Key Takeaways
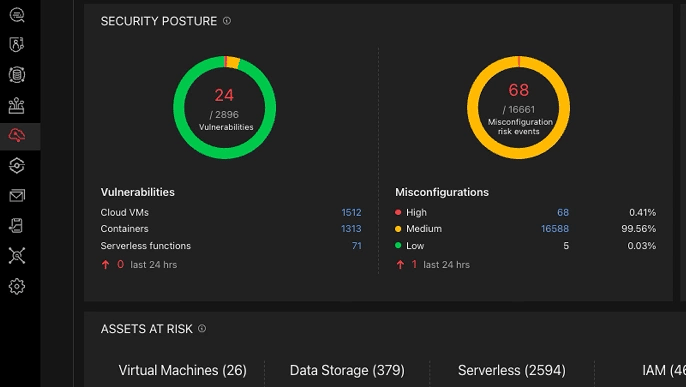
- 80% of companies experienced a cloud security breach in the past year, with the average incident cost of $4.40 million.
- There are multiple types of Cloud security tools, such as CSPM, CWPP, CNAPP, CASB, CIEM, and DSPM. Each addresses a different layer of your cloud stack.
- Detection alone isn’t enough. Tools like Wiz and Prisma Cloud excel at finding misconfigurations, but they can’t tell you which ones an attacker can actually exploit.
- The industry is consolidating toward unified CNAPP platforms that replace fragmented point solutions. If you’re juggling 5+ separate security tools, you’re likely creating the visibility blind spots you’re trying to eliminate.
- Pricing varies quite vividly; from Astra’s $1,999/year per target to Wiz’s $24,000+/year for 100 workloads to Cortex Cloud’s $50K+ enterprise contracts.
- Choosing the right tool comes down to four factors: your cloud providers, compliance requirements, team size, and whether you need detection-level monitoring or offensive validation.
By the end of 2026, the world will have over 200 zettabytes of data on cloud, that’s 200,000,000,000,000 GB! With such humongous amounts of data and the market value for cloud storage crossing the $380 billion mark by 2030, it’s no wonder that cloud security is becoming a top concern for >83% companies worldwide.
This is exactly why choosing the right cloud security tool becomes the difference between a secure business and a multi-million dollar breach. Especially when >69% professionals cite tool and visibility effectiveness as the coin in the air on which the fate of their firm floats.
But with dozens of cloud security solutions flooding the market with each blaring their trumpets, how do you actually pick the right one? That’s precisely what we’ll be sticking to in this guide.
We’ve thoroughly researched and compared the best cloud security tools in 2026 across categories like CSPM, CWPP, CNAPP, and CASB. So shall we?
11 Best Cloud Security Tools (Expert’s Opinion)
- Astra Security
- Wiz
- Palo Alto Networks’ Cortex Cloud
- CrowdStrike Falcon Cloud Security
- Microsoft Defender for Cloud
- Orca Security
- SentinelOne Singularity Cloud Security
- Sysdig Secure
- Check Point CloudGuard
- Zscaler Zero Trust Cloud
- Trend Vision One
Top 3 Tools Comparison
Before diving into all 11 tools, here’s a side-by-side comparison of our top 3 picks to help you spot the differences that matter most.
| Features | Astra Security | Wiz | Palo Alto Cortex Cloud |
|---|---|---|---|
| Primary Category | Cloud Scanner + PTaaS Platform | CNAPP | CNAPP |
| Best For | SMBs to mid-market seeking validation-based cloud security with pentesting | Large enterprises needing comprehensive agentless cloud visibility | Large enterprises wanting a full-lifecycle code-to-cloud-to-SOC platform |
| Cloud Providers Supported | AWS, Azure, GCP | AWS, Azure, GCP, OCI, Alibaba Cloud | AWS, Azure, GCP, OCI |
| Deployment Model | Agentless (read-only API keys) | Agentless (API snapshots) | Hybrid (agent + agentless) |
| Setup Time | Minutes | Minutes to hours | Days to weeks |
| Vulnerability Validation | ✅ Offensive-grade engine proves exploitability | ❌ Detection & prioritization only | ❌ Detection & prioritization only |
| Manual Penetration Testing | ✅ Expert-led pentesting included (PTaaS plans) | ❌ Not available | ❌ Not available |
| Automated Cloud Checks | 400+ cloud-specific config checks, 3,000+ automated tests | 2,300+ misconfiguration rules | 1,000+ built-in policies |
| CSPM | ✅ | ✅ | ✅ |
| CWPP | ❌ | ✅ | ✅ |
| CIEM | ✅ IAM misconfiguration scanning | ✅ Full CIEM | ✅ Full CIEM |
| DSPM | ❌ | ✅ | ✅ |
| Container / K8s Security | ❌ | ✅ (KSPM) | ✅ |
| Attack Path Analysis | ✅ Offensive validation of attack chains | ✅ Security Graph with toxic combinations | ✅ Attack path visualization |
| Web App & API Security | ✅ DAST + API scanning (10,000+ tests) | ❌ | ❌ |
| CI/CD Integration | ✅ Jenkins, GitHub Actions, GitLab CI, CircleCI | ✅ Single policy framework across CI/CD | ✅ Shift-left IaC scanning |
| Developer Tools | Slack, Jira, GitHub, GitLab, Bitbucket | Jira, Slack, ServiceNow, PagerDuty, 40+ integrations | Jira, Slack, ServiceNow, plus Palo Alto ecosystem |
| Compliance Frameworks | SOC 2, ISO 27001, HIPAA, PCI DSS, GDPR, CIS, NIST, OWASP | 150+ frameworks | 100+ frameworks |
| Pentest Certificate | ✅ Publicly verifiable | Depends on the pricing and contract | Depends on the pricing and contract |
| Trust Center | ✅ Astra Trust Center (live, branded compliance hub) | ❌ | ✅Available under Palo Alto offerings |
| False Positive Handling | Zero false positives (expert-vetted) | Low (risk-prioritized via Security Graph) | Moderate (requires tuning) |
| Runtime Protection | ❌ | ✅ (Wiz Defend add-on) | ✅ (agent-based) |
| AI Features | AI-powered remediation assistant | AI-SPM for AI pipeline security | WildFire ML + Cortex XSIAM AI |
| G2 Rating | 4.6/5 (167reviews) | 4.7/5 (756 reviews) | 4.1/5 (111 reviews) |
| Gartner Peer Insights | 4.5/5 | 4.7/5 (Customers' Choice 2025) | 4.0/5 |
| Pricing Model | Flat per-target/year (predictable, no per-asset fees) | Per-workload/year (custom quotes) | Credit-based licensing (custom enterprise) |
| Starting Price | $1,999/year (Scanner); $5,999/year (Pentest) | ~$24,000/year (100 workloads, Essential) | Enterprise-only (typically $50K+/year) |
| Free Tier / Trial | $7/week trial | Free demo only | Free foundational CSPM (limited) |
| Ideal Team Size | 1–50 person security/dev team | 10–100+ person security org | 20–200+ person security org |
| Notable Customers | Dream11, HackerRank, Loom, SpiceJet, CompTIA | 50%+ of Fortune 100 | Fortune 500 enterprises |
| Unique Differentiator | Only platform combining continuous offensive pentesting + automated scanning with proof of exploitability | Fastest agentless deployment with Security Graph for toxic combination analysis | Most comprehensive single-vendor code-to-cloud-to-SOC stack |
Top 11 Cloud Security Tools 2026
1. Astra Security
G2 rating: 4.6/5 [167 reviews]
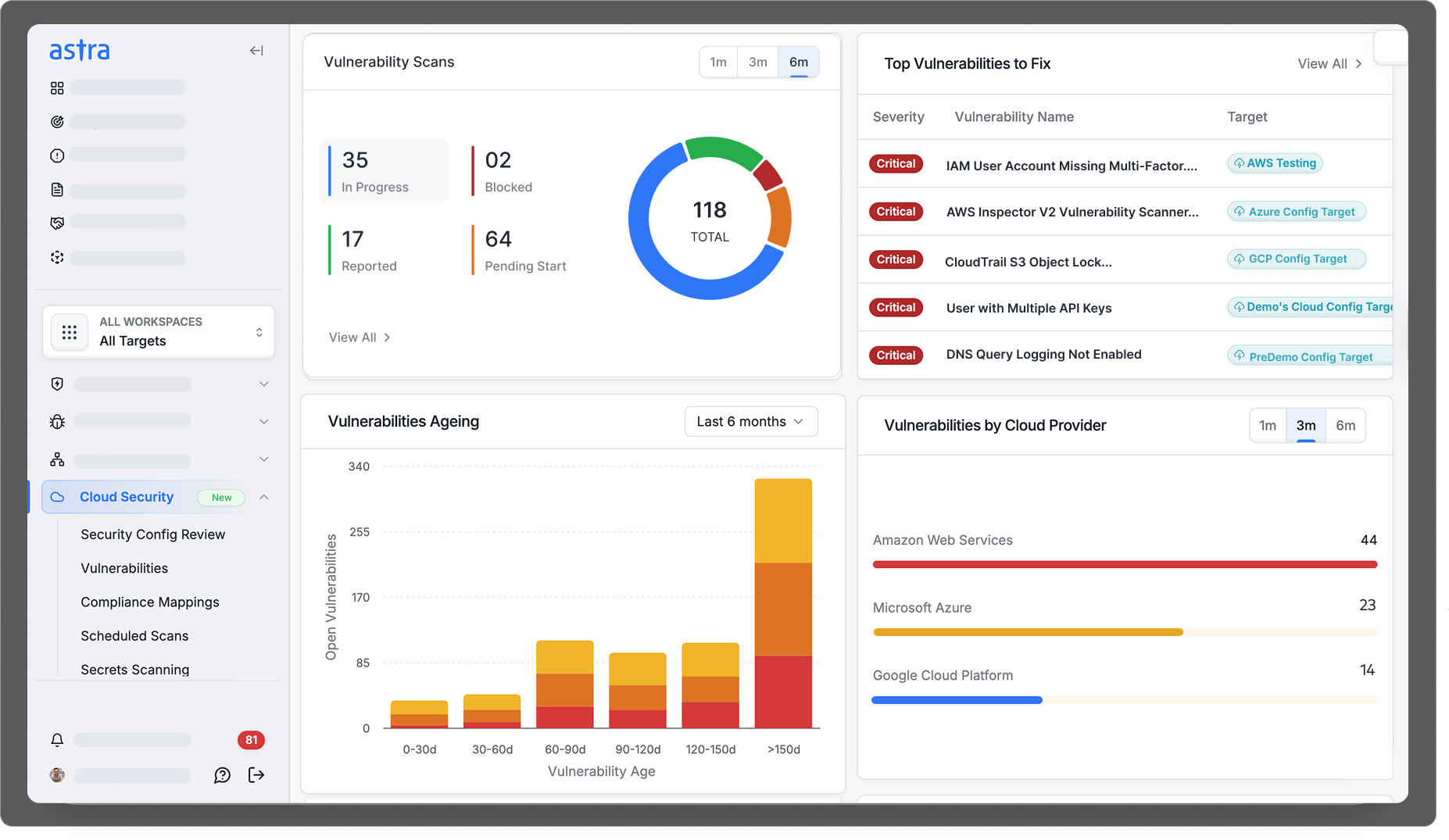
Key features:
- Offers AI-Powered Pentest Platform + DAST Scanner + Cloud Vulnerability Scanner + API Security platform
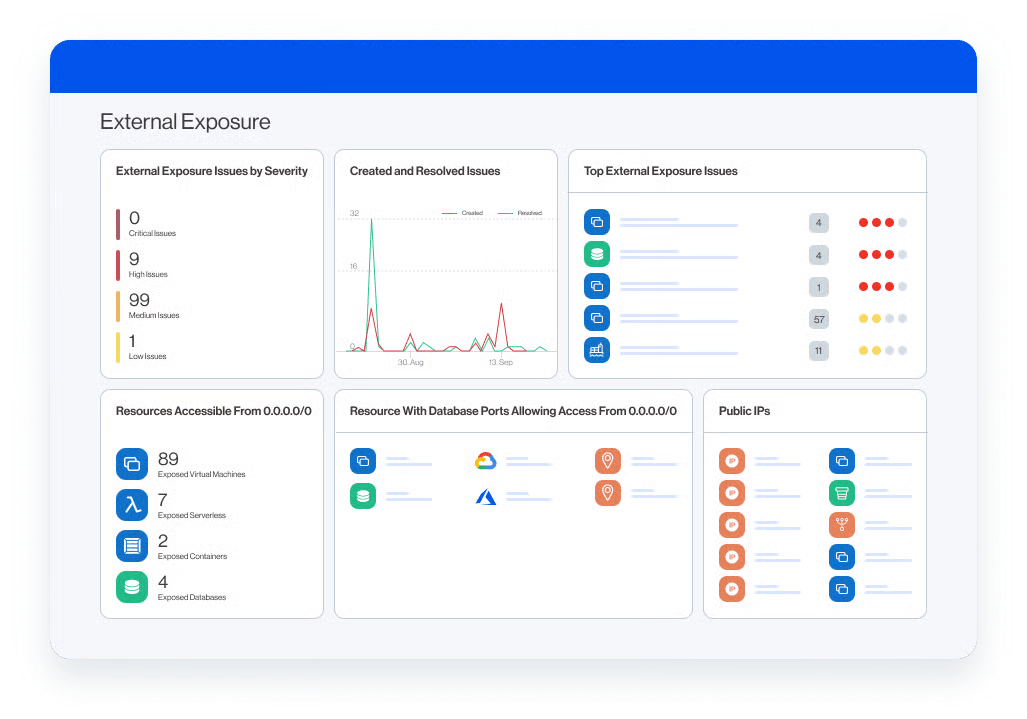
- Unified platform covering web apps, APIs, cloud infrastructure (AWS/Azure/GCP), mobile apps, and network security from a single dashboard
- Combines AI-powered automated scanning with manual vetting. One of the best platforms that blends both continuously
- Cloud Vulnerability Scanner (launched December 2025): agentless, continuous multi-cloud scanner with 400+ cloud-specific configuration checks and 3,000+ automated vulnerability tests
- Security professionals with various certifications & CVEs [OSCP, CEH, eJPT, eWPTXv2, and CCSP (AWS)]
- An offensive-grade validation engine that doesn’t just detect misconfigurations, but also proves whether they’re actually exploitable
- 400+ test cases based on OWASP and a publicly verifiable pentest certificate, and
- Deep CI/CD integration (Jenkins, GitHub Actions, GitLab CI, CircleCI), plus Slack and Jira for developer-first workflows
Compliance support: SOC 2 (including Type II), ISO 27001, HIPAA, PCI DSS (Astra is a PCI Approved Scanning Vendor), GDPR, CIS Benchmarks, NIST, OWASP Top 10, SANS 25. Astra is itself ISO 27001 certified and CREST-accredited.
Strengths:
- CXO-friendly dashboard with a dedicated CSM
- Active contributor to OWASP and other similar open-source projects.
- Conducts compliance-specific scans as well
- Scans are performed in the cloud, ensuring no strain on your servers
- The vulnerability management dashboard allows your team to engage directly with our experts, facilitating smoother collaboration and remediation
- Validation-first approach directly addresses the #1 pain point of alert fatigue; proves exploitability rather than just detecting misconfigurations
- Predictable pricing without scale-based fees (no per-asset charges that balloon unpredictably)
- Very high user satisfaction: 4.6–4.7/5 on G2 (165+reviews), 4.8/5 on Capterra (107 reviews), 4.5/5 on Gartner Peer Insights
- Notable customers include HackerRank, Loom, CompTIA, Dream11, SpiceJet, and organizations covering the US, Europe, and Asia.
Pricing:
- Scanner: $1,999/year per target
- Pentest (PTaaS): $5,999/year per target (includes manual pentest + cloud config review + compliance reporting + pentest certificate)
- Enterprise: Starting from $3,999/year per target (custom)
Best suited for: SMBs to mid-market enterprises needing continuous, validation-based cloud security with compliance reporting — especially SaaS companies, fintech, healthcare, and e-commerce organizations pursuing SOC 2, ISO 27001, or PCI DSS compliance.
2. Wiz
G2 rating: 4.7/5 [756 reviews]
Category: CNAPP | Acquired by Google Cloud in 2025
Key features:
- Agentless scanning via read-only API snapshots
- Its Cloud Native Application Protection Platform (CNAPP) consolidates CSPM, KSPM, CWPP, Vulnerability management, IaC scanning, CIEM, and DSPM into a single platform.
- Wiz drives visibility, risk prioritization, and business agility.
- Unified CNAPP (CSPM/CWPP/CIEM/DSPM/KSPM), AI-SPM for AI pipeline security, multi-cloud support (AWS, Azure, GCP, OCI, Alibaba Cloud)
- 2,300+ misconfiguration rules and 150+ compliance frameworks.
Strengths:
- Fastest deployment and time-to-value (visibility within hours)
- Superior risk prioritization through “toxic combinations.”
- Used by 50%+ of Fortune 100 companies and nearly $1B ARR.
Limitations:
- Premium pricing ($24K–$38K/year for 100 workloads)
- An agentless-only model means no real-time inline blocking
- Google acquisition raises multi-cloud neutrality concerns.
Pricing:
- Per-workload, custom quotes.
- Via AWS Marketplace: Essential ~$24K/year (100 workloads), Advanced ~$38K/year (100 workloads).
Best for: Large enterprises with complex multi-cloud environments needing rapid, comprehensive visibility.
3. Palo Alto Networks’ Cortex Cloud
G2 rating: 4.1/5 (111 reviews)
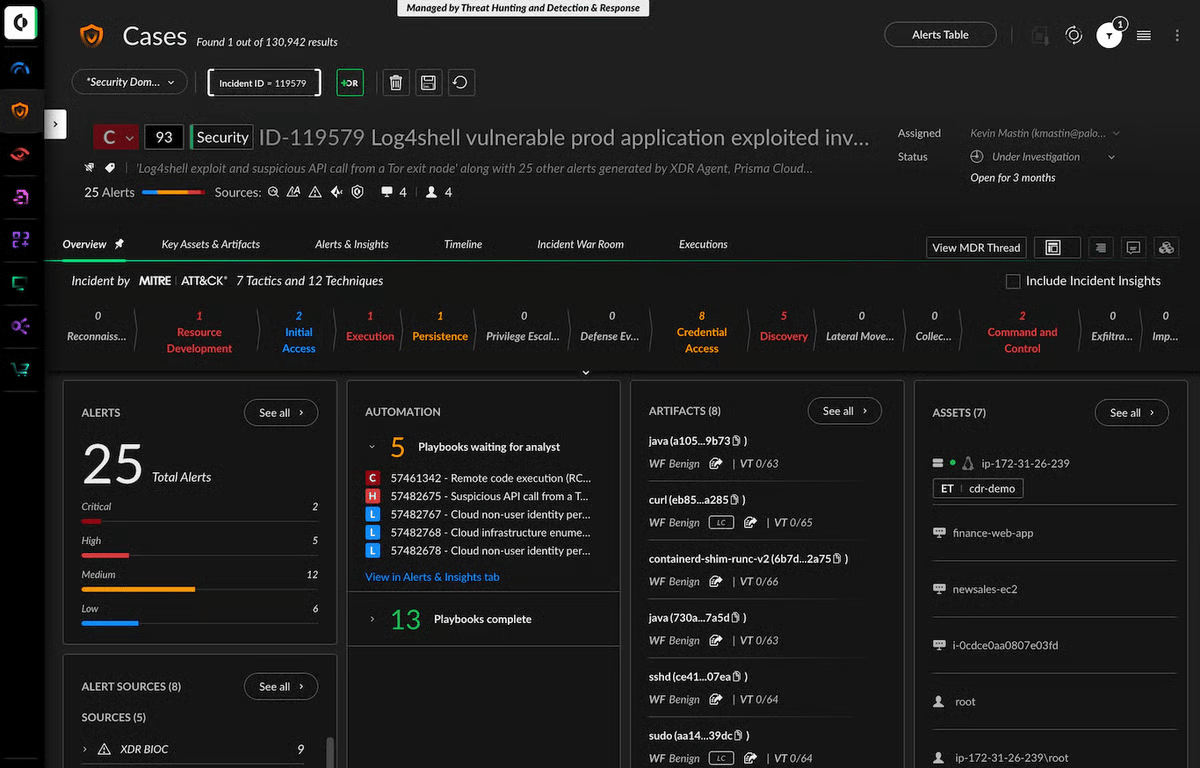
Category: CNAPP
Key features:
- Full lifecycle code-to-cloud-to-SOC platform
- Integrates CSPM, CWPP, CIEM, DSPM, AI-SPM, and CDR
- Hybrid agent/agentless architecture
- Cortex Cloud integration with SIEM (XSIAM)
- Powered by Unit 42 threat intelligence and WildFire malware prevention
Strengths:
- Most comprehensive and mature CNAPP with the broadest feature coverage
- Strong Palo Alto ecosystem integration with ~$700M+ ARR.
- Leader in Forrester Wave: Cloud Workload Security Q1 2024
- Leader in IDC MarketScape for CNAPP
Limitations:
- Expensive and complex
- Integration of modules from multiple acquisitions may come across as a little siloed
- Requires agent deployment for full runtime protection
Pricing: Enterprise-only, credit-based licensing. Premium tier.
Best for: Large enterprises seeking an all-in-one platform, especially existing Palo Alto customers.
If you’re looking for enterprise-grade cloud security without enterprise-grade complexity, try out our Comprehensive Cloud Security scanner at just $7 for a week. See Astra’s transparent pricing
4. CrowdStrike Falcon Cloud Security
G2 rating: 4.6/5 [81 reviews]
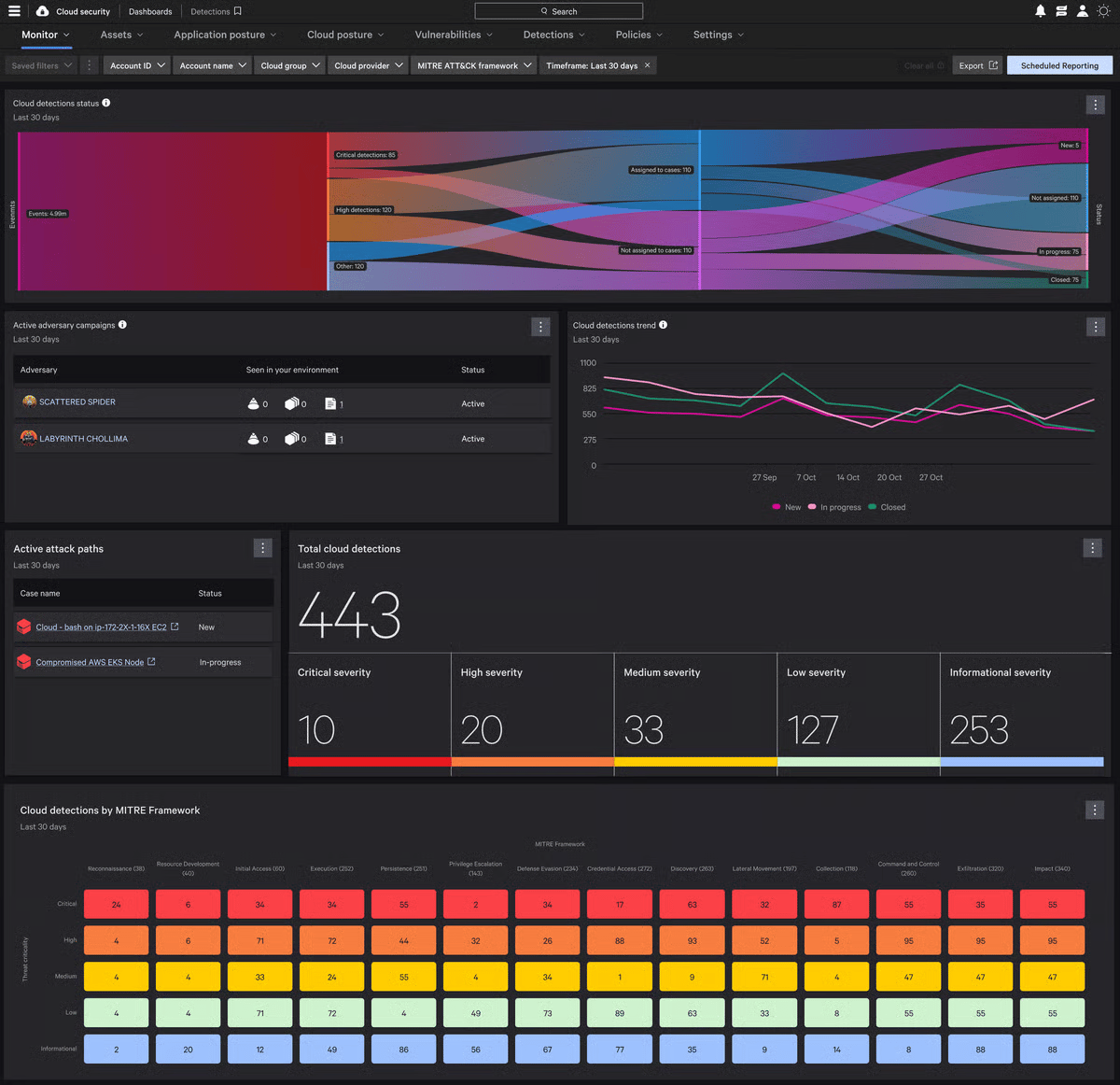
Category: CNAPP (with CWPP/EDR heritage)
Key features:
- Unified Falcon Platform single agent/console for endpoint + cloud + identity
- Real-time runtime protection using behavior-based Indicators of Attack (IOAs)
- OverWatch 24/7 managed threat hunting
- Charlotte GenAI assistant with 98%+ accuracy
Strengths:
- Unparalleled real-time threat detection extending proven EDR leadership into the cloud
- Strong adversary-focused threat intelligence
- Cost-effective for existing CrowdStrike customers
- Representative Vendor in the 2025 Gartner Market Guide for CNAPPs
Limitations:
- Cloud security evolved from endpoint heritage and thus may lack cloud-native depth
- Follows an agent-based approach, which may not fit every workload
- UI comes across as less intuitive for cloud-specific tasks
Pricing: Per-device annual subscriptions (Go: $59.99, Pro: $99.99, Enterprise: $184.99/device/year). Cloud modules are priced separately depending on enterprise agreements and negotiations.
Best for: Mid-to-large enterprises needing unified endpoint + cloud security with real-time protection and threat hunting.
5. Microsoft Defender for Cloud
G2 rating: 4.4/5 [303 reviews]
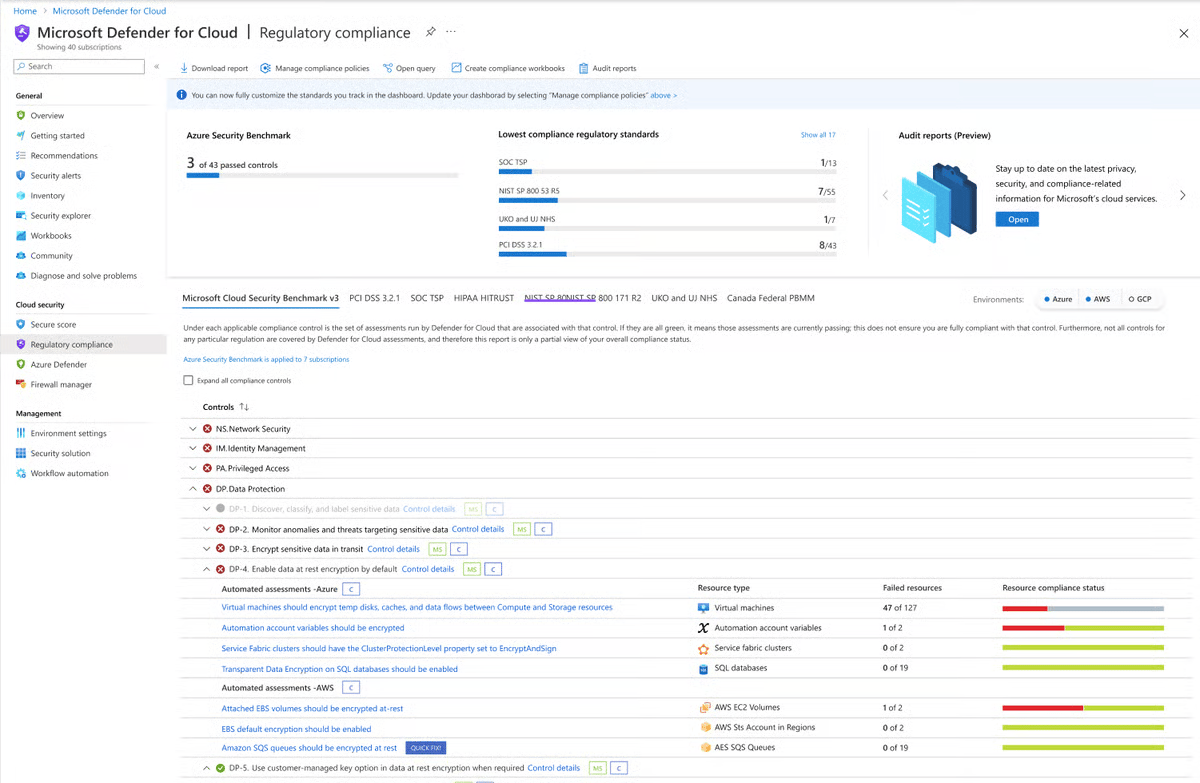
Category: CNAPP / CSPM / CWPP
Key features:
- Deep Azure integration with Microsoft security ecosystem (Sentinel SIEM, Entra ID)
- Multi-cloud CNAPP supporting Azure, AWS, GCP
- Free foundational CSPM with Secure Score
- Copilot for Security AI integration
Strengths:
- Free tier for Azure-native organizations.
- Seamless Microsoft ecosystem integration.
- #1 ranked CWPP on Gartner Peer Insights.
- Leader in IDC MarketScape: Worldwide CNAPP 2025
Limitations:
- Best optimized for Azure, but a complex setup for multi-cloud
- Advanced features ($5–15/server/month) can escalate costs.
- Users on G2 have raised concerns about false positives and delayed detections
Pricing:
- Free tier (foundational CSPM). Paid: per-resource ($5–15/server/month).
- 30-day free trial for paid plans.
Best for:
- Organizations heavily invested in Microsoft/Azure, from SMBs using the free tier to large enterprises.
6. Orca Security
G2 rating: 4.6/5 [224 reviews]
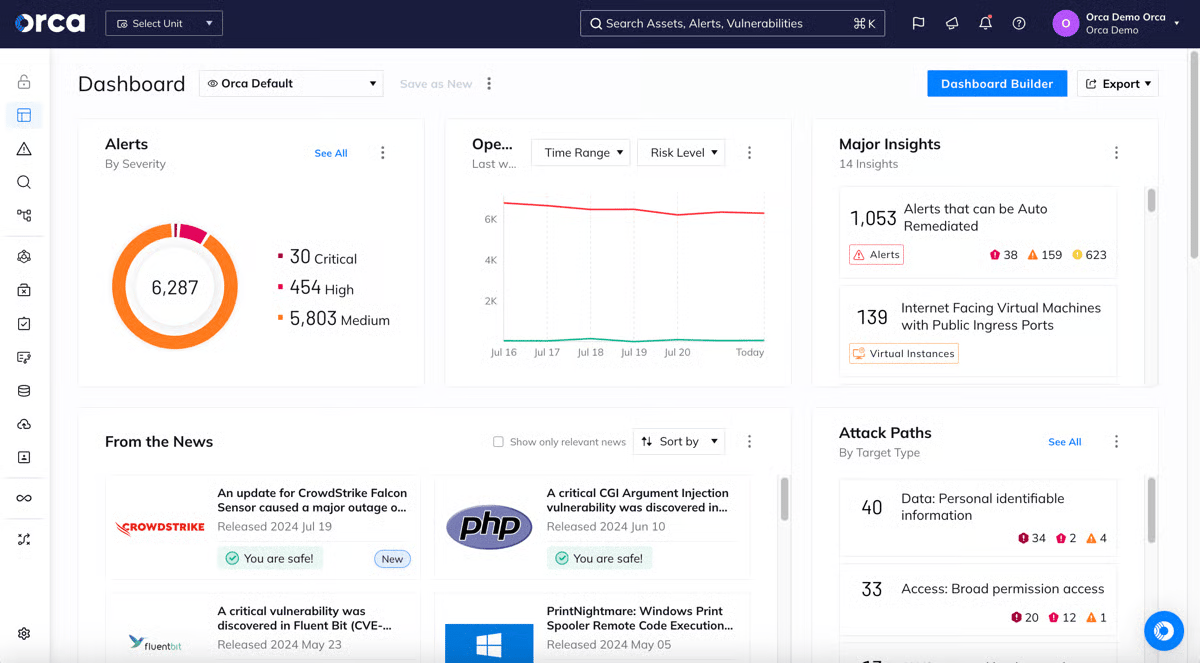
Category: CNAPP (Agentless-first)
Key features:
- Patented SideScanning™ technology; agentless scanning of all workloads via a single license Unified data model for assets, compliance, and risks.
- Consolidates many point solutions in one platform, including: CSPM, CWPP, CIEM, Vulnerability Management, Container and Kubernetes Security, DSPM, API Security, CDR, Multi-cloud Compliance, Shift Left Security, and AI-SPM
- Attack path analysis with data sensitivity context
- 100+ compliance frameworks
- GenAI-powered investigation
Strengths:
- Fastest deployment (100% agentless, zero performance impact)
- Unified platform from a single codebase (not stitched from acquisitions)
- Strong CDR capabilities (#2 on PeerSpot) and Representative Vendor in the 2025 Gartner Market Guide for CNAPPs
Limitations:
- Agentless-only limits real-time inline blocking
- Alert volume can be high
- Less mature in code-level security
Pricing:
- Enterprise-only, custom pricing. No public pricing available.
Best for:
Mid-to-large enterprises wanting the simplest, fastest-to-deploy agentless CNAPP
7. SentinelOne Singularity Cloud Security
G2 rating: 4.9.5 [112 reviews]
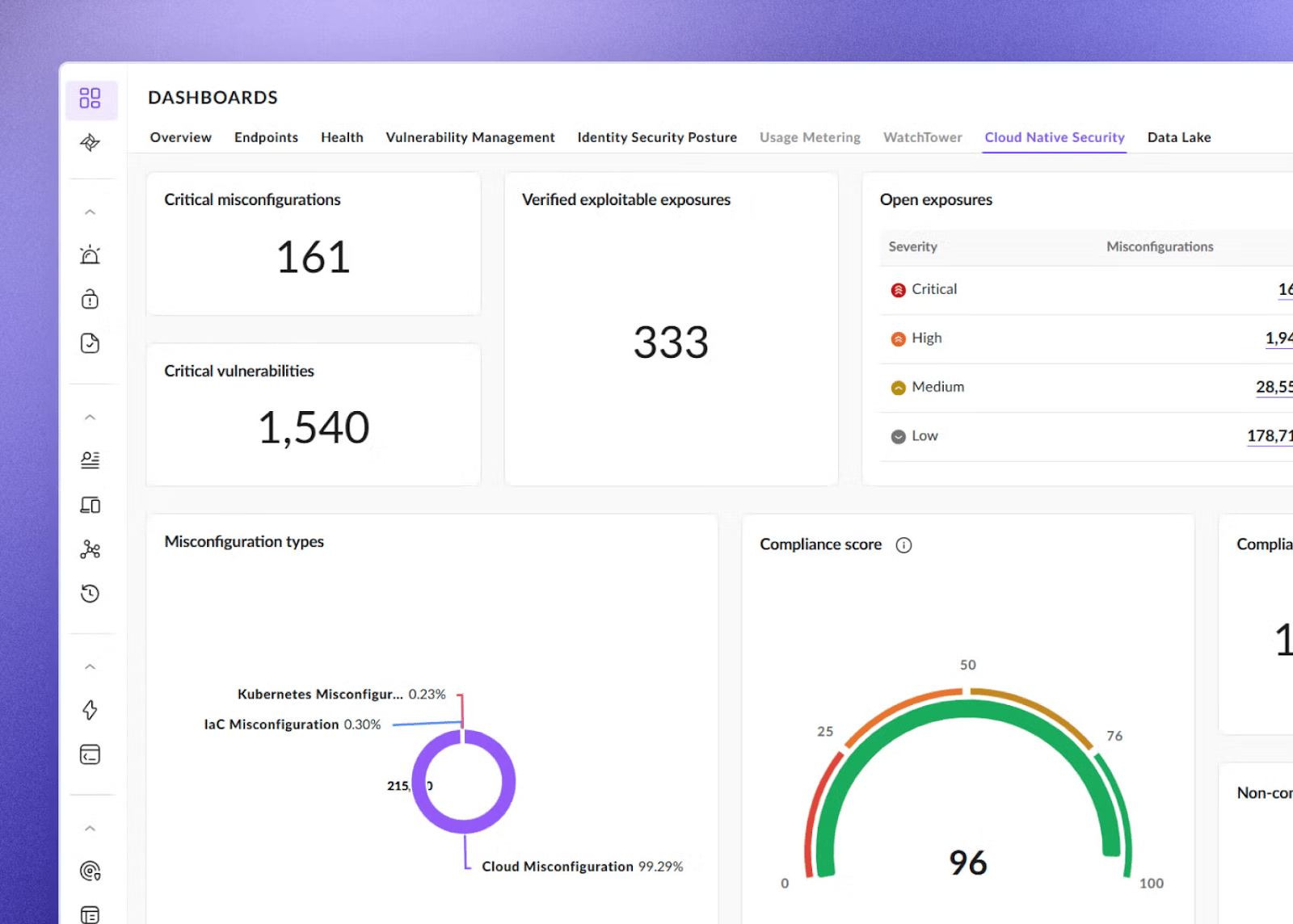
Category: CNAPP / CWPP
Key features:
- Autonomous AI-powered prevention, detection, containment, and remediation without human intervention
- Unified agent for endpoints + cloud
- Purple AI GenAI analyst. Patented Storylines™ forensic technology
- Vigilance MDR 24/7 managed service
Strengths:
- 3.5-minute average detection time
- 100% protection in MITRE evaluations
- Unified endpoint-to-cloud security
- Leader in 2025 Gartner Magic Quadrant for Endpoint Protection Platforms (5 consecutive years).
Limitations:
- Cloud security offering newer than established CNAPP leaders
- Agent-based approach is still maturing in agentless capabilities
- Narrower threat intelligence vs. CrowdStrike
Pricing:
- Per-endpoint: Singularity Complete $179.99/device/year
- Commercial $229.99/device/year
- Cloud security is priced separately
Best for:
Organizations want unified endpoint + cloud under autonomous AI-powered protection.
8. Sysdig Secure
G2 rating: 4.8/5 [111 reviews]
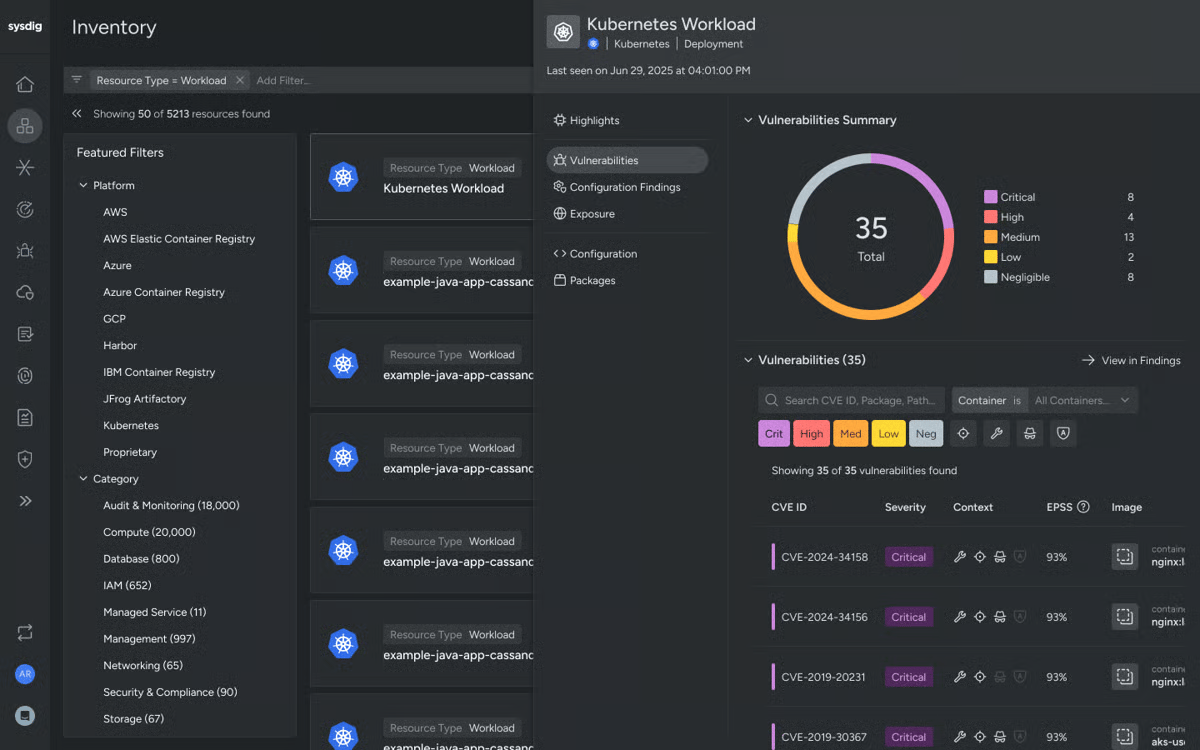
Category: CNAPP (Runtime-focused / Container Security)
Key features:
- Real-time runtime threat detection using the open-source Falco engine at the kernel level
- Runtime Insights that highlight only issues in packages actively loaded and in use
- Sysdig Sage AI analyst. Open-source foundation (Falco is a CNCF-graduated project)
- Connects signals across runtime, identity, and posture to eliminate blind spots and reduce tool sprawl
Strengths:
- Consolidates CSPM, CWPP, CIEM, vulnerability management, and threat detection into a single open and real-time platform
- Best-in-class runtime and container security with 5-second threat detection benchmark
- 700+ enterprise customers (Goldman Sachs, SAP Concur, Experian)
- Transparent open-source heritage
- Representative Vendor in 2025 Gartner Market Guide for CNAPPs
Limitations:
- Requires agent deployment
- Features are bundled and cannot be purchased individually
- Managing large teams requires custom tooling
Pricing:
- Per-host, per-month subscription
- Custom enterprise quotes. Mid-range pricing
Best for: Cloud-native organizations running extensive Kubernetes and container workloads needing real-time runtime detection.
9. Check Point CloudGuard
G2 rating: 4.5/5 [167 reviews]
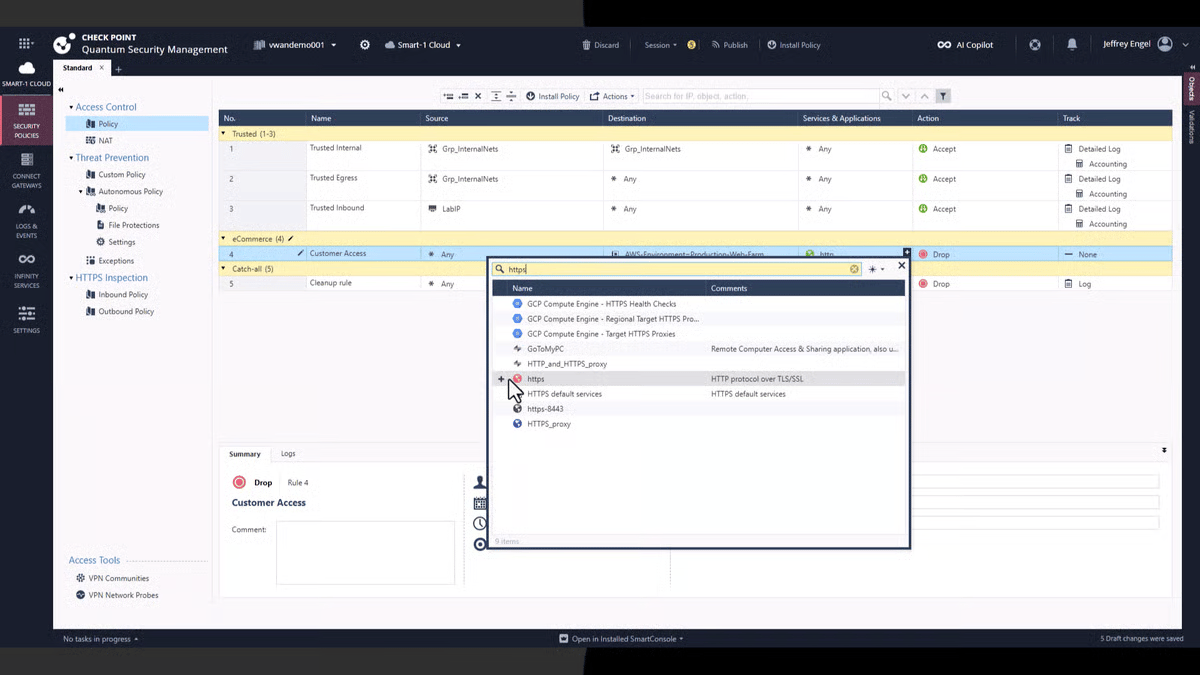
Category: CNAPP / CSPM /WAF/ Cloud Network Security
Key features:
- CSPM with auto-remediation and network topology visualization
- Cloud Network Firewall extending on-premises Check Point policies
- Context-Based Web Application and API Protection (WAF)
- Shift CNAPP Left to Secure Applications in the CI/CD Pipeline
- Context Graph Visualization & Cloud Detection and Response
Strengths:
- Their platform offers a suite of security features, including a firewall, DLP, intrusion prevention system (IPS), application control, IPsec VPN, URL filtering, antivirus, anti-bot protection, threat extraction and emulation, etc.
- Industry-leading threat intelligence via ThreatCloud; natural extension for existing Check Point customers; strong compliance automation
Limitations:
- Built from multiple acquisitions, and thus the platform may feel fragmented
- Steep learning curve
- Agentless scanning is limited in some clouds.
Pricing:
- Custom enterprise pricing based on modules
- Generally competitive vs. pure-play CNAPPs
Best for:
- Enterprises with existing Check Point infrastructure extending to multi-cloud.
10. Zscaler Zero Trust Cloud
G2 rating: 4.5/5 [42 reviews]
Category: SASE / CASB / CNAPP (Zero Trust)
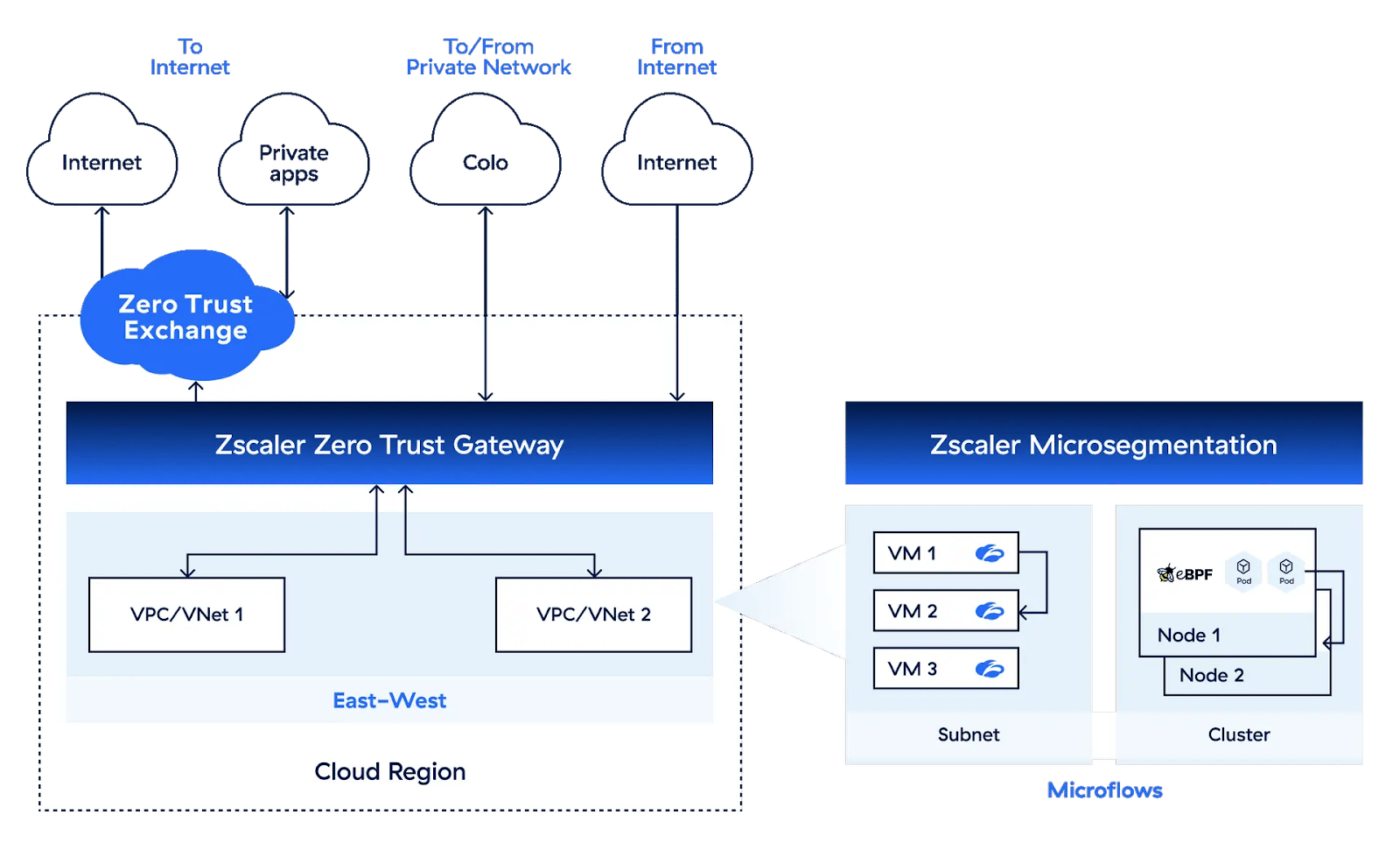
Key features:
- Zero Trust Exchange (world’s largest security cloud, 185+ countries)
- Posture Control CNAPP — agentless correlation across security engines.
- Integrated CASB and DLP with GenAI data protection.
- Zero Trust Network Access replacing VPNs.
- Well, their SSE (Security Service Edge) is now Quantum ready, allowing you to inspect post-quantum cryptography (PQC) traffic and maintain visibility, control, and protection
Strengths:
- Leader in Zero Trust architecture
Comprehensive SASE platform - Delivers the entire gateway security stack as a service
- Strong AI-powered threat correlation
Limitations:
- Posture Control CNAPP is newer and less mature than dedicated platforms
- Primarily known for network/access security
- Complex multi-cloud CNAPP deployments
Pricing:
- Per-user/year (ZIA ~$72–200/user/year; ZPA ~$72–120/user/year).
- Posture Control custom. Enterprise spend: ~$28K–286K/year.
Best for: Organizations prioritizing Zero Trust and SASE transformation with large remote/hybrid workforces.
11. Trend Vision One
G2 rating: 4.7/5 [225 reviews]
Category: CNAPP / CWPP / XDR
Key features:
- CSPM, ASM, EASM, CIEM, AI-SPM, DSPM, IaC/template scanning, agentless vulnerability and malware scanning, attack path analysis, and API risk visibility.
- Unified Vision One platform consolidating endpoint, cloud, email, network, and identity security with XDR
- Industry-leading CWPP for VMs, containers, and serverless. CSPM (formerly Conformity)
- AI-driven threat intelligence monitoring 45B+ URLs/emails/files
- Strong hybrid cloud support
Strengths:
- Their Trend Vision One Cloud IPS integrates seamlessly with AWS Network Firewall, which is supported by Trend Zero Day Initiative™ (Trend ZDI)
- Decades of hybrid cloud security experience with one of the most mature CWPP offerings
- 100% detection rate in MITRE evaluations
- Reduces operational costs by up to 79%
Limitations:
- Requires agent deployment
- The platform recently transitioned from “Cloud One” to “Vision One” (documentation is still catching up)
- Less cloud-native CNAPP depth vs. Wiz
Pricing:
- Custom/enterprise
- Credit-based licensing with pay-as-you-go options via cloud marketplaces.
Best for:
- Enterprises with complex hybrid cloud environments (on-premises + multi-cloud) that need mature workload protection and XDR
How to Choose and Evaluate Cloud Security Tools
Below, we offer you quick 8-key evaluation criteria you can base your decision on:
- Multi-cloud coverage and integration: Does it support all your clouds (AWS, Azure, GCP) and integrate with existing SIEM, SOAR, CI/CD, and ticketing systems? With 87% of organizations using multi-cloud, consistent cross-cloud coverage becomes essential.
- Unified platform vs. point solution: Check whether a CNAPP platform or specialized tools fit your needs. Unified platforms help reduce silos and thus blind spots.
- Deployment model (agent vs. agentless): While Agentless offers fast deployment and zero performance impact, Agent-based cloud security provides deeper runtime visibility. Also, many leading tools now offer hybrid approaches, but then pricing becomes a moot-point so navigate that after careful internal evaluation and consultation.
- Risk prioritization and context: Your tool should correlate vulnerabilities, misconfigurations, identity issues, and data exposure to surface truly critical attack paths and not simply generate alerts
- Compliance and regulatory support: Match their built-in framework support (SOC 2, PCI DSS, HIPAA, GDPR, NIST, CIS) to your specific industry requirements. Look out for automated reporting, audit-ready documentation, and compliance-specific scans, pentests, and certification support.
- Automated remediation and DevSecOps integration: Best tools offer guided remediation, one-click fixes, and CI/CD workflow integration, which enable you to Shift-left.
- Total cost of ownership and scalability: Analyze per-workload, per-asset, or flat-rate pricing. Make sure your ROI calculations factor in the cost of breach prevention as well.
- Vendor support and team readiness: Evaluate the vendor’s security research team, update frequency, available training, and whether the tool matches your team’s DevSecOps maturity level.
Still weighing your options? Here’s a shortcut: Astra Security is the only platform that combines automated cloud scanning + expert pentesting + validation-first results into a single subscription with zero false positives. Talk to an Astra cloud security expert
How Cloud Security Tools Discover Shadow IT and Unknown Devices

This starts with Network traffic analysis that examines data flows through firewalls and proxies, and identifies communications with unauthorized cloud services. This is the base or a foundational tactic and has blind spots in case of remote workers that operate outside the corporate network, so make sure you keep that in mind.
Next, you have your CASBs that act as the primary shadow IT discovery engine. They ingest logs from network devices, maintain catalogs of ~8,500–31,000+ cloud apps rated across 25–90+ risk attributes, and automatically assign risk scores.
Following the discovery engine, you engage with API-based (connects via read-only APIs to cloud accounts (AWS, Azure, GCP) and Endpoint-based cloud discovery (collects cloud traffic data directly from devices, providing visibility regardless of network location ). This is to enumerate all resources, including those provisioned outside your normal IT governance (developer-spawned workloads, rogue accounts). This becomes especially critical for remote and BYOD environments.
Now, once discovery is complete, you get on with the Attack surface management (ASM), which scans internet-facing assets from the outside-in and discovers organization-linked assets unknown to security teams. This is achieved by mapping assets to external attack surfaces that ought to be updated vigilantly.
Do keep in mind the scale of the problem that while organizations typically use 1,000+ cloud apps, IT is only able to track <100, while ~80% of employees use non-sanctioned apps.
Final Thoughts
Cloud breaches aren’t going to slow down, thus neither should your security strategy. The 11 cloud security tools on this list tackle different layers of the problem, from posture management and runtime detection to identity governance and Zero Trust access.
But here’s the thing most tools miss: detecting a misconfiguration isn’t the same as proving it’s exploitable. That gap between “theoretically risky” and “actually dangerous” is where breaches happen, as humans tend to grow lackadaisical in this space, and this is where validation-first platforms such as Astra Security earn their keep.
Pick the tool that matches your cloud stack, team size, and compliance needs. Then stop guessing and start comparing, validation and negotiating.
FAQs
What are the best cloud security tools?
The best cloud security tools for 2026 include Astra Security (best for validation-based cloud security and pentesting), Wiz (best agentless CNAPP for enterprises), Palo Alto Prisma Cloud (most comprehensive feature coverage), CrowdStrike Falcon (best for unified endpoint + cloud), and Microsoft Defender for Cloud (best free tier for Azure organizations). You need to decide which one to go for based on your sector, budget, IT constraints, certifications, etc.
What are the best cloud security tools for developers?
Developer-focused cloud security tools readily integrate directly into CI/CD workflows so as to minimize productivity disruptions. Overall, the best picks for cloud security tools for developers would be:
1. Astra Security (CI/CD integration with Slack-based vulnerability management),
2. Snyk (developer-first vulnerability scanning for code, dependencies, and containers)
3. Sysdig Secure (Kubernetes-native with deep DevOps integration)
4. Wiz (agentless with fast deployment and contextual remediation guidance)
Key traits to look for: CI/CD pipeline integration, actionable fix guidance (not just alerts), shift-left capabilities, and low false-positive rates.
How do cloud security tools find unknown devices?
Cloud security tools discover unknown devices through:
– Network traffic analysis (examining firewall/proxy logs)
– CASBs (cataloging cloud app usage against known app databases)
– API-based cloud enumeration (connecting to AWS/Azure/GCP accounts to inventory all resources)
– Endpoint agents (collecting data directly from devices)
– External attack surface management (scanning internet-facing assets from outside-in)
What is the difference between CSPM and CNAPP?
CSPM focuses specifically on monitoring cloud systems for misconfigurations and compliance gaps, while CNAPP is a unified platform that includes CSPM plus workload protection (CWPP), identity management (CIEM), data security (DSPM), IaC scanning, and more. Thus, CSPM is one component within a CNAPP.
How much does a cloud security breach cost?
As per Palo Alto Networks the average cost of a data breach reached $4.4million in 2025. That included:
1. Crisis Management + IR + Forensics
2. Extortion + Direct Payouts
3. Downtime + Business Interruption
4. Legal Fees + Regulatory Fines + Insurance Premiums
But actual cost is something more, a major multiplier, complexity, is missed out here, as firms increasingly use siloed diverse cloud tools that add friction and expand the attack surface and vectors.
Do I need multiple cloud security tools or one platform?
The industry trend favors consolidated CNAPP platforms over multiple point solutions since fragmented tools create visibility gaps.
The recommended approach would be to start with a unified platform as the foundation and then add specialized tools (e.g., deep CASB for SaaS governance or dedicated KSPM for complex Kubernetes) only where non-negotiable coverage gaps exist.
Additional Resources on Security Testing
This post is part of a series on Security Testing. You can
also check out other articles below.

- Chapter 1: What is Security Testing and Why is it Important?
- Chapter 2: Security Testing Methodologies
- Chapter 3: What is Web Application Security Testing?
- Chapter 4: How to Perform Mobile Application Security Testing
- Chapter 5: What is Cloud Security Testing?
- Chapter 6: What is API Security Testing?
- Chapter 7: What is Network Security Testing?
- Chapter 8: A Complete Guide to OWASP Security Testing?
- Chapter 9: What is DAST?
- Chapter 10: What is SAST?