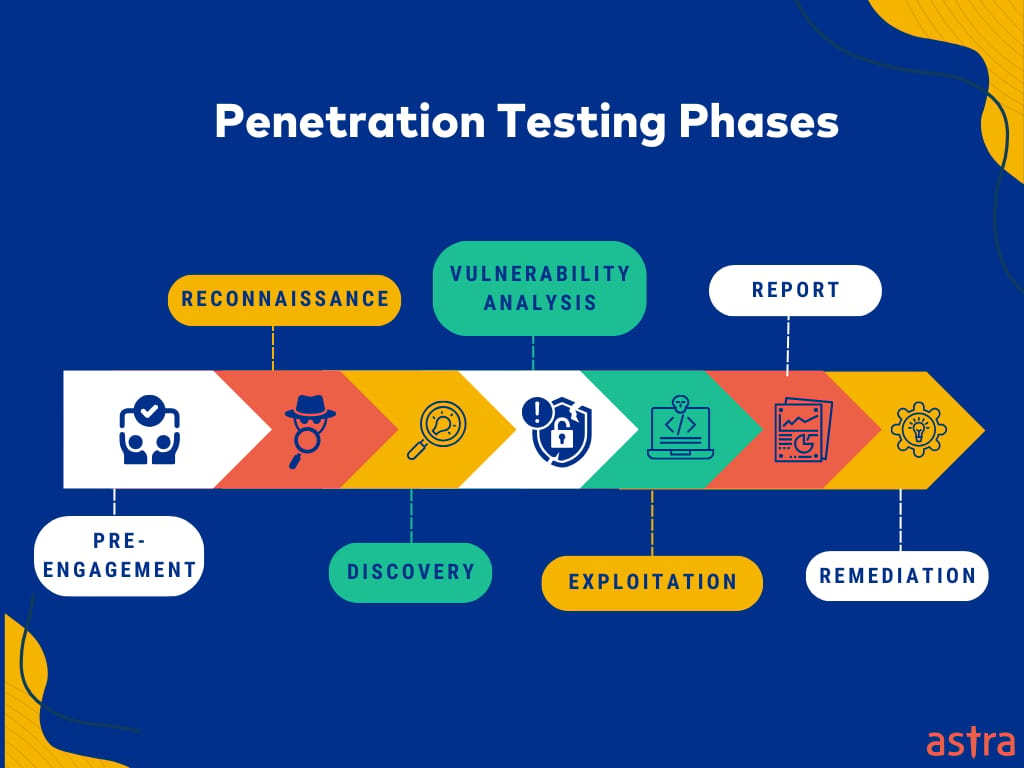
Penetration testing finds vulnerabilities in a given system or network and is, in essence, a stimulated cyber attack with multiple phases. The process begins by identifying the scope and objectives and gathering information about the target.
This ushers in the asset-mapping phase, which details identifying systems, networks, and applications within the target environment. After the assets have been mapped out, vulnerability analysis identifies any possible weaknesses. These are then exploited during and after exploitation to assess the potential impact.
Finally, in the reporting stage, the expert outlines the vulnerabilities found, provides the steps to remediate them, and suggests a rescan schedule to test the effectiveness of the countermeasures implemented.
New to security testing? Here’s the complete guide to VAPT and why it’s essential for every organization.
What are the Phases of Penetration Testing?
- Phase I: Pre-engagement phase of Pentesting
- Phase II : Reconnaissance
- Phase III: Discovery
- Phase IV: Vulnerability Analysis
- Phase V: Exploitation and Post-Exploitation
- Phase VI: Reporting and Recommendations
- Phase VII: Remediation and Rescan
Penetration Testing Phase I: Pre-Engagement Phase
At this stage, the security expert analyzes the test’s logistics and rules of engagement. The VAPT providers and the target organization discuss the exercise’s legal implications.
- Define the test’s objectives: The penetration testing team and the customer collaborate to establish clear goals for the test that align with the organization’s specific security requirements.
- Determine the test’s scope: The service provider and the customer define the systems, networks, and applications included in the test. They also identify off-limits areas or systems, helping both parties know what to expect from the testing process. This agreement holds the rules of engagement.
- Discuss legal and contractual implications: They then address legal considerations, such as potential liabilities and required authorizations for the testing process.
Want to see how these phases translate into measurable risk reduction?
[Book a Free Demo & Get a Sample Report]

What Makes Astra the Best VAPT Solution?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- The Astra Vulnerability Scanner runs 10,000+ tests to uncover every single vulnerability
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Penetration Testing Phase II: Reconnaissance
The pentester needs access to information about the target to simulate a cyber attack on an application or a network, and they gather this information in the reconnaissance stage.
Whether a hacker wants to target an entire network or a single web application, they need to know as much as possible about it. The scoping done in the previous phase helps the pentester narrow down the survey to increase the test’s efficiency.
Mapping is also integral to the recon operation while conducting a simulated attack on a web app. This step helps the attacker examine all the application pieces in one place and understand how it works.
There are two kinds of reconnaissance:
1. Active Reconnaissance
The pentesters engage directly with the target system to gather information in active recon. This is a more accurate approach to reconnaissance, although it is far more intrusive and direct since the intruder interacts with the system.
2. Passive Reconnaissance
In this method, the intruder does not interact with the target system and applies different passive strategies instead to gather information. They try to eavesdrop on network traffic and trace OS or internet footprinting.
Penetration Testing Phase III: Discovery
The discovery phase involves gathering information about the target network and identifying vulnerabilities. It can be divided into two parts:
1. Further Information Gathering
Pentesters gather more information about the target network using techniques like DNS interrogation, InterNIC queries, and network sniffing to uncover hostnames and IP information. During an internal test, the tester uncovers information like names and shares using NetBIOS enumeration and banner grabbing.
Want to see how these phases translate into measurable risk reduction?
[Book a Free Demo & Get a Sample Report]
2. Vulnerability Scanning
Pentesters scan the application or operating system for known vulnerabilities. They can perform automated scans, which test the system against a vulnerability database, or manual scans, which are more effective at finding new and hidden vulnerabilities.
Penetration Testing Phase IV: Vulnerability Analysis
During a security scan, several threat sources are discovered, which pentesters analyze to determine underlying vulnerabilities and prioritize them based on the risk they pose to the system. A consistent process is needed to examine the vulnerabilities in severity and risk, which VAPT providers do.
- CVSS: The Common Vulnerability Scoring System (CVSS) is a widely used semi-quantitative method for rating vulnerability severity. It assigns a numerical score to each vulnerability based on its severity. This score helps prioritize vulnerabilities for remediation, the final phase of penetration testing.
- Assessment Standards: Vulnerabilities are typically assessed according to various security and risk assessment standards, such as the Risk Assessment Guide for Information Technology Systems by the National Institute of Standards and Technology (NIST), ISO 27001, and HIPAA.
Penetration Testing Phase V: Exploitation and Post-Exploitation
The exploitation phase aims to establish access to a system in a simulated attack through the identified vulnerabilities. The pentester finds an entry point and then looks for assets that can be accessed.
The pentesters have to be very wary of the target’s functions while conducting this test and ensure that no workflow damage is done.
The Post-Exploitation Phase
After the pentester has exploited a vulnerability and identified an entry point to the system, the next job is to determine the value of that entry point. The questions to consider are:
- How much access does the entry point yield?
- How easy is it to maintain access?
- How much time may pass before the breach is spotted?
- What is the degree of harm that the vulnerability may cause?
The exploitation and post-exploitation phases help the tester gain access, locate sensitive data, identify communication channels, etc. They can also exploit the connection between different systems within the network and expand the breach.
The rules of engagement agreed upon in the pre-engagement stage determine how much a pentester may exploit a certain vulnerability.
Penetration Testing Phase VI: Reporting and Recommendations
All the previous penetration testing steps contribute to this phase, in which a VAPT is created and shared with the client. The pentesters provide detailed information about the vulnerabilities, such as:
- The description of the vulnerabilities.
- Ratings according to the Common Vulnerability Scoring System (CVSS).
- Severity and impact of vulnerability.
- Risk assessment report.
- Video POCs.
- Recommendations for fixing the vulnerabilities.
The quality of a VAPT report determines how quickly and efficiently you will reproduce and remove the vulnerabilities from your system.
Penetration Testing Phase VII: Remediation and Rescan
The VAPT report consists of step-by-step recommendations for fixing the vulnerabilities. Your developers can follow those recommendations to close the gaps in your application security.
An ideal remediation phase involves the following measures:
- Vulnerabilities are reported with detailed remediation steps.
- Security engineers provide video-based assistance.
- Developers get on a call to discuss the remediation steps when needed.
Once the vulnerabilities are fixed, the VAPT company should offer rescans to identify unattended security loopholes.
Recommend Reading: Top 10 Penetration Testing Companies for Compliance and Regulations
Timeline for the Phases of Pentesting
The first six penetration test phases, from conducting reconnaissance to producing a VAPT report, take approximately ten days to complete. This timeline may vary slightly depending on the scope of the test.
The remediation phase’s timeline depends on the efficiency with which your development team can work on the fixes recommended by the pentesting team. However, there is usually a stipulated time to avail of the free rescan a VAPT company offers.
Post-Pentest Rescans
After the vulnerabilities are found and fixed, the VAPT company recommends scheduled rescans of your application. If no more vulnerabilities are found in the rescans, the VAPT company could also provide a certificate to use for regulatory compliances such as ISO, SOC2, and HIPAA.
Conduct regular automated scans to keep your system’s security updated. You should also perform a scan every time you update your application or software to ensure the new versions do not contain vulnerabilities.
Top 3 Pentesting Tools
1. Astra Security
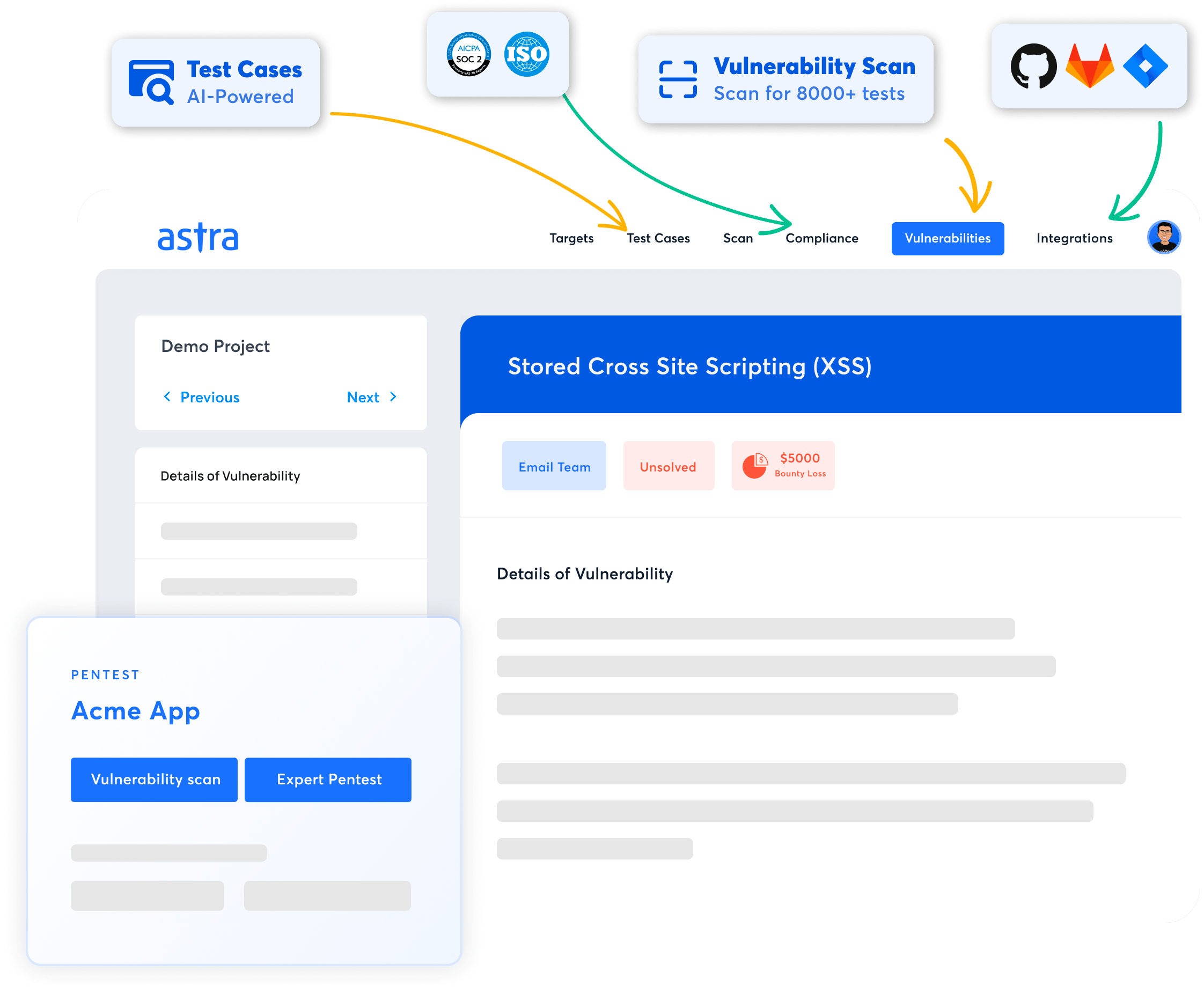
Key Features:
- Platform: Online
- Pentest Capability: Continuous automated scans with manual tests
- Accuracy: Zero false positives
- Compliance: PCI-DSS, HIPAA, ISO27001, and SOC2
- Expert Remediation: Yes
- Integration: Slack, Jira, GitHub, GitLab, Jenkins, and more
- Price: Starting at $1999/yr
The Astra Penetration Testing Services is a powerful pentesting suite that bridges AI-powered automated vulnerability scanning with deep, detailed manual pentesting. Our platform enables in-depth security assessments in compliance with OWASP TOP 10 and SANS 25 benchmarks, with our scanner conducting 9300+ tests.
While our vetted automated scans ensure zero false positives, our penetration tests conducted by security experts help reveal intricate vulnerabilities—like payment gateway hacks and business logic errors—that often slip through automated detection.
We provide features like scan-behind-login pages and reports that can be customized to the level of detail required for people from different hierarchies. After the testing process, clients are given several free rescans to validate the fix, along with a publicly verifiable Pentest certificate.

2. Kali Linux (Open-Source)
Key Features:
- Target: Online and physical systems, applications, and networks
- Pentest Capabilities: Unlimited Scans for vulnerability scanning, exploitation, privilege escalation, and post-exploitation
- Compliance: Not applicable since it’s open-source
- Integrations: 600+ pentesting tools like Nmap, Wireshark, John the Ripper
- Expert Remediation: No
- Accuracy: False positives are possible
- Price: Open-source OS
Kali Linux is an operating system designed for penetration testing and security auditing. Its vast platform, consisting of over 600 pre-installed tools, provides a complete solution for security professionals to conduct thorough vulnerability assessments.
From initial reconnaissance to post-exploitation analysis, Kali offers the necessary tools and functionalities to cover the entire spectrum of penetration testing tasks. This robust OS empowers security experts to delve deep into system vulnerabilities and exploit potential weaknesses.
While its extensive toolset and customization options make it a favorite among experienced professionals, it’s important to note that Kali Linux requires a solid understanding of Linux commands and a steep learning curve for beginners.
3. Burp Suite Professional
Key Features:
- Platform: Windows, macOS, Linux
- Pentest Capability: Automated and manual scans for web apps
- Accuracy: False positives possible
- Compliance: PCI-DSS, OWASP Top 10, HIPAA, and GDPR
- Expert Remediation: No
- Integration: Slack, Jira, Jenkins, GitLab, and more
- Price: $449/yr/user
Burp Suite Professional is a leading web application security testing platform globally recognized for its range of tools. They ensure rapid vulnerability discovery using both manual and automated testing techniques.
Burp Suite provides easy integration with external tools in an efficient testing environment. While usually sturdy, some users have also reported unstable crashes and socket connection errors with the tool.
Furthermore, although Burp Suite effectively identifies vulnerabilities, it does not highlight sensitive information leakage, such as personal and financial data exposures.
Final Thoughts
Penetration testing consists of seven important phases to help find and reduce the vulnerabilities in the system or network under consideration.
Security professionals can gain an in-depth understanding of an organization’s security posture by going through pre-engagement, reconnaissance, discovery, vulnerability analysis, exploitation, reporting, and remediation.
Manual testing is significant for finding complex vulnerabilities; however, automated scanning combined with manual testing increases the speed and efficiency of the process.
We have compared the top three pentesting tools that you can use to strengthen your overall security – Astra Security, Kali Linux, and Burp Suite Professional. Choose the right pentesting provider for your needs.
FAQs
What is the timeline for Penetration Testing?
Web app penetration testing takes 7-10 days. The vulnerabilities start showing up in Astra’s pen test dashboard on the third day so that you can get a head start on remediation. The timeline may vary depending on the scope of the pentest.
How much does Pentesting for a Web App cost?
Web app Pentesting costs $99 to $399 per month to perform web application penetration testing, depending on your choice of plan.
Do you get rescans after the vulnerabilities are fixed?
Yes, depending on your plan, you get 2-3 rescans. You can use the rescans within 30 days of the initial scan completion, even after a vulnerability is fixed.