PrestaShop has simplified online business for netizens. Be it shopping or selling, e-commerce sites could not have been more in demand. E-commerce rose to prominence and soon turned into an ore of data. Both personal and financial. PrestaShop websites are a quintessential example of this.
The web is full of possibilities as well as threats. PrestaShop hacking stats show that as many as 40% of PrestaShop websites are vulnerable to XSS attacks. Other 26.7% sites are vulnerable to Code injection, 20% to Gain Information attacks, 6.7% to SQL injection, etc. Additionally, a good number of PrestaShop websites run on outdated versions.
Operating your business on a vulnerable site can be a costly affair. This is where the need of a PrestaShop Security Audit & Penetration Testing comes in. A Security Audit can help you identify and fix underlying vulnerabilities in your site.
In today’s post, we are going to talk about how you can do complete a PrestaShop Security audit & penetration testing on your website. You will also find important tools that can make the whole process a breeze.
What is a PrestaShop Security Audit?
A security audit is the systematic analysis of the security of a software (PrestaShop in our case). It includes a thorough analysis of security issues that can be exploited by hackers in order to gain unauthorized access to your infrastructure.
Most PrestaShop sites are easy targets because they are not tested against real-life attacks. Hence, it is recommended to perform a full PrestaShop Security Audit on your site before deploying it for public access.
Learn how simulated attacks help identify vulnerabilities in our Guide to Software Penetration Testing
Why do you need a PrestaShop Security Audit?
Data Breach is the worst thing that can happen to your company. It will ruin your customer’s trust in you forever. There are enough instances where a hack brought complete debacle to a business.
Hackers are interested in data such as email addresses, phone numbers, account numbers, etc. This makes all sites a target. When you throw financial data into the picture the propensity of a hacker towards it go up the roof.
Being a desirable target and being vulnerable at the same time can be disastrous, to say the least. To protect your website and eventually your business, it is necessary to patch each and every vulnerability on your website. PrestaShop Security Audits and Penetration Tests do exactly that.
Steps to carry-out a PrestaShop Security Audit
A good security audit will analyze every asset on your website (including add-ons, themes, core, etc.) for security vulnerabilities that can be exploited by hackers. It will map out all the security issues in a detailed report containing how to reproduce them. A PrestaShop penetration test, then, exploit these vulnerabilities. This step is crucial to estimate the weight of a vulnerability.
The first step is – Manual enumeration.
During this step, you will enumerate all the information that you can about the target i.e PrestaShop Website. This includes things like:
- the version of the software
- usernames
- login pages
- webpages
- any hidden information available on the site
There are various automated tools available for this. However, it is recommended that you follow the automated enumeration with some manual inspection.
A few of the automated tools are mentioned below:
1. Mozilla Observatory: Uncover CVE’s
Mozilla HTTP Observatory is one of the best online vulnerability scanners on the web. It is was made by the Mozilla Foundation. This vulnerability scanner will use different methods to identify security vulnerabilities and offer a fix to them.
In order to scan your site follow these steps:
1. Got to https://observatory.mozilla.org/
2. Enter your site URL in the ‘Scan Me‘ bar. That’s it!

3. The site will show you, your PrestaShop installation report.

This is will be a good starting point for your PrestaShop Security Audit. This will point out all the low-level security misconfigurations and version based CVEs that hackers can exploit against your site.
2. GoBuster: Detect Vulnerable Files & Directories
The method of trying common directories or file paths on a website to retrieve hidden file paths or directory is called Directory Busting or Dir Busting.
The tool we are going to use is GoBuster. It is simple and fast. It requires two arguments to run. First, the website you wanna attack (in our case is the PrestaShop Installation) and second, the wordlist you wanna attack it with.

The wordlist I’ll recommend is this one. It has a decent length and has all the common file paths and names that are generally exposed.
Now run the tool with the following command:
gobutser dir -u http://example.com -w wordlist

Once you find all the exposed file names, hide the sensitives ones and you are good to go.
3. LFI/RFI check
Local File Inclusion or Remote File Inclusion flaw allows an attacker to include a local file such as “/etc/passwd” or a remote file (mostly a malicious script) to be hosted on the server. This attack can allow an attacker to read source code file which may help in further exploitation or get Remote Code Execution(RCE).
The trick to noticing this attack is pretty simple. Since this attack depends on improper validation which can be exploited, you may be able to leak contents of file “/etc/passwd” on a Linux server.
If the above payload works you have potential LFI/RFI vulnerability. Try out some of these payloads to increase damage.
4. Password Brute Forcing
If the login form you found is not vulnerable to SQL Injection, Password Brute Forcing might get you access. The idea is to try all common passwords for a user until one of them works. The tool used for this process is Hydra.

Hydra is a popular brute-forcing tool used for this attack. You also can write your own script but hydra is optimized for speed thus will lot quicker. To use hydra simply run the command:
hydra [some command line options] [-s PORT] TARGET PROTOCOL [MODULE-OPTIONS]
PrestaShop Security Audit & Penetration Testing by Astra
I hope you did a successful security audit with the steps above. In case you didn’t, we are here to help.
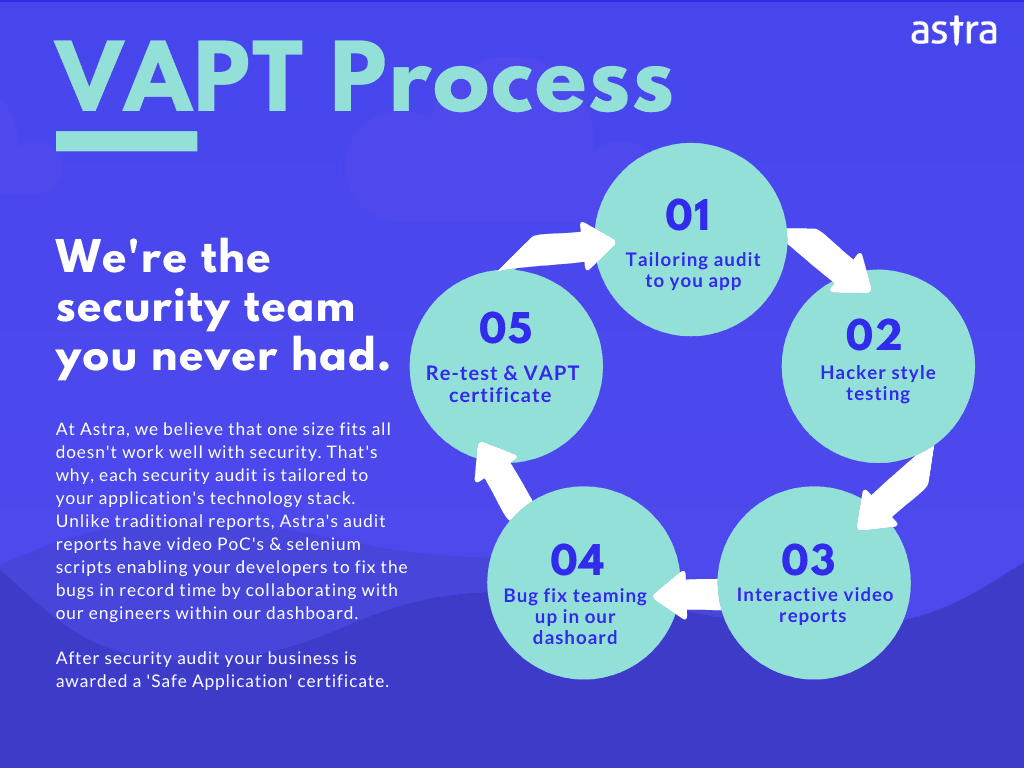
Astra offers PrestaShop VAPT services that will make sure all the security vulnerabilities in your PrestaShop Site are corrected before it is deployed.
Sign up with Astra’s Vulnerability and Penetration Testing and leave the hard part to us. Astra’s hacker style security testing offers real-world attacks to the website and provides precise results of the vulnerabilities in your website.
Additional Read: WooCommerce Security Audit
This VAPT program covers detailed code analysis, business logic error testing, infrastructure testing, server configuration testing, and more.
The expert team of Astra makes sure no damage to the infrastructure is done during the audit. Astra makes sure that no security bug or vulnerability in your website is gone unseen. Thus provides rock-solid protection to your website and infrastructure from hackers.
Conclusion
The blog talked about why PrestaShop Security Audit is important for your company and how you can perform it in simple steps. Hackers are waiting for you to make one mistake. It’s better to secure your website before that.
If all this seems a hassle to you, you should check out Astra. Astra provides rock-solid security to your company’s infrastructure.








Hi, what folder permission must be assigned in a prestashop based site? I am not a developer but I would like to secure my store in every possible way.
Thanks for reaching out to us. Prestashop file permission should not be confused with the only security measure for your website. Yet, we can’t disagree that it carries its own importance. It can come handy in defending your website from some of the common attacks.
Are there any addons or plugins that I can use which are helpful for my store. I am running a prestashop store btw.
Thanks for responding to the article. PrestaShop, for sure, is one of the top CMS(s) available for e-commerce. Its versatility and flexibility add to its excellence. Plus, it is also budget friendly. If you already own a shop on Prestashop, you might want to look further for different tools to take care of the varied aspects of an online e-commerce store.
How can I secure my prestashop? I am hearing a lot of attakcs are happening on the stores by hackers.
Thanks for responding to the article. PrestaShop, no doubt, is a lucrative target for hackers. Hackers are continuously on the hunt for an overlooked vulnerability in popular CMS(s). They are always on the lookout for new methods to deliver their payload like injecting malware in the traffic of open Wi-Fi via ARP poisoning. Further, PrestaShop Malware is any kind of malicious code deployed by the hackers via a vulnerability in order to exploit a Prestashop store.
Are there any fake accounts that can be created in prestashop? If yes how and how can I protect my store?
Thanks for responding to the article. If you are running a website on PrestaShop then there is a reason for you to worry. According to PrestaShop, it is under massive spam exploit.
Hi there, so what is the difference between Prestashop and woocommerce?
Thanks for responding to the article. Well, PrestaShop & WooCommerce are both open-source platforms to build your e-commerce websites on. Hence, the dilemma of choosing one between them. We have detailed article comparing both of them visit here: https://www.getastra.com/blog/cms/prestashop-vs-woocommerce/
I own a prestashop store and I heard a lot of credit card hacks are going now. Is there a way I can defend against them?
Thanks for responding to the article. Prestashop credit card hijack can be conducted in multiple ways. It could be a malicious script on the server or lines of Javascript. Often it can be an SQL injection or a phishing page. So this diversity of possibility makes it hard to detect.
Is there any way we can perform an audit on our own for prestashop? If possible how?
Thanks for responding to the article. Yes, you can go through this article on how exactly you can do a security audit of your prestashop store. For more info, visit here: https://www.getastra.com/blog/security-audit/prestashop-security-audit-and-penetration-testing/ If you need a professional help, visit here: https://www.getastra.com/prestashop-vapt
Would like to know about the top breaches in prestashop and its statistics cause it’ll be helpful for me to understand better before getting into it.
Thanks for responding to the article. So, we have a detailed article ready on this and you can get detailed info on everything. For more info visit here: https://www.getastra.com/blog/cms/hacking-statistics/#Hacking_Statistics_in_PrestaShop