A data security audit involves assessing an organization’s systems, processes, and controls to identify vulnerabilities and loopholes. This helps prevent costly and dangerous data breaches, which can expose highly sensitive, confidential, and personal information about individuals, companies, and their financials.
The average cost of a data breach in 2023 in the USA was $4.45 million. Conducting regular data security audits helps prevent such grave financial and reputational losses.
Data security audits are a preventive solution that is highly cost-effective when compared to dealing with the costly blowout of a data breach.
This article will detail the top tools for data security audits, provide a checklist, and explain the common risks and targets of a data breach.
Data Security Audit – 7-Point Checklist
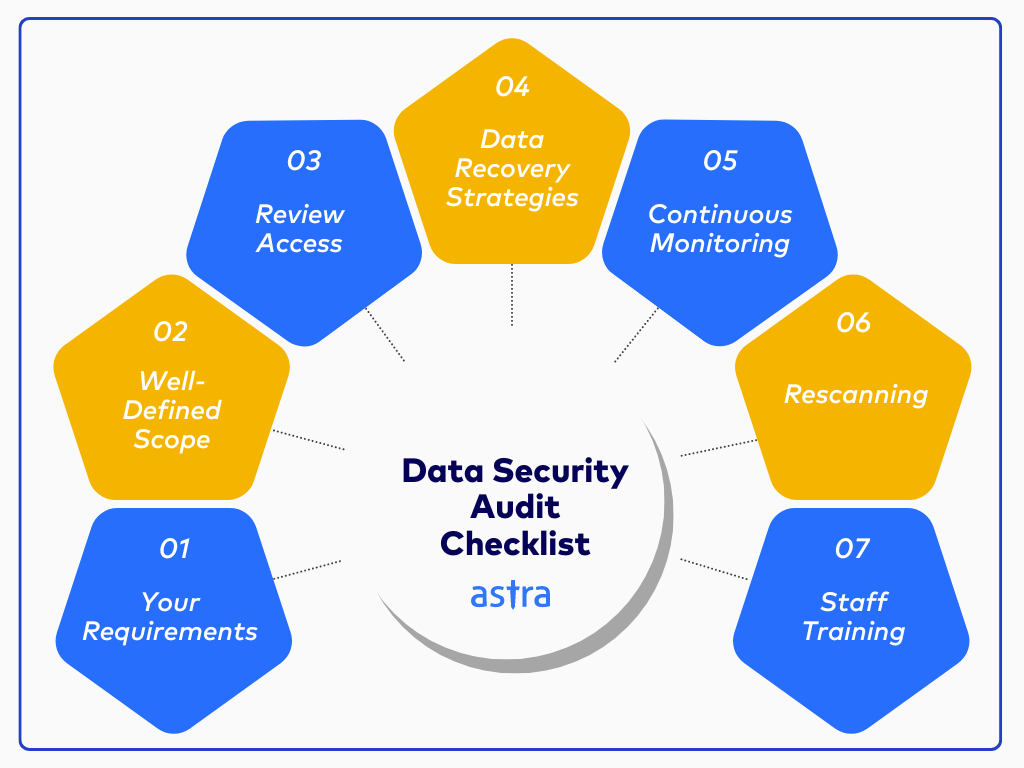
Here are some of the factors to consider and check before starting a data security audit:
1. Your Requirements
Setting your requirements from the audit with the security provider before the testing can begin is essential. This would help them create a clearly defined scope and plan for the necessary scans and tests.
Identifying your needs includes any specific goals (e.g., improving incident response), problem areas, and compliance regulations you want to achieve (e.g., GDPR, SOC2, HIPAA), etc.
2. Well-Defined Scope
Defining a scope includes creating an asset inventory listing all the systems, applications, databases, and networks within the audit scope and prioritizing them based on risk, sensitivity levels, and impact on the organization.
Within the scope, you should also establish clear audit boundaries by defining the start and end points of the audit to avoid scope creep and resource constraints.
3. Review Access
Access mismanagement is a significant concern that often leads to data theft and breaches. Therefore, reviewing different individuals’ access to confidential assets is crucial.
Ensure that multifactor authentication protects assets from authorized access. To streamline management and prevent privilege escalation, you should grant access based on roles rather than individual users.
4. Data Recovery Strategies
In the event of a data breach, theft, or a calamity that might affect data storage, the next step is to recover the data as soon as possible.
Data recovery strategies often involve continuous backups, which can reduce the time it takes to recover from a breach or calamity. Simulated disaster recovery exercises should be regularly conducted to prevent long-term data loss.
5. Continuous Monitoring
The tool should continuously monitor and scan assets to find hidden or new vulnerabilities that may have emerged. The security service provider should also implement intrusion detection and prevention systems to prevent unauthorized access.
Log management and analysis tools should be utilized to monitor system and application logs for anomalies and security incidents. Automated vulnerability scanning with every feature update should be incorporated into your CI/CD pipeline for quick and seamless patching.
6. Rescanning
Rescanning refers to scanning assets after the remediation process is completed. To ensure ongoing protection, prioritize high-risk assets and focus on critical systems and data.
Rescanning helps identify any further issues with a target’s security and analyze the effectiveness of new security patches.
7. Staff Training
Yet another crucial factor is that all staff must undergo awareness training during a security audit to ensure they’re trained to avoid phishing threats and social engineering tactics.
Your organization should conduct regular security training sessions and inform employees about emerging threats and security updates. Employees should also be encouraged to follow policies that instill habits like locking their computers when they leave their workplaces.

What Makes Astra the Best VAPT Solution?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- The Astra Vulnerability Scanner runs 10,000+ tests to uncover every single vulnerability
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Data Security Audit Inclusions
1. Inward Data Flow Audit
Scrutinizing the data flowing into your infrastructure is vital to maintaining security. This data ranges from user inputs to data from external APIs and partners, among other sources, and is constantly flowing into your technical architecture.
- Data Validation: Implement data validation rules at the application server so that data received from the client is guaranteed to be in the expected formats, patterns and within known ranges. This, in turn, helps prevent data manipulation and injection attacks.
- Sanitization: Sanitize all user-generated content to remove harmful characters or code that could exploit vulnerabilities.
- API Security: Every API request should be authenticated and authorized to prevent unauthorized access and data leakage.
- Third-Party Risk Assessment: Controls within third-party providers that impact security practices should be assessed to help combat risks associated with data shared through external APIs or integrations.
- Anomaly Detection: Advanced analytics should be applied to detect abnormal patterns in data or behaviors that can indicate threats.
2. Outward Data Flow Audit
Just as monitoring incoming data is important, keeping track of data leaving your organization is also essential. It would be best to exercise control over shared sensitive data, such as personally identifiable information. If such data needs to be transferred, stringent policies for its encryption should be set in place.
- Data Classification: Set data sensitivity levels to determine appropriate protection measures tailored to the data.
- Data Loss Prevention: Implementing a DLP solution allows organizations to monitor and prevent unauthorized data transfers.
- Encryption: Encrypt all sensitive data, both at rest and in transit, to protect it from unauthorized access.
- Access Controls: Ensure tight access control over who can view, modify, and export data is developed.
3. Geographical Data Flow Audit
Mapping your data journey across geographies is crucial to understanding the intricacies of worldwide data regulations. Countries have different data privacy laws.
For instance, storing US healthcare data in foreign countries could violate HIPAA. Knowing where your data resides at any given time will help you ensure adherence to local and international laws, lowering potential risks.
- Data Mapping: Create a detailed map of where data is stored, processed, and transferred.
- Regulatory Compliance & Enforcement: Ensure that your data is stored according to data residency and transfer requirements in multiple jurisdictions.
- Data Sovereignty: Evaluate the risk of probable data breaches globally and take appropriate measures to increase overall security.
- Incident Response: Develop region-specific incident response plans to address data breaches.
- Vendor Management: Evaluate the vendors’ practices for handling data in different geographical areas.
4 Best Data Security Practices
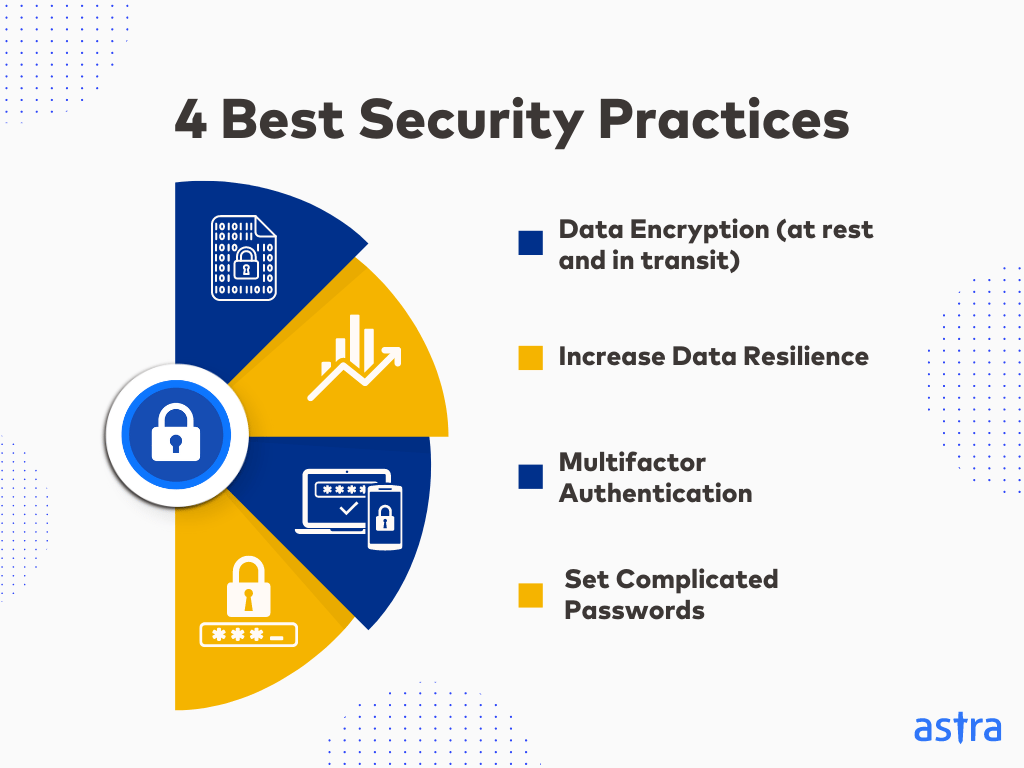
1. Data Encryption – At Rest and In Transit
When data is in transit, it can be encrypted using Transport Layer Security (TLS). Another data protection practice is exercising control over encryption keys so others cannot decrypt customer data.
To ensure data security is at rest, a hierarchy of security levels, encryption on both ends and regular audits are recommended.
2. Increase Data Resilience
Increase data resilience through backups in different locations and implementing disaster recovery plans. These plans list the steps to take during a disaster, a breach, or other security incidents.
It generally contains information such as procedures for restoring systems, which can help minimize the impact and ensure that your organization can recover promptly.
3. Multifactor Authentication
Multi-factor authentication (2FA) adds a layer of security to prevent unauthorized access. Under 2FA, a user has to provide two pieces of evidence to verify their identity.
Multi-factor authentication can help prevent unauthorized access even if a user’s password is compromised.
4. Set Complicated Passwords
Set passwords that are difficult to guess or brute-force through and change them regularly to avoid password-related data risks. This should also be enforced for all your users and employees alike.
Ensure that passwords are not written down on workstations that are accessible to anyone. If you are using a password manager service, verify its security.
Common Risks To Data Security
1. Tampering
When data in transit or at rest isn’t adequately protected, hackers and impersonators can modify it by adding to or deleting information.
A simple example is modifying a transaction amount from $10 to $100 through unauthorized interception of data in transit.
2. Theft
Data stored in an unsecured location, with adequate protection, like encryption, or if there are sufficient protective measures for the network through which the transmission is taking place, can lead to data theft.
A multi-layered security approach, including encryption, access controls, employee training, network security, and regular vulnerability assessments, can prevent this.
3. Unauthorized Access
Unauthorized access to data through improperly placed passwords, implementation of weak passwords, or having access that wasn’t revoked on time are ways a hacker can gain unauthorized access.
Strong authentication and authorization methods, access controls, regular monitoring, and incident response planning can prevent this.
4. Falsification
Hackers falsifying information gathered from the theft of identities is a prime example of falsification. For identification, credit card numbers and other personal information are used to gain authorized access to a person with malicious intent.
Astra Pentest is built by the team of experts that helped secure Microsoft, Adobe, Facebook, and Buffer

Astra Security – Data Security Audit Provider

Key Features:
- Platform: SaaS
- Pentest Capabilities: Continuous automated scans with 10,000+ tests and manual pentests
- Accuracy: Zero false positives (with vetted scans)
- Compliance Scanning: OWASP, PCI-DSS, HIPAA, ISO27001, and SOC2
- Publicly Verifiable Pentest Certification: Yes
- Workflow Integration: Slack, JIRA, GitHub, GitLab, Jenkins, and more
- Price: Starting at $1999/yr
Astra Pentest offers data security audits that focus on finding vulnerabilities. We conduct penetration testing and in-depth vulnerability scans that help businesses understand their security posture and prioritize fixes.
Our vulnerability scanner tests for 10,000+ test cases based on the OWASP 10, SANS 25, and emerging vulnerabilities that are updated fortnightly.
With user-friendly dashboards, zero false positives (via vetted scans), detailed reports, and compliance-specific scans, we provide actionable insights and support organizations in achieving and maintaining security standards.
At Astra, we go beyond vulnerability detection by offering remediation assistance and a publicly verifiable pentest certificate that you can use as proof of security excellence.
Steps In A Data Security Audit
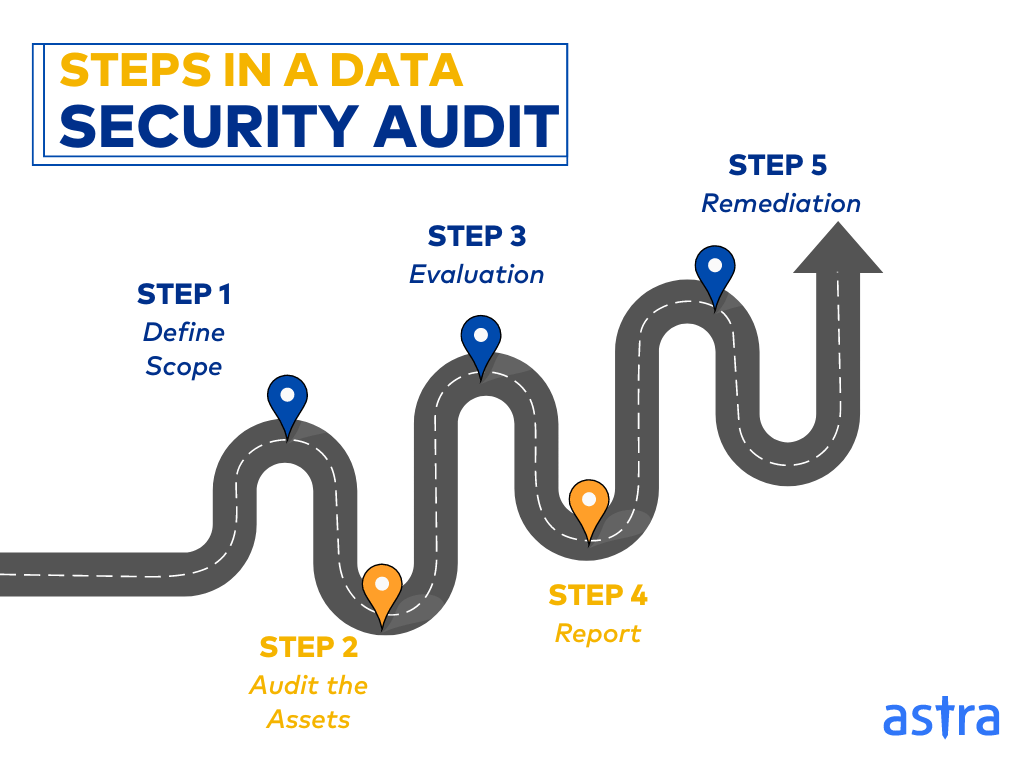
1. Scope
This is the initial phase of a security audit in which the scope is agreed upon by the pentesters and the customer, detailing the number of assets to be audited, the rules of the attack, and a summary of the customer’s needs.
Proper scoping is required for a thorough data security audit to avoid scope creep and future legal troubles. This step also helps set the expectations for the audit for both parties involved.
2. Audit
This is the second phase of the data security audit. The assets are scanned and audited for any vulnerabilities or areas of non-compliance that endanger data safety using automated security audit tools and pentesting.
This is also the step in which compliance assessment, access control review, incident response plan evaluation, and data classification and protection occur.
3. Evaluation
The vulnerabilities discovered during the data security audit are evaluated and categorized based on the severity of the threat. This risk score helps you prioritize the remediation efforts.
This is usually done according to CVSS (Common Vulnerability Scoring System) scores, in which 8-10 represents critical vulnerabilities, 5-7 medium-level vulnerabilities, and 1- 4 low-level vulnerabilities.
4. Report
Once the data security audit is completed, a detailed audit report is generated to help the customer understand the measures taken, vulnerabilities found, remediation measures that can be opted for, and help with good security documentation.
It would help to look for a data security audit provider that offers customizable reports that can be altered according to the reader’s required information, such as a report with bird’s-eye-level information for a CTO.
5. Remediation
The data audit report will contain remediation measures for the vulnerabilities found in your systems. These vulnerabilities must be remediated and patched based on their criticality.
Some audit providers also assist your security team with the remediation process, making it faster and more convenient while using fewer resources.
What Are The Common Data Breach Targets?
The most common information that is targetted during the theft or breach of data are:
- Personal Identifiable Information (PII): This refers to personal details like date of birth, government-issued identification numbers like social security numbers, contact information, and more.
- Financial Details: This includes susceptible information such as credit card numbers, account details, investment details, and confidential PINs.
- Health Information: This refers to individuals’ personal health information stored in hospitals and other healthcare institutions, such as pharmaceuticals. It can also include prescriptions and treatment details.
- Legal Data: The confidentiality information and documents that relate to court cases, regulatory rulings, business acquisitions, propriety information like constituents for pharmaceuticals, and more.
Make your SaaS Platform the safest place on the Internet.
With our detailed and specially
curated SaaS security checklist.

Final Thoughts
Data security is of the utmost importance in today’s rapidly-paced digital world. By identifying vulnerabilities and compliance gaps, these audits help prevent costly data breaches, which can devastate reputations and finances.
A well-structured audit, comprising data flow analysis, penetration testing, and compliance assessments, helps assess an organization’s security.
Continuous monitoring, staff training, and incident response planning are crucial for maintaining a strong security stance. Tools like Astra Pentest can streamline the audit process with vulnerability scanning, penetration testing, and compliance checks.
A successful data security audit is a collaborative effort between the organization and the audit provider. Organizations can build a resilient security framework that safeguards sensitive information and protects their bottom line by working together.
FAQs
1. What is a data security audit?
A data security audit systematically evaluates your assets, including websites, applications, and networks, to ensure that the company’s and its customers’ information and data are stored and transmitted safely and with industry-standard security.
2. What are the different types of security audits?
The different types of security audits include penetration tests, vulnerability assessments, compliance audits, and risk assessments. Pentests involve manual hacker-style simulations, while vulnerability assessments are usually automated.
3. How is a data security audit done?
A data security audit starts with establishing a thorough scope based on which an audit is carried out. The risks identified are evaluated, and a data security audit report is generated, based on which remediation is carried out.