The Sysdig 2023 Cloud-Native Security and Usage Report reported that 87% of Container images have high-risk vulnerabilities. In simple words, containers refer to packages of software files that contain everything needed to run an application.
They are an essential step forward in modernizing applications, however, with the benefits of containers also comes the responsibility of securing them, especially container images that often contain vulnerabilities due to the use of outdated packages. This is where container vulnerability scanning steps in.
This blog will help IT professionals understand why they should be scanning container technology, how to do it, and the most critical question, how they know they are running a secure environment.
Action Points
- Container vulnerability scanning is the act of checking containerized applications for security problems or weaknesses to keep them safe from potential threats.
- Common container vulnerabilities include escape vulnerabilities, attribute disclosure, and known vulnerabilities in components.
- There are 5 different types of container vulnerability scans.
- Follow practices like unique UIDs, limiting user IDs, using mandatory access control, and more to maximize security.
- Tools like Astra, Clair, Grype, Docker Bench for Security, Trivy, and more can help secure against the same.
What is Container Vulnerability Scanning?
Container vulnerability scanning is a process that uses automated tools to compare the contents of each container to a database of known vulnerabilities. If a library or other dependency within a container image is subject to a known vulnerability, the tool will flag the image as insecure.
What are Containers?
Containers, on the other hand, are lightweight, stand-alone, executable packages that include everything needed to run the application: code, runtime, system tools, system libraries, and settings. They provide an isolated environment for applications to run in. The application is installed within a container, including a specific operating system, libraries, and executable files.
Why is Everyone Using Them?
When the container is started, the application runs on the operating system in that isolated environment. Containers are easy to deploy and start. They are independent and can run on their own. This makes them portable to many different environments and easy to integrate into existing applications.
Introduction to Vulnerability Scanning
Vulnerability scanning is finding security vulnerabilities in the applications (web, mobile, network, blockchain) using manual or automated scanners. Vulnerability scanning is a crucial part of any security program. It allows security personnel to keep track of known vulnerabilities, prioritize them, and plan the best way to fix them.
The vulnerability scanning process includes data collection, analysis, categorization, prioritization, and reporting of vulnerabilities. Manual vulnerability scanning is increasingly being replaced with automated vulnerability scanning. Automatic vulnerability scanning is performed on a website or software using an automated vulnerability scanner.
Automated vulnerability scanning is more cost-effective and scalable than manual vulnerability scanning. Automatic vulnerability scanning is being used by organizations to test for security vulnerabilities.
Protect your business from hidden threats. Try Vulnerability Scanning Services for continuous monitoring and zero false positives.
Why is Container Security complex?
Container security scanning has become more and more popular in recent years. That is because Docker has grown in popularity, and the process has become more and more complex.
- The container ecosystem has grown significantly, which means many more components need to be checked for vulnerabilities.
- The more components you add to your application, the more complex the process of checking for vulnerabilities becomes.
- The complexity of containers makes them a more difficult target for developers and security researchers.
- The challenge is that containers are a new technology and container security is relatively new.
What Kind of Container Vulnerabilities Can Be Detected?
Container technologies such as Docker are often considered to be safe and reliable. However, the reality is that they are vulnerable to several issues concerning security. The only way to eliminate the risk is to avoid containers altogether. When it comes to container-level vulnerabilities, the most common are:
1. Escape vulnerabilities
This vulnerability is caused by code that allows execution from user input due to improper isolation or insufficient restrictions such as input validation. The vulnerability can be used to escape the container by using a command that the user provides.
2. Attribute disclosure
This vulnerability is caused by a lack of restriction on the environment variables that the container can access and manipulate. This vulnerability can be used to obtain information that should not be available to the container.
For example, the container should not manipulate the host’s network interfaces, but the vulnerability allows the container to do so.
3. Known Vulnerabilities in Components
One of the most common ways to exploit vulnerabilities in the Docker daemon is to get a root shell, which allows the attacker to read any file on the server and execute any command as root. One way to compromise the Docker daemon is to exploit a vulnerability in a library that is used by one of the many Docker tools (e.g., docker-cli-js).
Container Vulnerabilities And How To Avoid Them
Several types of container vulnerabilities can be detected and mitigated. Here are some common examples:
Image vulnerabilities
The container image itself can contain vulnerabilities, such as outdated or unpatched software components.
Avoid this by keeping your images up-to-date with the latest patches and security updates.
Configuration vulnerabilities
Misconfigurations can also lead to security vulnerabilities. For example, running a container with unnecessary privileges or leaving open ports can leave your system vulnerable to attacks.
To avoid this, it is important to follow best practices for container configuration and use tools like security scanners to detect potential issues.
Runtime vulnerabilities
Once the container is running, it may still be vulnerable to attacks. For example, a container running as the root user may allow attackers to gain access to the host system.
To avoid this, it is important to use appropriate user permissions and to monitor the container for any suspicious activity.
Supply chain vulnerabilities
Containers may contain dependencies from external sources, which can introduce vulnerabilities.
Avoid this by carefully reviewing and auditing any external dependencies before adding them to your container.
Types of Container Security Scanning
Here are some common types of container security scanning:
Image Scans
Image scanning analyzes container images for vulnerabilities and misconfigurations before they are deployed. Image scanning tools use various methods to detect potential issues, such as analyzing software dependencies, comparing with known vulnerabilities databases, and examining system configurations.
Runtime Scans
Runtime scanning analyzes running containers for any changes or suspicious activities that could indicate a security breach. Various methods are used to monitor the behavior of running containers, such as examining system logs, network traffic, and file systems.
Compliance Scans
Compliance scan checks containers and images against security policies, regulations, and standards such as HIPAA, PCI DSS, or GDPR. Deviations from these standards are detected and alerts and reports on potential compliance issues are provided.
Configuration Scans
Configuration scans check container configuration settings for security issues, such as open network ports, elevated privileges, or insecure authentication mechanisms. Configuration scanning tools can detect misconfigurations and guide how to remediate them.
Dependency Scans
This analyzes container dependencies, such as libraries and frameworks, for known vulnerabilities and exploits. Outdated or vulnerable dependencies are identified and recommendations are given on how to update them.
How to discover container vulnerabilities during the SDLC pipeline?
Container images are the deliverable artifacts of a software project. Security vulnerabilities must be detected in the source code and the container images. Modern software development life cycle (SDLC) offers an opportunity to check container images for security vulnerabilities known as container vulnerability scanning.
In the past, image vulnerability scanning was only conducted at the time of image build (or build time). However, this process is not comprehensive enough as it doesn’t cover the time when the image is being used in production.
The approach mentioned above does not also cover the vulnerabilities introduced at image build. It is essential to scan images simultaneously as code is scanned (during code review) for potential security issues. This scanning can be manual or automated based on the organization’s decision.
10 Best Practices to Avoid Container Vulnerabilities
The use of containers is now considered a best practice, especially in terms of speed and flexibility. As with any new technology, it is essential to follow best practices to avoid common security concerns, such as:
- Assign unique UIDs and GIDs to each container.
- Limit and control user IDs, groups, and capabilities.
- Enable mandatory access control.
- Do not share host directories with containers.
- Disable container login by default.
- Use seccomp for filtering system calls.
- Avoid using root user
- Perform regular container vulnerability scanning
- Disable container capabilities.
- Use security-enhanced Linux for fine-grained controls.
Although the list is never-ending the above-mentioned are must-haves.
Top 5 Open Source Container Vulnerability Scanning Tools
Scanning containers for vulnerabilities is still a relatively new concept. Thus, only a few excellent open-source container vulnerability scanning tools are available.
1. Clair: Clair is one of the most used open-source container scanners that offers a static analysis of vulnerabilities in application containers. Vendors use it for vulnerability detection and users for vulnerability analysis.
2. Grype: Grype is an easy-to-use and straightforward container vulnerability scanner. It is designed to provide quick container security scan containers and filesystems for common vulnerabilities in the most popular CVE database. Grype is powered by Syft, the open-source software bill of materials (SBOM) tool for container images and filesystems.
3. Docker Bench for Security: Docker Bench for Security, commonly abbreviated as DBFS, is a script to audit Docker containers against security benchmarks. DBFS is best described as a security benchmarking tool, which checks for standard best practices around deploying Docker containers in production environments. DBFS has been developed by the Sysdig team in collaboration with the SANS Institute, the University of New Haven, and many other awesome folks.
4. Trivy: Trivy is a great security scanner among container security scanning tools for container images. It allows you to scan images for vulnerabilities and configuration issues before using them. The goal is to help you verify your containers’ security and detect configuration issues or vulnerabilities before you deploy your application. Trivy is an entirely open-source project with its source code hosted on Github.
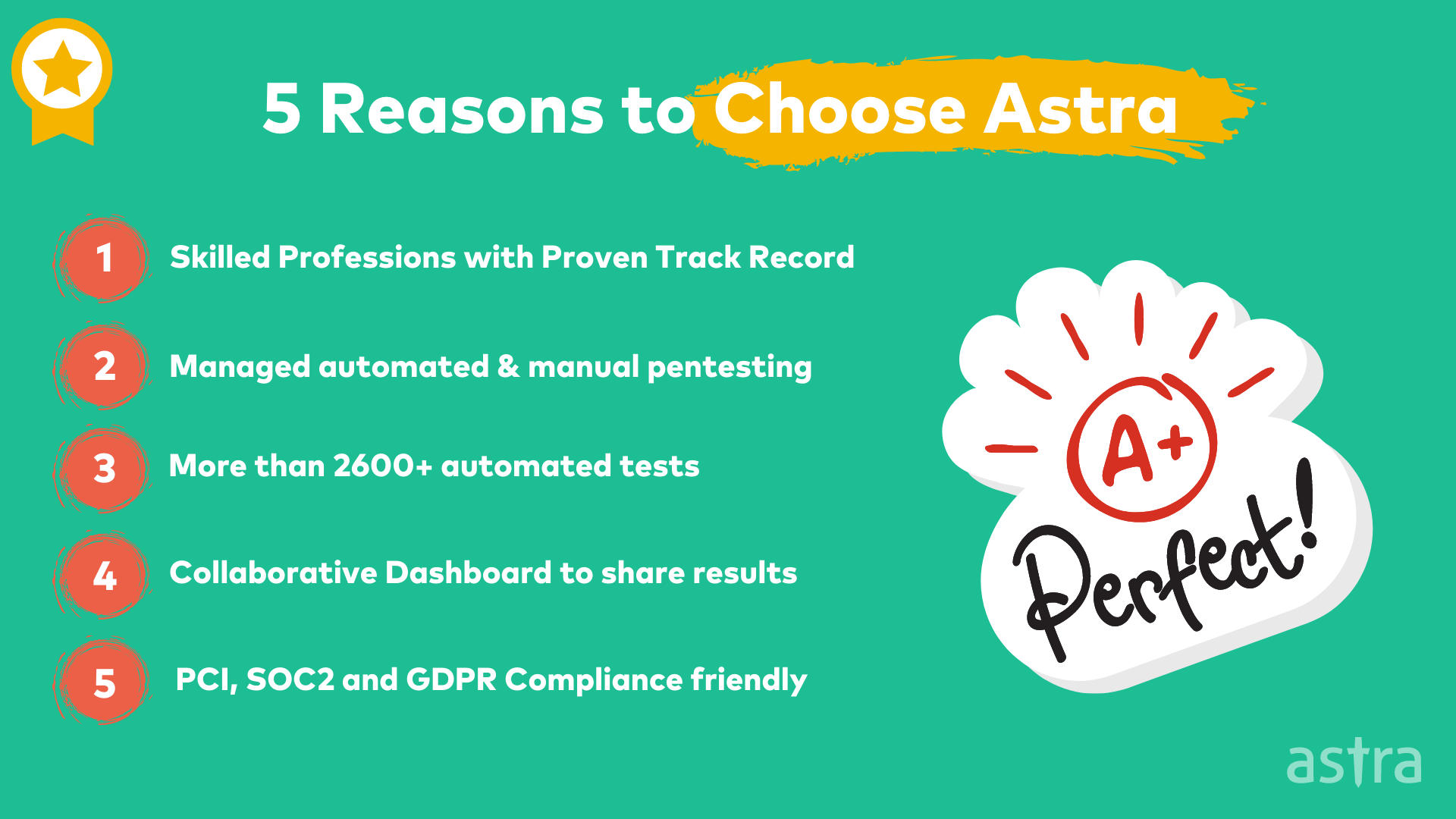
Why Choose Astra Security for Container Vulnerability Scanning?
Astra Security is one of the leading continuous PTaaS platform & DAST Scanner. At Astra, we provide a wide range of cybersecurity services, including Container Vulnerability Scanning by security engineers using open source tools with an offensive approach, Web Application Security, Network Penetration Testing and Penetration Testing. All of this happens on Astra’s one of a kind Pentest Platform.
Conclusion
Hopefully, this guide has provided you with all the information you need to understand better container vulnerability scanning and the different tools you can use to help keep your containers safe. If you want to learn more about how we can help you with container vulnerability scanning, feel free to contact us anytime. Thank you for reading. We are always excited when one of our posts can provide helpful information on this topic!
FAQs
How does container scanning work?
Container scanning works by comparing the contents of a container, including its software dependencies and configurations, against a database of known vulnerabilities. Automated tools identify and flag any matches, indicating potential security issues. This process helps ensure that containers are free from known vulnerabilities, enhancing their security in a rapidly evolving threat landscape.