Red teaming and penetration testing are like two sides of the same coin, both aiming to expose vulnerabilities in a security system. While penetration testing focuses on finding specific weaknesses using technical tools, red teaming takes a more holistic approach, simulating real-world attacks to reveal systemic flaws.
But what is the difference between red team and penetration testing? Which is the best choice for you? Let’s explore both further to help you make an informed decision.
Red Teaming vs Penetration Testing
| Feature | Red Teaming | Penetration Testing |
|---|---|---|
| Scope | Focused on simulating real-world attacks and assessing overall security posture | Focused on identifying specific vulnerabilities in systems and applications |
| Methodology | Adopts adversarial tactics and techniques to exploit weaknesses | Employs technical tools and methods to systematically identify vulnerabilities |
| Goal | To expose weaknesses in an organization's security controls and identify potential attack vectors | To identify specific vulnerabilities that could be exploited by attackers |
| Approach | Often involves deception, social engineering, and other advanced techniques | Typically relies on automated tools and scripts |
| Team Composition | Includes security experts with diverse backgrounds, such as ethical hackers, social engineers, and intelligence analysts | Often involves security professionals with technical expertise in network and application security |
| Timeline | Can be conducted over an extended period to mimic real-world attack scenarios | Typically conducted within a defined timeframe or window |
| Reporting | Provides a comprehensive assessment of the organization's overall security posture, including recommendations for improvement | Generates a detailed report of identified vulnerabilities and potential risks |
What is Red Teaming?
Red teaming is the process of assessing and exploiting a target system like a hacker to understand how well your organization can defend itself against cyberattacks by simulating the actions of real hackers.
Originally used as a military concept, the modern-day practice involves various techniques, such as social engineering, network exploitation, physical intrusion, and web application attacks.
What is Penetration Testing?
Penetration testing is a type of cybersecurity assessment that simulates real-world attacks to identify vulnerabilities in a system or network. It involves ethical hackers attempting to exploit weaknesses in an organization’s security controls such as XSS, SQL injections and more to gain unauthorized access.
In fact, security regulations like PCI-DSS, HIPAA, and ISO 27001 mandate or require risk assessments to be carried out yearly to assess the fulfillment of cybersecurity best measures and help improve security postures.
No other pentest product combines automated scanning + expert guidance like we do.
Discuss your security
needs & get started today!

Red Teaming vs Pentesting: A Detailed Comparison
Scope:
Between red team vs penetration test, the former typically has a broader scope, encompassing the entire organization’s security infrastructure. It involves assessing the security of various systems, networks, and applications to identify potential weaknesses that attackers could exploit.
Penetration testing, on the other hand, is often more focused, targeting specific systems or applications. For example, a penetration test might focus on a web application to identify vulnerabilities such as SQL injection or cross-site scripting.
Methodology:
Red teaming employs adversarial tactics and techniques to simulate real-world attacks, often involving deception, social engineering, and other advanced methods. This approach allows red teams to identify vulnerabilities that might not be detected through traditional penetration testing methods.
Meanwhile, pentesting relies on technical tools and scripts to systematically identify vulnerabilities. This approach is often more efficient and can be automated to a certain extent.
Approach:
Red teaming takes a more holistic approach to uncovering weaknesses in an organization’s security controls. This involves assessing the organization’s security posture from an attacker’s perspective, identifying potential attack vectors, and simulating real-world attacks.
Nonetheless, between red teaming vs penetration testing, the latter is more targeted, focusing on specific vulnerabilities within systems and applications. This approach is often more efficient and can be used to identify specific weaknesses that attackers could exploit.
Teams:
Red teaming typically involves a diverse team of security experts, including ethical hackers, social engineers, and intelligence analysts. This diverse team brings a range of skills and perspectives to the assessment, allowing them to identify vulnerabilities that a more traditional penetration testing team might miss.
Penetration testing often involves security professionals with technical expertise in network and application security. These professionals are well-versed in using tools and techniques to identify vulnerabilities.
Time & Cost:
Due to its broader scope and complex methodologies, red teaming can be more time-consuming and expensive. It often involves a longer engagement period to allow red teams to simulate real-world attacks and assess an organization’s security posture.
Penetration testing is generally more cost-effective but may require additional resources for complex systems or applications. The specific time and cost associated with red teaming and penetration testing will vary depending on the size and complexity of the organization’s security infrastructure.

What Makes Astra the Best VAPT Solution?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- The Astra Vulnerability Scanner runs 10,000+ tests to uncover every single vulnerability
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Red Teaming vs Penetration Test: What Should You Conduct?
We have understood the differences between Red teaming & penetration testing. Now, what should you choose?
While red teaming is often favored by larger, more complex organizations, smaller and medium-sized businesses can also benefit from it. Here’s how to decide:

- Complexity of Systems and Processes: If your organization has intricate systems and processes, red teaming can provide a more comprehensive assessment of your security posture.
- Potential Impact: If a security breach could significantly impact your business, such as financial loss, reputational damage, or disruption of operations, red teaming can help identify critical vulnerabilities.
- Well-Defined Environment: A well-structured and documented environment can facilitate red team operations. However, organizations with less-defined environments can benefit from red teaming to identify vulnerabilities and strengthen their security.
How can Astra Help?
Astra Security’s comprehensive penetration testing services offer a unique and valuable solution. They use an industry-leading pentest suite that combines automation and human expertise.
It provides a fully managed vulnerability dashboard, an automated scanner capable of running 10,000+ tests, detailed steps to reproduce and fix vulnerabilities, expert assistance, and a monetary loss value associated with each identified risk.
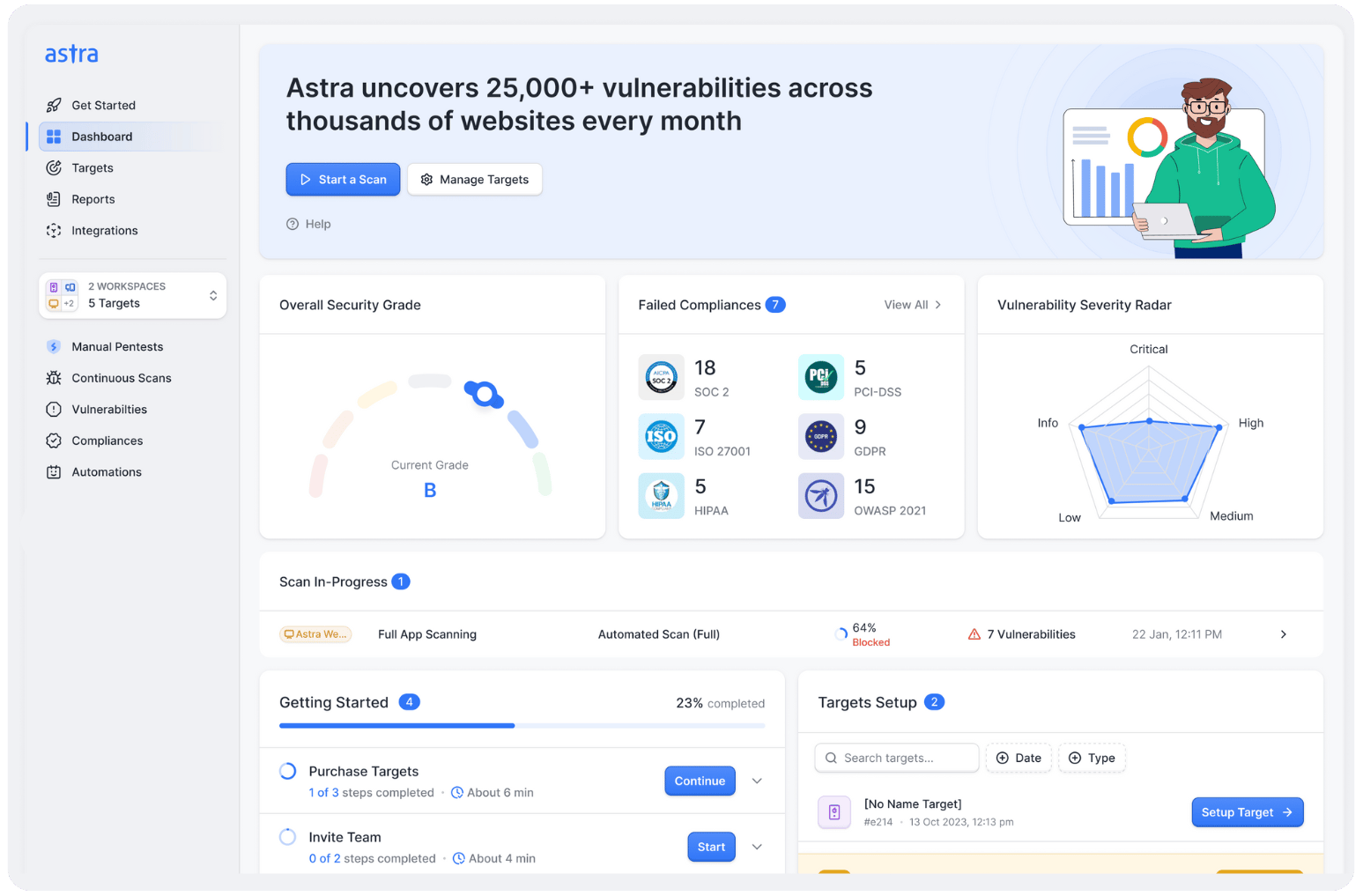
Additionally, our intelligently calculated risk scores and grading system help organizations prioritize vulnerabilities and assess the overall security of their assets.
Final Thoughts
Hidden biases and groupthink can hinder even the strongest security defenses. Red teaming provides a comprehensive assessment of an organization’s security posture, offering valuable insights and alternative approaches to building effective frameworks.
While red teaming vs penetration testing have distinct methodologies, organizations can choose the most appropriate method based on their complexity and specific needs, be it security or compliance, or something else.
Let experts find security gaps in your cloud infrastructure
Pentesting results without 100 emails,
250 google searches, or painstaking PDFs.

FAQs
1. Is red teaming the same as penetration testing?
Red teaming and penetration testing are similar but distinct. Red teaming simulates real-world attacks, while penetration testing focuses on technical vulnerabilities. Red teaming involves a broader scope, including social engineering and physical security, to assess overall security posture.
2. What is red teaming and penetration testing?
Penetration testing refers to the process of evaluating a system’s security posture by finding and exploiting vulnerabilities present in the said system. In red teaming, a group of security experts tries to break into a system by using hacker-style methodologies.
Who is a red team penetration tester?
A red team penetration tester is a cybersecurity professional who acts as a hacker to identify and resolve vulnerabilities in a network. They launch their attacks without prior notice to their team to identify any loopholes in their network. They are ethical hackers who are on the offense, staging strategic attacks.