When you think of IoS technology — security is of paramount importance. Handling sensitive user data, and coding to minimize vulnerabilities are fundamentals for any application running on the marketplace.
As such, in this article, we will be discussing the following:
- Why is iOS app security important?
- Understanding the threat landscape of IOS app security
- Best practices to improve IOS security

Why is Astra Vulnerability Scanner the Best Scanner?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Why is iOS App Security Important?
As data theft and breaches become more frequent in a world of digital advancements, strong iOS app security becomes increasingly significant. End-users frequently interact with sensitive data: passwords, profiles, credit card information, and more. A breach may lead to daunting consequences – from financial loss to shattered credibility. That’s why prioritizing iOS App security is both a necessity and a responsibility for developers. It isn’t just about keeping data safe, but also preserving user trust and adhering to stipulated privacy laws.
A secure encryption system keeps all communication and content safe, while face recognition and fingerprint authentication instill trust in users. Additionally, apps must comply with global data governance regulations to protect business integrity and improve brand reputation.
Examples of security breaches and the damages they caused
The Yahoo data breach exposed the personal information of around 3 billion user accounts, damaging Yahoo’s reputation and eventually leading to its downfall. Facebook’s Cambridge Analytica scandal in 2018 had a similarly damaging impact on user trust and financial performance, demonstrating the necessity of iOS App Security.
iOS Application Security: Understanding the Threat Landscape
In this digital space, where apps constantly interact with multiple servers and users, it is essential to understand potential threats.
These can range from minor errors, such as weak app encryption, to serious risks like advanced persistent threats (APTs) using ransomware or other destructive tools.
Threat agents can be either opportunist hackers, corporate-sponsored cyber criminals, or state-sponsored intrusions.
To ensure strong iOS app security, developers need to be aware of these ever-changing risks and take steps to detect and reduce them. This will help protect user privacy, data, and reputation.
Common Types of Security Threats
There are a multitude of threats that can undermine the safety of your app:
- SQL Injection: SQL injections can manipulate your database and extract valuable data. It’s critical to use libraries that protect from such attacks.
- Cross-Site Scripting (XSS): Cross-Site Scripting (XSS) enables attackers to inject malicious scripts into websites viewed by users. If present in a mobile application, this vulnerability can allow intruders to access users’ sensitive credentials like cookies and session tokens.
- Unsecured Third-Party Libraries: While integrating libraries, hackers may attempt to exploit these third parties’ potential vulnerabilities. Employ libraries from trustworthy sources.
- Insecure Data Storage: Mobile data can be potentially accessed beyond the app’s coded functionality, hence discreet processes for enforcing secure storage are essential.
- Hard-coded valuable information: Coding pitfalls like embedding keys or latitudes into the app code make it easy for decompilers to extract sensitive data. Encrypted exchange, instead, should follow best practices.
- Faulty Encryption: High-quality encryption techniques need proper execution. Faults promote illegal access to data.
- Phishing Attacks: Imposing genuine apps/services to dupe users into revealing confidential details. Educating end-users becomes particularly crucial in such cases.
The safety and data integrity of macOS and iOS users must be protected through understanding and defending against security threats – it is not optional.
Potential Consequences of Insecure Apps
Insecure applications can bear severe ripple effects not just for businesses but end-users as well. From triggering negative financial implications to entailing legal issues and degrading trust levels, such lapses must not be treated lightly.
1. Financial Loss
The financial impact of a single security breach can be devastating. Direct costs, such as dealing with the breach and recovery, as well as fines for non-compliance, legal expenses, compensation for those affected, and increased insurance premiums, all add up.
2. Legal and Regulatory Consequences
If an app falls short of privacy laws and regulations, businesses might have to face hefty penalties and possible lawsuits from aggrieved parties.
3. Brand Reputation Damage
Trust, once lost, is hard to recover. A security breach can yield irreparable harm to a company’s image resulting in loss of current and potential customers.
4. User data compromise
Leaked user data such as personal records, health information, credit card details, and more can potentially impact end-users financially as well as socially.
5. Business process disruption
In the wake of a security breach, regular business operations might be affected too, causing delays and operational difficulties.
6. Increase threat to other systems
Hackers who manage to break into an insecure app might get access to wider network systems leading to exponential losses.
Safety should consequently rank topmost during an app’s development process including meticulous testing, monitoring, firewall setup, and hiring ethical hackers to identify the scope for improvement.
iOS Security Features
iOS comes equipped with several intrinsic features focused on user and data security:
- Secure Enclave: It is a dedicated chip for data encryption and decryption.
- Touch ID and Face ID: To ensure secure access.
- Apple Pay: A secure and effortless mode for financial transactions.
- Two-step verification: For protection against unauthorized access.
- Automated Software Updates: Keep iOS devices protected with the latest security tools and patches.
- App Transport Security: Standard procedure for networking that ensures data protection.
- Restricted app permissions: Apps have to explicitly request permission for access.
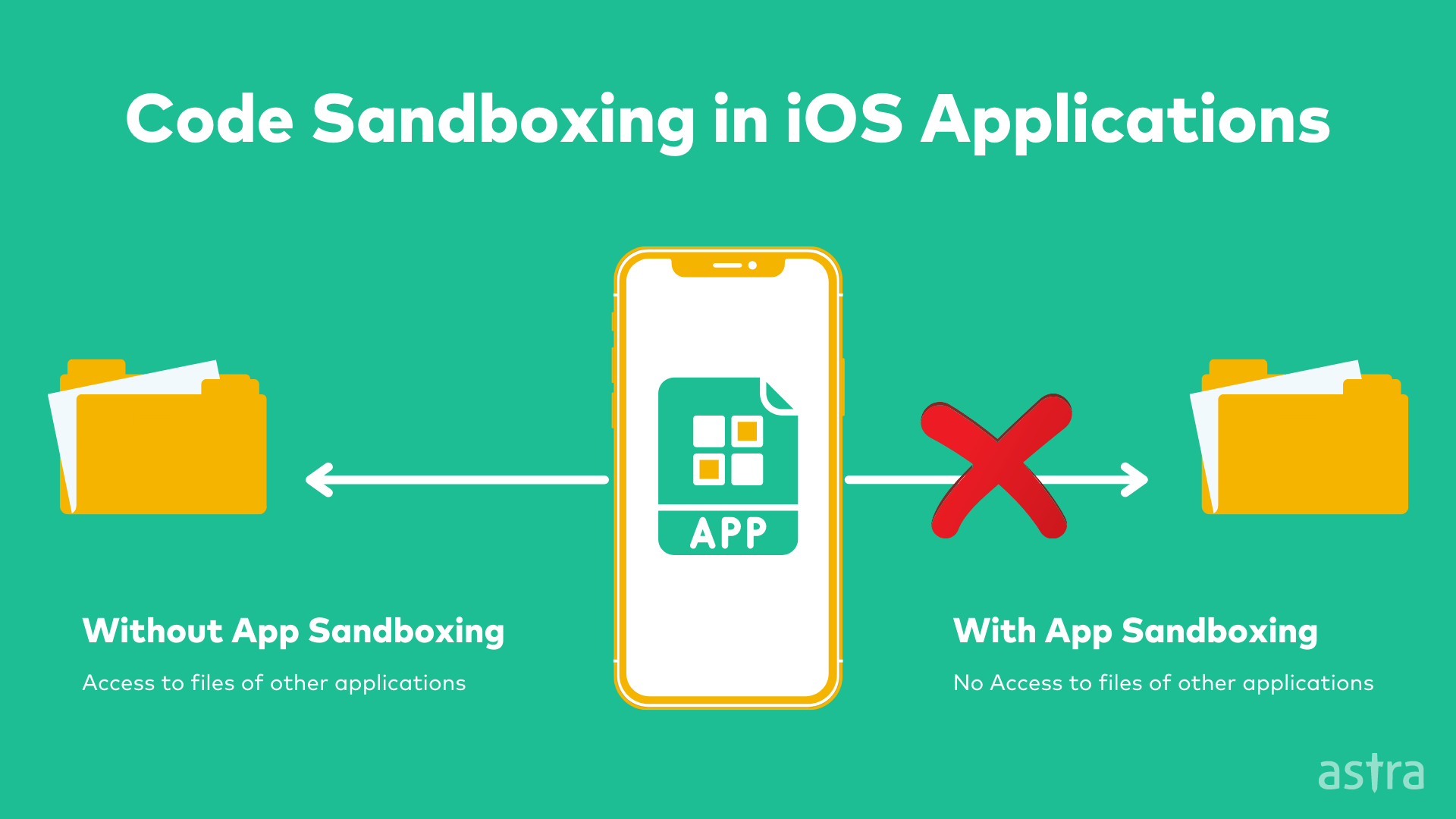
- App sandboxing: Isolates applications, ensuring they run independently without affecting other apps or the OS overall.
- Data Protection APIs: Long-lasting keys give developers powerful methods to encrypt information and maintain its privacy.
- File-level encryption: With each new iOS update, Apple enhances data protection capabilities, making separate files unreadable outside the user’s device.
- iCloud Keychain: It can safely store credentials, allowing only trusted devices access.
- On-device Intelligence and Differential Privacy: Assists with user interface and suggested auto-completions without risking your sensitive data being compromised.
- Security Certificates and Public Key Infrastructure: These form the backbone of Apple’s internet services guiding the identification process to safeguard against malicious sites or phishing attempts.
- Privacy settings: iOS provides granular and accessible control over privacy settings, enabling users to define app permissions and data access.
- Find My Device: A setting to help locate and secure a lost or stolen iOS device. It ensures user data isn’t accessible to others.
- Built-in malware protection: Advanced protection at the OS level helps express robust threat responses against malware and harmful websites.
- Code signing: Apple’s code signing prevents modification of the app code and verifies that applications are from a trusted developer, reducing threats.
- Erase Data function: After ten failed passcode attempts, iOS offers an option to completely erase the device and its data, iPhone Secure Erase.
While this isn’t an exhaustive list — each iOS update usually brings with it new security safeguards — the features mentioned demonstrate Apple’s rigorous attention to privacy and security.
iOS App Security Best Practices
From the early stages of app development, iOS engineers and security teams ought to be mindful of several best practices to ensure the delivery of secure and robust applications.
1. Consumer Privacy Necessity
Prioritize end-user privacy as a primary requirement. Protection of user information should be at the core of your app’s structure using encryption, proper security measures, and access control.
2. Principle of Least Privilege
Every element of an app should have the least possible access privilege necessary to function effectively. Exceeding privileges exposes unnecessary security threats.
3. Regular Updates and Patches
Ensure your application’s security features keep pace with evolving threats by pushing out regular app updates armed with the latest version of iOS protections and patched vulnerabilities.
4. Secure Coding Practices
Avoid hard-coding sensitive information, such as passwords or API keys, within the app. Instead, store these within a secure server or encrypt them in the app. Using secure keychains can significantly enhance system security.
Security Layer Implementation
Ensure the use of multi-layered security, such as protecting network access with tokens, browser session longevity, role-based access, and server security measures including Secure Sockets Layer certificates (SSL).
5. Testing and Monitoring
Conduct thorough testing of your app, and check for vulnerabilities. Testing on different devices and employing diverse testing methodologies can pinpoint a broad range of potential security issues. Continuous monitoring for any security compromises will help in timely remediation.
6. Third-Party Code Inspection
Third-party libraries, while often efficient, can come with security risks. So, a careful inspection of third-party code is crucial to detect malicious code activity. All resources like components, bytes, and chipsets obtained from third-party entities must be reviewed and verified to maintain your app’s security integrity.
7. User Authentication and Session Management
Iterative revisions and robust strategies for verifying user identity are paramount – Biometric measures, password encryption, and secure session management will add an extra layer of protection.
How can Astra Help?
Astra Security is a vulnerability assessment and penetration testing company that provides round-the-clock IOS app security testing services to assess internet-facing assets as quickly and efficiently as possible to detect vulnerabilities with zero false positives.
Our customizable, detailed pentest reports, AI-powered chatbot & human support, along with the CXO-friendly dashboard make it a perfect fit for your application testing.
In conclusion, protecting sensitive user data, adhering to privacy laws, and maintaining user trust is vital to ensure IOS app security. Although iOS provides inherent security features, developers must also follow best practices, prioritize user privacy, and regularly update their apps. Ultimately, safeguarding iOS apps is not just a choice; it’s a responsibility with far-reaching implications for businesses and users alike.
FAQs
How to make an iOS app secure?
To make an iOS app secure, follow these key steps: Implement strong encryption for data in transit and at rest, use Apple’s security features like Secure Enclave and Touch/Face ID, employ secure coding practices, regularly update the app with security patches, conduct thorough testing, review third-party code, and prioritize user authentication and session management.