The Gramm-Leach-Bliley Act (GLBA), also known as the Financial Services Modernization Act of 1999, is a US federal law governing how financial institutions handle individuals’ private information. It mandates disclosure of information-sharing practices, and safeguards for sensitive data, and includes the Financial Privacy Rule, Safeguards Rule, and Pretexting provisions.
With the rising prevalence of online banking and digital wallets, GLBA, although explicitly designed for American financial institutions, has the potential to indirectly affect other businesses. This is particularly true for provisions related to data privacy and security practices. These regulations can influence non-financial businesses that engage with such institutions or manage their financial information as a part of their operations.
This is where GLBA risk assessments come into play! In this article, we will delve into the requirements, process, and benefits of conducting a risk assessment, emphasizing its significance in achieving regulatory compliance and enhancing data security.
What is a GLBA Risk Assessment?
A GLBA risk assessment is an extensive procedure that aims to evaluate and categorize identified security risks or threats. It assesses the confidentiality, integrity, and availability of information systems and customer information, as well as outlines the mitigation or acceptance of such risks based on the assessment.
GLBA Risk Assessment Requirements
The GLBA establishes specific requirements for financial institutions to conduct GLBA-style internal risk assessments as part of their information security programs. These requirements include:
Legal and Regulatory Framework
GLBA necessitates financial institutions to provide clear explanations of their information-sharing practices to their customers and take measures to protect sensitive data, as outlined by the following three key sections:
This rule governs the collection and disclosure of customers’ private financial information. Financial institutions must inform customers about their information-sharing policies and practices, allowing customers the opportunity to opt out of certain data-sharing arrangements.
This rule mandates financial institutions to establish comprehensive security programs to safeguard customer information by implementing administrative, technical, and physical safeguards to protect against unauthorized access or data breaches.
These provisions specifically address the practice of pretexting, which involves using false pretenses to obtain an individual’s private information. GLBA prohibits this deceptive practice, aiming to prevent unauthorized access to sensitive data.
In essence, GLBA regulations are required to disclose their online and offline data-sharing practices and provide customers with the option to “opt-out” if they prefer not to have their information shared with specific third parties. Additionally, financial institutions must furnish customers with written privacy policy notices that detail the specifics of their data-sharing practices.
This ensures transparency and empowers customers to make informed decisions about their data privacy.
Why are GLBA Risk Assessments Important?
The significance of conducting a GLBA risk assessment lies in its capacity to offer financial institutions a methodical and organized approach to appraise the security of their information systems and safeguard customer data.
Through the identification of potential risks and vulnerabilities, institutions can take proactive steps to shield against data breaches and prevent unauthorized access, ultimately fortifying their overall security posture. In essence, it serves as a preemptive safeguard against potential
threats to sensitive information.
What is the penalty for Non-Compliance?
Failure to comply with the GLBA can result in:
- Penalties for non-compliance, including fines of up to $100,000 per violation.
- Fines for officers and directors, potentially reaching up to $10,000 per violation.
- Criminal penalties, such as imprisonment for up to 5 years.
- The potential revocation of licenses.
- Substantial fines and harm to the reputation of financial institutions.

Why is Astra Vulnerability Scanner the Best Scanner?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

What is the GLBA Risk Assessment Process?
1. Initiation and Preparation
- Scope Definition: Determine the scope of the risk assessment, including the information systems, data types, and business processes to be assessed.
- Team Formation: Assemble a cross-functional team with expertise in IT, security, compliance, legal, and business operations to conduct the assessment.
- Documentation Review: Review existing documentation, policies, and procedures related to data security, privacy, and risk management.
2. Gathering Data
- Data Collection: Gather data on the information systems, customer information, and existing security controls. This includes inventorying all systems that store, process or transmit customer information.
- Use of Templates: Utilize GLBA risk assessment templates or software to assist in systematically collecting and organizing this data.
3. Data Classification
- Categorization: Classify customer information based on its sensitivity and potential impact. Categories may include non-public personal information (NPPI), financial data, and other sensitive data.
- Risk Level Assignment: Assign risk levels to each data category based on the potential harm that could result from unauthorized access or disclosure.
4. Risk Identification and Assessment
- Threat Identification: Identify internal and external threats that could compromise the security of customer information. This includes intentional and unintentional threats like data breaches, cyberattacks, and employee negligence respectively.
- Vulnerability Assessment: Assess vulnerabilities by leveraging a quality vulnerability Scanner like Astra, to identify weaknesses within information systems that could be exploited by identified threats of malware, injection attacks, DDoS attacks, and more.
- Penetration Testing: Incorporate penetration testing to actively assess the security of critical systems. These tests involve ethical software and hackers simulating real-world attacks to identify vulnerabilities that may not be apparent through passive assessments.
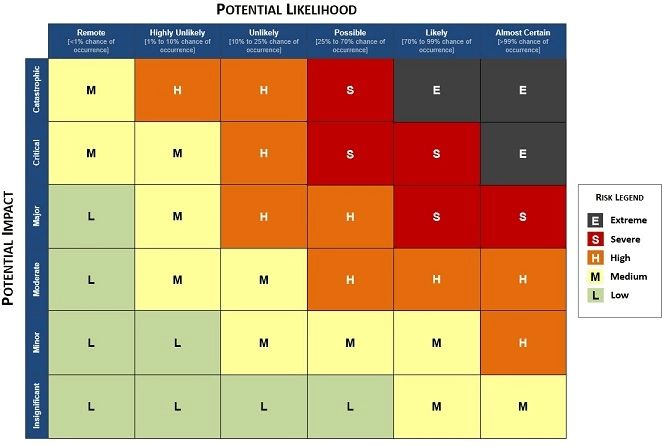
5. Risk Assessment Matrix
- Risk Analysis: Evaluate the likelihood and potential impact of risks. This involves assigning risk scores to identified threats and vulnerabilities.
- Matrix Creation: Develop a GLBA risk assessment matrix, typically a spreadsheet or software tool, to evaluate the likelihood and impact of identified risks.
- Prioritization: Use the risk assessment matrix to prioritize risks and determine appropriate safeguards based on their severity.
6. Developing Safeguards
- Safeguard Development: Based on the risks identified and prioritized, financial institutions must develop a set of safeguards and security measures.
- Safeguard Categories: Safeguards may include administrative controls (e.g., policies and procedures), technical controls (e.g., encryption and access controls), and physical controls (e.g., facility security measures).
7. Risk Mitigation
- Implement Safeguards: Implement the identified safeguards to reduce the identified risks to an acceptable level.
- Penetration Testing Follow-Up: Rerun the assets through a vulnerability scanner and pentest to ensure the quality of patches and any new security measures implemented.
8. Documentation and Reporting
- Record Keeping: Maintain detailed documentation of the entire risk assessment process, including findings, risk scores, safeguards, and any changes made to security measures.
- Report Preparation: Prepare a comprehensive report summarizing the risk assessment results, including identified risks, mitigations, and recommendations for improvement.
- Board of Directors: Present the risk assessment results to the board of directors or an equivalent governing body for review, approval, and oversight of the information security program.
9. Ongoing Monitoring and Review
- Continuous Monitoring: Continuously monitor the effectiveness of implemented safeguards and security measures. This includes regular security assessments, vulnerability scans, and incident monitoring.
- Periodic Updates: Review and update the risk assessment periodically to account for changes in technology, threats, regulations, and business operations.
10. Incident Response Planning
- Be Specific: Outline detailed step-by-step procedures to follow in the event of a security incident or data breach. Ensure that the plan aligns with the risk assessment findings.
- Responsibilities & Roles: Clearly define the individuals, departments, and agencies involved and their individualistic roles and responsibilities in case of a cyberattack.
- Standard Messages: Draft standard communication that needs to be circulated internally and externally in case of any cybersecurity incident to comfort all those impacted while maintaining as much transparency as possible.
By integrating penetration testing and vulnerability scanning into the risk assessment process, financial institutions can proactively identify and remediate security weaknesses, reducing the likelihood of data breaches and enhancing compliance with GLBA regulations. These practices provide a more comprehensive view of the organization’s security posture and improve the overall effectiveness of the risk assessment process.
Make your Web Application the safest place on the Internet.
With our detailed and specially
curated Web security checklist.

What are the Benefits of GLBA Risk Assessment?
1. Enhanced Security
This process enables organizations to meticulously pinpoint vulnerabilities, threats, and shortcomings in their information systems and customer data handling practices.
By systematically evaluating and addressing these risks, financial institutions can implement robust security measures, including encryption, access controls, and intrusion detection systems. These enhanced security measures serve as a bulwark against data breaches and cyberattacks, fostering a more secure digital environment.
2. Legal Compliance
Compliance with the GLBA is a legal mandate for financial institutions operating in the United States. Among its various requirements, it stipulates the need for regular risk assessments and the implementation of safeguards to protect customer data.
Thus, ensuring adherence helps financial institutions avoid regulatory and legal liabilities, underscoring their commitment to maintaining a strong and lawful footing within their industry.
3. Customer Trust
By transparently showcasing their dedication to safeguarding customer data through diligent risk assessments and the implementation of stringent security measures, financial institutions instill confidence in their clientele. This trust is a valuable asset that can result in increased customer loyalty, expanded business relationships, and positive word-of-mouth referrals.
4. Cost Savings
While there are upfront costs associated with conducting GLBA Assessments and implementing safeguards, early identification and mitigation of risks serve as a preventive measure, averting costly data breaches, legal fines, and regulatory enforcement actions. Thus, effective security measures minimize the financial impact of security incidents and mitigate reputational damage.
What are Some Common Challenges of GLBA Risk Assessment Security?
1. Changing Threat Landscape
Cyber threats, in particular, are dynamic and are only growing increasingly sophisticated. New attack vectors and techniques continuously emerge, making it crucial for institutions to stay vigilant. To keep pace with these changes financial organizations must proactively adapt their security measures and risk assessment strategies to counter emerging threats effectively.
2. Resource Allocation
Conducting thorough assessments and implementing safeguards are resource-intensive endeavors. Thus, financial institutions must strike a balance between allocating resources effectively to address identified risks and ensuring operational efficiency. This requires careful budgeting and prioritization of risk mitigation efforts.
3. Updating the IT Risk Assessment for GLBA
Financial institutions must revisit and review their assessment process to reflect the continuous changes in the regulations, technology, and business operations accurately. This includes incorporating new data sources, assessing emerging risks, and ensuring that safeguards remain aligned with the evolving security landscape.
How can Astra help?
Astra Security is a vulnerability assessment and penetration testing company that provides round-the-clock security testing services to assess internet-facing assets as quickly and efficiently as possible to detect vulnerabilities.
Our VAPT offerings include 9300+ tests that help you:
- Improve your holistic security coverage for web and mobile applications, cloud infrastructure, networks, and APIs.
- Detect and remediate vulnerabilities and security gaps of varying criticality.
- Maintenance of compliance with regulatory requirements like GLDA, HIPAA, SOC2, PCI-DSS, ISO 27001, and GDPR.
Moreover, our CXO-friendly dashboard, seamless integrations, and customizable reports all help you simplify GLBA Risk Assessments.
Conclusion
In conclusion, the GLBA-based risk assessment process is a critical component of safeguarding customer information, ensuring legal compliance, and maintaining trust in the financial industry. By complying with this framework, institutions can enhance security, meet regulatory requirements, adapt to evolving threats in the face of modern cybersecurity challenges, and maintain the integrity of financial systems. Lastly, in case, you want to share the load, reach out to our experts today!
FAQs
Which are three key rules of the GLBA?
The GLBA comprises three vital rules: the Financial Privacy Rule, which demands privacy notices and opt-out choices; the Safeguards Rule, necessitating security programs; and the Pretexting Provisions, prohibiting fraudulent data acquisition, all safeguarding consumers’ financial information.