Tasked with securing complex digital assets without compromising on business goals, CTOs often face conflicting priorities. With growing cybersecurity risks as well as resource constraints, they are often forced to choose between internal and external vulnerability scanners.
The terms “internal” and “external” can be misleading, as both types of scanners can potentially identify vulnerabilities within the organization’s network. However, the primary difference lies in their scope and access, which can lead to confusion and potential security gaps. Let’s take a better look at each of them individually!
What is an Internal Vulnerability Scanner?
An internal vulnerability scanner is a security tool that examines your internal systems, servers, and applications from within to identify potential weaknesses like unpatched software, misconfigured settings, or weak passwords.
Such a scanner uses asset discovery, vulnerability signature matching, exploitation, and configuration auditing techniques to pinpoint and analyze the impact of potential attacks.
What is an External Vulnerability Scanner?
An external vulnerability scanner is an automated tool designed to simulate hacker-like attacks to identify and assess potential security weaknesses in systems accessible from the Internet, such as networks, websites, and applications, for vulnerabilities that could be exploited.
Such a scanner uses port scanning, DNS enumeration, credential stuffing, fuzzing, and exploitation to simulate real-world attacks.
Astra Pentest is built by the team of experts that helped secure Microsoft, Adobe, Facebook, and Buffer

Internal vs External Vulnerability Scanner
| Feature | Internal Vulnerability Scanner | External Vulnerability Scanner |
|---|---|---|
| Purpose | Identifies vulnerabilities within an assigned perimeter of the asset. | Identifies vulnerabilities exposed to the internet. |
| Scope | Scans systems, applications, and networks within the organization's internal infrastructure. | Scans systems, applications, and networks accessible from the internet. |
| Access | Requires internal application access and credentials. | Does not require internal access but may need credentials and asset mapping for specific scans. |
| Focus | Identifies vulnerabilities that could be exploited by insiders or compromised systems. | Identifies vulnerabilities that could be exploited by external attackers. |
| Common Techniques | Asset Discovery, port scanning, vulnerability signature matching, exploit testing, configuration audits | Network scanning, port scanning, DNS enumeration, web application scanning, exploitation, fuzzing. |
| Advantages | Provides a more comprehensive view of the organization's security posture. Can identify vulnerabilities that may not be detectable from the outside. | Identifies vulnerabilities that could be exploited by external attackers. It can help prevent public-facing breaches. |
| Disadvantages | May not detect vulnerabilities that are only accessible from the internet. Requires internal network access and credentials. | May not detect vulnerabilities that are only accessible from within the network. |
| Use Cases | Internal security assessments, compliance audits, and vulnerability management programs. | External security assessments, penetration testing, and risk management. |
How Does a Vulnerability Scanner Work?
1. Internal Vulnerability Scanner
Internal vulnerability scanners start by systematically locating and cataloging all an organization’s connected devices, operating systems, and services for comparison against a comprehensive vulnerability database. Using the login creds, the scanner also scans behind login screens to assign risk scores to each CVE based on its severity and potential impact.
In some cases, exploit testing may be performed in a controlled environment to assess the actual impact of vulnerabilities. Finally, it generates a detailed report outlining identified vulnerabilities, their severity, affected assets, and remediation recommendations.
2. External Vulnerability Scanner
An external vulnerability scanner simulates an attacker’s perspective to identify potential weaknesses in a network’s public-facing assets. It starts by discovering public assets through DNS enumeration and IP address scanning and then probing them for open ports and services.
Once the CVEs have been identified, they assess their severity and provide recommendations for remediation. Unlike internal scanners, external scanners have limited access and focus solely on the network’s external perimeter.
Essential Features To Look For in a Vulnerability Scanner
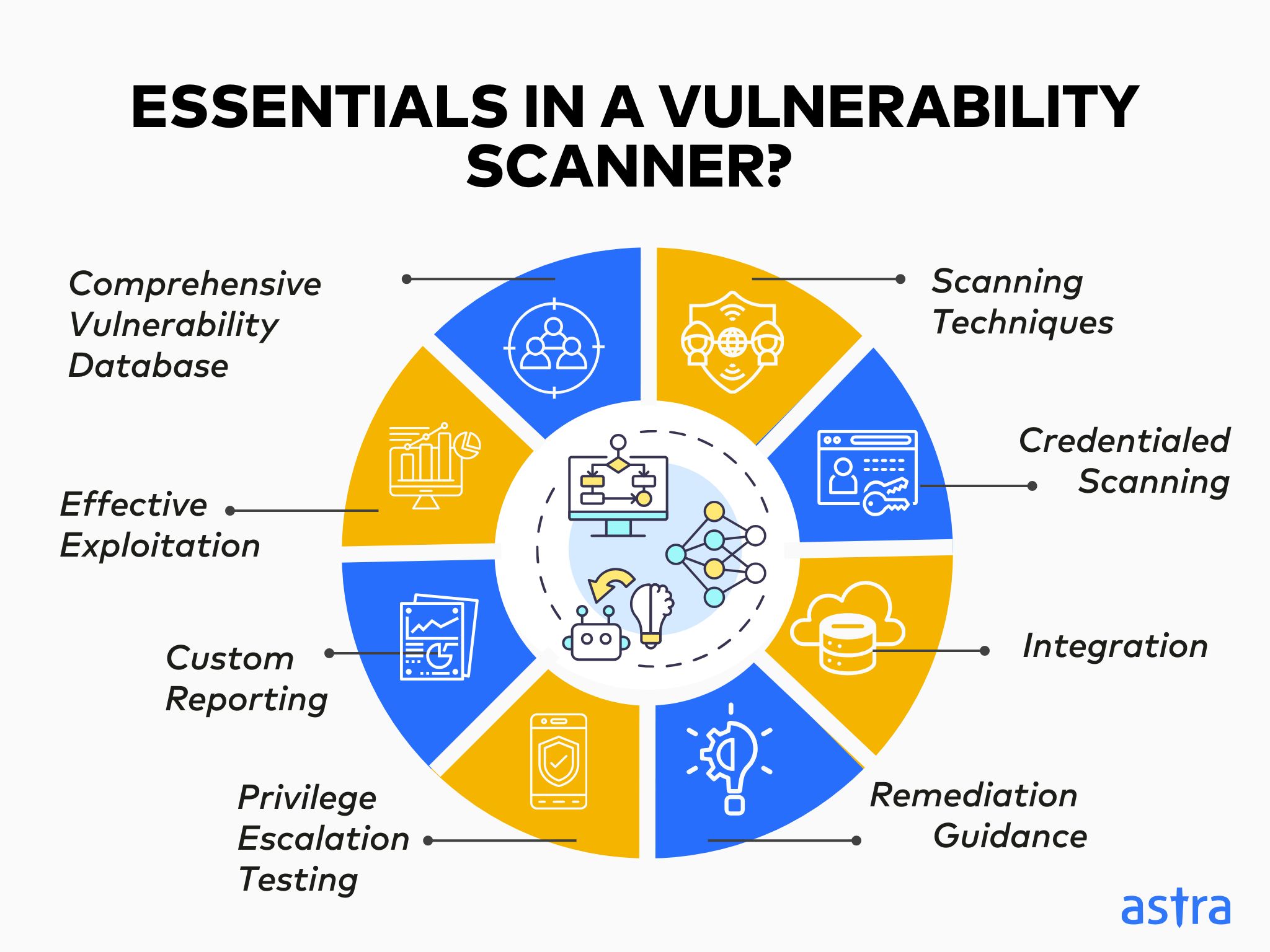
1. Comprehensive Vulnerability Database:
Access and integration into a robust database of known vulnerabilities is vital for internal and external scanners to identify potential threats accurately.
2. Advanced Scanning Techniques:
Both internal and external scanners should employ advanced scanning techniques, such as heuristic and web application scanning, to detect a wide range of vulnerabilities.
3. Credentialed Scanning:
For internal scanners, the ability to use valid credentials to gain access to systems and perform more in-depth scans is crucial. External scanners may also require credentials for specific scans, such as a grey-box automated pentest.
4. Effective Exploitation:
Both types of scanners must be able to test identified vulnerabilities to confirm their existence and gather additional information on their impact and severity.
5. Custom Reporting:
The ideal scanner should provide detailed reports summarizing identified vulnerabilities, their severity, and potential impact customized to the needs of their audience, i.e., short executive management reports and detailed reports for dev teams.
6. Remediation Guidance:
The best scanners offer step-by-step remediation guidance to help organizations effectively address the vulnerabilities identified in the scans.
7. Integration with Other Security Tools:
Internal and external scanners should integrate seamlessly with other workflow and CI/CD pipeline tools, such as GitHub, GitLab, Slack, JIRA, and other security information and event management (SIEM) solutions.
8. Privilege Escalation Testing:
The scanners should be able to test for privilege escalation vulnerabilities, which allow attackers to gain elevated privileges within a system.
It is one small security loophole v/s your entire website or web application.
Get your web app audited with
Astra’s Continuous Pentest Solution.

Which is the Best Scanner for You?
Choosing between an internal and external vulnerability scanner depends on your specific security needs and goals. If your primary concern is identifying vulnerabilities within your internal infrastructure or patching possible insider threats, an internal vulnerability scanner is the best choice.
On the other hand, an external vulnerability scanner is the better option if you want to assess the security of your internet-facing systems and identify vulnerabilities that external attackers could exploit. Ultimately, the best approach is to use a scanner like Astra that combines the functionalities of internal and external scans to view your security posture comprehensively.
How can Astra’s Vulnerability Scanner Help Secure Your Assets?
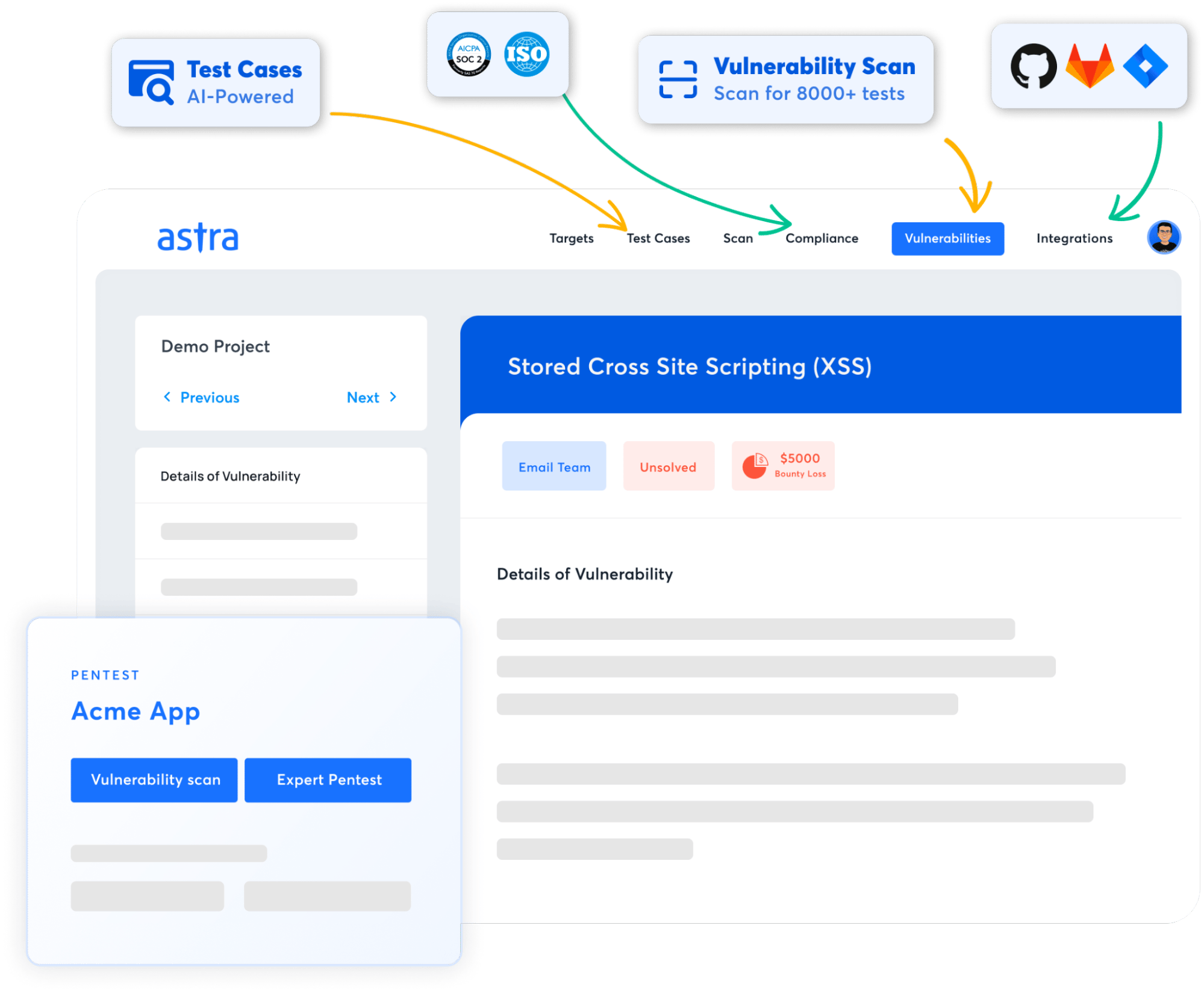
Astra’s external vulnerability scanner runs 10,000+ tests to check for emerging and existing vulnerabilities per OWASP, NIST, and SANS25. It scans your web applications and the API integrations it consumes.
While our vetted scans guarantee zero false positives, the scan-behind-login and in-depth hacker-style automated penetration tests with port scanning and subdomain takeover reveal critical vulnerabilities across assets and industries.

Why is Astra Vulnerability Scanner the Best Scanner?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Final Thoughts
While internal and external vulnerability scanners are crucial for pinpointing CVEs and zero-days, based on their focus areas – they serve specific purposes.
Simply put, internal scanners are primarily used to assess vulnerabilities within an organization’s internal network, while external vulnerability assessment tools help identify vulnerabilities that malicious external actors can exploit.
You can significantly enhance your security posture and compliance by effectively utilizing both, or ideally, a tool that combines their strengths.
FAQs
What is an external vulnerability scan?
An external vulnerability scan scans the front-facing network and web applications from an outside perspective to find vulnerabilities or weaknesses that could be exploited by hackers.
What are some of the best open-source external vulnerability scanners?
Some of the best open-source external vulnerability scanners include Nikto, OpenVAS, and W3AF.
What is the price range of a good external vulnerability scanner?
A good external vulnerability scanner like Astra Pentest provides affordable customizable prices that vary from $199 per month to $5999 for a fully inclusive package.