Imagine moving into a smart home with automated locks, motion sensors, and AI-driven surveillance. Everything looks secure. But what if the front door’s passcode is weak, the security cameras aren’t monitored, and a backdoor is left unlocked? The technology is there, but small gaps make it easy for intruders to walk right in.
This is how many organizations approach Azure cloud security. They assume built-in controls will keep threats out, but misconfigurations, excessive permissions, and unmonitored assets create openings that attackers can exploit. A single overlooked setting—an overprivileged account or an unpatched container—can become a full-blown breach.
Cloud security isn’t about stacking more tools but designing protocols that actively prevent, detect, and respond to threats before they escalate.
What is Azure Cloud Security?
Azure Cloud Security is the set of controls, tools, and strategies that protect applications, data, and workloads within Microsoft Azure, including identity management, network security, threat monitoring, and compliance enforcement.
From securing DevOps pipelines to enforcing least privilege access across distributed teams, Azure infrastructure security ensures businesses can scale without making trade-offs between innovation and protection.
Benefits of Cloud Security in Azure
Security is no longer just about keeping threats out; it’s about building resilience. CTOs and security engineers must think beyond firewalls and focus on securing the entire attack surface. Azure offers a security-first cloud ecosystem designed to protect, adapt, and scale with modern business needs.
1. Bridging Hybrid Security Gaps
Hybrid cloud is like managing both a high-rise office and a remote cabin, you need security that works everywhere. Azure’s Arc-enabled security ensures that workloads remain uniformly protected, whether on-prem, in the cloud, or at the edge.
Zero Trust principles and Defender for Cloud proactively monitor and remediate vulnerabilities, giving security teams a single pane of glass for risk management.
2. Confidential Computing & Data Protection
Sensitive data isn’t just stored; it’s constantly in use, making it vulnerable. Azure’s Confidential Computing acts like a bank vault that locks up data even while it’s being processed.
With hardware-backed encryption and secure enclaves, enterprises can ensure that even cloud administrators and attackers with root access can’t see the data. Pair this with Microsoft Entra ID and Azure Key Vault, and you have a security architecture that locks out unauthorized access at every level.
3. Scalability Without Security Trade-offs
Security shouldn’t slow down growth. Azure’s adaptive security model automatically ensures that every new node, user, or workload inherits security policies.
With DDoS Protection and Sentinel SIEM, businesses get real-time threat intelligence without the overhead of manual intervention. The pay-as-you-go model in cloud security Azure ensures that security investments align with usage, preventing unnecessary costs.
4. Security Automation & Proactive Threat Detection
Attackers move fast, but AI moves faster. Azure’s AI-driven security automates threat identification, analysis, and mitigation in real time, while Microsoft Defender for Cloud continuously evaluates security posture, offering proactive recommendations and auto-remediation options to ensure your teams spend less time firefighting and more strategizing.
5. Enterprise-Grade Compliance & Governance
Regulatory compliance shouldn’t feel like red tape but a competitive advantage. Azure’s compliance portfolio covers 100+ global standards, including ISO, NIST, GDPR, and HIPAA, offering policy-based access controls and audit-ready monitoring, such that enterprises can enforce governance while maintaining operational agility.
Best Practices for Strengthening Azure Cloud Security
Cloud security isn’t a settings problem—it’s a strategy problem. Azure offers robust tools, but security gaps pile up like technical debt without a structured approach. The real challenge? Designing security that evolves as fast as threats do.
1. Clarify Shared Responsibility to Close Security Gaps
Cloud security often fails due to unclear boundaries. Think of it like renting an apartment—Azure secures the building, but locking your doors and setting up cameras is your job.
Key actions:
- Conduct a responsibility mapping exercise to define ownership for identity management, data security, and workload protection.
- Automate policy enforcement using Azure Policy to prevent misconfigurations before they become vulnerabilities.
- Audit permissions continuously to prevent privilege creep from turning into a security liability.
2. Make Monitoring a Living Process
Many security teams treat monitoring as a static checklist. In reality, it’s more like checking the pulse of a patient—vital signs change, and ignoring early symptoms leads to bigger problems.
For an effective monitoring strategy, ask:
- What are the early indicators of compromise in your environment?
- Are you correlating identity, network, and workload data for deeper insights?
- How quickly can you act on alerts without creating alert fatigue?
Azure Security Center and Microsoft Sentinel provide insights, but real security comes from action. Automate remediation where possible, but ensure your team remains in control.
3. Strengthen IAM Before Attackers Exploit Weak Links
Compromised credentials remain the most straightforward way in for attackers. Think of your IAM strategy like a high-security vault: the fewer people with access, the lower the risk of a break-in.
IAM best practices:
- Use role-based access control (RBAC) to enforce least privilege.
- Require multi-factor authentication (MFA) for all users, especially admins.
- Set up Conditional Access policies to restrict logins based on risk signals.
- Automate access reviews to prevent outdated permissions from lingering.
4. Treat Cloud Penetration Testing as a Reality Check
Security tools tell you how things should work. Cloud penetration testing tells you how attackers can actually break in.
Why external testing matters:
- Attack simulation: Red teams test your Microsoft Azure cloud security like real-world adversaries would.
- Beyond automated scans: Manual pentests uncover logic flaws and chained exploits that automated tools miss.
- Actionable insights: Get tailored fixes for your specific Azure environment instead of generic reports.
5. Extend Protection with Microsoft Defender XDR—But Configure It Right
Think of Microsoft Defender XDR as a security camera with AI—powerful, but only if positioned correctly. Too many teams deploy it without fine-tuning detection rules, leading to blind spots.
What to configure for better results:
- Customize behavioral detection to flag anomalies in privilege escalation.
- Integrate Defender for Kubernetes and Defender for Storage to secure cloud-native workloads.
- Use automated responses to contain threats before manual intervention is needed.
How can Astra Help?
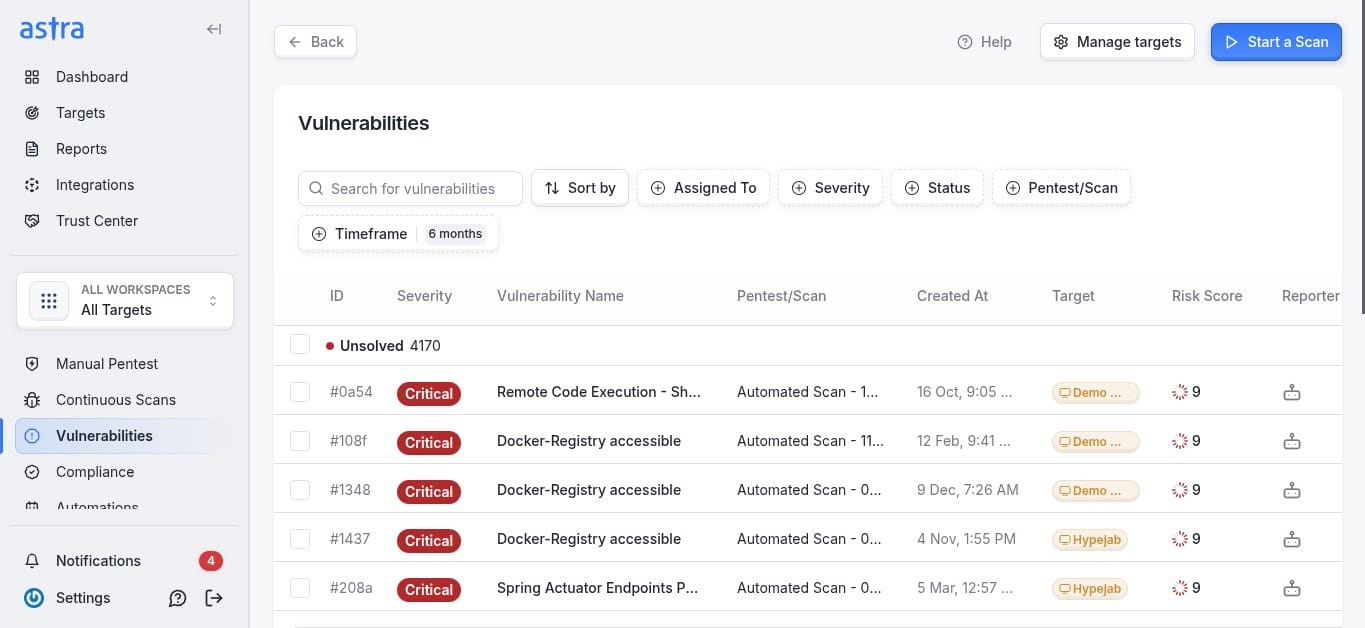
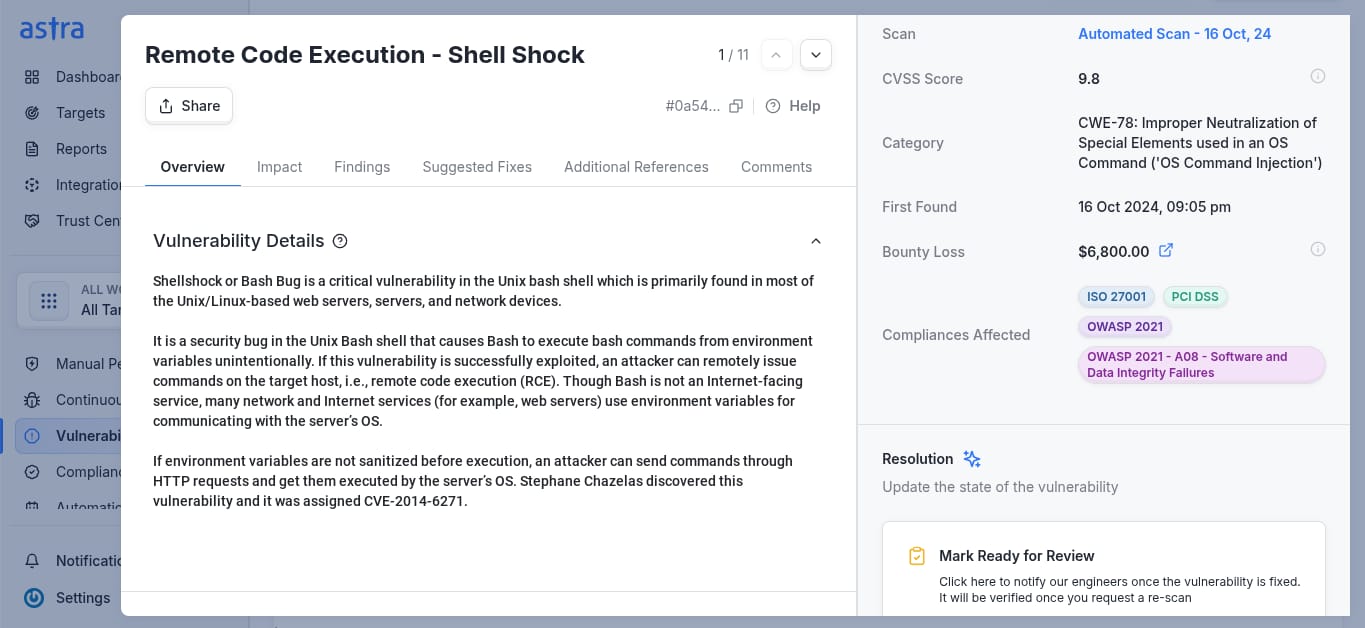
Astra’s cloud security and penetration testing goes beyond surface-level scans, offering a deep dive into IAM, network security, logging, and Azure cloud VM configurations. With 180+ security tests aligned with OWASP and CSA CCM, we identify misconfigurations, enforce best practices, and ensure your cloud environment is resilient against evolving threats.
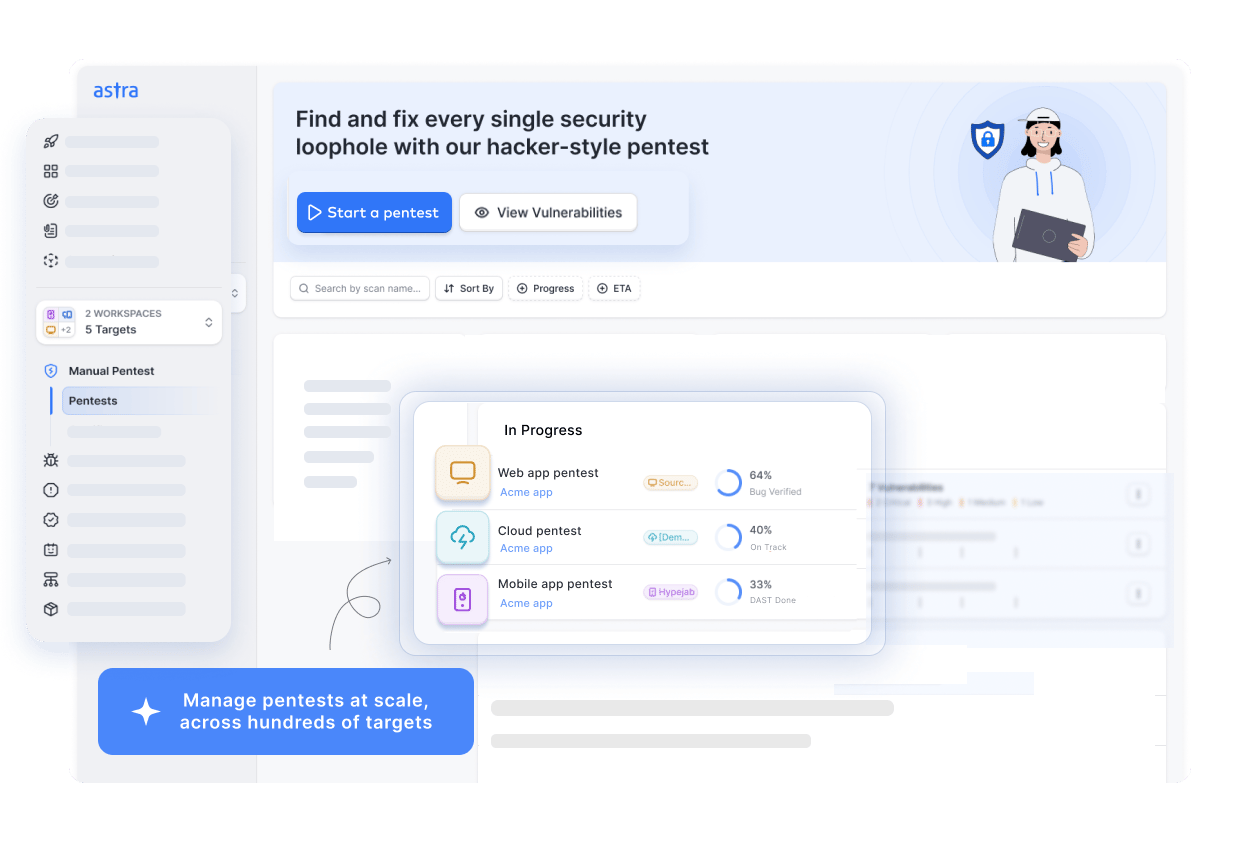
Our AI-powered testing integrates with Slack, JIRA, GitHub, and more, enabling real-time collaboration with all your assets. A CXO-friendly dashboard, compliance-specific scans, and expert-led manual testing ensure actionable insights. With free rescans and public certifications, we help teams stay audit-ready while scaling securely in the cloud.
Final Thoughts
Security in Azure fails when treated as a checklist rather than a continuous, evolving discipline. Too often, teams assume built-in controls are enough, only to find gaps when it’s too late. Proper cloud security isn’t about piling on tools; it’s about engineering security into every layer, ensuring threats are contained before they become incidents.
This means taking ownership where it matters: enforcing least privilege before attackers exploit it, making monitoring a living process rather than a compliance task, and pressure-testing defenses with real-world attack simulations. Azure cloud security gives you the building blocks, but resilience comes from strategy.
FAQ
What are the layers of security in Azure?
Azure security has multiple layers: Physical, Identity & Access Management, Network, Compute, Data, and Application. Each layer includes protections like firewalls, encryption, identity controls, and monitoring to safeguard workloads from threats across cloud, hybrid, and on-prem environments.
Is Azure Cloud safe?
Azure cloud is generally safe, with strong security measures like encryption, threat detection, and compliance certifications. However, risks remain due to misconfigurations, shared responsibility, and evolving threats. Proper Azure cloud security practices and continuous monitoring are essential for protection.
Is Azure cloud free?
Azure offers a free tier with 55+ services, including 750 hours of virtual machines for 12 months and some permanently free services. However, usage beyond limits incurs charges. A free $200 credit is available for 30 days.