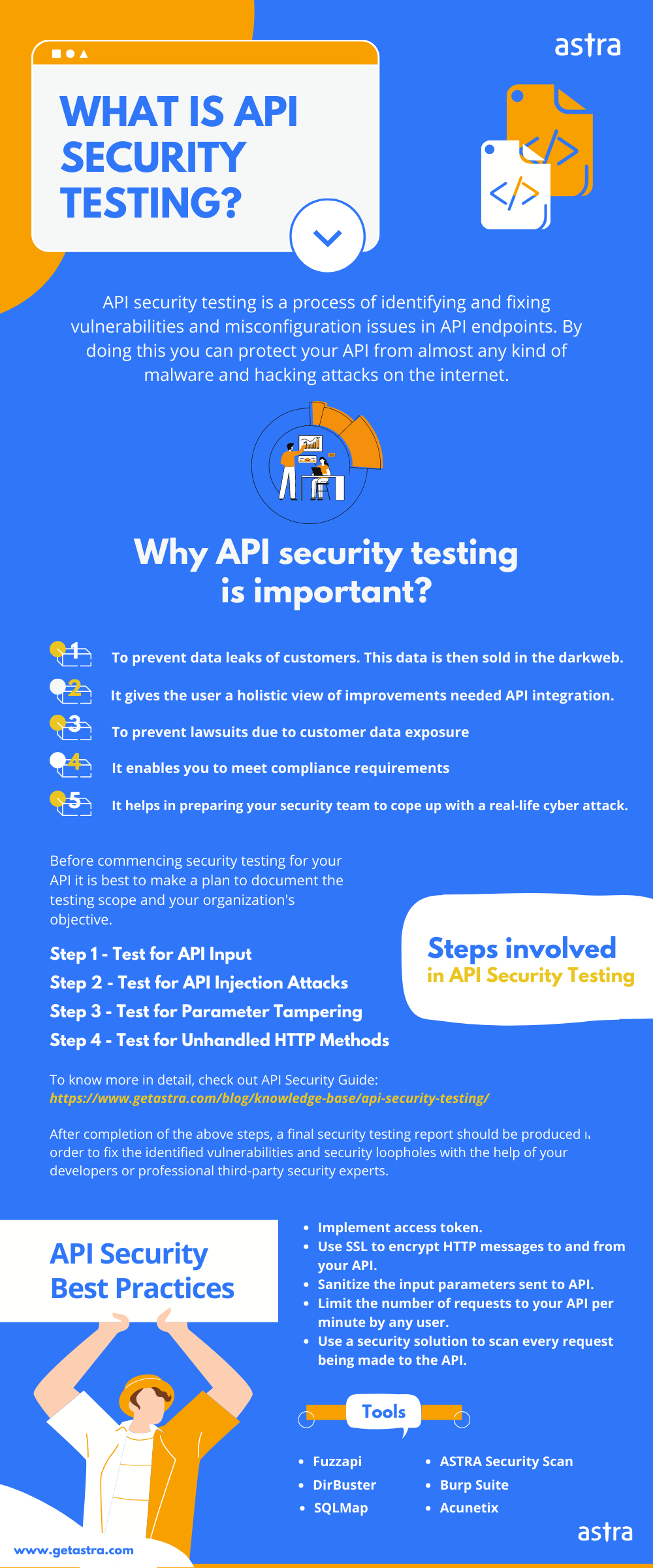
API security testing refers to checking and pentesting the API endpoints to ensure it is free from vulnerabilities, fuzzy inputs, injection vulnerabilities, tampered parameters, and more. Regular API security testing keeps the endpoints secure and safe from malicious attackers.
API security is nothing but securing the API endpoints from attackers and building your APIs in a secure fashion. A vulnerable API could lead to:
- Unauthorized Access
- Data leakage
- Sanctioning Fuzzy input
- Injection Vulnerabilities
- Parameter Tampering, etc.
Not sure if you have vulnerable API rules on your website? Just stick around till the end. The API security testing methods depicted in this blog are all you need to know & protect your API better. All that in a minute.
First, let us take a look at the different kinds of API security vulnerabilities and the tools one could use to find them.
| Security Issues | Tools to Test |
|---|---|
| Injection Flaw (SQLi, LDAP, CRLF) | Burp Suite, Proxy, SQLmap, Astra Security Scan |
| Broken Authentication | Burp Suite, Manual Testing, Astra Security Scan |
| Data Exposure | Acunetix, DirBuster, Astra Security Scan |
| XSS | Burp Suite, Manual Testing, Astra Security Scan |
Why Do You Need API Security Testing?
As we said, API allows data exchange between applications. If a hacker breaches API security, he/she can access sensitive data stored on your website.
Other bitter consequences of an API security breach could be:
- Leakage of customer data. This data is then sold on the dark web.
- Defacement to your website & business. It can severely affect you & your brand’s reputation in the market.
- Number of users and revenue take a plunge.
- Lawsuits (if there is negligence on your behalf).
The following API security breaches in popular companies will paint a more realistic picture before you:
- Airtel API was found leaking the information of their customers by just using their numbers. According to an estimate, there are around 325 million active users of Airtel. Not to say, the result could have been disastrous!
- In 2019, a bug CVE-2019-5786 was found in the File Reader API. This led to a vulnerability in almost all major browsers. Hackers exploited it wildly to target Chrome users!
- Hostinger, a famous hosting service provider, said one of its servers was hacked; using which the attackers were able to access its internal API. Details of around 14 million clients were stolen!
- JustDial, the largest local search engine platform in India, was accused in 2019 of leaking its entire database of customer data of over 100 million users. The leaked information included their names, emails, mobile phone numbers, date of birth, gender, occupation, photos, and more. Essentially, any piece of data provided through the use of its website, its app, its customer support system, everything, was leaked.
We are here to help you steer your business clear of similar situations. Read on.
What is the REST API?
REST is basically an API designing style. It stands for “Representational State Transfer“. By designing style we mean – it is a set of rules that API designers follow while creating an API.
Almost all popular companies like Facebook, YouTube, etc. use REST API (internally or externally). REST API is used in almost all popular open-source CMSes like WordPress, Magento, etc.
Remember that REST API is a designing style of an API and therefore is platform-independent. Rest API can be implemented in any language (PHP, Python, etc.). Generally, the data is exchanged in XML or JSON. Although it’s not specified.
Moving on.
REST API is not free from vulnerabilities. You need to look-out for the common vulnerabilities if you never want to fall prey to them.
Time to learn some truth and bust some myths about API security.
1. API security is integral to API
Quite often consumers view API security as a feature of API. It’s not a feature. It’s a different technology. Understand that securing your API requires looking elsewhere, beyond your API itself. We say, API security is a mindset and not a feature.
2. Using software to secure your API is enough
Software-based API security is an option available to you as you look to manage your API. It’s pretty convenient and might give you the sense that it is all fine. Unfortunately, you’d be wrong, and there’s history to show why. All the infamous API security breaches have been connected to software: running alien code on your site is going to leave a whole host of vulnerabilities. So, go for a more concrete option such as API security testing.
3. It’s simple
As a concept API itself can be summed up with a good degree of simplicity – two programs are connected through an API, and that’s it. However, API security is not that simple. And this might be one reason for you to think about investing in some advice from an expert in the area. The ironic part is that the simpler your actual API connection is, the less simple securing it is going to be. In the modern era, sharing data but at the same time securing it is what makes API security a necessarily complicated task.
4. API gateway is the same as API security gateway
API security gateways ought to be used all the time as a solution to the ongoing API security problems. Security gateways are able to limit the flow of data to the point of necessity and stop you from hemorrhaging data that doesn’t necessarily need to be out there. A normal API gateway might be useful for your connection but it will never compare to a secure API gateway.
5. APIs automatically means better security
Many companies talk about their products being safe because they have features of API security, and they believe that API security ultimately means the best security. However, this is not true. Just having features from API security doesn’t mean that your product is secure or more secure than others. A penetration testing of APIs will help you discover the loopholes that can lead to hack.
While APIs can enhance your security and protection, and they can amp up the protection that your security system gives, they will not keep you safe enough on their own.
How Does API Security Testing Work?
API security testing starts by defining the API that needs to be tested to detect and identify vulnerabilities. This is followed by testing for various cases mentioned below after which a detailed API vulnerability report is released to the customer.
1. Test for API Input Fuzzing
Fuzzing simply means providing random data to the API until it spills something out – some info, some error message or anything to imply that random data has been processed by the API.
For numerical inputs, you can try 0 or negative numbers or very large numbers. For string inputs to the API, you can try SQL queries or system commands or random characters like “, ‘, //, etc. But if you wish to automate the whole process, there is an open-source fuzzing tool called Fuzzapi.
To use Fuzzapi follow these steps:
Step 1: Download and install Fuzzapi. Read this to know how to do that.
Step 2: Now, once Fuzzapi is installed, open your browser and navigate to localhost:3000. You will see something like the image given below.
Also Read: 7 Best API Penetration Testing Tools And Everything Related

Step 3: In the URL field, add the URL you want to test. Select the method of your choice. In the Raw Headers and Parameters field, add the info if needed otherwise leave them blank. Finally, click the Scan button.

Step 4: Wait while the test goes on. Once finished, if the API is vulnerable, final results will be shown like the image given below.

2. Test for API Injection Attacks
a) SQL Injection (SQLi)
SQLi attacks are successful when the unsanitized API input is processed by the database. Hence, it is important to test your REST API for any SQLi bugs. Try providing SQL commands in the input like:
'or 1=1--
"and 1=1--
If the API is vulnerable to SQLi (error-based and/or SQLi), these values into the parameters may help bypass some restrictions and respond with 200 OK. i.e.
www.xyz.com/api/auth-token/user=admin'or 1=1--
If the API is vulnerable to SQLi but not necessarily error-based and/or vulnerable, it may still generate a DBMS error in the message and respond with 500 Internal error. Like the one shown in the image.

Moreover, if you wish to automate the process, try using Sqlmap.
b) Command Injection
The API inputs can also be injected by various OS commands. These commands then get executed on the server. However, for different Operating systems(Windows, Linux, etc), the commands would be different. For instance, for a Linux system, the command “rm /” can remove the entire root directory. When URL encoded, this command would look something like rm%20/.
So for instance, an API is being used to view the contents of a site, then malicious code can be executed in the following manner.
https://example.com/view?name=file.txt;rm%20/
The semi-colon after the file.txt ends the input parameter and executes the OS command. However, be careful with this command as it can delete the entire directory. Try something a little less harmful like:
https://example.com/view?name=file.txt;reboot
However, if you wish to automate the process, try using Commix.
3. Test for Parameter Tampering
Often, parameters sent through an API request may be vulnerable to tampering. By tampering them, an attacker can change the values of a product and therefore purchase it almost for free.
For instance, if there is a hidden field in the form submitted by the user like this:
<input type="hidden" name="price" value="100.00" />
The attacker can change the value from 100.00 to 1 and get the product almost free of cost. This can be done using the element inspector in any browser. So make sure to test such hidden fields sending requests to your API endpoint.
4. Test for Unhandled HTTP Methods
Web applications communicating using API often use various HTTP methods. These HTTP methods are used for saving, removing or getting the data. So if a server does not support an HTTP method, typically it should show an error. But this is not the case always, especially for vulnerable APIs.
To test for such vulnerability, make a HEAD request to your API endpoint which requires authentication. There are several ways to send HEAD requests. To accomplish this using python, add the following code to a python script and run it:
import requests x = requests.head('API-URL')
print(x.headers)
Replace API-URL with the URL you wish to test.
- If you get a 405 method not allowed or 501, everything is fine.
- In case you get a 200 OK without authentication, it may be a vulnerability.
API Security Best Practices
- Implement access token. Access tokens are available to users while signing up to maintain a level of authorization. Validate Access tokens every time a user requests the API. Also, add an option to revoke or reset the token.
- Use SSL to encrypt HTTP messages to and from your API.
- Always sanitize the input parameters sent to API. This should include the access token field.
- Limit the number of requests to your API per minute by any user.
- Use a security solution to scan every request being made to the API.
Also Read: Top 5 Software Security Testing Tools in 2022 [Reviewed]
In Conclusion
The most important thing is to follow the API security practices mentioned above. As they can provide a sufficient layer of security to the API endpoint.
However, if your website’s API has still been compromised, Get immediate professional help.
It is common to find it cumbersome to identify and patch the vulnerability. You can always go for automated security solutions such as Astra to test and secure your API.
FAQs
1. What is the timeline for API Secuity testing?
API security testing ideally takes 4 to 5 days. You start seeing the vulnerabilities from the 2nd day on your dashboard. The timeline may differ a little depending upon the scope of the test.
2. How much does API security testing cost?
The cost of API testing is between $349 and $1499 per scan depending on the number of scans and the scope of the pentest.
3. Why choose Astra for Security Testing?
1250+ tests, adherence to global security standards, intuitive dashboard with dynamic visualization of vulnerabilities and their severity, security audit with simultaneous remediation assistance, multiple rescans, these are the features that give Astra an edge over all competitors.
4. Do I also get rescans after a vulnerability is fixed?
Yes, you get 2-3 rescans depending on the plan you are on. You can use the rescans within a period of 30 days from initial scan completion even after a vulnerability is fixed.