Cloud penetration testing involves exploiting vulnerabilities, either manually or with automated tools, to simulate hacker behavior and uncover weaknesses.
By identifying these risks, cloud providers and customers can better prioritize security and prevent breaches like the 23andMe incident that exposed millions of users’ data.
Evaluation Criteria: Our criteria for selecting these cloud penetration testing services and tools focus on cloud provider coverage (AWS, Azure, GCP), ensuring support for multi-cloud environments. We prioritized tools that offer a combination of automated scanning and specialized penetration testing techniques, such as those targeting serverless functions or cloud-specific misconfigurations.
Actionable reporting, remediation guidance, and seamless integration with security workflows were also key considerations. Finally, we balanced functionality with pricing, including open-source options, to cater to a range of budgets and organizational needs.
11 Best Cloud Penetration Testing Tools
- Astra Pentest
- Intruder
- Nessus
- Scout Suite
- Pacu
- Nmap
- AWS Inspector
- CloudBrute
- MicroBurst
- SkyArk
- BurpSuite
| Feature | Astra Pentest (Top Choice) | Intruder | Nessus |
|---|---|---|---|
| Best For | Enterprises, compliance-driven orgs | SMBs, automated scanning | Large orgs, detailed scans |
| Supported Clouds | AWS, Azure, GCP | AWS, Azure, GCP | AWS, Azure, GCP |
| Key Features | 15,000+ test cases, AI/manual pentesting, zero false positives, CXO dashboard, detailed remediation | Continuous scan, agentless AWS, risk alerts, asset-based scans | Config audits, malware/compliance, point-in-time scans, customizable policies |
| Integrations | Jira, GitLab, CI/CD, Slack | Jira, GitHub, Azure DevOps | SIEMs, ticketing tools |
| Reporting | Real-time, CXO dashboard, detailed CVEs | Alerts, prioritized risks | Detailed, customizable |
| False Positives | Zero false positives (human verified) | Not guaranteed | Low rate, not zero |
| Compliance Scans | GDPR, HIPAA, SOC2, PCI-DSS, ISO 27001 | No dedicated suite | PCI, HIPAA, ISO 27001 |
| Price Range | $1,999+ /year | From $113/month | From $2,790/year |
| Review Score | 4.8/5 | 4.7/5 | 4.6/5 |
Factors in Choosing the Right Cloud Pentesting Tool
Cloud security companies are aplenty; thus, choosing the right third-party cloud testing tools for pentests can be difficult. Here are some factors to keep in mind and why you must do so:
- CI/CD Integration: The cloud pentesting tool should be easily integrated into your system for automated scanning after every update.
- Experience and Reputation: The company’s expertise in conducting penetration tests is crucial, as the skill of the pentesters and the range of tests conducted by the company are directly determined by it.
- Compliance Checks: What compliance do you want to achieve, and does the pentest service provide compliance-specific scanning?
- Tailored Requirements: Cloud pentest companies should be able to tailor the pentest according to your organizational demands and its assets.
- Pricing and Scalability: Are the prices offered affordable and within budget? Does it provide an option to scale up its services based on your growing demands?
- Advanced Functionalities: Features like scan-behind-login, customizable reports, and business logic error detection are not offered by every company but are required for high-quality pentesting.
1. Astra Pentest [Get Started]
Key Features:
- Platform: SaaS
- Pentest Capabilities: Cloud-native manual pentests + automated scans for web apps, APIs, and infrastructure
- Accuracy: Zero false positives with validated findings
- Compliance Scanning: PCI DSS, ISO27001, SOC2, HIPAA, and OWASP
- PCI Readiness Toolkit: Gap analysis, scoping guidance, and auditor-ready reports
- Workflow Integration: Slack, JIRA, GitHub, GitLab, and CI/CD pipelines
- Price: Starting at $1999/yr
Astra Pentest is a leading provider of continuous cloud penetration testing services, combining both manual and AI-powered pentesting solutions to run various tests and compliance-specific scans, including GDPR, ISO 27001, SOC 2, HIPAA, and PCI-DSS.
With tests covering Azure, GCP, and AWS infrastructures, we aid in cloud vulnerability management to ensure a seamless penetration testing experience with zero false positives, a CXO-friendly dashboard, and an easy-to-navigate interface. With real-time reporting, a detailed list and analysis of all CVEs, along with their corresponding CVSS scores and remediation steps, are shared with your team.
Pros
- Carries out scans behind logins and detects business logic errors.
- Features a comprehensive vulnerability scanner with the option to rescan once vulnerabilities are resolved.
- It provides gap analysis for companies to find gaps in their security measures.
- All-around customer care is provided, and queries are answered via email or phone if necessary.
- Astra Pentest Certificate will be provided upon remediation of the found vulnerabilities.
- CI/CD integration is possible, allowing the move from DevOps to DevSecOps.
Cons
- Trial available at $7
Best for: Enterprises and compliance-driven organizations seeking an all-in-one cloud pentesting solution with robust integrations and certification for remediation.
Experts Review
Why did we choose Astra Pentest?
Astra Pentest is known for its comprehensive approach to cloud penetration testing, combining AI-powered automation with manual expertise. Their coverage of major cloud providers (Azure, GCP, and AWS), compliance-specific scans, and assured zero false positives make it a strong choice for organizations with diverse cloud environments and stringent regulatory requirements. The real-time reporting, detailed CVE analysis, and remediation guidance further streamline the vulnerability management process.
2. Intruder

Key Features:
- Continuous, automated vulnerability scans for AWS, Azure, GCP
- Agentless scanning, cloud asset monitoring, prioritized alerts
- Integrates with Jira, GitHub, Azure DevOps
- Asset/tag-based scan management, real-time notifications
As one of the cloud security testing tools, Intruder is available for Azure, GCP, and AWS. It continuously performs incredibly thorough scans that can identify weaknesses.
Organizations may take action on vulnerabilities depending on their severity rating and monitor their attack surfaces for any changes or flaws that can expose them online.
Discover why security teams are switching from Intruder.io to alternatives that offer continuous monitoring and lower false positives.
Experts Review
Why did we choose Intruder?
Intruder is designed to simplify security assessments for websites, servers, and cloud environments. It scales effectively by emphasizing ease of deployment and management, making it ideal for growing organizations. While it does not guarantee zero false positives and its pricing may be a factor to consider, it offers transparent, evidence-based inputs.
Pros
- Helps with cloud vulnerability management in Azure, GCP, and AWS.
- Provides real-time intruder alerts.
Cons
- The reports could be more detailed.
- The Integrations could be widened.
Best for: Small and mid-sized businesses seeking easy setup and automated cloud vulnerability scanning.
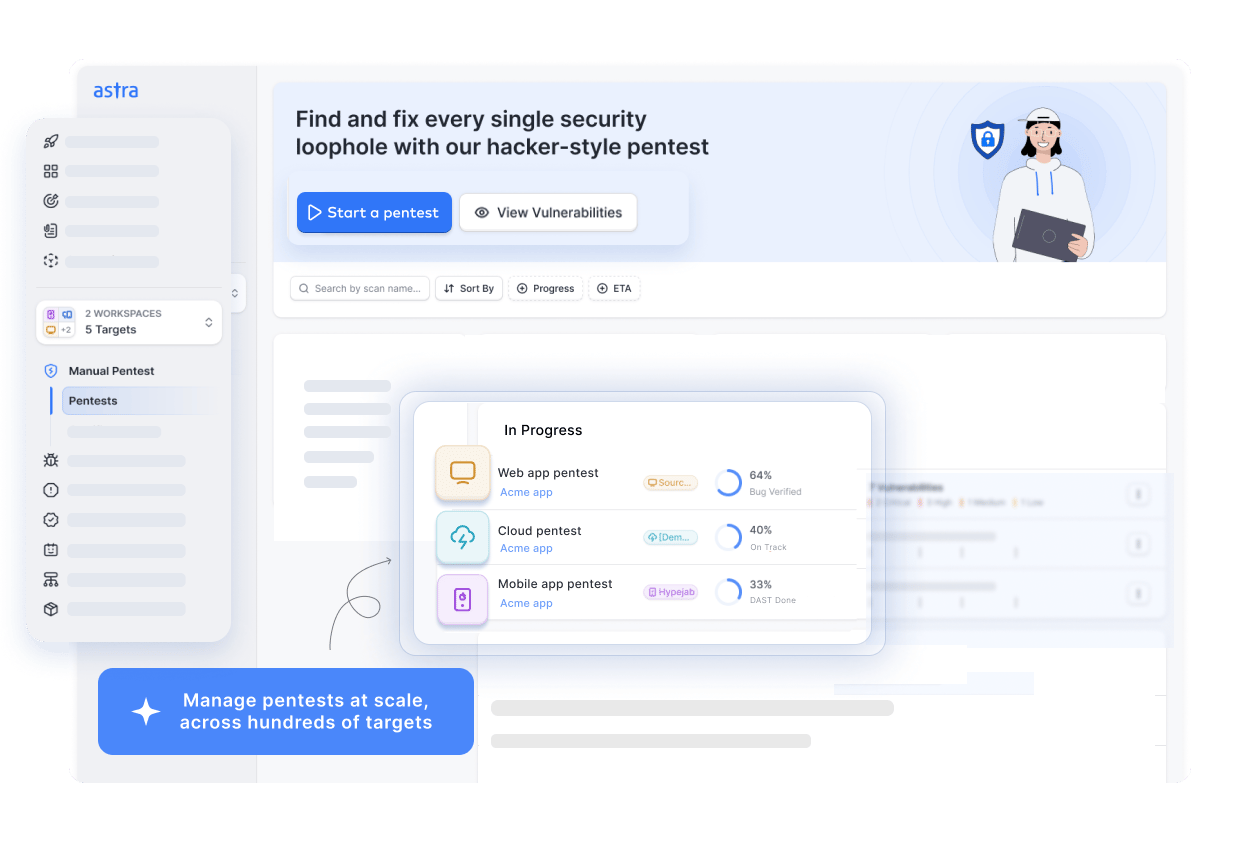
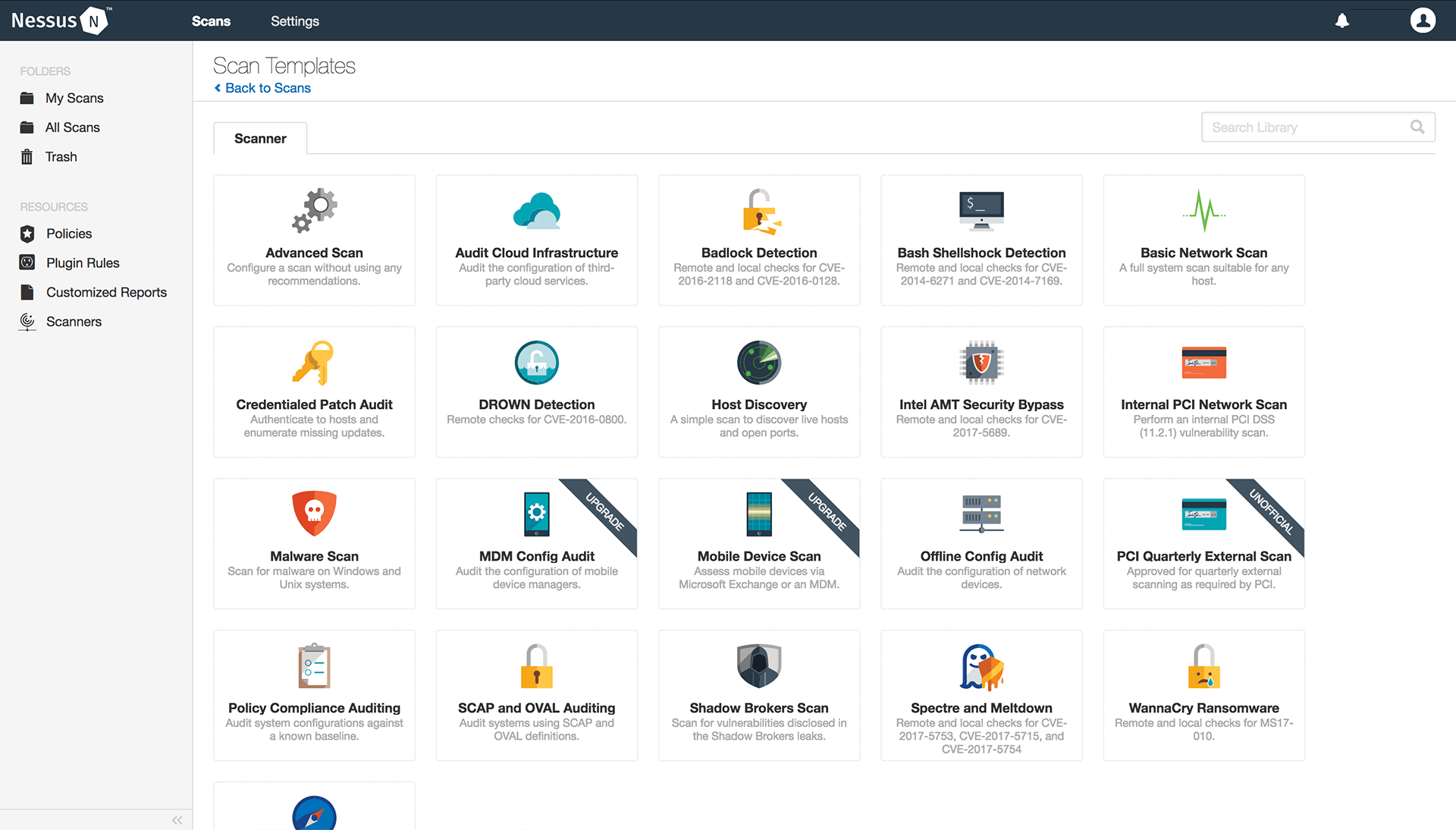
3. Nessus
Key Features:
- Comprehensive point-in-time vulnerability scanning
- Customizable scan policies, over 100,000 plugins
- Detailed compliance checks (PCI, HIPAA, ISO, etc.), misconfiguration/malware detection
- Integration with SIEMs and ITSM tools
Nessus is a cloud-based security and security testing tool that aids businesses in finding gaps in their security systems. This vulnerability assessment tool provides point-in-time analysis, simplifying and expediting detection and treatment.
Pros
- Notifies users in real-time when a new vulnerability is discovered
- A vulnerability scan’s configuration can be greatly altered to meet the demands of the target.
- Aids in maintaining PCI compliance.
Cons
- Several customization options with very minute differences make it difficult to choose based on needs.
- Time-consuming scans.
- It’s expensive when compared to other options.
Best for: Large organizations and compliance auditors requiring in-depth, policy-driven scans and detailed remediation.
Experts Review
Why did we choose Nessus?
Nessus is a vulnerability assessment tool that extends its capabilities to the cloud. We included it as it provides point-in-time analysis and has customizable scanning options. While its customization can be complex and scans can be time-consuming, Nessus’s real-time notifications and PCI compliance support are valuable assets.
4. Scout Suite
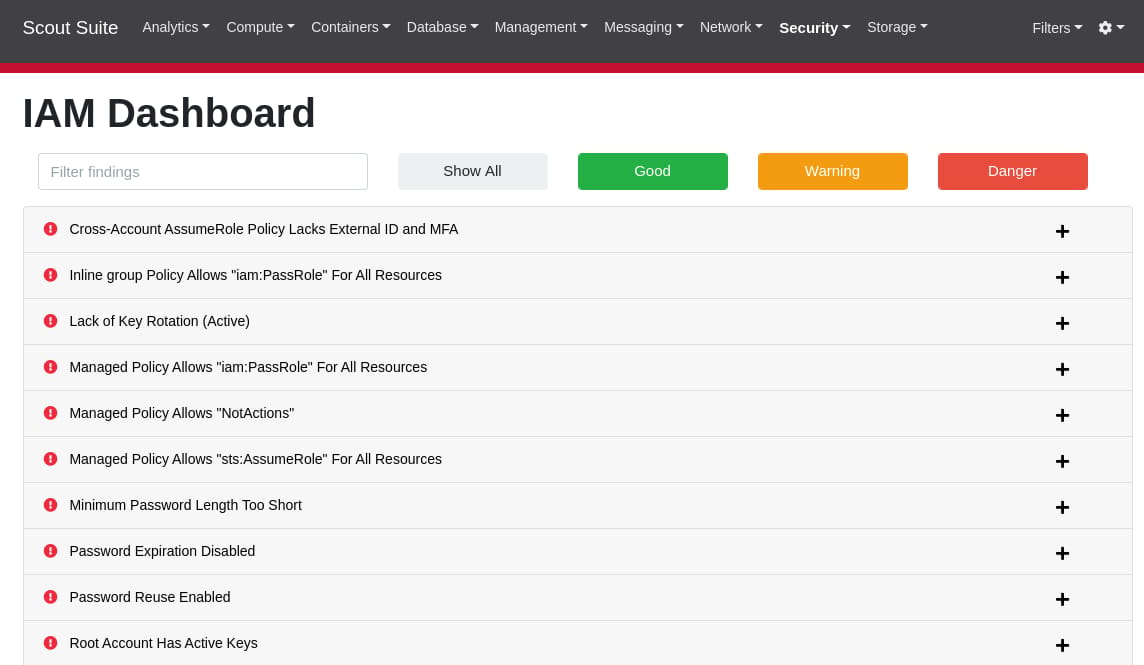
Key Features:
- Open-source tool for AWS, Azure, GCP, Alibaba Cloud
- Scans cloud configurations and identifies misconfigurations
- User-friendly interface, attack surface overview
This open-source multi-cloud penetration testing tool can conduct security tests on cloud platforms. Scout Suite looks for configuration data and provides an overview of the attack surface and cloud-specific vulnerabilities.
This data can be perused for manual inspection to develop detailed remediation plans.
Best For: Security analysts needing free, multi-cloud configuration auditing and manual inspection insights.
Experts Review
Pros
- Provides free trials.
- Easy-to-use interface.
- Provides a free version with good features for cloud penetration testing.
Cons
- The paid version has more specifications.
- Services can be a bit slow.
Why did we choose Scout Suite?
Scout Suite’s open-source nature and multi-cloud support make it a good option for organizations exploring cloud security testing. Its ability to identify configuration data and provide an overview of the attack surface is helpful for manual inspection and remediation planning. The free version offers a good starting point for cloud penetration testing.
5. Pacu
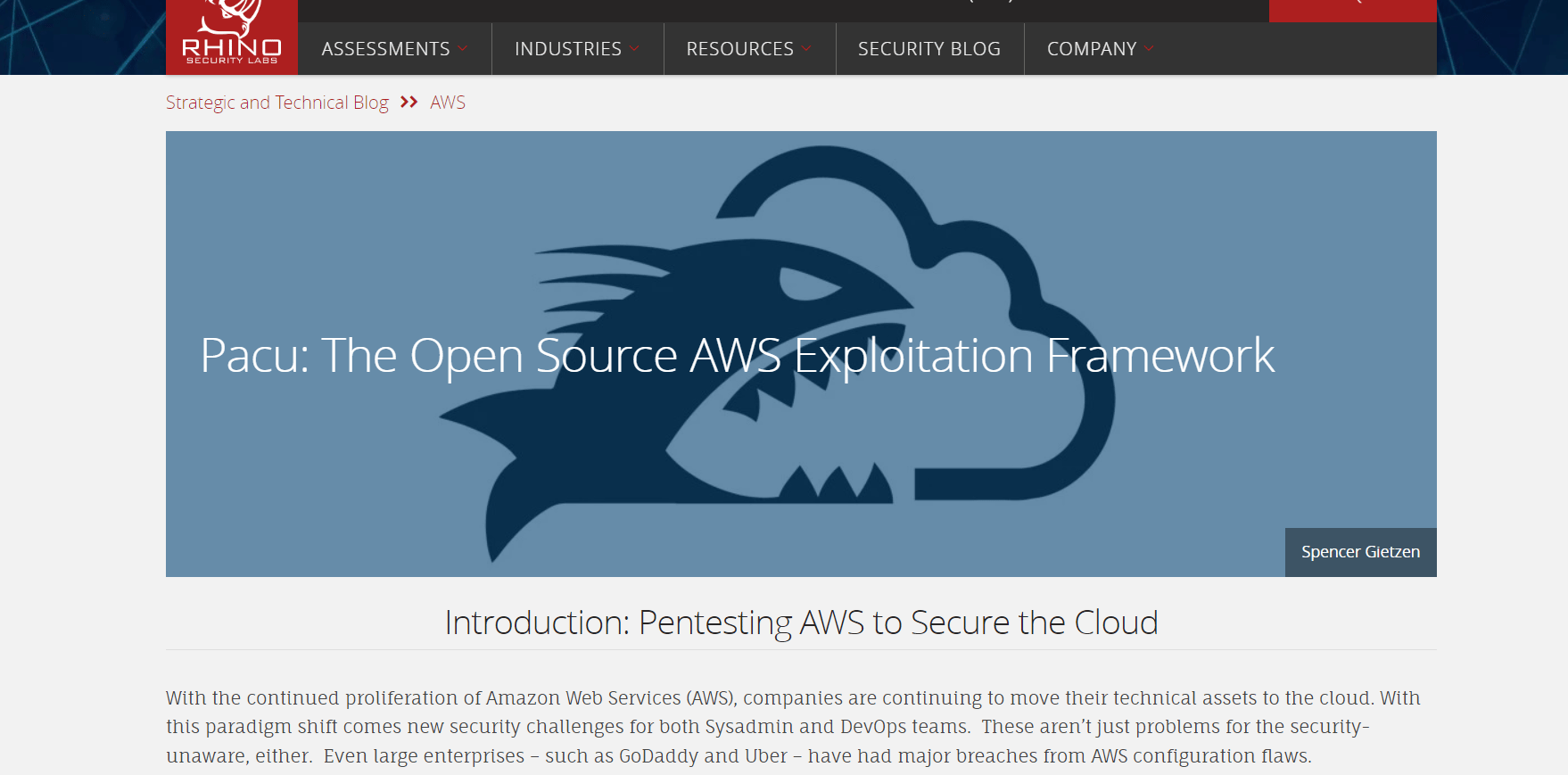
Key Features:
- Free, open-source AWS penetration testing framework
- Automates detection of config flaws, privilege escalation, and credential misuse
- Modular with many attack plugins
Pacu is an open-source cloud testing platform available for free on GitHub. It automates vulnerability detection in the AWS cloud platform. This framework enables penetration testers to identify and target configuration flaws in an AWS environment, including privilege escalation.
Best For: Security professionals focused on AWS, seeking deep privilege analysis and automated attack simulation.
Experts Review
Pros
- Capable of detecting AWS vulnerabilities
- It helps in quick scanning of the AWS cloud environment for user permissions.
Cons
- Does not offer as many features as its commercial counterparts.
Why did we choose Pacu?
Pacu is a specialized open-source tool focused on AWS cloud penetration testing. Its ability to automate vulnerability detection and target configuration flaws, such as privilege escalation, makes it a valuable asset for security professionals working within the AWS ecosystem.
6. Nmap
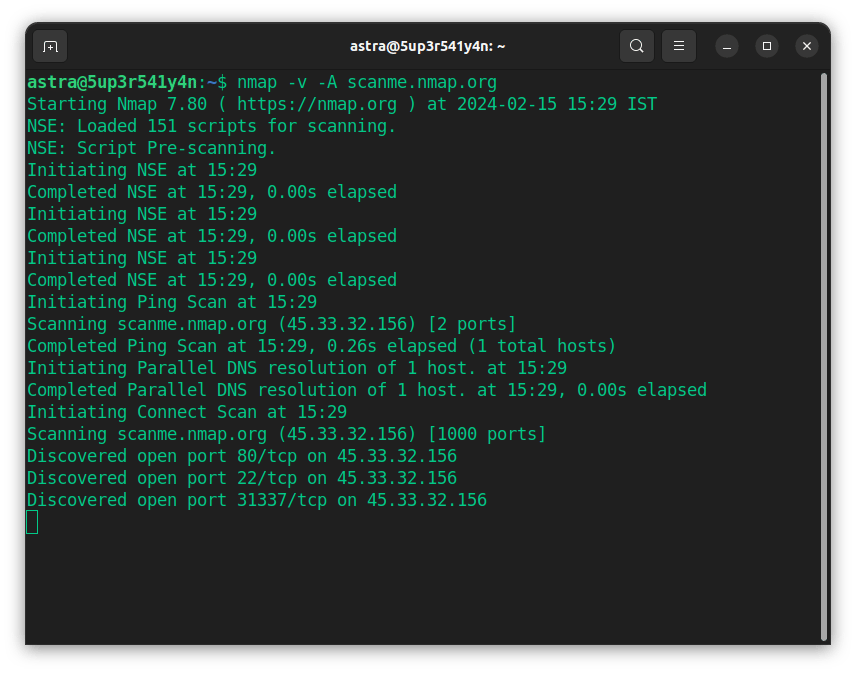
Key Features:
- Open-source network/cloud scanner
- Advanced host discovery, port/service/version/OS fingerprinting
- Scripting engine for automation; broad platform compatibility
Nmap is an open-source vulnerability scanner and one of the most popular ethical cloud hacking tools that helps with cloud network discovery, management, and monitoring. It is designed to scan large cloud networks, but works fine against single networks.
Best For: Network and cloud admins needing a reliable, free scanner for discovery and basic vulnerability mapping.
Experts Review
Pros
- Shows open ports, running serves, and other critical facets of a network
- Freely available.
- Usable for large and small networks alike
Cons
- The user interface can be improved.
- It might show different results each time.
Why did we choose Nmap?
Nmap’s inclusion is based on its versatility as a network discovery and monitoring tool, extending its utility to cloud environments. Its ability to scan large networks, identify open ports and running services, and its open-source availability make it a valuable asset for cloud network analysis.
7. AWS Inspector
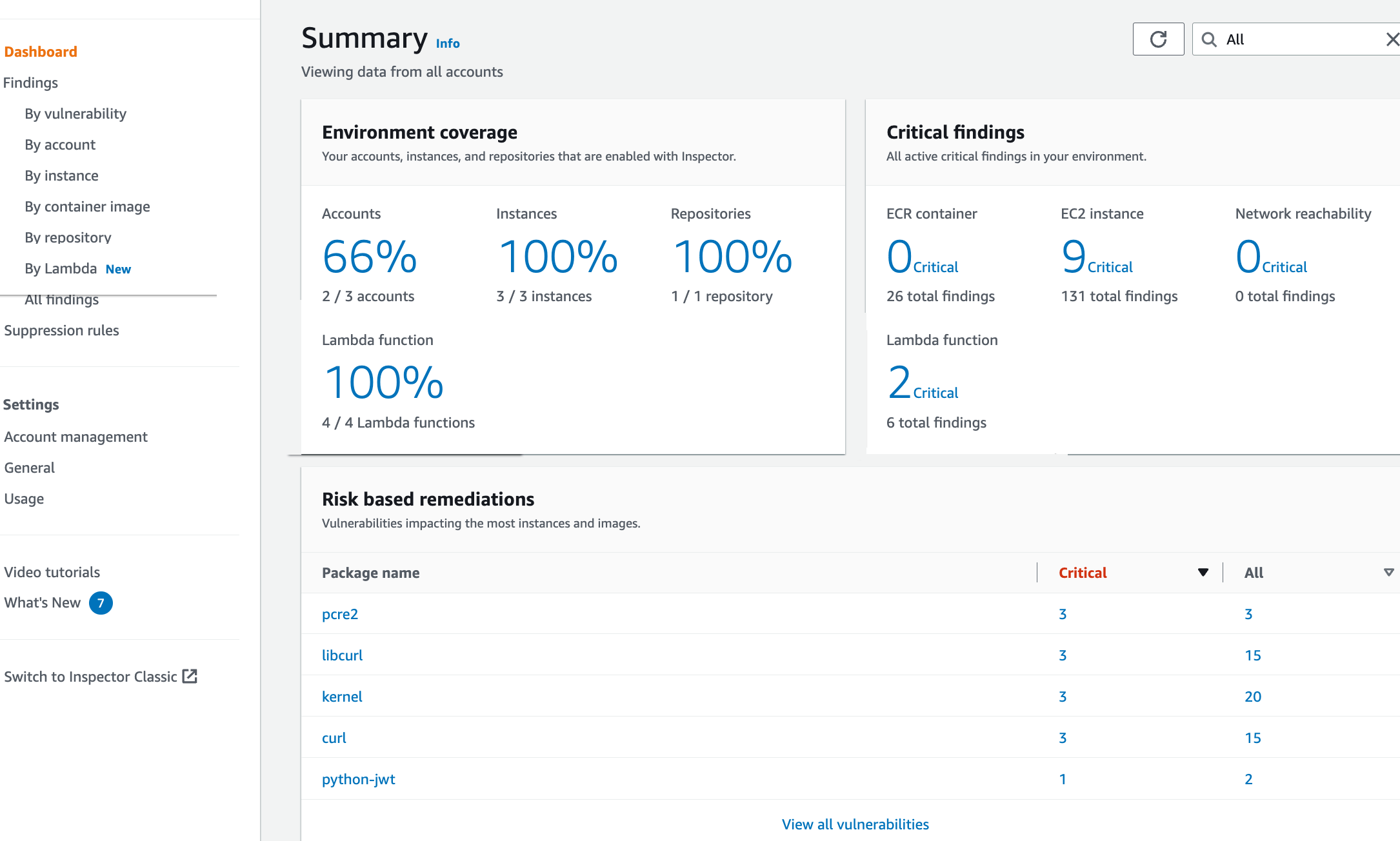
Key Features:
- Native AWS vulnerability management
- Automated and continuous scanning for EC2/ECR/Lambda
- Contextual risk scoring, cross-account support
This automated vulnerability management tool helps by continuously scanning the automatically detected AWS workloads for vulnerabilities and unintentional exposures.
After a few easy steps to enable its services, AWS Inspector can be used across all your AWS accounts.
Best For: AWS-centric organizations seeking native, automated vulnerability management.
Experts Review
Pros
- Discovers EC2 instances and images.
- Assess the plastic container registry for flaws and areas of exposure.
- Contextualized risk scores
Cons
- Does not provide a classification of individual findings.
- Billing can be a bit tricky.
Why did we choose AWS Inspector?
AWS Inspector is a natural choice for organizations heavily invested in the AWS ecosystem. Its automated vulnerability management service, continuous scanning of AWS workloads, and contextualized risk scores make it an essential tool for maintaining AWS cloud security.
8. CloudBrute
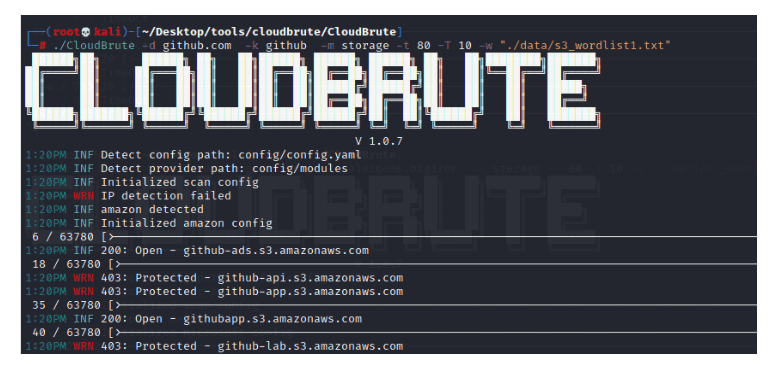
Key Features:
- Brute-force-based black-box cloud pentesting
- Finds open buckets, apps, outdated endpoints, and storage misconfigurations
- Supports Amazon, Azure, and others
Supports Amazon, Azure, and others. CloudBrute helps you identify key elements, such as open buckets, apps, and data, by performing brute-force attacks on cloud environments. It targets the company’s infrastructure and files, making black box cloud pentesting easier.
As one of the leading cloud pentest tools, it identifies vulnerabilities such as incorrect file storage, outdated endpoints, and inadequate concurrency.
Best For: Security teams wanting to uncover exposed cloud assets through brute-force enumeration.
Experts Review
Pros
- It works with multiple service providers like Amazon, Windows, and more.
- Brute force attack based on a pre-defined word list.
- Black-box cloud penetration tests were provided.
Cons
- It’s not as extensive as its commercial counterparts.
Why did we choose CloudBrute?
CloudBrute’s focus on brute-force attacks to uncover vulnerabilities like open buckets and outdated endpoints makes it a valuable tool for black-box cloud penetration testing. Its multi-cloud support is also a plus.
9. MicroBurst
Key Features:
- Open-source toolkit for Azure security testing
- Weak configuration auditing, Azure service discovery
- Post-exploitation actions like credential dumping
This freely available toolkit, created by Karl Fosaaen, can be used to carry out cloud-based penetration tests for the Azure cloud platform. It aims to identify weak configuration audits and enables post-exploitation steps, such as credential dumping.
Best For: Azure security specialists requiring detailed auditing and post-exploitation capabilities.
Experts Review
Pros
- Open-source penetration testing tool.
- Offers Azure Services discovery and weak configuration auditing.
- Post-exploitation actions like credential dumping.
Cons
- Does not offer many features like commercial tools.
Why did we choose MicroBurst?
MicroBurst is a specialized open-source toolkit for Azure cloud penetration testing. Its ability to identify weak configurations and perform post-exploitation actions, such as credential dumping, makes it a valuable resource for Azure security assessments.
10. SkyArk
Key Features:
- Identifies shadow admins and sensitive identities in AWS/Azure
- Detects exposed privileges and additional attack surfaces
- Specialized for cloud “shadow” privilege discovery
Available for Azure and AWS, this cloud infrastructure testing tool is useful for identifying additional attack surfaces and specializes in combating the risk of cloud shadow admins. It helps detect these shadow admins that could be present in any cloud environment and safeguards companies against them.
Best For: Organizations concerned with privilege escalation and hidden admin risks in AWS/Azure.
Experts Review
Pros
- Detects the presence of shadow cloud admins.
- Helps in assessing entities in AWS and Azure.
Cons
- Not available for the Google Cloud platform.
Why did we choose SkyArk?
SkyArk’s focus on detecting shadow cloud admins and identifying additional attack surfaces makes it a unique tool for cloud infrastructure testing in AWS and Azure. This specialized functionality addresses a critical security concern in cloud environments.
11. BurpSuite
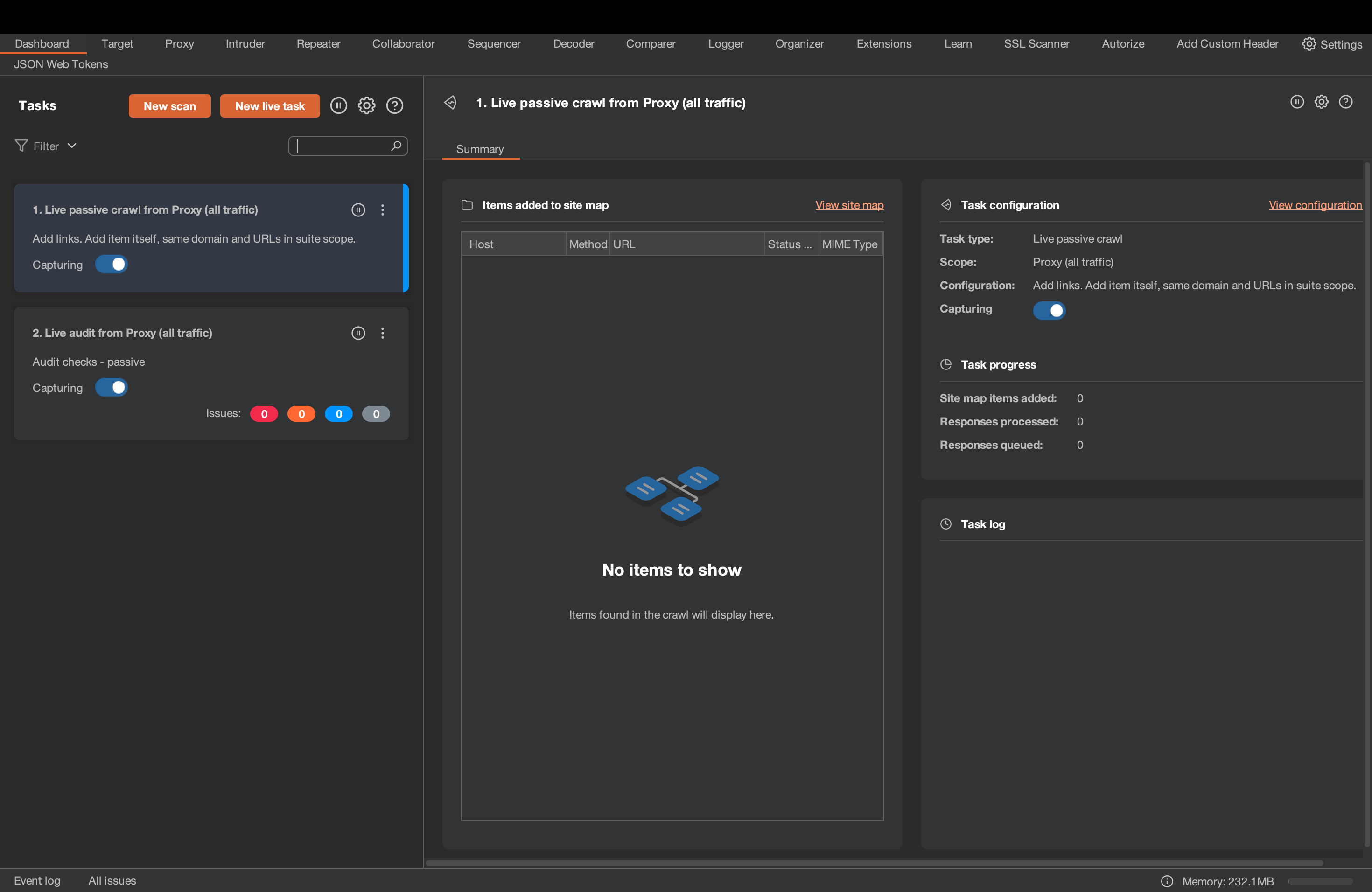
Key Features:
- Web app/cloud vulnerability scanner (manual and automated)
- Advanced proxy, scanner, intruder, and repeater tools
- Integrates with ticketing/workflow; S3 bucket testing support
BurpSuite is a constantly evolving vulnerability scanning and cloud pentesting tool that provides integrations for easy ticket generation. Now, it also provides scope for testing cloud environments and identifying misconfigurations in S3 buckets.
Best For: Web applications and cloud pentesters demanding powerful, extensible vulnerability testing with automated and manual capabilities.
Experts Review
Pros
- Provides advanced automated web app and cloud penetration testing services.
- Provides step-by-step advice for every vulnerability found.
- Can crawl through complex targets with ease based on URLs and content.
Cons
- Advanced solutions are commercialized and can be expensive.
- Does not provide expert customer service and assistance.
Why did we choose Burp Suite?
Burp Suite’s inclusion is due to its evolving capabilities, extending to cloud environments, including S3 bucket testing. Its comprehensive web application testing features and cloud-specific functionalities make it a versatile tool for cloud security assessments.
12. Qualys

Qualys provides continuous monitoring and compliance solutions and manages vulnerabilities in web application firewalls, making it a top contender in the best cloud security remediation software.
Experts Review
Pros
- Well-designed and easy-to-navigate user interface.
- Constant updates ensure the current security measures for the cloud environment.
Cons
- Limited scheduling options.
- Scans do not apply to all applications.
Why did we choose Qualys?
Qualys is a strong contender for cloud security remediation and continuous monitoring. Its focus on vulnerability management across web application firewalls and its well-designed user interface makes it a good choice for organizations seeking comprehensive cloud security.
13. Sophos
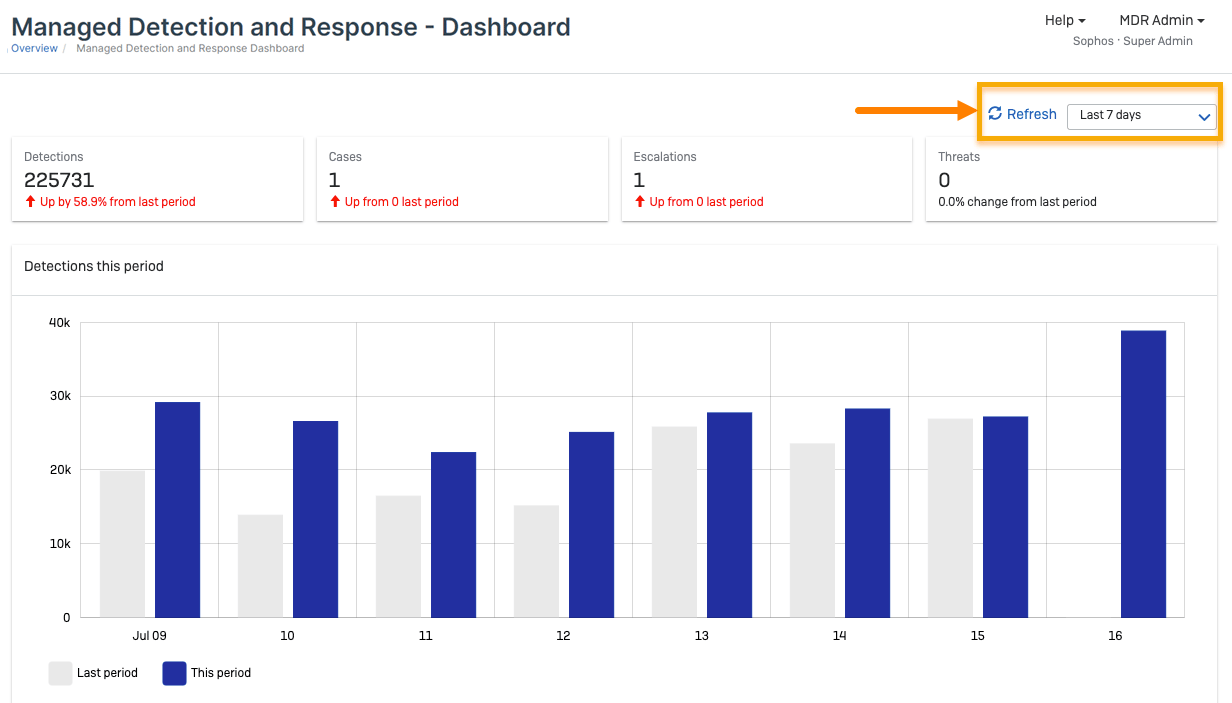
Sophos Cloud was founded in 1985 and offers enterprise-level cloud security architectural solutions, such as native protection, security automation for DevOps, and round-the-clock threat detection.
Experts Review
Pros
- Available for GCP, AWS, and Azure.
- Helps with automating security by employing DAST, SAST, and SCA code analysis.
- Intuitive, user-friendly dashboard.
Cons
- It can be expensive.
- Difficult to set up.
- Customer support could be better.
Why did we choose Sophos?
Sophos Cloud offers enterprise-level cloud security solutions, including native protection, security automation for DevOps, and threat detection. Its support for major cloud providers and its integrated approach to security makes it a valuable option for organizations seeking comprehensive cloud protection.
14. Guidepoint Security
Guidepoint Security offers detailed cloud security assessments that assess security strategies, migration readiness, and cloud health checks to determine any issues. They provide AWS, Microsoft, Google, and Oracle cloud security services.
Experts Review
Pros
- Provides customized, innovative solutions.
- Examines cloud environment against standard frameworks.
Cons
- It can be more expensive compared to other options.
- Could have a better user interface.
Why did we choose Guidepoint Security?
Guidepoint Security provides detailed cloud security assessments, covering security strategies, migration readiness, and cloud health checks. Its customized solutions and framework-based approach make it a good choice for organizations seeking in-depth cloud security evaluations.
Key Features of Good Cloud Penetration Testing Tools
1. Zero False Positives
A zero false positive assurance with vulnerability detection refers to automated scans being vetted by security experts to ensure that the scanner isn’t flagging any vulnerabilities that either do not exist or aren’t relevant to the company/industry. Every vulnerability found should be legitimate.
2. CI/CD Integrations
Ensure that the cloud penetration testing tools you have narrowed down can be integrated into your organization’s CI/CD pipeline, utilizing applications such as Slack, Jira, GitHub, and GitLab. Such integration enables your organization to transition from a DevOps model to a DevSecOps model, thereby prioritizing security.
3. Comprehensive Vulnerability Scanner
A vulnerability scanner that detects business logic errors, conducts scans behind login pages, and features customizable reports should be chosen for high-quality pentesting. Such scanners should be capable of detecting all known vulnerabilities based on intel, CVEs, and vulnerabilities mentioned in other standards, such as OWASP, NIST, and SANS Top 25.
4. Compliance-Specific Scans
The cloud pentesting tool should also provide compliance-specific scans to help organizations that store their confidential data comply with various industry-specific regulatory standards for data protection like GDPR, SOC2, ISO 27001, HIPAA, and PCI-DSS.
5. Detailed Reports
A good cloud penetration testing tool generates a comprehensive report that details the test scope, scanned assets, identified vulnerabilities, and attack methods used, along with customizations such as high-level summaries for executives and in-depth technical details for security engineers.
As such, the post-audit report should prioritize vulnerabilities by risk or CVSS score and include clear remediation steps, enabling swift action.
6. Pentest Certificate
The penetration testing company should provide a penetration testing certificate upon completing a penetration test and successfully remedying the identified flaws. This can be double-checked by conducting a re-scan. Providing a publicly verifiable penetration testing certificate strengthens customer trust and boosts sales, acting as a key selling point for potential cloud customers.
7. Customer Support
A reputable penetration testing company offers 24/7 customer support via phone and email to address any questions that may arise during the penetration testing process. Experts should provide customer support to ensure a seamless resolution of queries.
Benefits of Cloud Penetration Testing
Organizations with sensitive data and applications in the cloud, as well as cloud service providers, may benefit from tools for cloud penetration testing. Cloud penetration testing supports the shared responsibility framework that most cloud providers impose between their clients and themselves by:
- Finding Vulnerabilities: Identifying vulnerabilities through cloud penetration tests ensures quick fixes. Comprehensive scanners can detect even the most minute vulnerabilities, which is crucial as they facilitate immediate remediation before hackers exploit them.
- Enhancing Security: Another benefit of cloud penetration testing is that it helps constantly update security measures. If any security gaps are found, it helps improve the existing security measures.
- Improving Reliability: Conducting periodic cloud pentests enhances the reliability and trustworthiness attributed to cloud providers. This can attract more clients due to the security-conscious nature of the cloud provider, while keeping existing clients satisfied with the level of protection available for their data.
Final Thoughts
Cloud computing is taking over the business world by storm due to its ease of use and storage capabilities. Therefore, it becomes the responsibility of users and providers to ensure that their customers’ data is always secure, as even the cloud is vulnerable to hacking.
Choose the right cloud penetration testing tools based on their features, pros, and cons. Look for features such as CI/CD integration, compliance-based testing, affordable pricing, customization options, and a reliable penetration testing company.
Our top three picks to keep your cloud safe and sound include Astra Pentest, Intruder, and Nessus. Select the right tool to suit your needs.
FAQs
1. What are the top three cloud platforms?
The top 3 well-known and used cloud platforms are AWS by Amazon, Azure by Microsoft, and GCP by Google.
2. Top 3 cloud penetration testing methodologies?
The top 3 cloud penetration testing methodologies are:
1. Black box: In this pentesting methodology, the pentester is unaware of any target details and has to start to exploit from scratch—true hacker-style testing.
2. White box: In this type of pentesting, the testing knows all the relevant information about the exploitation. Also known as clear-box testing.
3. Gray Box: In this type of testing, details regarding the system are divulged partially.
3. What is AWS penetration testing?
This refers to exploiting the AWS platform service you use to find vulnerabilities within its security. AWS penetration testing is subject to its policies.
4. What is the Shared Responsibility Model?
The shared responsibility model splits cloud security between provider and customer. Each is liable for their part. Azure and AWS use this, with providers handling holistic security and customers responsible for their specific services. Responsibility increases from SaaS to PaaS to IaaS.