About PDF Invoice Plus Magento Extension Vulnerability
A couple of weeks ago, our security team was performing a security audit on a customer store using Magento. While testing the extensions used by the customer, a critical vulnerability was found in the extension PDF Invoice Plus. This extension is a widely used extension by hundreds of Magento stores to generate invoices for customers. Usually, these invoices contain end customer address and sometimes even their personal information.
Consequences of the Vulnerability:
- Loss of end user data
- Anyone can download invoice of any other users
- Leakage of invoice information via use of google dorks
The Details of Vulnerability:
- Go to any website using PDF Invoice Plus
- Simply visit a URL like: http://AnyMageStore.com/pdfinvoiceplus/order/print/order_id/208/
- Keep on changing the value of ‘208’ in the URL and if an invoice exists with that number, it will be downloaded
- This can be done even if a person is not logged-into the website also!
Mass Exploitation Possible:
We realized that since the URL at which PDF Invoice Plus extension releases the invoice remains constant for almost every store, this can be made into a google dork. We tried the following google dork:
[alert type=”success” enable_close=”no”]inurl:pdfinvoiceplus/[/alert] It showed all the websites using PDF invoice plus:
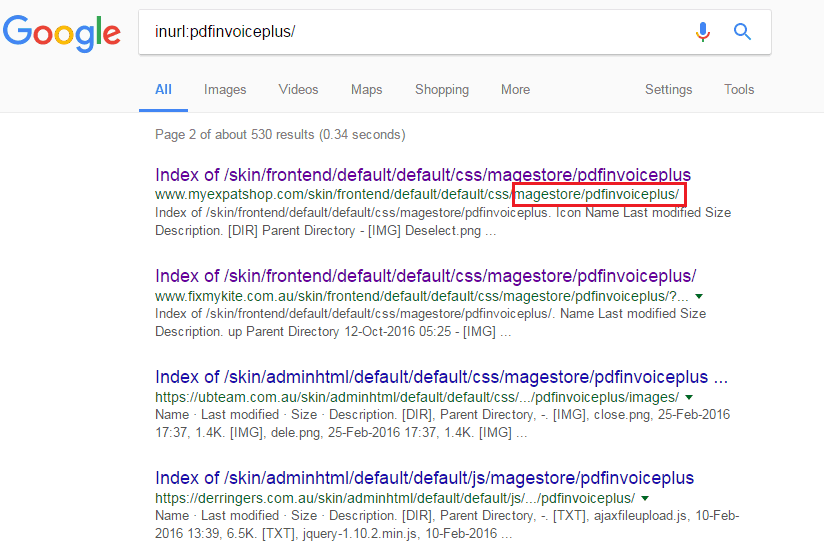
In such Magento stores, the following part: pdfinvoiceplus/order/print/order_id/508/ when added to the main website URL leads to downloading of invoices generated for customers of that store. The number 508 can be iterated/changed or guessed based on the store.
It is highly recommended that if you are using this extension, please update to the latest version to prevent yourself from this Magento extension vulnerability.
Timeline
PDF Invoice Plus team was very quick in understanding the issue and quickly work on fixing it. A person was quickly assigned from their team to work on the fix. Within no time a new version was sent to us to verify. After the verification, a secure version of the extension was released to their customers.

















Hi to all, it’s really a nice for me to pay a quick visit this web page, it includes important Information.