Article Summary
The blog post discusses symptoms, causes & fixes of a hacked drupal website
A hacked Drupal website can be acutely painful. Now, there could be numerous reasons for the hack. But, the most common ones are malware, code injection, spam, etc. If you are looking for Drupal malware removal techniques, you’ve hit the right spot. This guide contains step-by-step instructions to clean Drupal files and database of a hacked website. Also mentioned are malware and backdoor detection. This article is framed in a way so that it is easily applicable by an average user.
Drupal is one of the oldest & most secure CMS among the popular ones used today. It caters to over a million websites. However, multiple vulnerabilities were uncovered in Drupal this year. Much like a series of RCE vulnerabilities dubbed as Drupalgeddon. This has resulted in multiple hacked installations of Drupal within a few months, most of which were used to mine cryptocurrency. However, Drupal’s security team was quick enough to release necessary patch updates.
Drupal Hacked: Possible Outcomes of Drupal Hack
- Phishing pages designed to steal sensitive info appear on the website.
- Customers complain about malicious redirects.
- Sensitive info like login, banking details, etc up for sale on the darknet.
- Gibberish content appears on site due to Japanese Keyword Hack or Pharma Hack etc.
- ‘Your account has been suspended!’ message appears while logging in.
- The Drupal site gets blacklisted by search engines.
- The Drupal website becomes very slow & shows error messages.
- Multiple malicious ads & Pop-ups appear on the site.
- Users refrain from visiting the site due to a lack of trust.
- A Decline in user traffic and revenue.
- New, Rogue admins appear in the login database.
Get the ultimate Drupal security checklist with 300+ test parameters
Drupal Hacked: Examples of Drupal Hack
When Drupal sites are hacked, affected users can be found taking help from the community forums. One such example of hacked Drupal is given in the image below.
Possible Causes of Drupal Hacked
Drupal Hacked: Drupal SQL Injection
Drupal SQLi vulnerabilities can be often found within poorly coded modules. However, an SQLi within the core is pretty rare and dangerous. Such a dangerous flaw was once found within the Drupal core and was termed as ‘Drupalgeddon‘, although Drupal used PDO (PHP Data Object) to separate between a static SQL request and the dynamic values.
$query = $db->prepare("SELECT * FROM users WHERE user = :user AND password = :password");
$account = $query->execute(array(':user' => $_POST['user'], ':password' => $_POST['password']));Everything seems fine as the input is properly sanitized before reaching the database. However, the bone of contention lied within Drupal’s placeholder arrays. These were aimed towards giving flexibility to module developers, as these allowed database queries structure to be altered dynamically.
db_query("SELECT * FROM {node} WHERE nid IN (:nids)", array(':nids' => array(13, 42, 144)));Thereafter, the :nids placeholder would match the number of provided arguments. Like this:
SELECT * FROM {node} WHERE nid IN (:nids_0, :nids_1, :nids_2)This feature combined with PHP indexed arrays could be used to pass parameters such as (GET, POST and cookies). Drupal placeholder arrays would by default assume the $_POST['user'] parameter to be an array. Thereafter, it would use the raw array string indexes to generate the new placeholder names. As a result, the attacker can supply malicious values like Parameter: user[0 #], Value:foo. The, resulting query would be:
SELECT * FROM {users} WHERE user = :user_0 #Thereby the attacker successfully bypasses login authentication. Moreover, the attacker can even create new users by editing the parameter as user[0; INSERT INTO users VALUES ‘MalUser’, ‘Passw0rd!’, ‘Administrators’; #]. It was a highly critical flaw as it affected Drupal’s core. What is more alarming is that a Metasploit module was also released to exploit this!
Drupal Hacked: Drupal Access Bypass
A Drupal access bypass can result in users accessing the resources not intended for them. The latest such vulnerability has been dubbed as SA-CONTRIB-2018-081. The cause for this is a Drupal module named JSON:API module 8.x-1.x for Drupal 8.x. It is primarily used for:
- Accessing Drupal content and configuration entities.
- Manipulating Drupal content and configuration entities.
In this case, it doesn’t carefully check for permissions while responding to certain requests. This can allow malicious actors with insufficient permission to obtain sensitive info. As a result, only the GET requests can be used for this kind of attack.
Drupal Hacked: Drupal Cross-Site Scripting
Vulnerabilities like XSS and SQLi are fairly common in Drupal modules. The latest one in this series is SA-CONTRIB-2018-080. The E-Sign module was found to be vulnerable to XSS. E-Sign module basically allows integrating Signature Pad into Drupal. At the time of writing this article, around 875 sites were using this module. The vulnerability arose due to a lack of input sanitization when a signature is displayed. Thereby, the attacker can test for XSS using the code <script>alert(‘XSS Found!’)</script>. The vulnerable signature field would then spit out the message “XSS Found!”. This vulnerability can be then used by the attacker to:
- Steal user cookies.
- Redirect users.
- Download malware on the end user’s device while visiting the Drupal site.
Drupal Hacked: Drupal Remote Code Execution
Drupal security has been haunted by a series of Drupalgeddon bugs. Drupalgeddon 3 is the latest one found this year. This allows unauthenticated users to run code on the Drupal sites. Although Drupalgeddon 2 also allowed RCE. However, to exploit this, the attacker needed the ability to delete a node. The complete URL looked something like this:
POST /?q=node/99/delete&destination=node?q[%2523][]=passthru%26q[%2523type]=markup%26q[%2523markup]=whoami HTTP/1.1 [...] form_id=node_delete_confirm&_triggering_element_name=form_id&form_token=[CSRF-TOKEN]Here, on the pretext of deleting a node, the attacker injected the whoami command. The second line of code is to check for CSRF token. A CSRF token basically checks if the request has been generated on the same server. Thereafter, the attacker retrieves the form_build_id from the response as seen in the code below:
POST /drupal/?q=file/ajax/actions/cancel/%23options/path/[FORM_BUILD_ID] HTTP/1.1 [...] form_build_id=[FORM_BUILD_ID]This finally triggers the exploit and the output of Whoami command is displayed. Therefore, the attacker can execute all kinds of commands to manipulate the server. What makes this RCE bug more severe is that exploit for this has already been released!
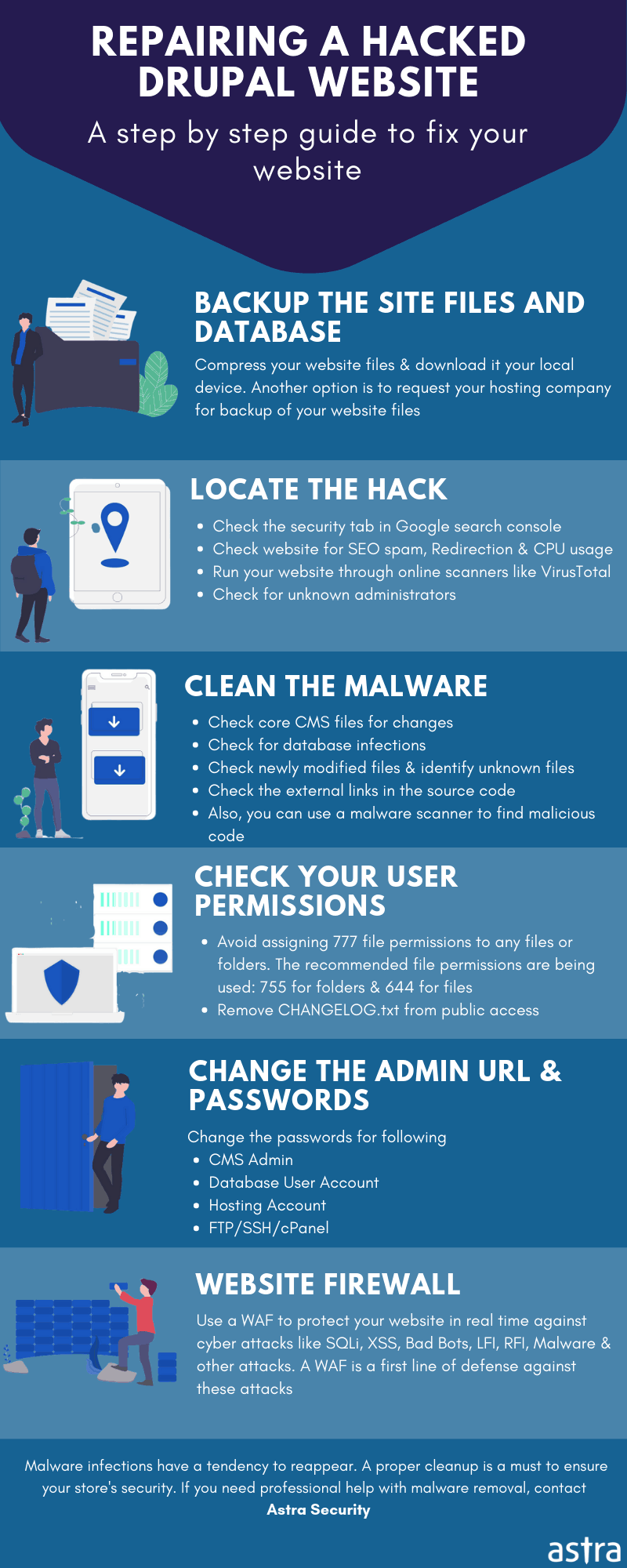
Cleaning Hacked Drupal Website: Steps to Clean Drupal Malware
Detect Infection
Use Google Diagnostics
When your Drupal site is hacked, it is often the case that search engines like Google blacklist it. Therefore, the diagnostics tools of Google can be used to identify the type and cause of infection. Google Transparency Report is helpful in such cases. To check that:
- Visit the Safe Browsing Site Status website from the following link.
- On this page, find the ‘Check Site Status’ option.
- Finally, enter your site URL below it and click on the ‘Search’ button.
- This will give the info regarding spam redirects etc. in case your site is infected. Identify the cause of Drupal infection and work towards its removal.
Scan Your Site
In order to detect the infected pages, scan your site. There are plenty of free options available like VirusTotal. Or, you can compress the entire file into a .zip file and upload it for scanning. However, free security solutions may not give you the desired results, it is therefore recommended to contact experts for malware removal.
Check Modified Files
Often, the backdoors infecting your Drupal site may modify the Drupal core files. File modification of Drupal site can be checked by the following steps:
- Connect to your Drupal site via SSH.
- Create a new directory using this command: mkdir drupal-y.x. Replace ‘y’ with your Drupal series i.e. 7,8,9. and replace ‘x’ with your Drupal release i.e. 4.7.1, 2.1.3, etc.
- Navigate to that directory using the command:
cd drupal-y.x - Download a fresh copy of your Drupal version by the command:
wget https://github.com/drupal/core/archive/y.x.tar.gz - Now, extract the tar.gz file using the command:
tar -zxvf core-y.x.tar.gz - Finally compare the difference between core files by the command:
diff -r core-y.x ./public_html
Alternatively, this can also be done by logging into the site via SSH and running the following command:
find ./ -type f -mtime -20
This command will list all the files modified in the last 20 days. Check the modified dates of the files and if there is anything suspicious, scan that file for malware.
Check User Logs
User logs can help you identify any suspicious logging into your site by the hackers. To do so:
- Login to the Administrative page of your Drupal site.
- From the Menu, Click on the option ‘People’
- Review the users present in this list and also see the ‘Last Access Time’ of every user. If you find any suspicious logins, proceed to find the vulnerability in your site.
Clean Infected Files and Remove Obfuscated Code
After the infected pages have been identified, the infection may be partial (some code in a core file) or an entire file. If the file contains gibberish characters, it could be due to the fact that most of the time, attackers tend to obfuscate the code in a format unreadable to humans. Base64 format is very popular among the attackers. To remove such code:
- Log into your site via SSH.
- Thereafter, check for base64 code using the command:
find . -name "*.php" -exec grep "base64"'{}'; -print &> hiddencode.txt.
This code would scan for base64 encoded code and save it inside hiddencode.txt. - Upload the text from hiddencode.txt to online services like the one in this link for further analysis.
- Click on the ‘Decode’ option on this site. This would display the original code.
- Other obfuscations like FOPO can also be decoded using online services.
- In case the infection is in an entire file which is not part of the core package. Delete the file.
- In case of partial infection in a core file, if you are able to identify the malicious code, delete it. Otherwise, comment it out and get help
Disable Drupal Backdoors
Drupal backdoors can be found hidden in folders like: /modules, /themes, /sites/all/modules, and /sites/all/themes. Detecting them is not easy as often the code may be obfuscated. To find such code, follow the steps mentioned above in “Clean Infected Files and Remove Obfuscated Code”. Also, these backdoors use certain PHP functions.
To disable those functions, follow these steps:
- Log in to your site and open the file manager.
- Browse and open the php.ini file.
- Add the following code to that file:
disable_functions = “show_source, system, shell_exec, passthru, exec, popen, proc_open, allow_url_fopen, eval”
Clean Drupal Database
The Drupal database is often targeted by malware. To clean the database of your infected Drupal site, follow these steps:
- Log into your Drupal site via the Administrator panel.
- Navigate to Data Access>Drupal Database
- Here, in the search bar, search for the suspicious links or content visible during malware scans.
- Open the table that contains those spammy contents and links. Thereafter, manually remove the content.
- When done, verify if the site is still working and remove any other database management tools.
Drupal Security: Block out Attackers
Ensure that no log-in credentials have been compromised. Reset the password to your Drupal site after the malware cleaning is done. To change your passwords, login to your Drupal site.
Using phpMyAdmin
- If you use have phpMyAdmin installed, Navigate to cPanel>Databases box>phpMyAdmin.
- Thereafter, select the Drupal database and click on the SQL tab.
- Now, in the text field enter the following command:
update users set pass=md5(’YOURPASS’) where uid = 1; - Replace ‘YOURPASS’ with the password you wish to set and finally click on Go!
Using Drush
- To manage your site via Drush, ensure that the Drush module is installed.
- To use Drush, connect to your site via SSH.
- Now, for Drupal-8 users, run the following command:
drush user-password UserName --password="your-new-password". - For Drupal-9, run the following command:
drush user:password UserName "your-new-password"
Here, replace the ‘UserName with the User of your Drupal site and ‘your-new-password’ with the password you wish to set. Make sure, the password is secure and has a good combination of alphabets, numbers, and characters.
Drupal Security: Restoring Files
Restore the infected pages from a backup. If the backup is unavailable then use a fresh copy. After the files are cleaned then clear your cache in the following manner:
- Login to your Drupal site via SSH.
- From the terminal, run the following command:
drush cache-rebuild( for Drupal 8)
or
drush cache-clear all(for Drupal 7).
In case your Drupal site is blacklisted by Google or your hosting provider, submit the site for review.
Drupal Hacked Mitigation
Protect Sensitive Folders
It is important to block access to sensitive folders. This can be done through the following steps:
- Login to your site and open the file manager.
- Create a new file titled .htaccess inside the folders you wish to protect.
- Within that file insert the following code:
Order Deny,Allow
Deny from all
Allow from 22.33.44.55
This snippet of code would deny access to the visitors of those particular folders. Here, the last line of code specifies which IPs to allow. Also, look inside modified .htaccess files too. In case any such file is found make it a priority to clean it first.
Update and Backup
Ensure that you are using the latest version of Drupal. The Drupal security team updates critical flaws with each new update. This can be verified using the changelog. Moreover, avoid using unreputed plugins as they are likely to contain buggy code. Make sure to create a copy of the site. This could come in handy to restore the site after an attack. Updates and backups are the cheapest and most effective methods to securing a Drupal site.
Security Audit
A security audit can reveal critical loopholes within the Drupal site. Not all web admins can be an expert in security. Therefore services like Astra can take care of security for the web admins. Astra security audit and pen-testing can responsibly disclose severe threats on the site.
This can allow web admins to take precautionary measures to prevent hacked Drupal sites. The Astra security audit simulates real-time attacks within a secure environment so that no harm is done to the site and at the same time, critical vulnerabilities can be found. Security audits like Astra’s can find common vulnerabilities like OWASP Top 10 within the Drupal site.
Drupal Malware Scanner and Firewall
New vulnerabilities are uncovered in Drupal each month. However, this doesn’t imply that Drupal sites will remain insecure. A firewall can prevent attackers from exploiting these flaws even if the Drupal site is vulnerable. However, it is important to choose the right firewall out of the multiple available ones on the market. Astra firewall is the one that stands out on all the parameters. It is highly robust and scalable. This means, be it small blogs or large e-commerce sites, Astra can secure them all. Moreover, Astra can honeypot the attackers and block common attacks.
The Astra Drupal malware scanner can detect malware from hacked sites within minutes. It will also fetch file differences for you which you can delete with a simple click of a button if they are malicious.