Invicti vs. Acunetix: features, pricing & security compared
Compare Invicti and Acunetix in terms of vulnerability detection accuracy, compliance mapping, and workflow integration depth, with detailed insights into deployment flexibility and pricing models.


Astra vs. Invicti vs. Acunetix








































































Still evaluating? Let us help you make the right call.
Get StartedWhy choose Astra over Invicti and Acunetix
Astra puts your ahead by finding and fixing every single security loopholde
with our hacker-style pentest.
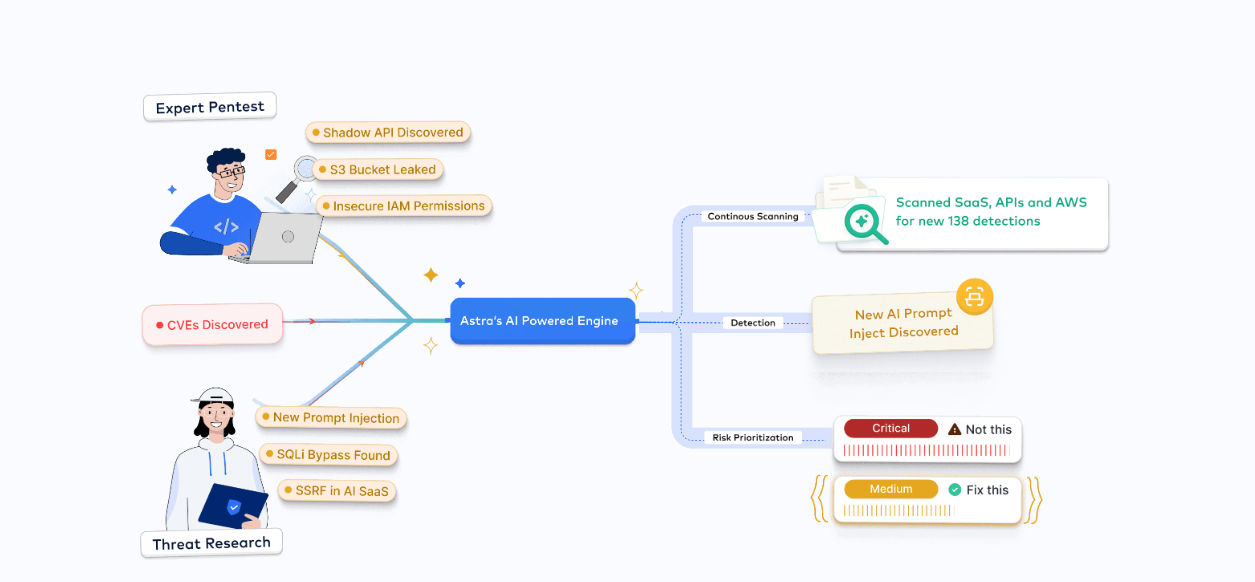
AI-Powered Intelligence
- Run 15,000+ tailored AI test scenarios to your unique app
- Contextual remediation advice at your fingertips
- Continuously improves detection accuracy through context-aware analysis and evolving ML models trained on real-world vulnerability patterns.
Compliance-First Approach
- Audit-ready reports aligned with ISO, PCI, SOC 2, HIPAA, GDPR, OWASP, NIST, and more.
- Expert support to simplify assessments and pass audits faster.
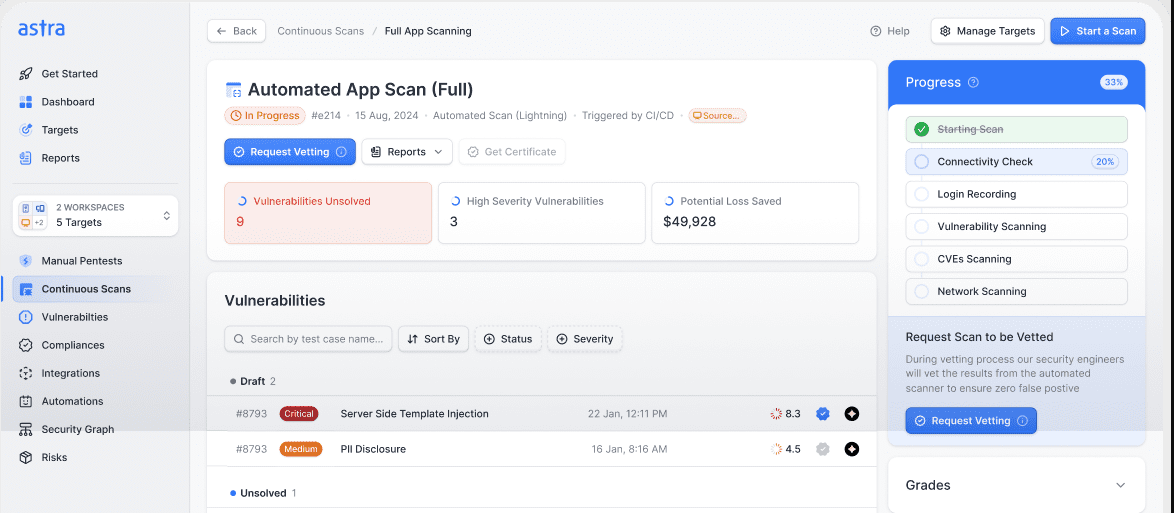
DevOps Integration
- Integrate into CI/CD with GitHub Actions, GitLab CI, Jenkins, Bitbucket, and more.
- Automate scans, send vulnerability alerts via Slack
- Create JIRA tickets, all without leaving your pipeline.

End-to-End, Fully Managed Platform
- Continuous, scheduled scans and pentests for web apps, API, and cloud without manual setup or tuning.
- Expert-tuned accuracy with optimized scanners to reduce false positives.
- Vulnerabilities triaged and mapped to real business impact.
- Auto-generated compliance-grade summaries with remediation guidance and automated rescans for verification.
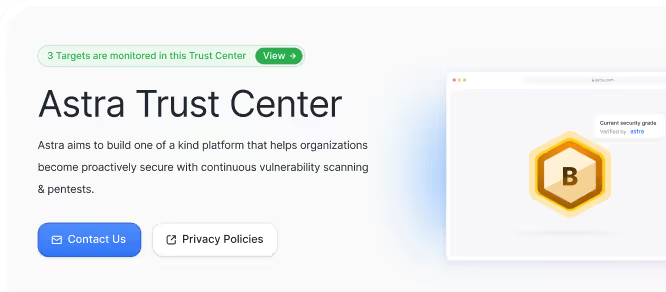
Pentest Certificate & AI-built Trust Center
- Publicly verifiable certifications with shareable links.
- Demonstrate your security commitment.
- Build client and partner trust.
- Summarize your security posture for easy sharing with customers and auditors

Discover why leading companies choose Astra over Invicti vs Acunetix.
Book your demo





Find and fix vulnerabilities before attackers do:
start continuous, accurate scanning today.
Get StartedOur pentesters? World class, certified &
contributors to top security projects
vulnerabilities discovered
and counting
bad guys do





Trusted by leading security conscious
companies across the world.












































.webp)





Experience zero false positives and seamless integrations with Astra Security PTaaS platform.
Book a demoFrequently asked questions

Both Invicti and Acunetix deliver industry-leading vulnerability detection with accurate findings and automated verification. Invicti targets enterprise clients with advanced automation, scalability, and proof-based scanning to minimize false positives. Acunetix, aimed at SMBs, offers fast, user-friendly scans but with fewer enterprise integrations.

Astra combines automated scanning with expert-led manual penetration testing, conducting over 15,000 test cases. Unlike Invicti and Acunetix, Astra guarantees zero false positives with human validation, provides compliance-ready reports, and seamless CI/CD integration with developer-focused dashboards.

Invicti leads with extensive out-of-the-box integrations, including Jira, Jenkins, GitLab, Slack, and strong enterprise CI/CD support. Acunetix offers core integrations suitable for smaller teams but lacks the broad workflow automation and enterprise readiness of Invicti. Astra supplements automation with personalized remediation support.

Yes, both Invicti and Acunetix support authenticated scanning with credentialed and token-based workflows. However, Invicti’s enterprise focus translates into better handling of large-scale and complex environments, whereas Acunetix is generally easier for SMBs with simpler needs. Astra offers additional manual verification for deeper coverage.

Invicti provides detailed remediation reports and enterprise support services. Acunetix offers strong core support but with fewer enterprise-grade options. Astra enhances remediation with expert validation and hands-on developer assistance via chat and dashboard comments, ensuring fixes are practical and timely.

























.webp)
















.svg)
.svg)





.svg)
.svg)
.svg)



.webp)










