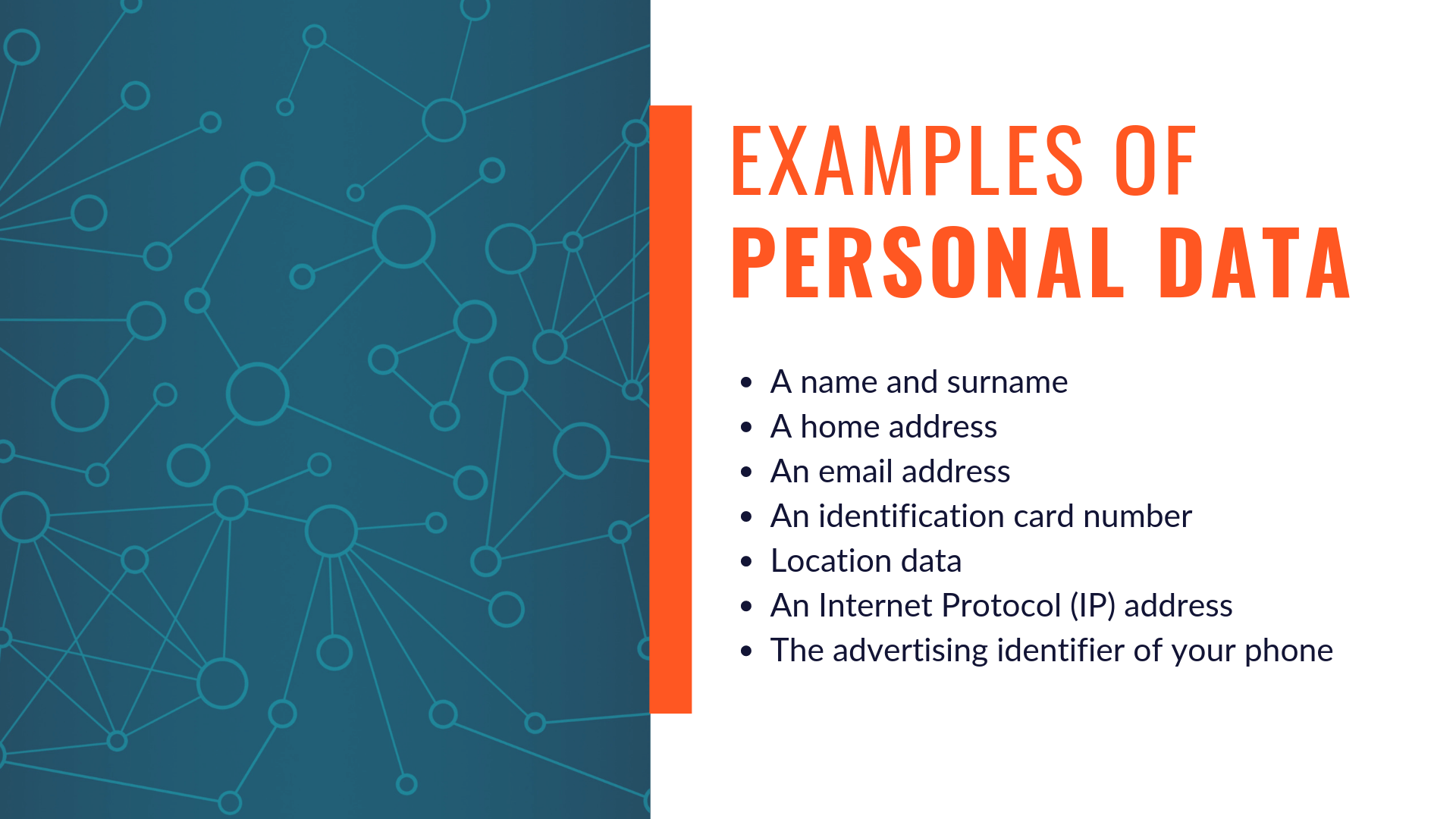
Big, small and ubiquitous. Data is everything, and everywhere. Users are giving it, websites are collecting it and policymakers, the tech industry, and the citizens are constantly dabbling with what to do with all of the information that is being gathered. From an email to credit card information, from passwords to shopping history, from photos to personal information – websites can ask and/or collect potentially a million things to analyze customers better.
As a business (and we will be focusing on e-commerce), you want to know your customer well and data is as close as you get to interpersonal interaction in getting to know them specially when you are trying to generate leads. However, by asking for more information, you put them and their details at risk from hackers, and consequently, from tangible and intangible losses. Not to mention breach of privacy is absolutely unethical. Data breaches have been increasingly common over the last few years and all companies, small or big, are vulnerable to this.
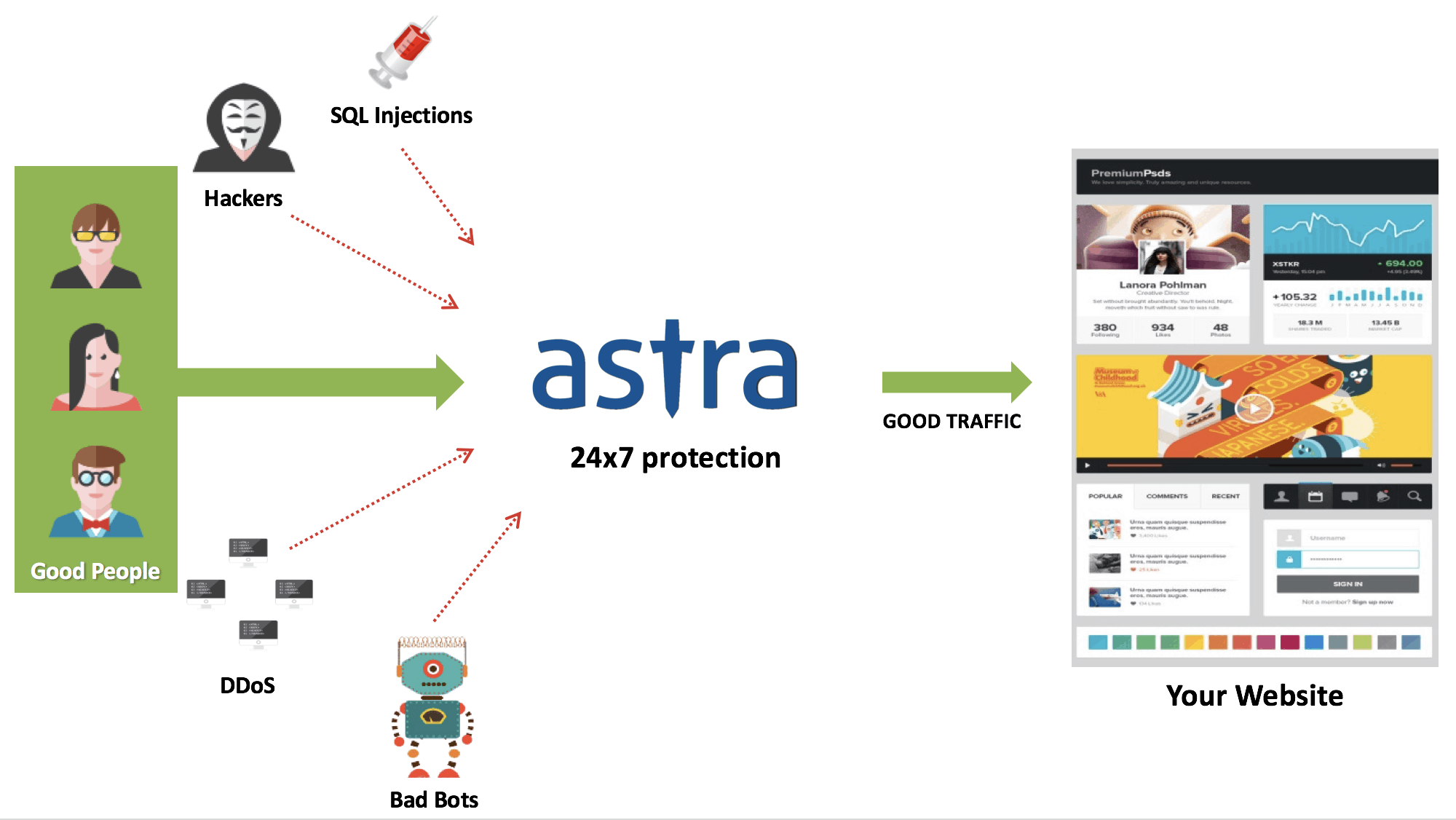
Preparing to combat both uncommon and common cybersecurity threats should be of utmost priority. As an e-commerce business, there are specific data types you may be asking for.
Here’s how to responsibly handle it:
1. Personal information
This is really basic and profoundly important. As customers shop and buy on your online store, they give up one of several things – name, phone number, email ID, birthdate, address (if and when shipping is involved), password. And whether they sign out as a guest or log in as customer adds another layer of security concern – should you store their data, and if yes, where and how?
First, have an elaborate and effective password policy. The truth is users can sometimes be inattentive of their passwords, but here is where you step in and don’t allow for easy passwords.
One of the most common policies is to require a mix of upper case, lower case and special characters.
Other policies include keeping a minimum and maximum age for passwords, and more. Take this into account from the very start, when you allow the customer to create logins on your WooCommerce store. You can use plugins to enforce strong passwords.
Encryption is another area you will want to invest in. Look up how you can tweak your WordPress code to enable secure storage. Alternatively, ensure offsite backups of user data are encrypted. For security specific to storing logged-in user information, you can use derivation functions to secure their data.
And there is always the option of using software services and products for this.
2. Credit Card information
The bigger responsibility with e-commerce site owners lies in that they are asking for banking details, and effectively taking responsibility for customers’ money. Buying an SSL certificate will get you started, but there are other practices you can adopt for bulking up security.
The Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards designed to ensure that ALL companies that accept, process, store or transmit credit card information must maintain to ensure a secure environment. Even small and medium businesses need to be compliant.
This credit card information is often stored only in the form of tokens on company servers, and storing sensitive data on online servers goes against PCI guidelines.
If you have any point of sale facilities, make sure they are protected from malware that would pass on credit card information, and ditto for your store and website. Malware causes credit card information to pass on to the hackers, much like what happened with Target in 2013.
Related Article: How to Fix Credit Card Hack in Magento & OpenCart
3. Front-end information
Most e-commerce website owners will take testimonials, quotes, and reviews for their website. It is possible that content producers could use these words out of context. To prevent this, install a content protection plugin to demotivate people from simply copy pasting the content. They are more less likely to want to type it out.
4. Backend information
For companies with employee laptops which could have important data, it is essential to use remote wipe software to delete data from a hard drive, in case of emergencies. Always review who has access to what (since most data leaks originate from insiders), and make sure that passwords are not stored online. Using an effective firewall is great for companies who may not want to invest in bulky security infrastructure.
Conclusion
All in all, building a culture of cybersecurity among your employees, your company and working towards safeguarding the rights of your customers can go a long way. Ensure you have a clear, easy-to-read privacy policy, state clearly what data is being collected, where it is stored and how it might be used. Collect only the required data.
Besides the ethics, it makes better business sense to invest in a trusted security solution from the beginning, then suffer a lapse and stand a chance to lose millions. Staying secure is a win for everyone, really.