In today’s modern digital age, the prevalence of cyber threats have increased significantly. No organization, regardless of its size or industry, is completely immune to potential cyberattacks. This is why Continuous Vulnerability Management (CVM) is of utmost importance.
Continuous vulnerability management can be likened to a perpetual check-up for an organization’s digital well-being. It involves a methodical approach to identifying, prioritizing, and addressing weaknesses (referred to as vulnerabilities) in an organization’s IT systems. These vulnerabilities can range from weak passwords and outdated software to improperly configured networks. By discovering and rectifying these vulnerabilities promptly, an organization can effectively shield itself against potential cyber threats.
Understanding Continuous Vulnerability Management
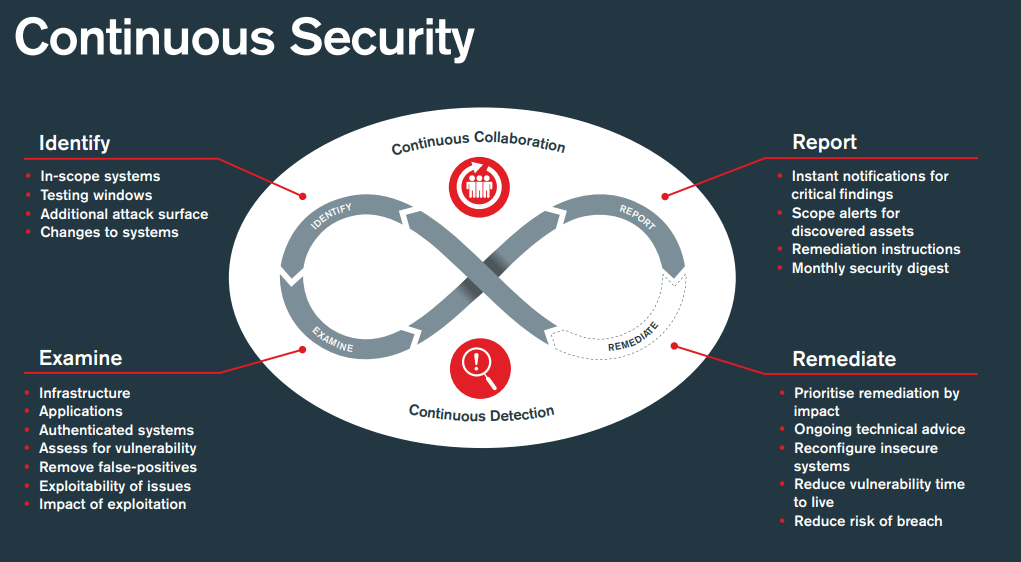
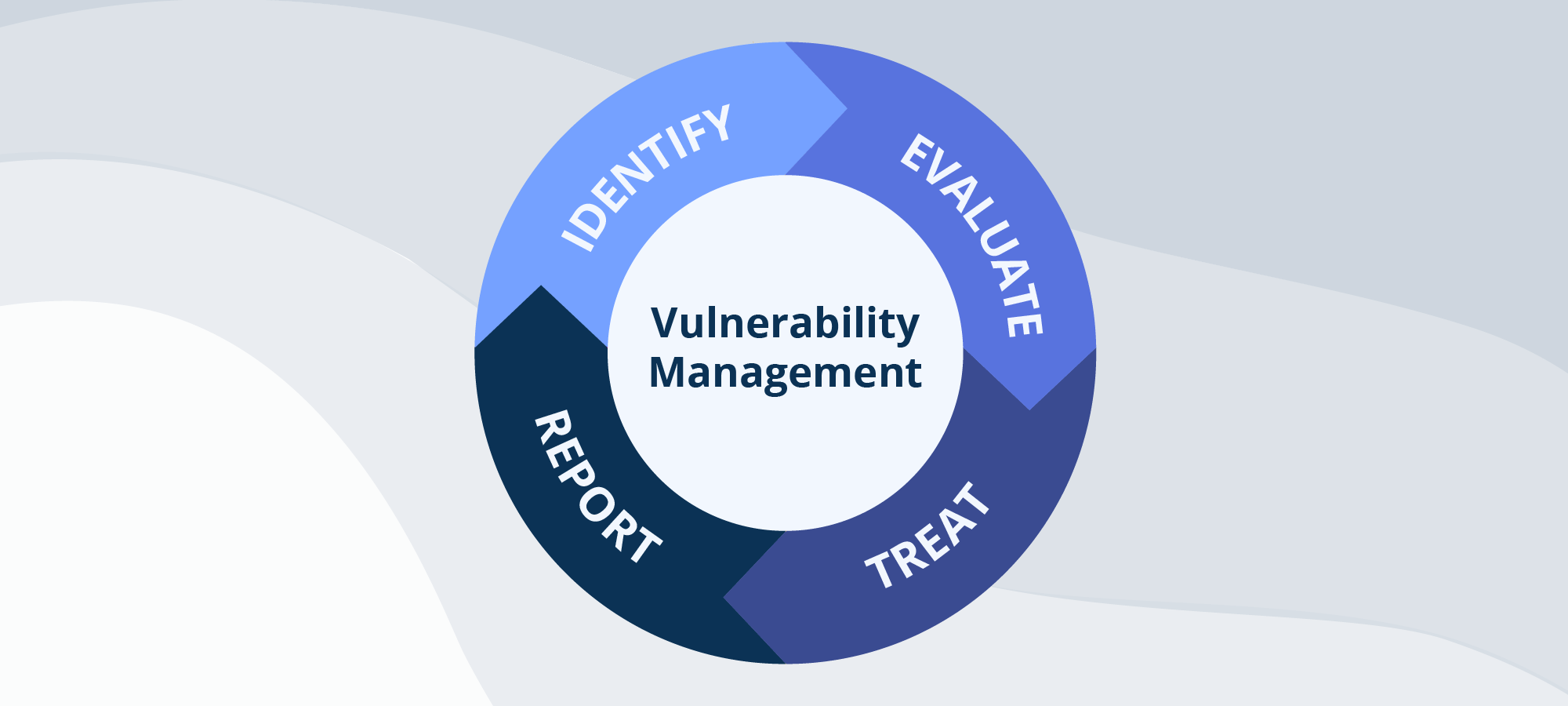
Rather than being a one-off endeavor, continuous vulnerability management operates as an ongoing cycle consisting of four stages:
A. Identification of Vulnerabilities: This initiates the continuous vulnerability management process by identifying all potential weak points present within an organization’s system, network, or application infrastructure. Such vulnerabilities may encompass software bugs, configuration errors, or outdated systems. The use of automated tools allows for comprehensive scanning and reporting on any identified vulnerabilities across the entire IT ecosystem.
B. Assessment and Prioritization of Vulnerabilities: Following vulnerability identification comes their examination and subsequent prioritization based on the level of risk they pose. Adhering to a risk-based approach, resources are allocated to resolving the most critical vulnerabilities initially – those that have the potential to cause maximum harm if compromised.
C. Remediation of Vulnerabilities: Once prioritized, vulnerabilities undergo remediation (i.e., fixing). This can involve actions like patching software, rectifying configuration errors, or replacing outdated systems with up-to-date alternatives. The primary objective is to eliminate vulnerabilities and fortify the overall security system.
D. Verification and Follow-up: In the final stage, verification checks ascertain the successful resolution of existing vulnerabilities and ensure no new ones were introduced during the process. Continuous monitoring plays a key role here – constantly checking for new vulnerabilities and initiating future cycles of the continuous vulnerability management process.
It is important to emphasize that Continuous Vulnerability Management should not be regarded as a “set it and forget it” procedure. It necessitates regular attention and ongoing maintenance. Through this iterative cycle, resilient security systems are achieved by adapting to emerging threats in real time.
Continuous Vulnerability Management Tools
CVM tools are indispensable as they automate and streamline the identification, assessment, and remediation of vulnerabilities. They save valuable time and resources, enhance the accuracy of vulnerability detection, and offer insights into potential vulnerabilities that may be overlooked during manual inspections.
Astra Security stands out as a remarkable tool making significant contributions to the field of CVM. Renowned for its comprehensive security suite, it showcases a robust vulnerability scanner capable of real-time vulnerability detection. Astra Security’s user-friendly dashboard simplifies comprehension of risk levels and even provides guidance on the path towards remediation. Through its commitment to simplicity and effectiveness, Astra Security has democratized access to CVM for businesses regardless of their size.
While Astra Security presents a holistic solution, it is worth mentioning other noteworthy tools as well. Open-source alternatives like OpenVAS provide cost-effective ways for smaller organizations or startups to handle vulnerabilities. Additionally, commercial options including Burp Suite can be considered due to their automated scanning capabilities and extensibility features.
Vulnerability Remediation
Now that we understand the tools involved let’s dive into one of the crucial steps in the Continuous Vulnerability Management process: Vulnerability Remediation.
Vulnerability Remediation is the action taken to resolve or mitigate detected vulnerabilities in an IT system or network. It is a crucial step in the process as identifying vulnerabilities is just half the battle won. The real task lies in addressing these vulnerabilities before they can be exploited by cyber attackers.
Importance of Vulnerability Remediation
The importance of remediation cannot be overstated. Unaddressed vulnerabilities can lead to data breaches, loss of sensitive information, and substantial financial damages. Effective remediation helps to secure the organization’s IT systems, protect critical data, maintain the trust of customers and partners, and uphold the organization’s reputation.
Steps in Vulnerability Remediation
The process of vulnerability remediation is systematic and involves the following steps:
- Patch Management: Once vulnerabilities are identified and prioritized, the first step in remediation involves applying patches. Patches are pieces of software designed to update a computer program or its supporting data, fixing or improving it. Patch management is a crucial aspect of remediation, as many vulnerabilities can be fixed simply by updating the software to its latest version.
- Configuration Management: Sometimes, vulnerabilities arise due to misconfigured systems. In such cases, the remediation process involves adjusting the system’s settings to secure it. This could involve changing default passwords, restricting user privileges, or adjusting firewall rules.
- Risk Acceptance and Transference: In some cases, a vulnerability might not be immediately fixable, or the cost of fixing it might outweigh the potential damage. In such cases, an organization might choose to accept the risk or transfer it, for example, by purchasing cyber insurance.
Challenges in Vulnerability Remediation
While the steps may sound straightforward, vulnerability remediation comes with its share of challenges. These can range from the complexity of the IT environment, the severity and volume of vulnerabilities, to the availability of patches. Moreover, balancing the need for system availability and security during the remediation process can also pose a challenge.
Despite these challenges, successful vulnerability remediation is possible with a structured approach and the right tools. Regular system scans, prioritizing vulnerabilities based on risk, timely patching, and system configuration are some of the best practices that can guide an effective remediation process.
Through vulnerability remediation, organizations can ensure that identified vulnerabilities are properly managed and mitigated, contributing to a safer and more secure cyber environment.
Role of Continuous Security in Continuous Vulnerability Management
Fully grasping the concept of Continuous Vulnerability Management (CVM) necessitates understanding the integral role of Continuous Security.
1. Defining Continuous Security
At its core, Continuous Security is a methodology that emphasizes incorporating security practices into every stage of IT operations. Rather than viewing security as a standalone aspect or an addendum, Continuous Security ensures that protective measures are consistently integrated and evaluated across the entire lifecycle of IT systems and applications.
This model goes beyond mere monitoring. It involves comprehensive and ongoing testing, updating, and bolstering of security measures to keep pace with continually emerging threats. It adopts a proactive strategy, focusing on averting security incidents instead of merely reacting to them once they occur.
2. The Intersection of Continuous Security and CVM
Integrating Continuous Security with CVM is not just beneficial—it’s essential. This integration fortifies vulnerability management initiatives with consistent, current, and robust security measures. As a result, the probability of vulnerabilities being exploited dwindles, and the overall strength of the system’s security is significantly enhanced.
By incorporating Continuous Security, organizations can approach their vulnerability management tasks with greater confidence and effectiveness. They can detect and remediate vulnerabilities swiftly and accurately while also enhancing their ability to predict and stave off potential vulnerabilities in the future.
3. Implementing Continuous Security in Vulnerability Management
To weave Continuous Security into the fabric of continuous vulnerability management, various strategies can be implemented:
- Security During Design: Begin with security in mind. It should be integral to the initial stages of an IT system or application design, not an afterthought or a hastily added component.
- Persistent Security Testing: As continuous vulnerability management underscores regular vulnerability scanning, Continuous Security emphasizes ongoing security testing to discover and address potential weaknesses.
- Security Measure Updates: To counter evolving threats, it’s crucial to regularly update security measures such as refreshing firewalls, antivirus software, and other security applications.
- Employee Training: Providing regular training on security best practices and emergency responses can significantly mitigate the risk of vulnerabilities stemming from human error.
Conclusion
In the age of endless online threats, Continuous Vulnerability Management (CVM) isn’t just about playing defense. It’s about being a step ahead, actively working to keep organizations safe from the constantly changing landscape of cyber dangers. You see, continuous vulnerability management isn’t just a buzzword; it’s about comprehending all the bits and pieces, including the ongoing security measures and available tools like Astra Security, to craft an unbreakable line of cyber defense.
The emphasis here is on non-stop monitoring, checking, and fixing. It’s a process that ensures weak spots are not just found but effectively handled.
Now a days, continuous vulnerability management isn’t an option – it’s a must-have. When a business incorporates it into its cybersecurity strategy, it’s not just guarding precious data and systems. It’s building trust and faith with the people who matter most – stakeholders.
Frequently Asked Questions
What are the 4 types of vulnerabilities seen in cybersecurity?
The 4 types of vulnerabilities commonly seen in cybersecurity are:
1. Human Error Vulnerabilities
2. Network Vulnerabilities
3. Procedural Vulnerabilities
4. Operating System Vulnerabilities
How are vulnerabilities categorized?
Vulnerabilities are categorized based on certain criteria, metrics, CVSS, and also by the level of risk they pose. They are generally categorized into CVEs, CCEs, and CPEs.
What is the difference between vulnerability management and vulnerability assessment?
Vulnerability management is a holistic continuous approach to security that involves constant monitoring, scanning, identifying, and mitigating vulnerabilities whereas vulnerability assessment is a point-in-time approach that is a part of vulnerability management.









