Cyberattacks are relentless today, with over 2,200 breaches occurring every day, that’s one every 39 seconds. Aside from the staggering need for cybersecurity to prevent these attacks, there are two other drivers of the growing popularity of SECaaS or Security-as-a-Service Providers.
One is the all-pervading emergence of cloud computing, and the other is the increasing adoption of DevOps environments.
Small companies without huge security teams, faster SDLC, and bootstrapped tech start-ups find it challenging to incorporate solid security practices into their regular functionality.
To make security simpler and more accessible to them, they hire security-as-a-service providers.
Who are Security-as-a-Service Providers?
Security-as-a-Service providers offer a subscription model for delivering cybersecurity solutions through the cloud. The provider possesses high domain expertise and the necessary infrastructure to deliver end-to-end protection. They combine threat intelligence, endpoint protection, cloud security, and identity and access management services.
SECaaS provides a range of services, including threat detection, incident response, and data loss prevention. By outsourcing security management, organizations can focus on core business activities. This is especially useful for smaller companies with small security teams.
Top 5 Security-as-a-Service Providers
- Astra Security
- Oracle
- Proofpoint
- Qualys
- Okta
7 Risks Security Providers Can Prevent
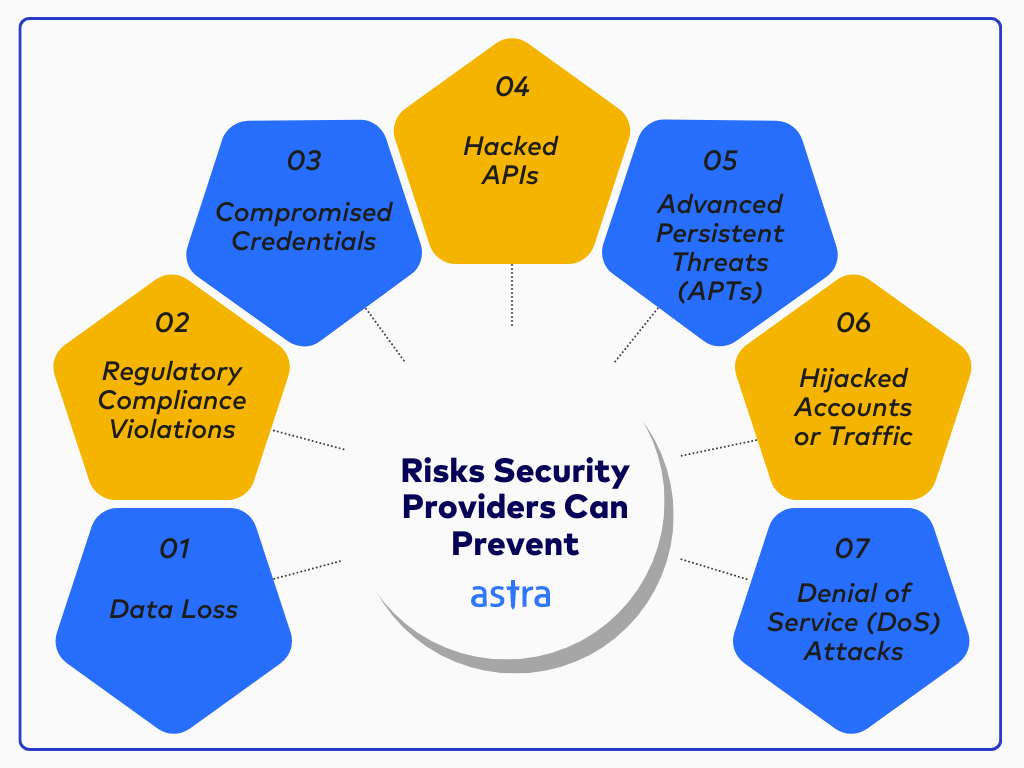
1. Data Loss
Data breaches can result in significant financial losses, damage to reputation, and regulatory penalties. SECaaS providers implement data protection through encryption, setting up access controls, and data backup provisions to prevent unauthorized access and data loss.
2. Regulatory Compliance Violations
Navigating multiple complex cybersecurity regulations can be overwhelming, and achieving compliance is a significant challenge. Hiring a security service provider with expertise in compliance frameworks like GDPR, CCPA, HIPAA, SOC 2, and PCI DSS will help you implement the requirements and attain compliance.
3. Compromised Credentials
Security-as-a-Service providers employ advanced authentication techniques, including multi-factor authentication, and identity and access management solutions to protect their credentials in the event of a leak or theft.
4. Hacked APIs
APIs have quickly become a common target for cybercrime, so it’s essential to look for a security provider specializing in API security solutions. They should provide API discovery and protection against common API vulnerabilities such as injection, broken authentication, and sensitive data exposure.
5. Advanced Persistent Threats (APTs)
APTs are highly advanced attacks that can usually bypass traditional security measures. Protection against them involves SECaaS providers identifying and eliminating vulnerabilities using modern threat detection and response capabilities, such as behavioral analytics and threat intelligence.
6. Hijacked Accounts or Traffic
Account hijacking and traffic redirections can disrupt operations and lead to data breaches. To combat this risk, SECaaS providers deploy network security solutions, such as intrusion detection and prevention systems, to analyze network traffic for any anomalies that indicate unauthorized access.
7. Denial of Service (DoS)/Distributed Denial of Service (DDoS) Attacks
DoS and DDoS attacks can affect even the most secure online services. By employing DDoS protection services, including mitigation techniques such as rate limiting, traffic scrubbing, and load balancing, service availability can be ensured, thereby preventing DoS attacks.
What SECaaS Providers Offer
Security-as-a-Service (SECaaS) providers deliver a suite of managed security solutions tailored to meet the diverse needs of different organizations. Typically, they offer:
- Continuous Threat Monitoring: Round-the-clock monitoring of networks, endpoints, APIs, and cloud environments for suspicious activity.
- Vulnerability Management: Regular vulnerability assessments, penetration testing, and automated scans to spot and remediate security gaps.
- Incident Response: Rapid detection, containment, and remediation of threats through expert-led incident response teams.
- Identity & Access Management: Enforcing multi-factor authentication and granular user access controls to protect credentials and sensitive data.
- Data Loss Prevention: Data encryption, backup, and access protocols to prevent data leaks and unauthorized access.
- Compliance Management: Helping organizations comply with standards like PCI DSS, HIPAA, SOC 2, and GDPR through audit-ready reporting and controls.
- API & Cloud Security: Secure APIs and cloud assets with specialized protections against modern attack vectors.
With SECaaS, organizations gain the benefit of enterprise-grade protection, the latest threat intelligence, and security expertise, without hiring in-house teams or deploying complex infrastructure.
How to Choose the Right SECaaS Provider
Selecting a Security-as-a-Service provider is a critical business decision. Here are the key criteria to evaluate when choosing the correct vendor:
- Breadth of Services: Ensure the provider offers comprehensive coverage, including threat detection, incident response, vulnerability management, API security, and compliance support.
- Expertise & Experience: Look for proven expertise, relevant certifications, and a track record of securing companies similar to yours.
- Scalability & Integration: The solution should adapt as your business grows and integrate smoothly with your existing cloud, DevOps, and IT stack.
- Real-Time Visibility: Prioritize platforms that deliver live dashboards, transparent reporting, and actionable alerts, so you’re always in control.
- Remediation Support: Effective providers don’t just find vulnerabilities, they guide your team through fixing them with contextual support and re-testing.
- Customer Support & SLAs: Responsive, 24/7 assistance and defined service level agreements mean you’re never left exposed when it matters most.
- Client Trust: Seek evidence of satisfied clients, such as recognizable logos, testimonial quotes, third-party awards, or industry partnerships.
By comparing providers on these criteria, you can confidently select a SECaaS partner that truly aligns with your organization’s size, goals, and security challenges.
5 Security-as-a-Service Providers in Different Categories
| Feature | Astra Security | Qualys | Proofpoint |
|---|---|---|---|
| Core Focus | Web Application Security | Network Security, Vulnerability Management | Email Security, Threat Protection |
| VAPT | Yes | No | No |
| CI/CD Integration | Yes | Yes | Yes |
| Zero False Positives | Yes (with vetted scans) | No | No |
| Remediation Assistance | Yes | Yes | Yes |
| Compliance Specific Scans | Yes | Yes | Yes |
1. Astra Security [Get Started]
Web application security testing can involve a combination of continuous vulnerability scanning and penetration testing.
The goals are straightforward: identify vulnerabilities in a web application’s security, assess the risk associated with each vulnerability, prioritize them based on threat level, and address them accordingly.
It’s complex to track every new vulnerability that emerges, every software that needs an update, every third-party vendor that might pose a risk, or every API that behaves oddly. Utilize a security testing company that can assess your security posture, generate a comprehensive report, and assist you in resolving the issues promptly.
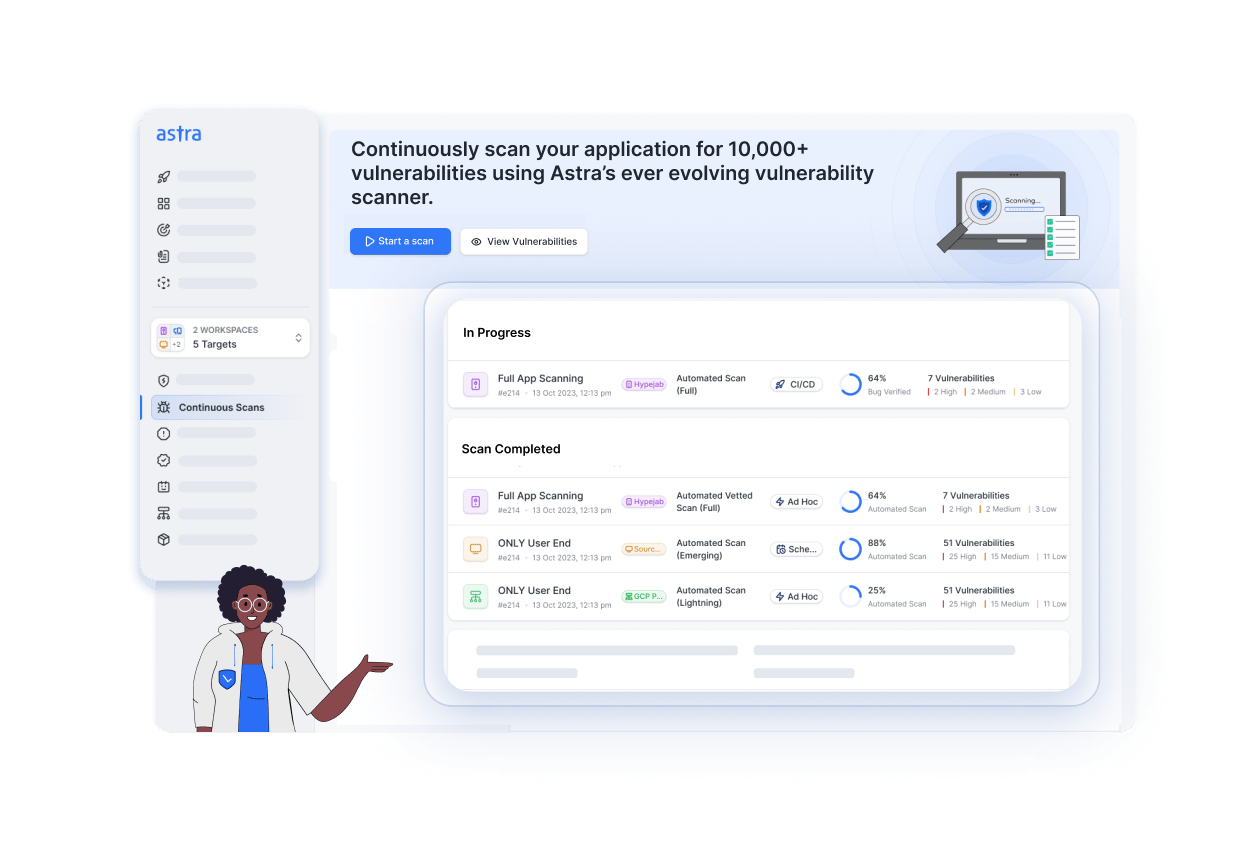
Key Features:
- Platform: SaaS
- Pentest Capabilities: Continuous automated scans with 15,000+ tests and manual pentests
- Accuracy: Zero false positives (with vetted scans)
- Compliance Scanning: OWASP, PCI-DSS, HIPAA, ISO27001, and SOC2
- Expert Remediation Assistance: Yes
- Publicly Verifiable Pentest Certification: Yes
- Workflow Integration: Slack, JIRA, GitHub, GitLab, Jenkins, and more
- Price: Starting at $1999/yr
Astra Security is a web app security testing provider that offers vulnerability assessment and penetration testing (VAPT) services. We incorporate automated scanning and web app pentesting to identify even the most hidden vulnerabilities. We also provide VAPT for networks, mobile apps, APIs, and cloud infrastructures.
Astra’s vulnerability scanner performs over 15,000 tests to detect zero-day vulnerabilities, including security control checks, static and dynamic code analysis, configuration tests, server infrastructure testing, DevOps testing, and business logic testing.
We update this list of tests on a fortnightly basis to stay on top of emerging vulnerabilities. Additionally, our CXO-friendly dashboard allows direct platform interaction with development teams and provides continuous vulnerability tracking.
2. Oracle CASB
Cloud access security brokerages (CASBs) are vendors that sit between cloud providers and cloud users to ensure that each side is upholding its end of the shared responsibility model.
CASBs ensure that the cloud service provider adequately protects the infrastructure and operating systems and help the cloud users secure their data in the cloud.
They also ensure that both parties maintain compliance with industry standards and government-enforced regulations.
Key Features:
- Platform: SaaS
- Core Function: Cloud Access Security Broker (CASB)
- Key Capabilities: Visibility into cloud environments (IaaS, PaaS, SaaS), threat detection with user behavior analytics (UBA), automated incident response, etc.
Oracle CASB offers comprehensive cloud security by providing visibility into cloud environments, advanced threat detection using UBA and threat intelligence, and automated incident response.
It simplifies compliance management through configuration management and seeding while also integrating with existing security tools for enhanced protection.
3. Proofpoint
A significant amount of vital data travels through your cloud-based email servers, which are often the primary target of various cyberattacks. Email can be the primary medium for phishing attacks, social engineering attacks, and clickjacking, so protecting your email servers is imperative.
Some security-as-a-service providers offer email security as a standalone service, while others offer it as part of a complete security package. You can choose the one that best suits you.
Key Features:
- Platform: SaaS
- Core Function: Email Security, Threat Protection
- Key Capabilities: Advanced threat detection (machine learning, behavioral analysis), multi-layered email protection, data loss prevention (DLP), user education, threat intelligence, incident response, identity defense, and account takeover protection.
Proofpoint is a software that protects organizations from sophisticated email-borne threats. Their platform combines advanced threat detection, machine learning, and behavioral analysis with a multi-layered approach to email security.
In addition to traditional email filtering, Proofpoint offers DLP, user education, and identity defense capabilities. Focusing on preventing account takeover and stopping lateral movement, Proofpoint provides comprehensive protection against various email-based threats.
4. Qualys
Network security protects the entire network, including all software and services running on it. It requires a more unique and comprehensive suite of services than testing for a single application does.
SECaaS providers help you monitor the traffic in and out of your network and detect open ports, outdated software, or vulnerable services running on the network.

Key Features:
- Platform: SaaS
- Core Function: Vulnerability Management, Detection, and Response (VMDR), Cloud Security, Compliance
- Key Capabilities: Asset discovery, vulnerability assessment, risk-based prioritization, remediation automation, compliance management, cloud workload protection, container security, and DevOps integration.
Qualys’ expertise lies in vulnerability management, detection, and response (VMDR). Its platform offers security services like asset discovery, vulnerability assessment, and risk-based prioritization.
They offer a range of network security services, including vulnerability management, continuous monitoring, threat protection, and compliance monitoring.
Vulnerability management helps identify and fix weaknesses in systems that attackers could exploit. Continuously monitoring your network can help detect and respond to threats in real-time, and threat protection helps defend your organization against attacks.
5. Okta
Single sign-on (SSO) enables your organization’s members to access any cloud app owned by the organization using a single set of credentials. Google’s SSO is an example of this, and many people use it on several platforms; however, it isn’t a secure solution.
Companies like Okta enable IT administrators to control and manage access easily, quickly set policies and exceptions, and build a more secure environment for everyone.
Key Features:
- Platform: SaaS
- Core Function: Identity and Access Management (IAM), Single Sign-On (SSO)
- Key Capabilities: User authentication and authorization, identity governance and administration, multi-factor authentication (MFA), single sign-on, identity provisioning, integration with various applications and identity providers.
Okta specializes in identity and access management (IAM) solutions, with a strong focus on single sign-on (SSO). Its platform enables organizations to manage user identities securely and provides easy access to applications and resources.
Okta offers a range of features, including user provisioning, de-provisioning, and lifecycle management, as well as advanced security capabilities such as multi-factor authentication and adaptive authentication.
Benefits of Using SECaaS
Adopting Security-as-a-Service (SECaaS) delivers significant advantages for organizations of all sizes:
- Cost-Effective Security: SECaaS eliminates the need for a hefty upfront investment in security infrastructure and specialized personnel. You pay for what you need, when you need it.
- Access to Latest Expertise: Tap into a team of certified security professionals with up-to-date threat intelligence and advanced skills, without the challenge of hiring in-house experts.
- Continuous, Proactive Protection: Enjoy 24/7 monitoring, automated threat detection, and rapid response, minimizing gaps and reducing the window of exposure to attacks.
- Scalability and Flexibility: Easily scale security services up or down as your organization evolves, whether you’re a startup or an expanding enterprise.
- Rapid Deployment: Cloud-based solutions can be activated almost instantly, with minimal disruption and integration hassles.
- Regulatory Compliance Made Simple: SECaaS providers streamline compliance by maintaining controls, reporting, and documentation that are aligned with standards such as PCI DSS, HIPAA, SOC 2, and GDPR.
Focus on Core Business: With security managed by trusted experts, your team can concentrate on innovation, growth, and core business activities, rather than worrying about evolving cyber threats.
Final Thoughts
SECaaS providers have become essential for cloud-based applications and technology-driven companies across various industries. They make it easier and cheaper to manage and monitor the security of organizations of all shapes and sizes.
Outsourcing security functions allows organizations to focus on core competencies while benefiting from advanced threat protection and compliance support. When choosing your provider, consider the scope of services, expertise, compliance certifications, and customer support.
It is essential to select the right security-as-a-service provider for your specific needs. Select a service that seamlessly integrates with your existing processes and secures your organization without compromising functionality.
FAQs
1. What does a security service provider do?
A security service provider (SSP) offers outsourced cybersecurity solutions. They protect businesses from cyber threats by managing IT security, monitoring networks, and responding to incidents.
2. What is the difference between SECaaS and MSSP?
SECaaS (Security as a Service) is a broad term for cloud-based security solutions. MSSP (Managed Security Service Provider) is a type of SECaaS that offers ongoing security management and monitoring services.
3. What is an ISP in security?
In security, an ISP (Internet Service Provider) typically refers to a company that offers internet connectivity with built-in security features like firewalls and intrusion detection systems.
4. What is the meaning of security as a service?
Security as a Service (SECaaS) is a cloud-based model in which a third-party provider delivers security solutions on a subscription basis. It offers services such as threat protection, data loss prevention, and more.
5. What is SECaaS?
Security-as-a-Service (SECaaS) is a cloud-based model in which organizations outsource their cybersecurity tasks to specialized providers. These providers deliver managed security services, such as threat monitoring, vulnerability management, and compliance, via subscription, ensuring robust, scalable, and up-to-date protection without requiring significant investments in in-house resources.
6. What is an example of SECaaS?
Astra Security is an example of SECaaS, offering continuous vulnerability scanning and penetration testing as a cloud service. Organizations can leverage Astra’s platform for automated threat detection, expert-guided remediation, and compliance reporting, all managed remotely with minimal need for internal security staff.
7. What are the four types of security, and examples?
a. Network Security: Firewalls, intrusion detection systems (IDS)
b. Application Security: Web app firewalls, code reviews
c. Endpoint Security: Antivirus, device encryption
d. Cloud Security: Identity access management, cloud workload protection








