At the heart of nearly every digital transformation strategy is a core focus on flexibility, scalability, and, most importantly, security. Amazon Web Services (AWS), a leader in the cloud services sector, empowers organizations to execute complex business processes while ensuring priority is given to robust AWS security practices. When you choose to move your data and applications to the cloud, security certainly takes a front-and-center role. This is where the AWS security checklist comes into play.
The AWS Security Controls Checklist serves as a critical tool to ensure the fortification of your AWS environment against potential threats and vulnerabilities. In this article, we’ll delve into the world of AWS security controls, exploring the key elements of the checklist and discussing best practices to enhance the security posture of your AWS infrastructure. We will talk about all the essential things related to AWS Security Controls – what the AWS security checklist is and how this checklist can change the way of managing cloud security.
Why is Astra Vulnerability Scanner the Best Scanner?
- Runs 8000+ tests with weekly updated scanner rules
- Scans behind the login page
- Scan results are vetted by security experts to ensure zero false positives
- Integrates with your CI/CD tools to help you establish DevSecOps
- A dynamic vulnerability management dashboard to manage, monitor, assign, and update vulnerabilities from one place.
- Helps you stay compliant with SOC2, ISO27001, PCI-DSS, HIPAA, etc.
- Integrates with Slack and Jira for better workflow management
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

What is the AWS Security Checklist?
The AWS Security Checklist is a comprehensive set of guidelines, recommendations, and best practices provided by AWS to help organizations ensure the security and compliance of their cloud infrastructure and resources. It serves as a valuable reference for businesses and individuals looking to establish a robust security posture within their AWS environment. The checklist covers various domains of security and offers actionable steps to enhance protection against potential threats and vulnerabilities.
Importance of AWS Security Checklist
The AWS Security Checklist holds significant importance as a comprehensive guide for ensuring the security, compliance, and resilience of your infrastructure and applications hosted on AWS. Here are some of the reasons why the AWS Security Checklist is so important:
1. Structured Guidance
The AWS Security Checklist provides a structured and organized approach to securing your AWS resources. It serves as a step-by-step guide, helping you systematically implement security controls, rather than relying on ad-hoc measures.
2. Comprehensive Security
The checklist covers a wide range of security aspects, including identity and access management, network security, data protection, logging and monitoring, disaster recovery, and compliance. The comprehensive coverage ensures that all critical security areas are addressed, reducing the risk of overlooking vulnerabilities.
3. Industry Best Practices
The checklist is based on AWS’s own security best practices and industry standards. By following these guidelines, you align your security posture with proven methods and strategies endorsed by both AWS and the broader cloud computing community.
4. Risk Mitigation:
Security breaches and data leaks can lead to financial losses, legal issues, and reputational damage. The checklist helps you identify and mitigate potential risks by implementing recommended security measures, reducing the likelihood of security incidents.
AWS Security Checklist
Mentioned below is the AWS security audit checklist that provides you with a detailed guide to keeping your systems, data, and set-up on AWS safe. It’s very important to regularly go through these points to make sure you’re giving the best protection possible to your cloud resources.
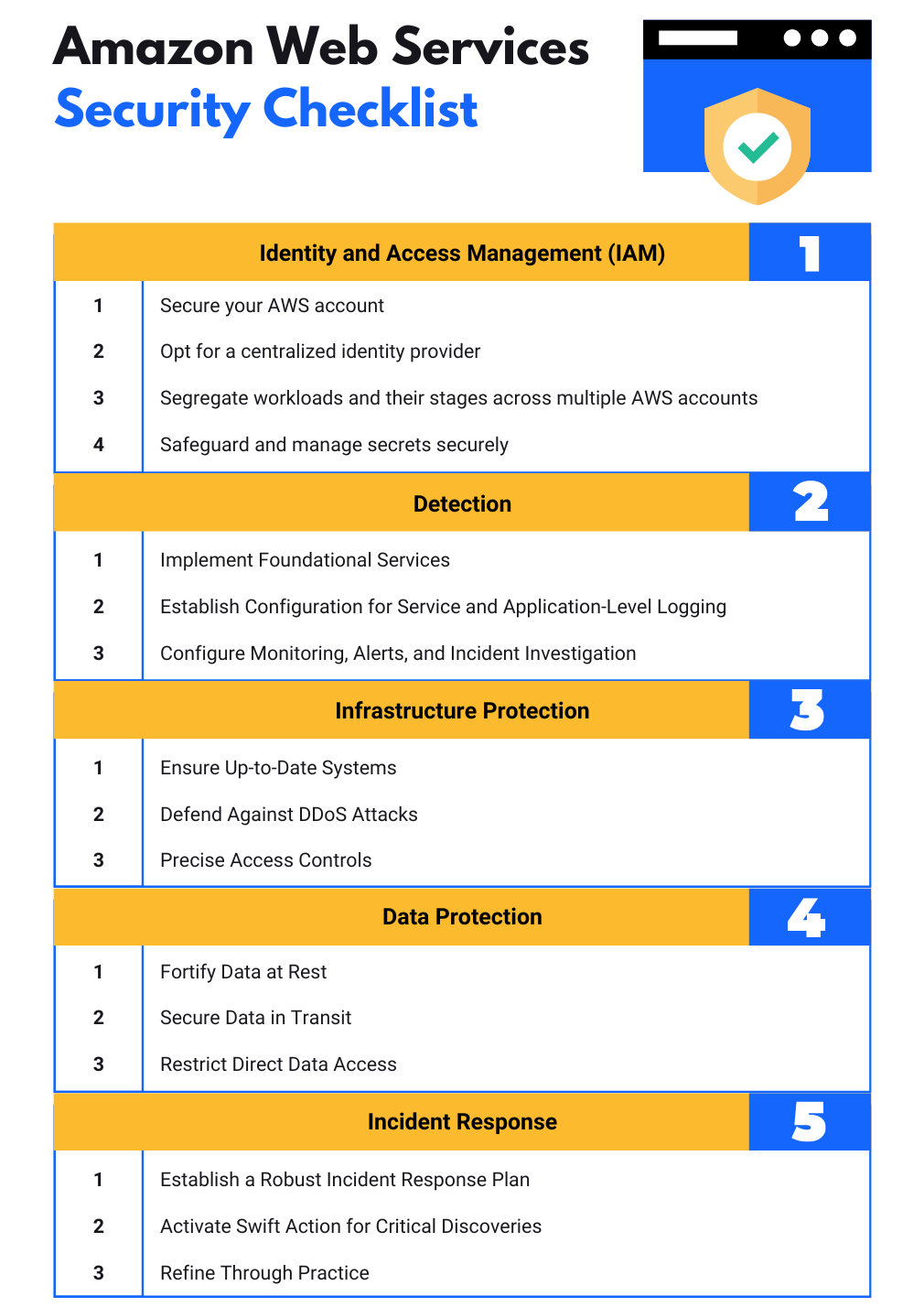
1. Identity and Access Management (IAM)
The steps to implement IAM include the following:
- Secure your AWS account: Implement AWS Organizations for streamlined account management, exercise caution with the root user, and utilize multi-factor authentication (MFA), while also configuring account contacts.
- Opt for a centralized identity provider: Centralize identities using either AWS Single Sign-On or a third-party provider to avoid routinely creating IAM users or using long-term access keys—this approach makes it easier to manage multiple AWS accounts and federated applications.
- Segregate workloads and their stages across multiple AWS accounts: Enhance security and resource management by employing separate AWS accounts for distinct workloads, such as production and non-production environments. Leverage Service Control Policies to establish strict controls, and simplify the creation and governance of a multi-account AWS ecosystem with AWS Control Tower.
- Safeguard and manage secrets securely: In scenarios where temporary credentials are not applicable, like AWS Security Token Service tokens, ensure secure storage of sensitive information, such as database passwords. AWS Secrets Manager offers encryption, rotation, and access controls to maintain the confidentiality of vital secrets.
2. Detection
The steps for detection include the following:
- Implement Foundational Services: Activate essential services including AWS CloudTrail, Amazon GuardDuty, and AWS Security Hub. For each of your AWS accounts, set up CloudTrail to log API activities, leverage GuardDuty for continuous monitoring, and deploy AWS Security Hub for an encompassing overview of your security stance.
- Establish Configuration for Service and Application-Level Logging: Beyond application-specific logs, enable logging at the service level. For example, activate Amazon VPC Flow Logs and log data for Amazon S3, CloudTrail, and Elastic Load Balancer access. Channel logs to a centralized account, safeguarding them against unauthorized changes or deletions.
- Configure Monitoring, Alerts, and Incident Investigation: Employ AWS Config to maintain a historical record of resource changes and utilize Config Managed Rules to promptly detect and rectify any undesirable alterations. Across all sources of logs and events, spanning AWS CloudTrail, Amazon GuardDuty, and your application logs, set up alerts for critical events and engage in a thorough investigation.
3. Infrastructure Protection
The steps for infrastructure protection include the following:
- Ensure Up-to-Date Systems: Maintain the security of your operating system, applications, and code through regular updates. Automate this process with AWS Systems Manager Patch Manager, which handles patches for your OS, applications, and code dependencies, ensuring comprehensive protection.
- Defend Against DDoS Attacks: Shield internet-facing resources from distributed denial-of-service (DDoS) threats. Employ a multi-layered approach using Amazon CloudFront, AWS Web Application Firewall (WAF), and AWS Shield. These services provide advanced safeguards at both the application (layer 7) and network (layer 3/layer 4) levels against potential DDoS attacks.
- Precise Access Controls: Exercise fine-grained control over resource access by utilizing VPC Security Groups and subnet segmentation. Harness security groups to manage incoming and outgoing traffic effectively. Enforce rules seamlessly for both security groups and WAFs via AWS Firewall Manager. Opt for subnet-based segmentation to establish distinct routing layers, ensuring specific resources like databases remain isolated from direct internet routes.
4. Data Protection
The steps for data protection include the following:
- Fortify Data at Rest: Safeguard your stored data by leveraging the AWS Key Management Service (KMS). Employ KMS to enhance the security of data at rest across various AWS services and your applications. Set up default encryption for Amazon EBS volumes as well as Amazon S3 buckets to ensure comprehensive data protection.
- Secure Data in Transit: Bolster your network’s security by enabling encryption for all network traffic. Utilize Transport Layer Security (TLS) for web-based network infrastructures under your control. AWS Certificate Manager comes into play here, facilitating the streamlined management and provisioning of certificates to establish encrypted connections.
- Restrict Direct Data Access: Adopt measures that maintain a separation between users and sensitive data or systems. Rather than direct database access, offer business users an Amazon QuickSight dashboard. When performing actions, employ a hands-off approach utilizing AWS Systems Manager automation documents and Run Command. This ensures a safer and more controlled environment for data handling.
5. Incident Response
The steps for incident response include the following:
- Establish a Robust Incident Response Plan: Lay the foundation of your incident response (IR) strategy by constructing runbooks designed to address unexpected occurrences within your workload. For comprehensive insights, refer to the AWS Security Incident Response Guide to ensure a well-informed approach.
- Activate Swift Action for Critical Discoveries: Begin by focusing on GuardDuty findings. Initiate the activation of GuardDuty and guarantee that a designated individual capable of taking necessary actions receives timely notifications. To seamlessly integrate GuardDuty findings into operational procedures, automate the creation of trouble tickets.
- Refine Through Practice: Enhance your incident response competency by engaging in regular practice scenarios. Conduct simulated exercises known as game days, incorporating the insights gained from these exercises into your incident management protocols. This continuous improvement approach ensures that your incident response strategies remain finely tuned over time.
What are AWS Security Controls?
AWS Security Controls are a comprehensive set of security capabilities provided by Amazon Web Services (AWS) to safeguard your data and applications hosted in the AWS cloud. By utilizing these controls, organizations can adhere to best security practices that protect customer data, systems, and assets.
For instance, In December 2021, a hacker collective known as “Uawrongteam” successfully breached FlexBooker, an internet-based reservation system. They managed to acquire information about approximately three million users. Subsequently, this pilfered data was exhibited for purchase across multiple cybercriminal forums.
The compromised data included details such as driver’s licenses and other personally identifiable particulars, along with password information. The breach occurred due to the exploitation of FlexBooker’s Amazon Web Services setup.
In light of these figures, AWS security controls become even more essential. They can help prevent unauthorized access, identify vulnerabilities, enhance encryption, and maintain overall cybersecurity hygiene.
Three types of security controls, namely – Preventive, Detective, and Responsive controls form the triad of a well-rounded cybersecurity framework. In the context of AWS security controls, they are implemented as follows.
Preventive Controls
These controls proactively protect your AWS resources from potential threats. Some AWS services related to these controls are:
- AWS Identity and Access Management (IAM): Manages access to AWS services and resources, preventing unauthorized access.
- Security Groups and Network Access Control Lists (NACLs): Security Groups and NACLs help regulate traffic flow in and out of subnets, further bolstering the protection of the virtual servers running within the AWS environment.
- Amazon Macie: Uses machine learning to recognize sensitive data like personally identifiable information (PII), proactively preventing data leaks.
- AWS Key Management Service (KMS): Manages cryptographic keys and policies, preventing unauthorized decrypting of encrypted resources.
Detective Controls
These controls identify and alert about security violations. AWS services related to these controls are:
- Amazon GuardDuty: A threat detection service that continuously monitors for malicious activity and unauthorized behavior to protect your AWS accounts and workloads.
- AWS CloudTrail: Records AWS API calls, delivering log files to detect operational and risk auditing issues.
- Amazon CloudWatch: Monitors AWS resources in real-time to collect data on operational health, allowing rapid detection of anomalies.
Responsive Controls
These controls react to a security incident to minimize the damage and restore the system. AWS services related to these controls are:
- AWS CloudWatch Events: Responds to state changes on your AWS resources with remedial, programmed actions triggered by specific incidents.
- AWS Lambda: Enables automatic execution of your code in response to events, thus you can set up Lambda functions as automated response solutions.
The AWS Security Checklist and AWS Security Controls are closely related elements that contribute to the overall security and compliance of an organization’s AWS environment. While they serve distinct purposes, they are interconnected and work together to ensure a robust security posture.
The AWS Security Checklist is a comprehensive set of guidelines, best practices, and recommendations provided by AWS to help users and organizations establish and maintain a secure cloud infrastructure. On the other hand, AWS Security Controls refer to the specific measures, configurations, and tools that organizations implement within their AWS environment to mitigate risks, protect data, and prevent security breaches.
AWS Security Checklist provides the overarching guidance and principles, while AWS Security Controls translate those guidelines into practical actions and configurations that enhance the security of an AWS environment.
AWS Security Best Practices
Some of the AWS security best practices to secure the AWS environment effectively are mentioned below.
1. Implement the Principle of Least Privilege (PoLP)
In line with the cybersecurity principle of least privilege (PoLP), AWS encourages limiting access rights for users, applications, and services to the bare minimum they need to perform their functions. Overprivileged accounts pose a significant security risk if they get compromised. By limiting permissions to what’s necessary, you insulate your systems and data from potential malicious activities and enhance security.
2. Enable Detailed Logging
With services like AWS CloudTrail, you can record all actions made in your AWS account. AWS Config provides a detailed inventory of your AWS resources and lets you audit your resource history. Making use of these tools enables you to review modifications to your environment and troubleshoot potential security issues.
3. Encrypt Data At-Rest and In-Transit
Encrypting data in transit and at rest should also be a top priority. AWS provides several tools to facilitate encryption, like AWS Key Management Service (KMS) for managing encryption keys and AWS Certificate Manager which handles SSL/TLS for your website or AWS-based applications.
4. Centralize and Govern Your AWS Environment
AWS Organizations is a service that enables you to manage multiple AWS accounts centrally, permitting consolidation of billing across multiple accounts, automated AWS account creation and management, and control over various accounts for meeting compliance requirements. When combined with AWS Control Tower, organizations can set up a landing zone to manage a secure, multi-account AWS environment quickly.
5. Monitor and Audit Proactively
Services like AWS CloudWatch and Amazon GuardDuty allow for real-time monitoring of your AWS resources and applications. CloudWatch collects and tracks customizable metrics, and provides system-wide visibility, and actionable insights. GuardDuty recognizes anomalous behavior and potential threats, such as an unexpected spike in data traffic or unauthorized deployment of instances.
6. Conduct Regular Vulnerability Assessments
Conducting regular vulnerability assessments is a crucial practice for identifying potential weak points in your AWS infrastructure. Astra’s Pentest Suite provides a comprehensive solution that encompasses both automated vulnerability scanning and meticulous manual pen testing. This combination renders it an ideal asset for businesses spanning various industries. The stand-alone vulnerability assessment tool stands out with its exceptional features, making it a compelling choice.
Astra’s Pentest Suite goes beyond by providing step-by-step guidance for effective remediation. The comprehensive vulnerability assessment report includes risk scores for each vulnerability, aiding in the prioritization of critical issues. The manual pentest conducted by Astra’s skilled security professionals complements the vulnerability assessment by guaranteeing zero false positives, uncovering business logic errors, and identifying concealed vulnerabilities. Furthermore, the seamless collaboration with these experts facilitates efficient issue resolution and remediation.
7. Design for High Availability and Resilience
Designing your AWS applications for high availability (HA) and resilience is key to ensuring minimal to no disruption of services in the event of an outage or failure. You can achieve this by using AWS services and features designed for resilience, e.g., replicating across multiple Availability Zones (AZs) and AWS regions.
8. Defense in Depth
AWS advocates implementing a multi-layer security architecture, applying security at all levels – edge network, VPC, subnet, load balancer, every instance, and so forth. Utilizing built-in security features like Security Groups and using services like AWS Shield for defending against DDoS attacks, and AWS WAF to protect your web applications contribute towards this strategy.
9. Leverage Identity and Access Management (IAM)
Using IAM, you formulate and implement a strong password policy, limiting who can perform actions on specific resources. For example, you can stipulate that only authorized users can launch or terminate certain Amazon EC2 instances. Implementing multi-factor authentication (MFA) for all user accounts, especially for privileged users and root users, adds another layer of security. Rotating security credentials like access key IDs and secret access keys routinely, except root user keys, is instrumental in protecting your resources.
Wrapping Up
The AWS Security Controls Checklist emerges as a guiding light in this endeavor, offering a comprehensive roadmap to bolster security and compliance. These tools provide the compass and the shield, ensuring that your cloud journey is paved with confidence, protection, and innovation. By meticulously following the AWS Security Checklist and implementing the Security Controls, organizations can erect robust fortifications around their digital assets.
In a similar context, Astra emerges as a powerful ally, equipped to seamlessly integrate into your security strategy. Astra’s Pentest Suite, with its blend of automated vulnerability scanning and expert manual pen testing, delivers a comprehensive solution. Safeguarding your data, applications, and digital infrastructure in the cloud is no longer a challenge, but an achievable reality with AWS and Astra by your side.
FAQ
What do you mean by security controls in AWS?
Security controls in the AWS security checklist are technical or managerial safety measures used in an AWS set-up to protect the security, secrecy, and availability of data and systems. These controls stop, tell about, and reduce security risks, including possible threats and weak spots.
Which security services in AWS let you use a collection of safety measures?
AWS Identity and Access Management (IAM) is a tool you can use to tightly manage access to AWS resources and services. It caters to your AWS users, groups, and roles, offering a secure environment. With IAM, you have the power to establish individual access controls with permissions, letting you dictate who can access specific services and resources and set out the conditions of that access.
What are the various types of security services?
Security services cover a wide range and include many types in different areas. Here are some common types of security services:
1. Firewalls: Firewalls help keep your network safe by managing data coming in and going out of your network.
2. Intrusion Detection Systems (IDS): IDS systems check the network or systems for any harmful activities or breaking of rules.
3. Virtual Private Networks (VPN): VPN gives a safe connection over a public network, making sure the data sent is coded and safe.
4. Data Loss Prevention (DLP): DLP tools can stop people from sending private information outside the network.
















