Key Takeaways:
A proactive approach reduces disruption: Regularly conducting assessments, testing security, and documenting mitigation plans protects customer trust, helps avoid penalties, and prepares the business for evolving threats.
Risks in payment environments build up quietly, not all at once: Minor updates and new integrations gradually introduce hidden exposures into your environment. PCI risk assessments identify weak points before they lead to costly incidents.
PCI DSS makes risk assessment mandatory: Any organization that stores, processes, or transmits cardholder data must conduct regular PCI risk assessments to uncover threats and evaluate where controls need strengthening.
PCI risk assessment turns compliance into practical security action: Beyond meeting PCI DSS requirements, it helps teams identify vulnerabilities, prioritize risks, and strengthen defenses in the cardholder environment.
Mastercard’s 2026 report found 10,500 active web-skimming attacks in 2025, compromising more than 23 million online transactions. This serves as a reminder that even small blind spots in payment environments can scale into major business risk. For CISOs, CEOs, and CTOs, the challenge is to ensure that the cardholder data environment remains secure in practice. Meanwhile, small infrastructure updates, new integrations, and third-party scripts slowly expand the attack surface and increase risk. Unfortunately, organizations often identify risks only after the exposure has existed for a while.
A PCI risk assessment exists to find that exposure before someone else does. PCI DSS provides a comprehensive structure that protects sensitive information during payment card transactions. PCI risk compliance follows a structured process to help you understand where your cardholder data environment is vulnerable and what needs to change.
In this article, we will delve into what PCI DSS is, the significance of PCI compliance risk assessment, and best practices for implementing PCI DSS.
What is a PCI-DSS Risk Assessment?
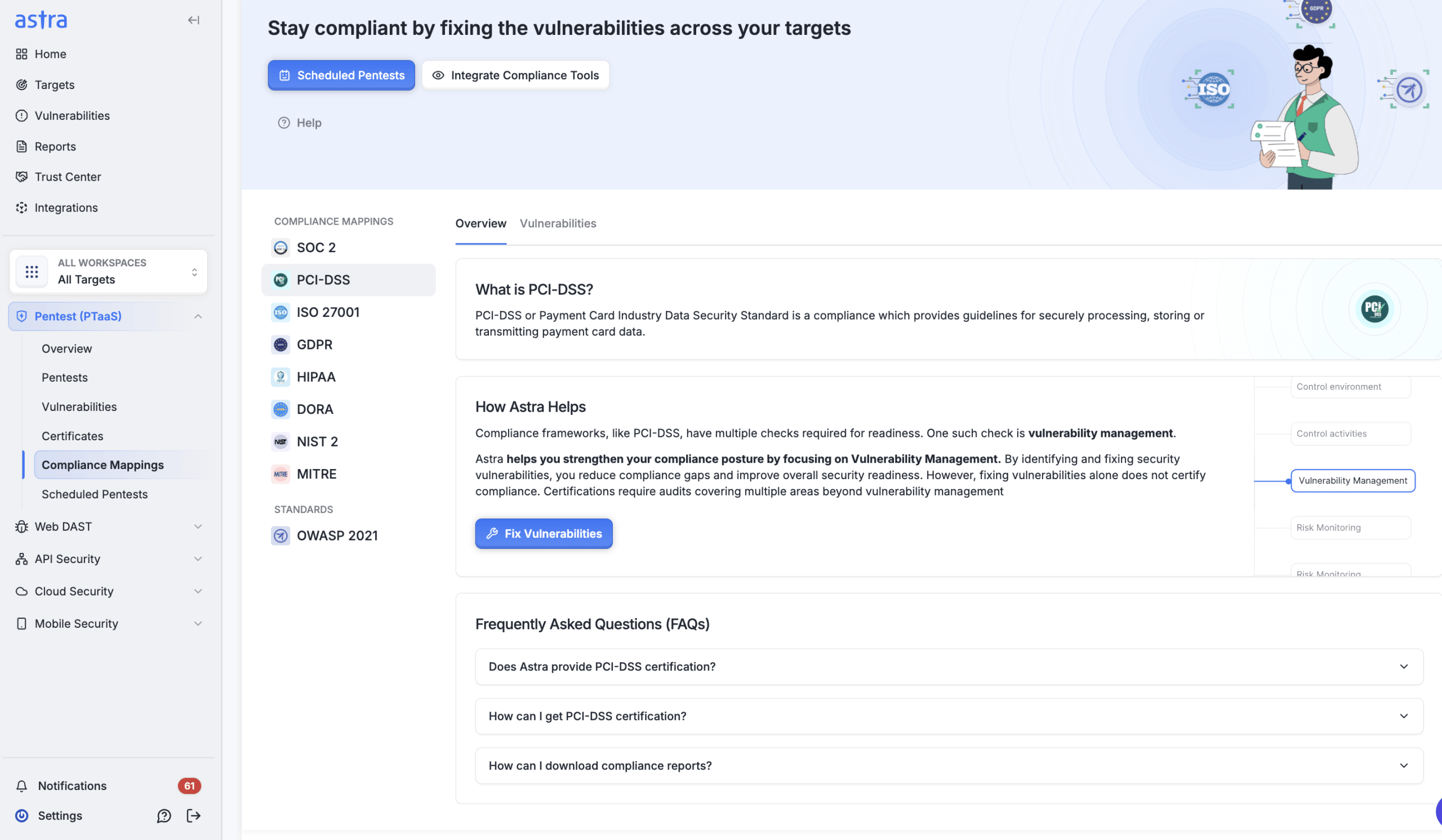
PCI-DSS risk assessment is a mandatory process that enables organizations to identify, analyze, and prioritize risks that could compromise their cardholder data environment or PCI compliance goals. Under Section 12.2 of the PCI DSS Fundamental Requirements, organizations must lay the foundation for a strong information security program. The process also estimates the potential impact of identified risks and prioritizes them based on their overall effect on organizational objectives.
Does your organization require a PCI-DSS Risk Assessment?
Organizations that manage cardholder data must comply with PCI-DSS. Under Section 12.2 of the PCI DSS Fundamental Requirements, you must conduct a PCI-DSS Risk Assessment. Therefore, if you store, process, or transmit cardholder data, you should conduct an annual PCI-DSS risk assessment to identify underlying threats or vulnerabilities in your cardholder data environment (CDE).
Why is PCI Risk Assessment Important?
PCI compliance risk assessment plays a crucial role in ensuring the security and compliance of organizations, and here are some compelling reasons why it is of utmost importance:
1. PCI DSS Compliance
Simply put, PCI risk assessment is a non-negotiable part of the PCI checklist required for the PCI compliance test. Skipping this step would be asking for trouble. Non-compliance carries heavy penalties, such as fines and legal liabilities. And worst of all, a damaged reputation. Once you lose the trust of customers, partners, and stakeholders, you face a challenging battle to win it back.
2. Data Breach Prevention
The truth is, cardholder data is a gold mine for cybercriminals. But with a comprehensive PCI risk assessment, you can stay one step ahead. When you identify vulnerabilities and set up the right controls, you reduce the risk of data breaches.
3. Cost Savings
A PCI risk assessment may seem like an upfront expense, but consider it a long-term investment in your organization’s financial health. Staying proactive about potential security risks can save you from the financial nightmare of a data breach, in addition to the costs of forensic investigations, legal actions, and lost business.
4. Business Continuity
A good PCI risk assessment acts as a shield for your business. It protects your critical systems and processes, minimizing disruptions. And even when a security incident occurs, your robust risk management strategy ensures you can bounce back quickly.
What are the PCI-DSS Fundamental Requirements?
Organizations must comply with 12 PCI DSS requirements, which provide a solid security framework for organizations that handle credit, debit, and cash card payments. The requirements are as follows:
| Objective | Requirements |
|---|---|
| Build and Protect a Secure Network | 1. Install and maintain network security controls 2. Apply secure configurations to all system components |
| Protect Cardholder Data | 3. Protect stored account data 4. Protect cardholder data with strong cryptography during transmission over open, public networks |
| Maintain a Vulnerability Management Program | 5. Protect all systems and networks from malicious software 6. Develop and maintain secure systems and software |
| Enforce Strong Access Controls | 7. Restrict access to system components and cardholder data by business need-to-know 8. Identify users and authenticate access to system components 9. Restrict physical access to cardholder data |
| Continuously Monitor and Test Networks | 10. Log and monitor all access to system components and cardholder data 11. Test the security of systems and networks regularly |
| Uphold an Information Security Policy | 12. Support information security with organizational policies and programs |
What are the Steps for PCI DSS Risk Assessment?
PCI DSS risk assessment tailors its process to meet the specific requirements of PCI DSS compliance. Its primary objective is to comprehensively evaluate an organization’s cardholder data environment, identifying and assessing potential risks related to the confidentiality, integrity, and availability of cardholder data.
The PCI risk assessment process typically encompasses the following key steps:
1. Scope Identification
You must clearly define the scope of the cardholder data environment within your organization’s infrastructure. The scope includes identifying all systems, networks, and processes that handle cardholder data. This, in turn, establishes your PCI scope. Proper PCI-DSS scoping ensures you do not overlook critical components during PCI assessments.
Details to mention during the scoping include:
- How is the data used?
- How is the cardholder information processed and transmitted?
- Who has access to the credit card data stored by your company?
- Any personnel or systems that could affect the cardholder data.
You must understand the flow of cardholder data across systems and processes to pinpoint potential vulnerabilities and areas of risk. This PCI assessment process helps you identify weaknesses in data flows, allowing you to implement targeted security controls.
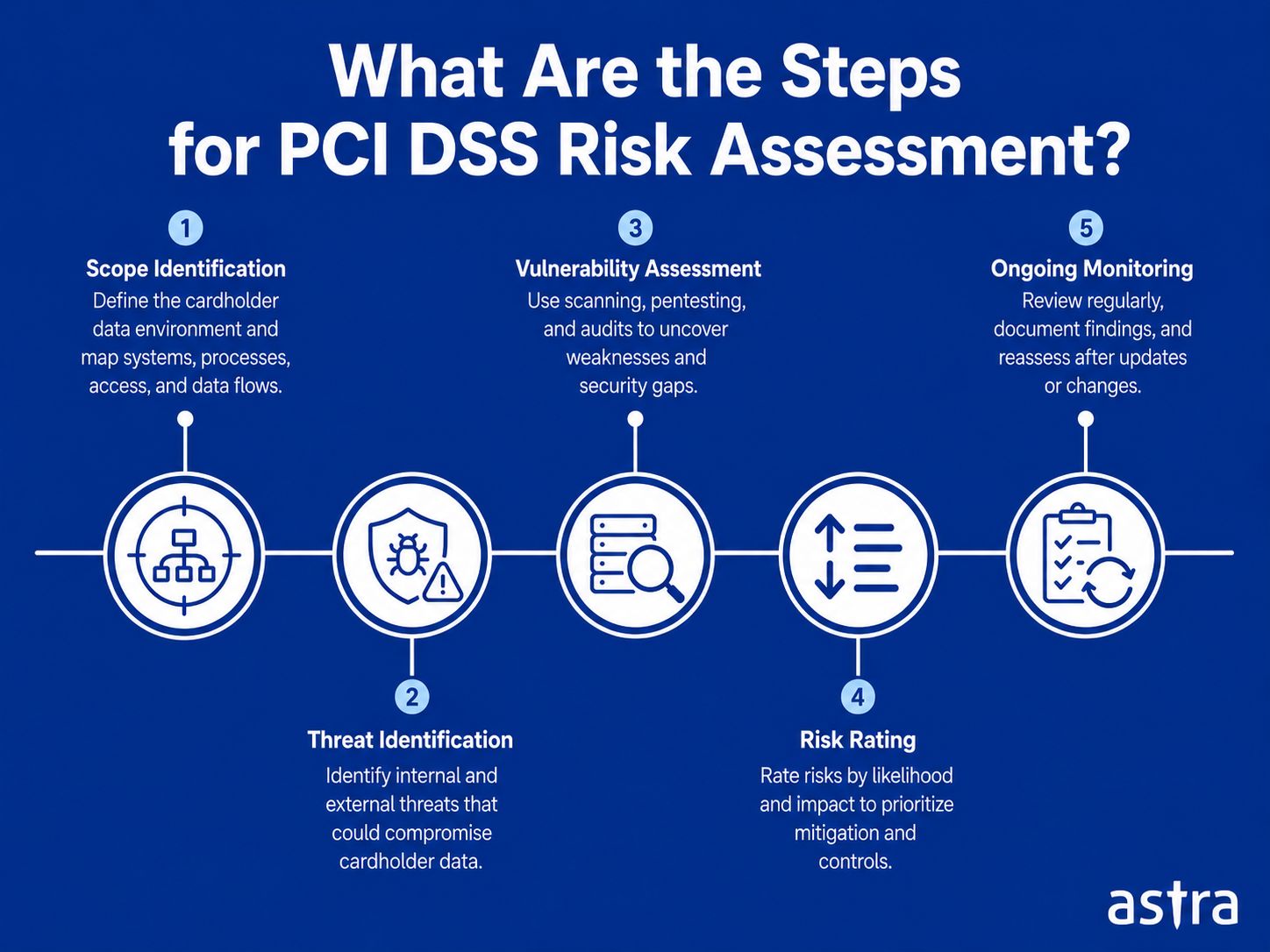
2. Threat Identification
The PCI risk assessment requires you to identify both internal and external threats that could compromise cardholder data. These threats may include cyberattacks, social engineering, insider threats, malware, and physical security breaches. Understanding potential threats helps you develop focused risk mitigation strategies.
When vulnerabilities are tested, systems that are scanned include:
- Digital assets (weak passwords, improper authorization measures)
- Physical assets (documents with cardholder information)
- Internal assets (company personnel and their access)
Mainly, threats arise from vulnerabilities and other risks. Vulnerabilities are essentially flaws in the components, procedures, or internal controls. Whereas risks refer to the likelihood that a threat will be exploited and the impact it would have on the cardholder data stored by your organization.
3. Vulnerability Assessment
You must conduct vulnerability PCI assessments on identified systems and processes to determine weaknesses that potential threats could exploit. Use techniques such as PCI vulnerability scanning, penetration testing, and security audits to identify and address security gaps.
Vulnerability assessments should identify a wide range of vulnerabilities, including top-level categories such as CVEs, OWASP Top 10, SANS Top 25, and other vulnerabilities that PCI-DSS considers a threat to cardholder data.
Once you complete the vulnerability assessment and identify the vulnerabilities and their potential impact, you should prioritize them based on the risk they pose to your cardholder data storage. This is known as risk rating.
4. Risk Rating
You should evaluate each identified risk based on its potential impact and likelihood. Assigning a risk rating helps you prioritize mitigation efforts, allowing you to focus on addressing the most critical risks first.
The two ways risks are classified include:
- Likelihood of risk: This refers to the chances that a detected vulnerability could be exploited. For example, if you suffered a breach last year, it is likely to happen again unless additional security measures have been implemented.
- Potential of risk: This refers to the potential impact of vulnerable exploitation on your organization.
Next, you must develop and implement risk mitigation strategies and controls as part of risk rating. Select appropriate security measures to reduce the likelihood and impact of identified risks. These controls may include encryption, access controls, network segmentation, regular security testing, and employee training.
5. Ongoing Monitoring
You must treat PCI risk assessment as an iterative process that requires regular reviews and updates. This approach ensures that your organization remains vigilant and adaptive to evolving threats and changes in the business environment.
Once you complete your risk assessment and subsequent mitigation, document the entire process and develop a risk management strategy for your organization’s systems. When you craft this strategy, understand and specify your goals for evaluating, prioritizing, and mitigating risks, threats, or vulnerabilities. You must also conduct pentests and/or vulnerability assessments at regular intervals or after any system update.
What are the Best Practices for Conducting PCI Risk Assessment?
To ensure the effectiveness of PCI risk assessment, organizations should adopt the following best practices:
1. Establish a Cross-functional Team
Involve stakeholders from IT, security, compliance, legal, finance, and various business units to ensure a holistic approach to risk assessment. Each team member brings unique perspectives and insights that contribute to a more comprehensive assessment.
2. Define the Scope Clearly
Clearly define the boundaries of the cardholder data environment to ensure that all relevant systems, processes, and third-party entities are included in the assessment.
3. Data Mapping and Flow Analysis
Thoroughly understand how cardholder data moves through the organization to help in identifying potential weak points. Data mapping and flow analysis facilitate the identification of areas where data is most vulnerable to compromise.
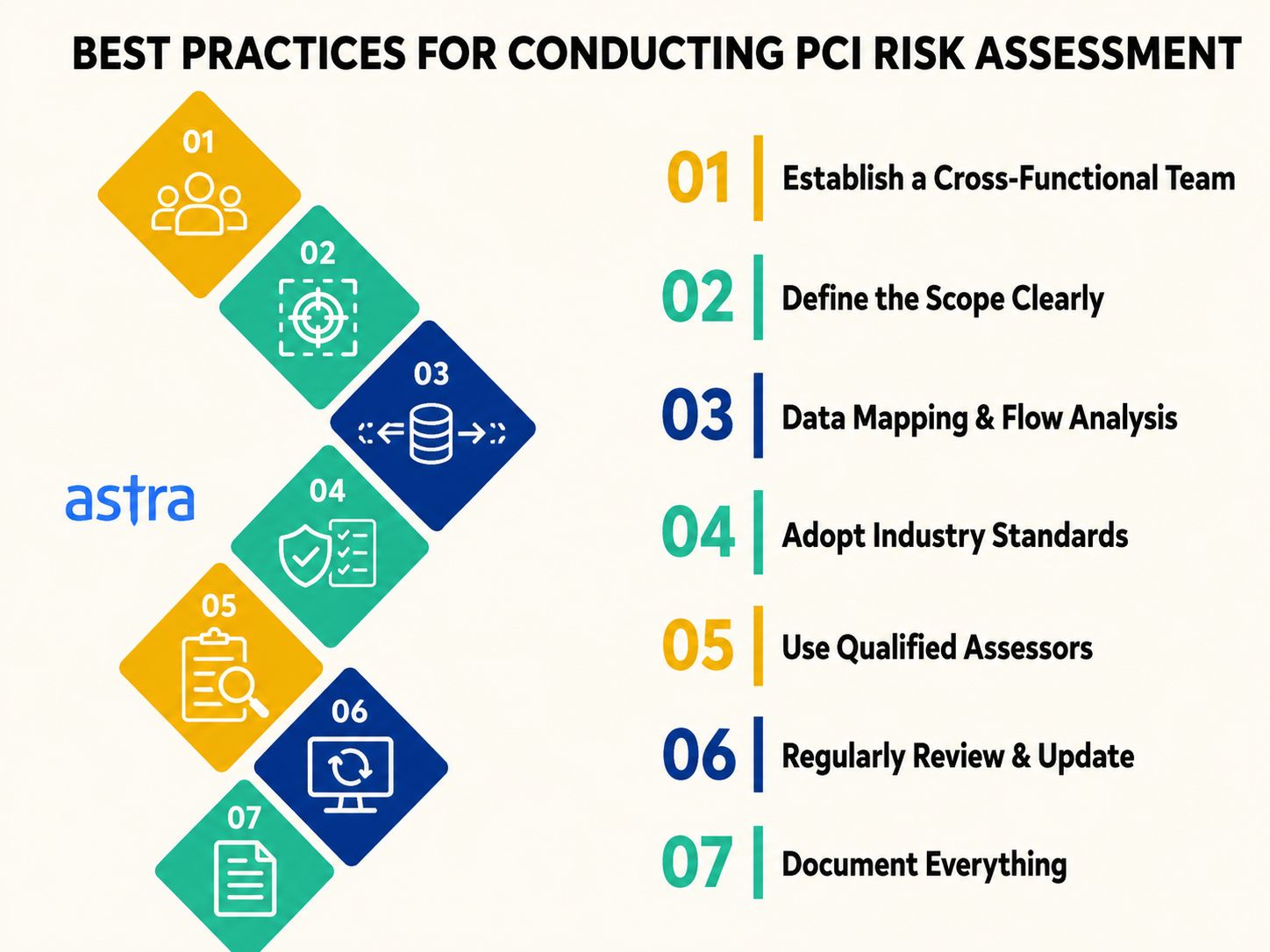
4. Adopt Industry Standards
While PCI DSS provides essential guidelines, organizations can benefit from adopting other established frameworks and best practices, such as the NIST Cybersecurity Framework or ISO 27001. These frameworks complement PCI DSS and provide additional insights into managing risks effectively.
5. Use Qualified Assessors
Engage qualified and experienced assessors to conduct the risk assessment. These individuals possess the necessary expertise and knowledge to conduct a thorough evaluation and provide valuable recommendations.
6. Regularly Review and Update
Risk assessment is not a one-and-done exercise. Regularly reviewing and updating the assessment ensures that the organization remains prepared to address new threats, changes in the business environment, and updates to PCI DSS.
7. Document Everything
Maintain comprehensive documentation of the risk assessment process, findings, and mitigation strategies. Proper documentation ensures that the organization can demonstrate its commitment to security during audits and assessments.
How to Integrate Risk Mitigation Strategies?
Once risks are identified and assessed, organizations must implement suitable risk mitigation strategies. Some effective strategies include:
1. Strong Access Controls:
Implementing access controls is a cardinal task for organizations. They allow only authorized personnel to interact with sensitive information while restricting access for others. This ensures each user only has the minimum levels of access they require to perform their work. Implementing measures such as multi-factor authentication helps add an additional layer of security. Most organizations set this up once and forget it. The reviews are where it actually holds up over time.
2. Data Encryption:
Data encryption transforms readable data into a coded version that is unreadable to unauthorized individuals. Thereby playing a crucial role in security. Encrypting data both during transmission and storage would mean that even a successful breach doesn’t automatically translate into a usable payload. Encrypted cardholder data is useless to an attacker without the decryption keys.
3. Network Segmentation:
Split your computer network into smaller parts so that cardholder data is isolated from the rest of your systems and limits potential attack surface. This can act as a buffer and ensures that even if one part of the system is compromised, the attacker does not gain free access to all areas, thus limiting potential damage.
4. Regular Security Testing:
Regular security testing, such as penetration testing and vulnerability assessments, is a proactive measure to identify and fix security gaps. Performing PCI Risk Assessments helps keep you ahead of exposure. The ultimate goals should not be to just pass the test but to find potential exploit paths.
5. Employee Training and Awareness:
Human error or ignorance is often a weak point in the security chain. Even the most complex state-of-the-art controls cannot compensate for employees clicking on phishing links and credentials shared on Slack. Hence, educate employees on the importance of security, best practices, and how to recognize and report potential security threats. A well-aware employee could act as an additional layer of defense.
6. Incident Response Plan:
Staying prepared for potential security incidents is invaluable for organizations. They need to prepare a clear incident response plan covering how to identify, contain, eradicate, and recover from a security incident. This would help your team minimize the impact of potential security incidents and make innovative decisions under pressure.
Final Thoughts
PCI risk assessment is a fundamental process in achieving and maintaining PCI DSS compliance. It is not just a compliance task to check off once a year. By thoroughly understanding the cardholder data environment, identifying potential risks, and implementing effective risk mitigation strategies, organizations can significantly enhance their security posture and protect sensitive data from cyber threats.
Choosing the right PCI QSA company is crucial in safeguarding the security and compliance of your organization’s web resources. It is highly recommended that you forge partnerships with industry-leading PCI QSA companies, such as Astra Security. You can tap into their expertise and gain invaluable insights into your current security posture.To discover the full range of benefits of partnering with PCI QSA companies and to explore how they can tailor their solutions to your specific needs, we invite you to schedule a free consultation with the team of experts at Astra Security. Don’t leave your security to chance – consult with us today!

FAQs
What is the role of PCI QSA companies in PCI-DSS audits?
PCI QSA companies are authorized firms that assess organizations’ compliance with the Payment Card Industry Data Security Standard (PCI DSS). They conduct comprehensive audits, evaluate security controls, and recommend improved data protection practices.
How do PCI QSA companies help organizations achieve PCI-DSS compliance?
PCI QSA companies assist organizations in achieving PCI DSS compliance by conducting thorough assessments of security controls, identifying gaps, and providing remediation guidance. They also offer services such as vulnerability scanning, penetration testing, and security policy development.
What are the key services offered by PCI QSA companies?
PCI QSA companies offer a range of services, including PCI DSS compliance assessments, vulnerability scanning and penetration testing, security policy development, remediation support, and more. These services help organizations strengthen their security posture and meet PCI DSS requirements.
What sets Astra Security apart from other PCI QSA companies?
Astra Security stands out for its expertise in cybersecurity, going beyond compliance. They combine advanced technologies with industry best practices, providing a holistic approach to security and actionable insights for effectively protecting web resources.