A security audit is a complete evaluation of an organization’s information systems. This includes scanning networks, physical devices, applications, software, and firewalls and evaluating employee safety training.
Given the alarming surge in data breaches with publicly disclosed incidents exceeding 4,100 in 2025 alone, i.e., roughly a 75 % year-over-year increase organizations should prioritize robust security strategies to reduce risk and exposure.
Promptly employing security audit tools is the key to staying safe and avoiding becoming a statistic in a cybersecurity attack.
Here are some of the top cybersecurity audit tools to consider:
- Astra Security
- Sprinto
- Qualys
- Nessus
- Symantec
- Palo Alto Networks
- Check Point
Top 3 Cybersecurity Audit Tools Comparison
| Features | Astra Security | Palo Alto | Qualys |
|---|---|---|---|
| Platform | SaaS | SaaS | SaaS |
| Capabilities | Continuous automated scans with 9300+ tests, manual pentests | Threat Prevention, IDP, continuous monitoring, and remediation guidance | Automated monitoring and threat detection with remediation |
| Accuracy | Zero false positives | False positives possible | False positives possible |
| Compliance | OWASP, PCI-DSS, HIPAA, ISO27001, SOC2, and more. | HIPAA, PCI-DSS, and GDPR | PCI-DSS, HIPAA, GDPR |
| Workflow Integrations | Slack, JIRA, GitHub, GitLab, Jenkins, etc. | Cisco, AWS, Slack, and more | IBM, Splunk, Cisco, and more |
| Price | Starting at $1,999/yr | Available on quote | Available on quote (Trial starts at $500/month) |
| Used by Customers Like | Go Daddy, Ford, UN, DLF | Accenture, Salesforce, Dish | Ancestry, CapitolOne, Cisco |
Top 7 Security Audit Tools
1. Astra Security [Get Started]
Key Features:
- Platform: SaaS
- Pentest Capabilities: Continuous automated scans with 10,000+ tests and manual pentests
- Accuracy: Zero false positives (with vetted scans)
- Compliance Scanning: OWASP, PCI-DSS, HIPAA, ISO27001, and SOC2
- Publicly Verifiable Pentest Certification: Yes
- Workflow Integration: Slack, JIRA, GitHub, GitLab, Jenkins, and more
- Price: Starting at $1999/yr
Best for: Organizations seeking a comprehensive, continuous security audit with zero false positives, combining automated scans with manual pentesting and expert remediation support.
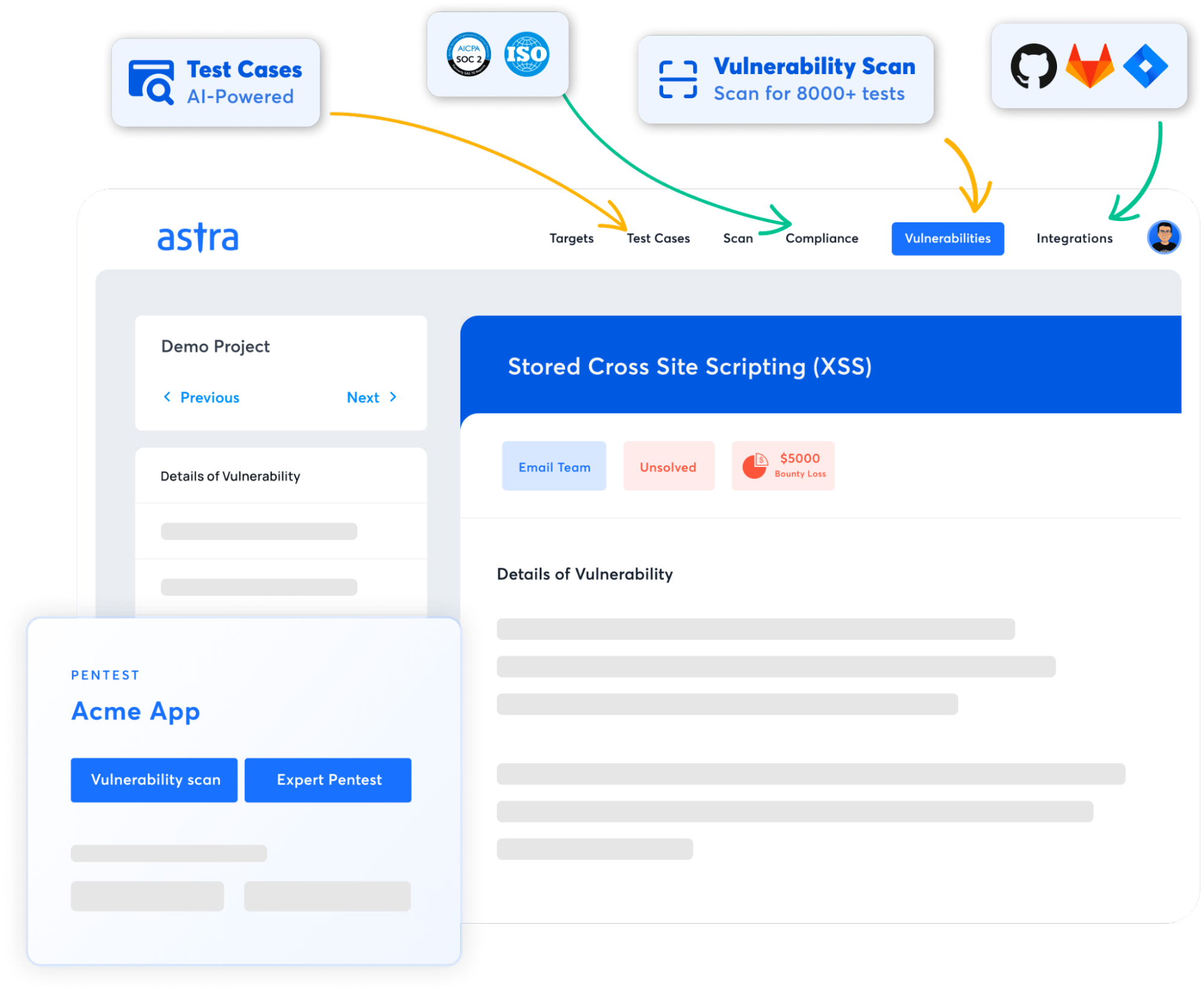
Astra Security provides comprehensive security audits with the assurance of zero false positives in vetted scans to find all vulnerabilities across your systems—networks, web applications, mobile applications, and APIs.
Our vulnerability scanner can find system loopholes using NIST and OWASP methodologies, testing for 10,000+ test cases. The list of tests is updated fortnightly to include emerging vulnerabilities, known CVEs, OWASP Top 10, and SANS 25.
Astra’s user-friendly dashboard displays the vulnerabilities found in real-time with the severity scores and allows collaboration with the target’s development team for a smoother patching process.
We can help you achieve and maintain compliance with our specific scans for regulatory standards like PCI-DSS, SOC 2, GDPR, ISO 27001, and HIPAA. Our publicly verifiable certificate can be displayed on your website to showcase its reliability and security-conscious nature.
Pros:
- Detailed reports that can be customized to the level of detail required.
- Remediation assistance and customer support.
- Easy to use and navigate.
- Pocket-friendly.
- Assures zero false positives with vetted scans.
Limitations:
- Does not provide free trials but offers a $7/week trial.
Astra Security G2 Review:
How to Choose the Right Security Audit Tool
Selecting the right security audit tool is crucial for protecting your organization’s assets, meeting compliance requirements, and streamlining remediation. Here are the key factors to consider before making your choice:
- Coverage & Capabilities: Ensure the tool addresses all your audit needs, including networks, web apps, cloud, endpoints, and APIs, and isn’t limited to a single asset type.
- Accuracy & Reliability: Look for solutions with minimal false positives and a mix of automated scanning and manual verification for precise, actionable results.
- Compliance Support: If you need to meet standards such as SOC 2, PCI-DSS, HIPAA, ISO 27001, or GDPR, select a tool with built-in compliance checks and reporting capabilities.
- Ease of Integration: The right tool should fit seamlessly into your existing workflows, whether that’s CI/CD pipelines, ticketing systems like JIRA, or DevOps tools.
- Remediation Assistance: Prioritize solutions that go beyond detection and provide expert guidance, proof-of-concept fixes, and re-testing support.
- Scalability: As your infrastructure grows, your tool should scale effortlessly to cover an increasing number of assets, users, and new technologies.
- User Experience & Support: An intuitive dashboard, clear reporting, and responsive customer support can dramatically reduce the learning curve and time to value.
Pro Tip: Don’t just compare features, compare outcomes. The best tool is the one that consistently identifies real security risks and empowers your team to fix them quickly.
2. Sprinto
Key Features:
- Platform: SaaS-based compliance automation platform
- Core Functionality: Automates compliance and audit readiness
- Compliance Scanning: SOC2, GDPR, ISO 27001, HIPAA and more
- Workflow Integration: Slack, AWS, GCP, Azure
- Pricing: Available on quote
Best for: Cloud-hosted businesses looking to automate compliance and audit readiness quickly, with minimal manual effort and streamlined SOC 2 preparation.
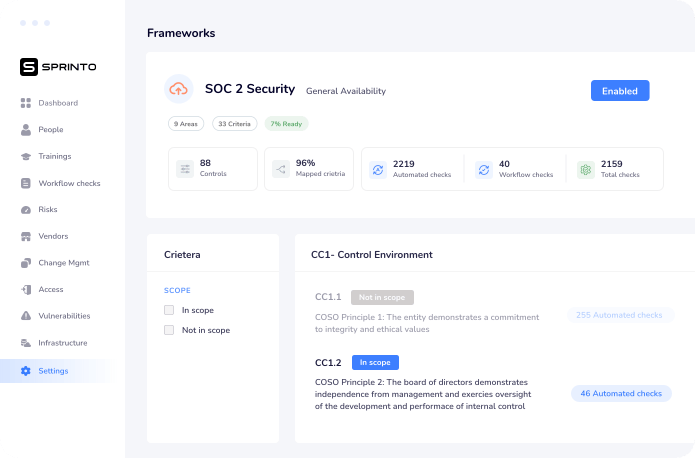
Sprinto’s intelligent automation speeds up security auditing, which can be completed in weeks. Some of its main features include a compliance checklist and systems integration.
With Sprinto’s automation-driven SOC 2 compliance program, cloud-hosted businesses can quickly, accurately, and efficiently prepare for audits. It automates all the tedious work associated with achieving compliance before you meet with auditors.
Pros:
- Provides zero-touch audits.
- Automated evidence collection.
- Conducts live sessions to construct better security plans.
Limitations:
- Can be a bit difficult to navigate and has a learning curve.
Sprinto G2 Review:
3. Qualys
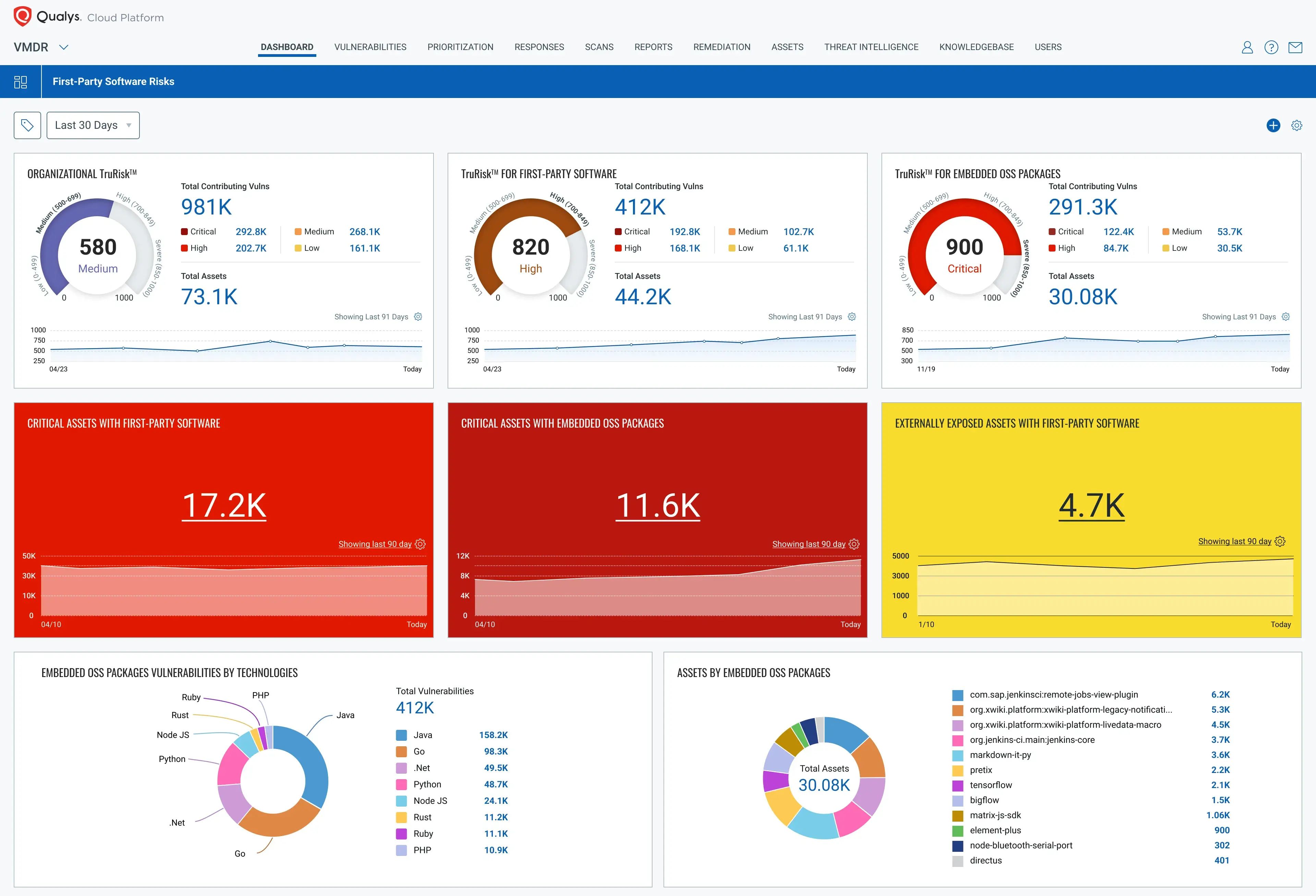
Key Features
- Platform: Cloud-based security and compliance platform
- Core Functionality: Vulnerability management, detection, and response
- Compliance Scanning: PCI DSS 4.0, GDPR, HIPAA, and more
- Pricing: Available on quote
Best for: Enterprises needing scalable, cloud-based vulnerability management and continuous threat detection across hybrid IT infrastructures.
Qualys is a cloud security audit tool for assessing cloud assets, vulnerabilities, and compliance status. Its extensive database of known CVEs is constantly updated and known for its scalability and accuracy.
With its VMDR and Threat Protection, Qualys protects hybrid IT infrastructure with a single cloud platform that continually finds, levels, and fixes vulnerabilities on all devices.
Pros:
- A highly scalable security audit solution.
- Provides vulnerability management, detection, and response.
- Accurate reporting that is easy to follow.
Limitations:
- Can be slow when scanning.
- Difficult to navigate for beginners.
- Slightly on the expensive end.
Qualys G2 Review:
4. Nessus
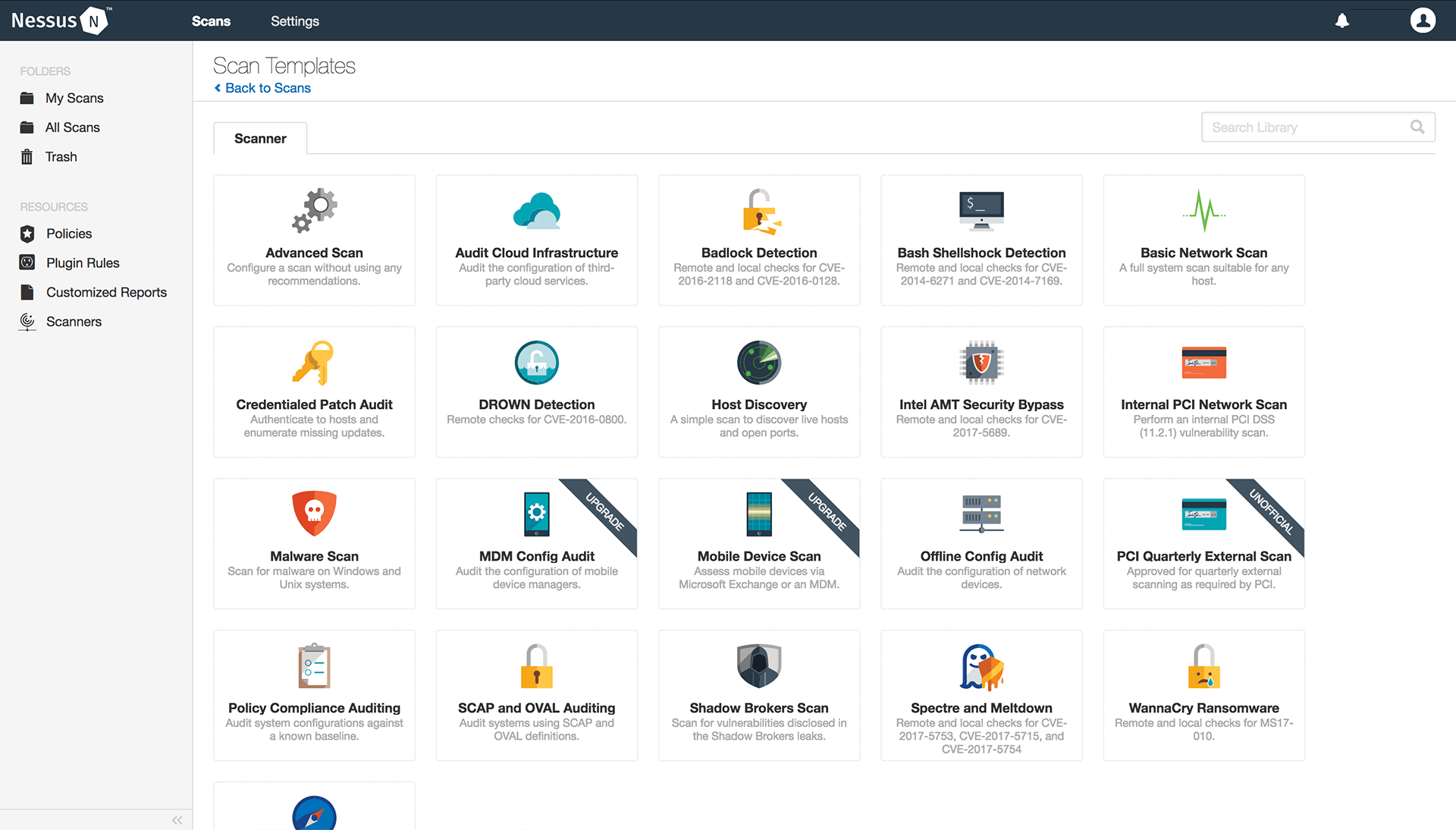
Key Features:
- Platform: SaaS
- Core Functionality: Vulnerability scanning and assessment
- Workflow Integration: AWS, GCP, Jira, Azure, and other Tenable product
- Pricing: Nessus Pro starts at $4,700/year
Best for: Security teams requiring in-depth point-in-time vulnerability scanning and assessment with detailed patching guidance.
Nessus is a web application security audit tool released by Tenable. It helps with point-in-time analysis of security systems to find vulnerabilities that may be plaguing them.
They also provide a detailed reporting feature that details the vulnerabilities found and the appropriate patches for them.
Pros:
- Helps find missing patches that are critical to maintaining security.
- Point-in-time analysis of security system.
- Helps achieve compliance with the scans.
Limitations:
- Advanced technical support is only available upon additional payment.
- Takes time to complete scans.
- It can be an expensive solution.
Nessus Review G2:
5. Symantec
Key Features:
- Platform: Hybrid (cloud and on-premises)
- Core Functionality: Endpoint protection, threat detection, data loss prevention, and access control
- Pricing: Starts at $39/year
Best for: Organizations prioritizing endpoint protection and threat detection with integrated malware defense and data loss prevention.
Accenture just acquired Symantec’s cyber security software, which protects networks, data, and devices against malware and viruses.
Symantec offers cloud workload protection, which provides automated security measures, including cloud security audits, for your cloud providers and customers. In addition to security audits, it also provides anti-malware, intrusion prevention, and more.
Pros:
- Provides end-point protection and threat detection.
- Has malware detection capabilities with the capacity for immediate remediation.
- Can be integrated within the CI/CD pipeline.
Limitations:
- A pricey solution that may not be feasible for small to medium-sized companies.
- Could provide better integration possibilities.
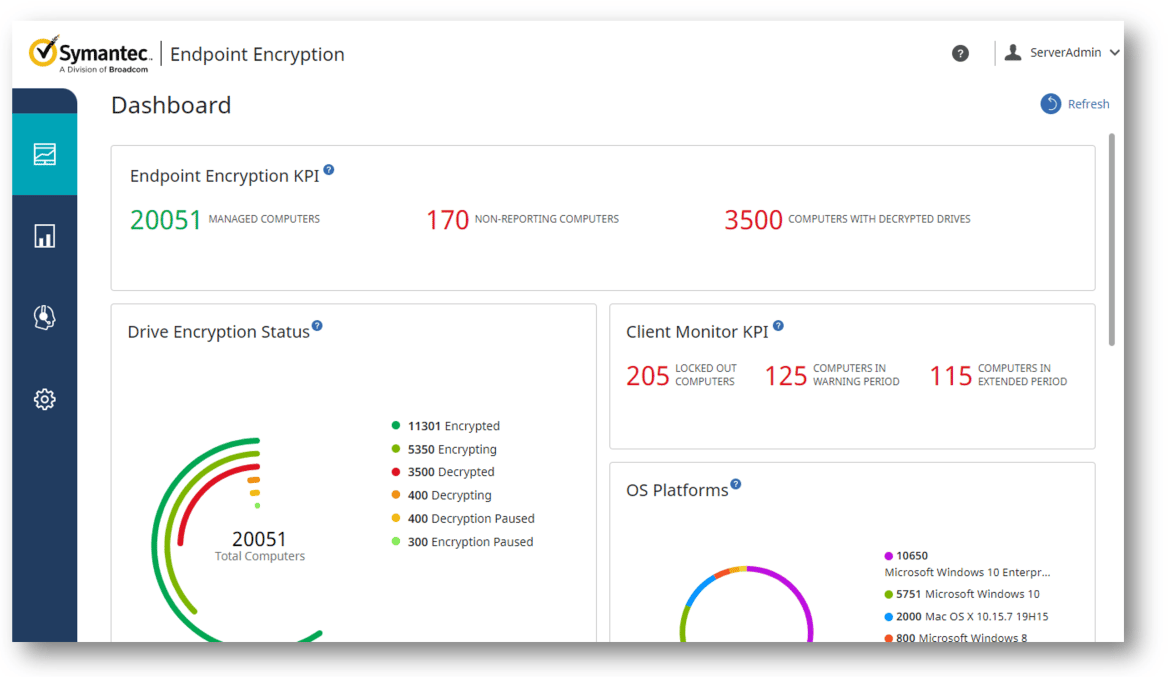
Symantec G2 Review:
6. Palo Alto Networks
Key Features:
- Platform: Cloud-delivered security platform
- Core Functionality: Next-generation firewall, threat prevention, cloud security
Best for: Enterprises focusing on threat prevention and advanced firewall capabilities alongside AI-driven cloud and network security.
Palo Alto Networks is a leading cybersecurity solution provider focusing more on prevention than detection. Its products protect networks, applications, and cloud environments.
Their new-age firewalls guard your network, Prisma Cloud safeguards cloud apps, and Cortex XDR uses artificial intelligence (AI) to detect and neutralize threats in all directions—from the cloud to your network.
Pros:
- Strong focus on prevention and threat detection.
- Advanced threat intelligence and analytics.
- Strong reputation for innovation and product development,
Limitations:
- Can be complex to manage and configure.
- Pricing can be higher compared to some competitors.
- Focus on prevention might require additional tools for incident response.
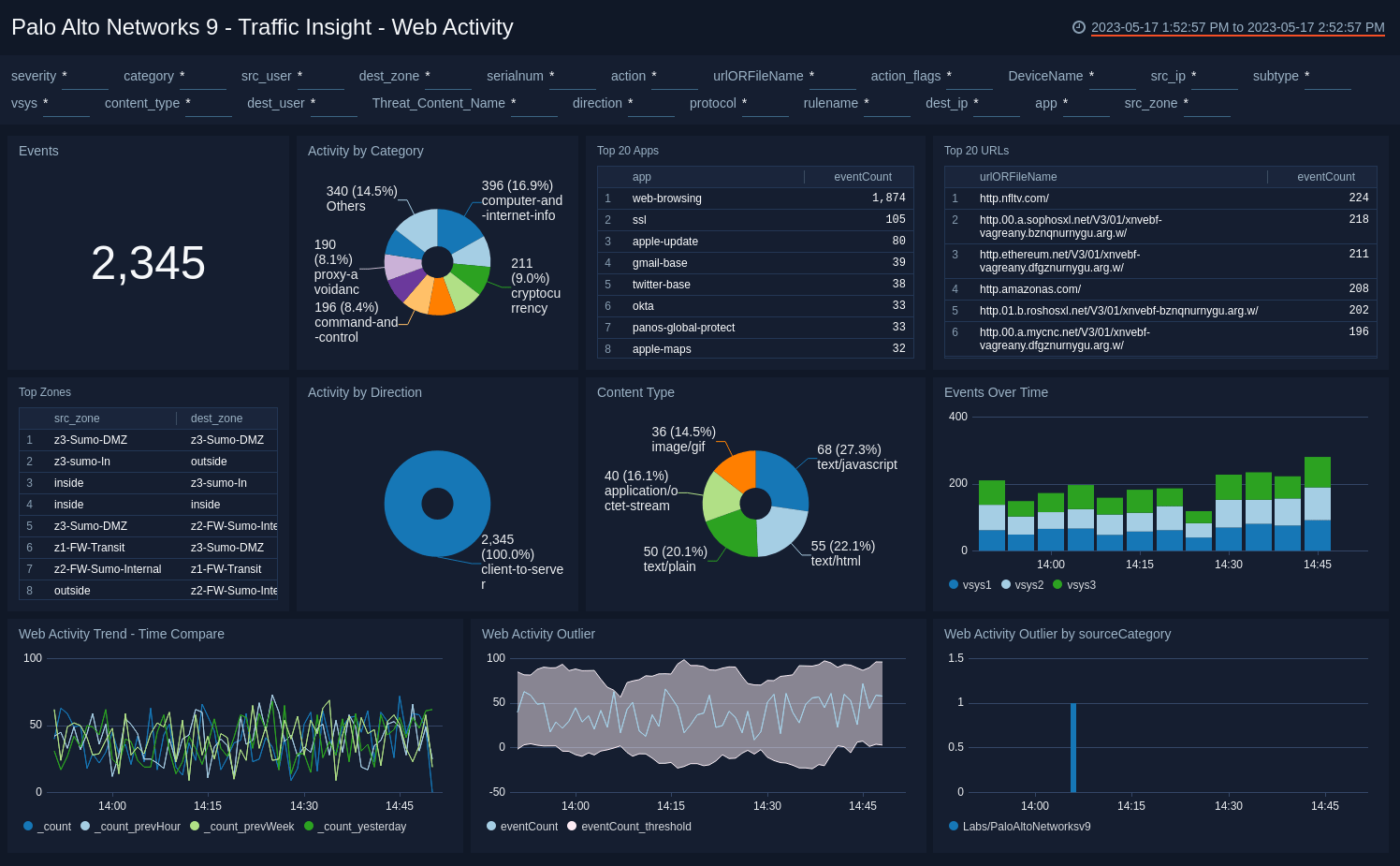
Palo Alto Networks G2 Review:
7. Check Point
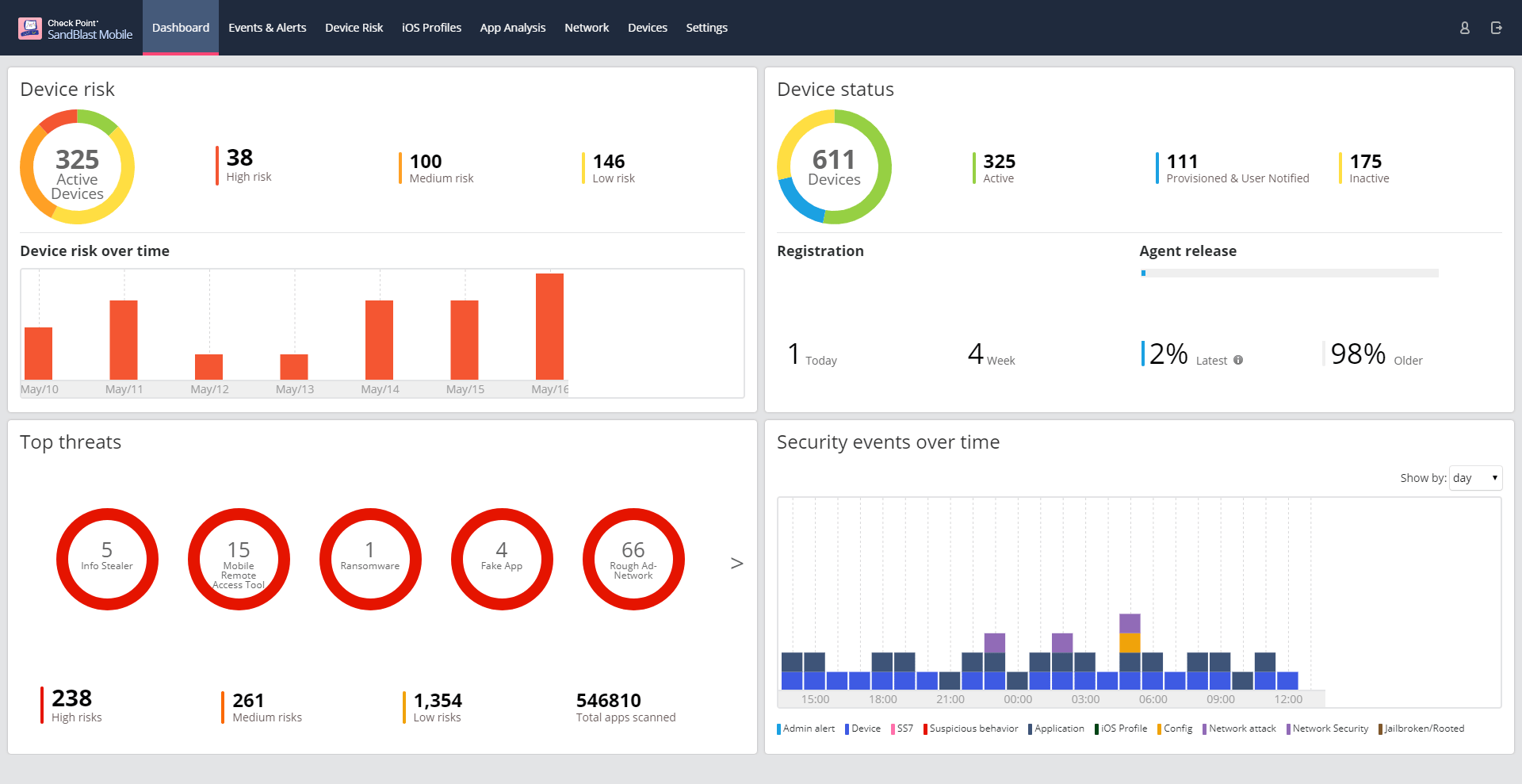
Key Features:
- Platform: Hybrid (cloud and on-premises)
- Core Functionality: Network security, endpoint protection, cloud security
Best for: Companies needing a broad, integrated security portfolio addressing network, endpoint, and cloud protections with strong global support.
Among cybersecurity companies, Check Point Software Technologies is an expert that offers customers an extensive selection of security solutions, from cloud security to network security and endpoint protection.
Check Point prioritizes prevention and threat detection while providing complete security to organizations of all sizes.
Pros:
- Strong focus on network security with advanced firewall capabilities
- Vast product portfolio addressing various security needs
- Global presence and strong customer support
Limitations:
- Can be perceived as a more traditional security vendor compared to newer competitors
- Product portfolio can be complex to manage
- Pricing can be competitive but might vary based on specific requirements
Check Point G2 Review:
What Features Should You Look for in a Security Audit Tool?
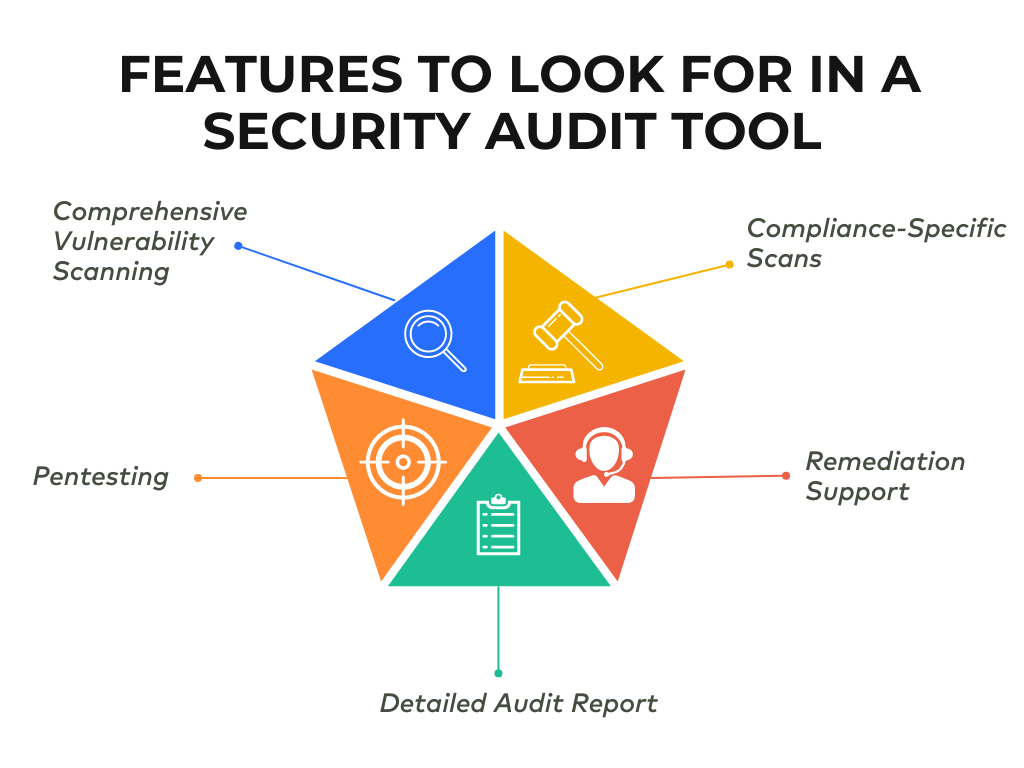
1. Comprehensive Vulnerability Scanning
The tool should be able to continuously monitor and scan assets to find hidden or new vulnerabilities. Using automated scanning often, you can detect vulnerabilities that arise post-pentest and with every software update or feature addition.
A scanner integrated into your CI/CD pipeline would make it convenient to conduct continuous tests.
2. Pentesting
The security audit provider should be able to conduct continuous pentests to assess an organization’s security posture regularly and find vulnerabilities that quick scans could’ve missed.
Based on the target organization’s initial scope and needs, it should deploy its automated scanner combined with manual pentesting efforts to find its security flaws.
3. Detailed Audit Report
Detailed audit reports are an essential feature of security audit tools as they help customers make fixes based on risk priority. It should also include detailed remediation steps for patching each vulnerability within the report and their CVSS scores.
It would also be helpful to have an audit provider that offers customizable reports tailored to the level of technicality the reader requires. For example, this would be different for a CTO vs. a security engineer.
4. Remediation Support
They should be able to provide expert assistance with vulnerability remediation for your organization’s security.
This includes supplying POC videos, immediate query clearance, detailed steps within the security audit report, and prioritized remediation plans based on risk assessment.
5. Compliance-Specific Scan
Compliance-specific scans can help your organization achieve and maintain the compliances it requires in a completely hassle-free manner. It conducts compliance checks for GDPR, HIPAA, PCI-DSS, ISO 27001, and SOC2.
A dashboard devoted to compliance can help you choose the compliance you want to scan for based on which the scan detects any and every non-compliance that needs to be remedied.
Types Of Security Audit
1. Network Security Audit
Network security is an integral part of overall IT security. Employing network security audit tools to conduct audits regularly is very important, as networks usually see high data transfer and storage activity.
This involves examining devices like routers, switches, firewalls, and servers for vulnerabilities, misconfigurations, and unauthorized access points. Organizations can protect sensitive data from breaches, unauthorized access, and denial-of-service (DoS) attacks by identifying weaknesses in network security.
2. Web Application Security Audit
Web security audit tools help identify vulnerabilities and loopholes in web applications before they can be exploited. This staves off various threats, like DDoS attacks, and can even help find business logic errors.
These audits examine the application’s code, infrastructure, and functionality to find weaknesses such as SQL injection, cross-site scripting (XSS), and other common vulnerabilities.
3. Cloud Security Audit
Cloud security audit tools scan cloud servers, where copious amounts of data and applications are stored and transmitted. Cloud server providers should conduct regular audits to ensure all vulnerabilities are found and fixed.
These audits assess cloud environments’ configuration, access controls, data protection measures, and overall security posture.
Essential Steps In A Security Audit
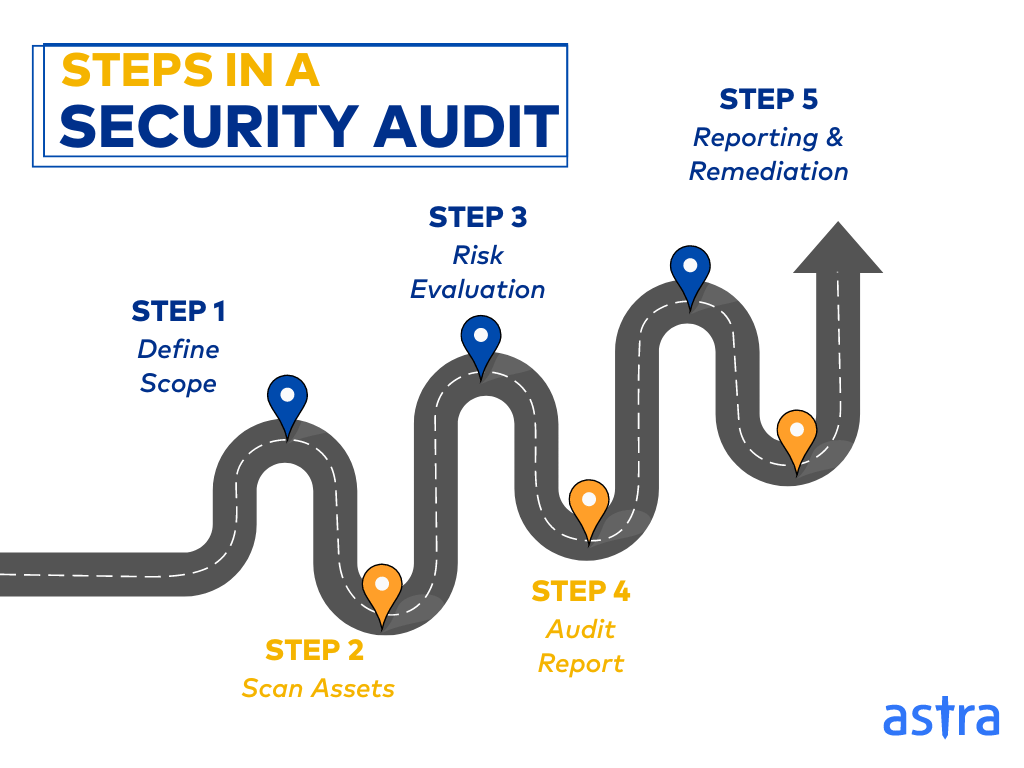
1. Define Scope
This is the initial phase of the audit, where the security audit provider and the customer agree upon a scope detailing the number of assets to be audited, the rules of attack, and the understanding of the client’s needs. Proper scoping is required for a thorough security audit to avoid scope creep and legal troubles.
2. Scan Assets
This is the second phase of a security audit, where the organization’s assets are scanned for any vulnerabilities or areas of non-compliance using automated security audit tools. Open-source and freely available security audit tools can be used for this task.
3. Risk Evaluation
The vulnerabilities discovered are categorized based on the threat’s severity. This is usually based on CVSS (Common Vulnerability Scoring System) scores, in which 8-10 represents critical vulnerabilities, 5-7 medium-level vulnerabilities, and 1- 4 low-level vulnerabilities.
4. Audit Report
Once the security audit provider completes the security audit, it generates a detailed audit report for the customers to help them understand the measures taken, vulnerabilities found, remediation measures that can be opted and help with good documentation of security.
5. Remediation
The audit report will contain remediation measures for the vulnerabilities found on them. These vulnerabilities are to be remediated and patched based on criticality; the ones with high criticality should be patched immediately.
Final Thoughts
Security audits are in increasing demand from most compliance departments, and customers are beginning to see value in maintaining high levels of security. They help assure the quality of your security system, increase trust in your brand, and also help achieve compliance.
These audits require systematically assessing networks, systems, and applications to identify vulnerabilities and establish countermeasures for securing sensitive data.
The rising incidences of data breaches solidify the importance of strong security measures. This article discusses some critical features to consider in a security audit tool, including penetration testing, automated scanning, and remediation support.
We have compared and contrasted the top seven security audit tools so you can evaluate your needs and make the right choice. Our top three picks would be Astra Security, Palo Alto Networks, and Qualys. Ultimately, choosing the right security audit tool depends on the customer’s budget, organizational size, industry, and specific security requirements.
FAQs
1. What type of tools are used in a security audit?
Different tools, including vulnerability scanners, penetration testing tools, network scanning tools, database auditing tools, compliance auditing tools, and log analysis tools, are used to gain an in-depth analysis of a security system during a security audit.
2. What are the two types of security audits?
Security audits are of two types:
1. Internal audits are security audits conducted internally within an organization using its auditing department and resources.
2. An auditor is hired to conduct a thorough audit of one’s security for external audits.
3. What are some of the open source tools available for security audits?
Some of the open-source tools for carrying out security audits are ZAP, a web app security scanner, SQLmap, which checks for SQL injections, OpenVAS, a vulnerability scanner, and Metasploit, which is a pentesting framework.
4. What are some best practices for network security auditing?
Effective network security auditing involves periodic risk-based reviews, a mix of manual and automated processes using relevant tools, continuous monitoring with fast remediation, employee training, and consideration of third-party audits. These practices will equip organizations to identify and address network vulnerabilities quickly.
5. What is auditing in cybersecurity?
Cybersecurity auditing is the structured examination of an organization’s IT infrastructure to identify and assess security risks. This consists of assessing systems, networks, applications, and security controls to determine whether they protect sensitive information and are in compliance with regulations.