AWS vulnerability management is the continuous process of identifying and managing vulnerabilities within your organization’s AWS environment. Vulnerability management in AWS also includes reporting and remediation of detected security risks and is a vital practice in good AWS security management.
This article will provide you with an in-depth understanding of the processes, steps, benefits and tools that come under AWS vulnerability management.
Processes That Come Under Vulnerability Management In AWS
Here’s a list of the processes that come under AWS vulnerability management aiding in the efficient identification and mitigation of flaws within the AWS environment.
Vulnerability Scanning
Vulnerability scans are automated tests carried out for ease of use and quickness. They detect any vulnerabilities present in the assets through a quick scan after which an automated vulnerability scan report is generated for the customers.
Vulnerability Assessments
Vulnerability Assessments are a bit more comprehensive when compared to scans, it involves vulnerability scans which is later evaluated and prioritized according to their potential impact. This is then mentioned in the vulnerability assessment report along with remediation measures and PoC videos for the resolution of each vulnerability.
Penetration Testing
The most comprehensive process under AWS vulnerability management, penetration tests are great for assessing the security in AWS cloud environment in an in-depth manner. However, they take time and can be costly. Therefore it is carried out once or twice a year to find and exploit vulnerabilities to understand their true impact.
Remediation And Patching
One of the most important processes within AWS vulnerability management is the remediation and patching of the vulnerabilities detected and identified. Patching can be done using automated tools or if they are extensive, then carried out manually.
AWS Vulnerability Management Best Practices
Here are some of the best practices to follow when maintaining you AWS platform.
Continuous Vulnerability Scanning
Continuous vulnerability scanning helps greatly with vulnerability management in AWS. A good AWS cloud vulnerability scanner should be able to continuously scan and detect even the most minute of vulnerabilities.
It should also have an extensive vulnerability database so that all vulnerabilities are rightly assessed. The tool should also have features like behind-the-login scans, detection of logic errors, false positive detection as well as ensure that are no false negatives.
Varied Integrations
Integrating vulnerability scanning into the development allows for continuous scanning for vulnerabilities throughout the progress of the application.
Such integration also allows AWS customers to be continuously compliant with the important regulatory standards they need to abide by like GDPR, ISO 27001, HIPAA, and PCI-DSS.
Regular Penetration Testing
Regular pentests are an excellent practice for AWS vulnerability management. They go a step further from vulnerability scanning by exploiting the found vulnerabilities to properly assess the extent of damage that could occur from such an attack in real-life.
Updated Software
Ensure that your applications and security measures within the AWS environment are regularly updated to reduce the chances of any security gaps and the potential risk of exploitation.
Timely updation allows the patching of any vulnerabilities with your software in the AWS platform.
Using AWS Services
AWS provides a variety of security tools such as AWS Security Hub, AWS Inspector, AWS Identity, and Access Management among others, all of which play a crucial role in helping you maintain the security of your AWS environment without any compromise.
Incident Response Plan
It is vital to create and implement an incident response plan since in the event of a security incident it helps shorten the response time, and speed up the recovery process as well. The plan should include steps for the identification and resolution of the incident with communication measures and recovery plans.
Major AWS Security Services Provided by AWS
Amazon Web Services provides a lot of tools to heighten the security measures within their platform. Customers can choose and use them based on their requirements. Few of the important ones are:
AWS Security Hub
AWS Security Hub is a cloud security posture management service that enables the automation of security checks for best practices and aids with the acceleration of mean-time response through automated response and remediation.
It performs a quick analysis of the attention-demanding security alerts across all regions and accounts within your AWS platform. It consolidates these findings to a standard format to allow you to take quicker action.
This service in tandem with others provided by AWS like AWS Inspector, Amazon Macie, and more allows you to have a 360-degree view of your AWS security.
AWS Inspector
This automated vulnerability management service helps by performing continuous scans of the automatically detected AWS workloads for vulnerabilities and unintentional exposures. After a few easy steps to enable its services, AWS Inspector can be used across all your AWS accounts.
Once enabled, it discovers EC2 instances and images within the Amazon ECR (Elastic Container Registry) and starts assessing them for flaws or areas of exposure. It provides a highly contextualized risk score that factors in a lot of criteria through the correlation between CVEs, network accessibility, and exploitability.
AWS Shield
AWS Shield is one of the AWS security services that provide protection to the infrastructure such as network connections. It provides protection against DDoS attacks thus securing the applications running on the AWS cloud.
AWS Shield is of two types: Standard and Advanced. Standard Shield protects against basic threats like common network DDoS attacks. Advanced Shield goes above and beyond the standard services by also providing identification and prevention of large-scale DDoS attacks, integration, and closely monitored visibility of attacks.
AWS Identity And Access Management
This service allows one to define and set parameters for access with specific credentials, and to scale the privileges as and when required. It allows you to fine-tune the access and authorization allowing you to decide which individuals, groups, or roles can access certain information.
The features offered by AWS IAM include:
- AWS Single Sign-On
- Manage permissions for single accounts
- Manage single-account roles
Steps in AWS Vulnerability Management
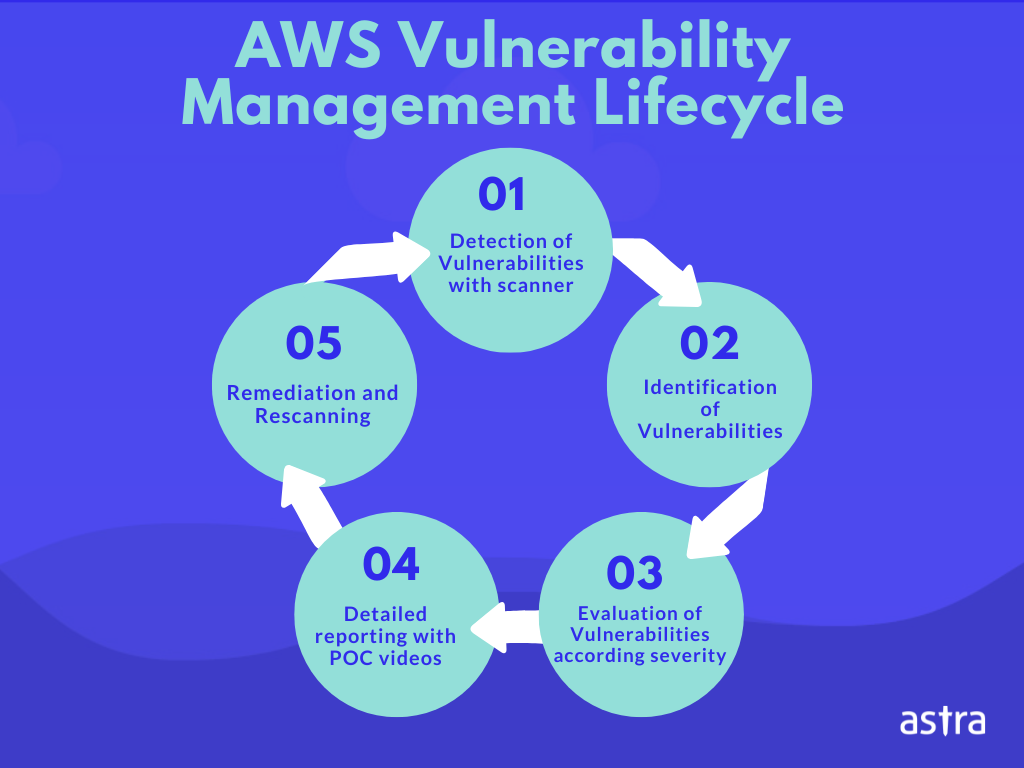
The below detailed are the steps taken in AWS threat and vulnerability management.
Identification
The initial step in a well-implemented AWS vulnerability management program involves the identification of vulnerabilities. This is done using comprehensive vulnerability scanners capable of detecting a wide range of vulnerabilities.
This step results in the detection of known CVEs, and vulnerabilities mentioned in standard frameworks like the OWASP Top 10 and SANS 25. Your assets are mapped out in detail and scoured for any flaws, gaps, or vulnerabilities that pose a threat to your cloud environment.
It is vital to schedule such scans during slower traffic times as it can cause disruptions in regular operational conditions.
Vulnerability Prioritization
The identification of vulnerabilities is followed by their matching to the vulnerability database at hand. They are assessed further to understand the extent of their threat levels.
The evaluation of identified threats aids in their prioritization according to the mentioned risk levels posed by each vulnerability. This allows a team to understand which of the vulnerabilities need to be fixed immediately and make a diligent plan in lieu of it.
The most common system used to identify the extent of threats posed and prioritize them is the CVSS system. Based on the CVSS scores, potential threat impact, and other contextual data, the vulnerabilities are prioritized for patching.
Vulnerability Reporting
The AWS vulnerability testing report has details such as the executive summary of the scan, the methods employed to detect vulnerabilities, and the vulnerability database used as a standard reference.
Along with this, the vulnerabilities found are listed and extensively explained with their CVSS scores as well as possible remediation measures.
Vulnerability Remediation
Once the vulnerabilities are assessed according to the risk they pose, it is now time to respond and fix each flaw found. This is done based on the data from the risk assessment.
Based on the threat level there are general measures that can be opted for to create a viable and healthy security solution for the cloud. These measures include:
- Fixing the highest risk posing vulnerabilities immediately based on their risk severity is known as patching.
- When fixing the problem at hand isn’t a feasible solution, then the risk posed by them is managed thus reducing the chances of them being exploited. This is known as mitigation.
- Sometimes if the vulnerabilities discovered are not critical or have a low CVSS score, they are left as such since the chances of them being exploitable are minuscule.
Rescanning
The final step is to avail a re-scan to ensure that your AWS platform is safe from the initially found vulnerabilities. This assures, builds, and increases trust for your existing and potential clients. It also increases your reputation as a safety-conscious provider and increases trustworthiness.
Top AWS Vulnerability Management Companies
Here are some of the top AWS vulnerability management companies that you should consider:
Astra Security
Astra Pentest, one of the best vulnerability management providers, provides a world-class comprehensive vulnerability scanner with the following features for effective vulnerability management:
Comprehensive vulnerability scanner
Astra Pentest provides continuous scanning facilities with its comprehensive scanner that is capable of conducting more the 3000 tests to find any and every hidden vulnerability.
It offers deep scans for web applications, APIs, networks, mobile applications, and cloud infrastructure.
Detailed Reports
Once the vulnerability scanning is completed a report is generated which includes the scope of testing, a list of vulnerabilities found, their details, and possible remediation measures.
It also mentions its CVSS score and Astra goes a step further by providing customers with an actionable vulnerability risk score based on which critical vulnerabilities can be prioritized.
Remediation Support
Once vulnerability scanning with Astra is complete Astra also provides detailed steps for remediation based on risk prioritization. This is done with the aid of POC videos and collaboration within the vulnerability dashboard.
Alert Logic
AlertLogic is a well-known SOC-as-a-service and vulnerability management provider that provides managed threat detection and response services (MDR).
Their holistic services include 24*7 threat monitoring, incident validation, remediation, log management, and more.
Orca Security
Orca Security helps you cover vulnerabilities its vulnerability management services for cloud infrastructures like AWS, Azure, and Google Platform. It combines all cloud assets in a single graph and supports more than 40 CIS benchmarks and other security regulations.
Orca’s vulnerability management program makes actionable data easily available to the right teams. Managed services from Orca Involve a simple 3-step process that includes discovery, monitoring, and assessing the assets.
Benefits Of Vulnerability Management In AWS
Vulnerability management forms a crucial component in maintaining the AWS infrastructure. Here are some of the benefits that comes from AWS vulnerability management.
Reduces Chances of Security Breaches
Identifying potential threats and addressing vulnerabilities in one’s AWS environment plays a significant role in reducing the risk of security breaches and protect sensitive information.
Aids in Maintenance of Compliance
AWS vulnerability management aids companies in achieving and maintaining regulatory compliance for standards such as PCI-DSS, SOC2, ISO27001, and HIPAA.
By implementing the best practices in AWS vulnerability management, you become compliant with the requirements put forward by international standards.
Better Visibility To Your AWS Environment
Efficient and effective vulnerability management in AWS provides great visibility and transparency to your AWS environment. This helps in the identification of potential threats and mitigatory steps to thwart the same.
Comes With Remediation Assistance
Vulnerability management isn’t just about detection and identification of vulnerabilities, but also its remediation. Once the detection of vulnerabilities is done, vulnerability management companies provide assistance in order to ensure effective patching and mitigation of risks.
Time And Cost Effective
Organizations spend valuable time fixing the after-effects of the exploitation of vulnerabilities rather than the vulnerabilities themselves. This is where having good AWS vulnerability management helps save time and a lot of manpower.
This quick detection and remediation of flaws mean that the amount spent on fixing the vulnerabilities and dealing with the blowout from the exploitation of these vulnerabilities will be significantly reduced.
Builds Customer Trust
Having a AWS vulnerability management program instills trust and confidence in customers with regards to the cybersecurity measures maintained to protect their data in AWS.
Since AWS vulnerability management ensures the continuous detection and remediation of vulnerabilities, customers can rest assured that their information is in safe hands.
Conclusion
This article talks in detail about the various facets of AWS vulnerability management while describing the processes that are used for the identification of vulnerabilities. Alongside various risk assessment measures, vulnerability patch management is also a crucial component of AWS vulnerability management.
With more and more companies migrating to the cloud environment, security and compliance is more important than ever and as such, companies need to actively make an effort to keep their AWS platform secure.
FAQs
What is AWS vulnerability scanning?
AWS vulnerability scanning is the process of meticulously analyzing the AWS environment for the presence of any vulnerabilities that could lead to compromise of a companies AWS platform and the sensitive information stored.
Does AWS have a vulnerability scanner service?
AWS offers its vulnerability management service program called AWS inspector which comes with a vulnerability scanner to detect vulnerabilities inside an AWS environment.
















