Docker Hub is one of the most popular repositories of docker images. Millions of users download docker images from Docker Hub regularly. And like anything on the internet that has a large user base, Docker Hub also draws a lot of hacker attention.
In 2019, data of 190,000 users was compromised in a Docker Hub hack and the hacker had access to the database only for a few seconds. According to a statement by the company, the exposed data belonged to just 5% of their user base. You can imagine why a hacker should want to intrude into this channel and why it is important to learn about Docker Hub vulnerability scanning.
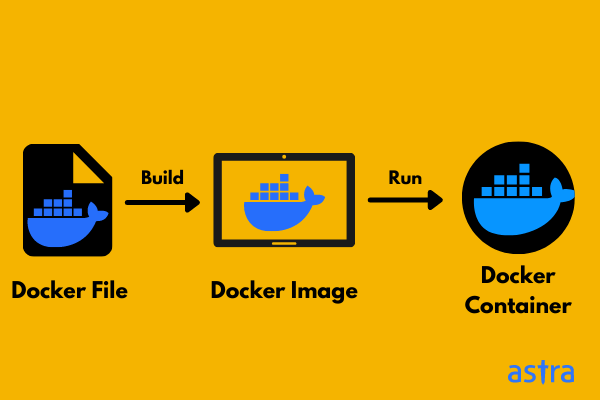
Before we get on with our discussion of Docker Hub vulnerability scanning, let us quickly understand what docker images are and why are they important.
What is a docker image?
Every explanation in this section will raise some more questions and we will try to answer as many of them as possible. Let us start at containers and learn what they are and why they are important.
A container is a unit of software used to pack code and dependencies. Containers can be transferred easily from one computing environment to another computing environment, thus helping developers to package, test, and deploy their code, while bypassing the hassle of transitioning between environments.
A container image is a static file with executable code that is used to create a container quickly and reliably in a loosely isolated environment.
Now, Docker is one of the containerization platforms. A docker image is like a blueprint that helps you create multiple containers with the same configuration. We call these containers, docker containers.
How is a docker image used?
Let us see if an example can help us understand this. If a company needs to develop an application on Java, the developer would setup a tomcat server and create a development environment around it. Now, once the application is developed, the tester would require to build a tomcat environment from scratch, and after that, the same procedure would have to be repeated while creating the production server.
There are two major issues with this.
- The company loses hours in designing the environment for the application to run.
- There might be inconsistencies between the Tomcat servers created by the developers, the tester, and the product admin, resulting in a severe misconfiguration.
A docker image offers a solution. If the developer creates a docker container that contains information about the tomcat environment, he can use the tomcat docker image as a blueprint. The tester and the system admin can use the same docker image to create the testing and the production servers. Thus the company does not lose time and the whole process is leaner and more reliable.
Docker Hub is a platform that allows you to find and share docker images with your team and it is widely used across industries.
Now that we have familiarized ourselves with docker images and Docker Hub, let us learn about Docker Hub Security and vulnerability scanning, as promised.
1. Why should you be worried about docker image security?
Docker images are a reliable and secure medium of sharing information. But they can pose a security threat. Security issues related to Docker Hub and Docker images have been ignored for quite some time, however, a study in 2020 involving 2,227,244 docker images and corresponding meta information from Docker Hub has unveiled a lot of serious issues.
- Docker container run commands often have sensitive parameters that can expose users to denial of service attacks, or leakage of host files.
- They found 42 malicious images capable of allowing remote execution of code and malicious cryptomining.
- It was also found that patches for docker image vulnerabilities are often delayed or ignored.
Another survey conducted in 2020 found that 51% of the 4 million publicly available docker images were critically vulnerable and more than six thousand of them had malware.
One of the primary concerns about docker image vulnerabilities is that most of the users pay very little attention to its security aspect. According to a survey 97% users of docker images ignore run-command parameters and are concerned only about whether the command runs successfully.
2. The damage that can be caused by exploiting a docker hub vulnerability
A hacker can obtain the display of a host by applying the --privileged parameter provided by Docker. This is an incredibly powerful parameter and an operator can gain access to all the devices running on a host by using this.
With --privileged a hacker can hijack the display of a user’s desktop with one line of code:
cp/dev/fb0 user_desktop.txt
The hacker can steal user files, view the display of a user, and do practically anything without restriction.
The --pid parameter enables a container to access the host’s PID Namespace. An intruder can use this to see all the programs running on a user’s host and manipulate them to launch an attack.
There are a bunch of malicious images in Docker Hub that do something completely different from what they are supposed to do.
3. Some Docker Vulnerabilities That Demand Your Attention
Containers in general are isolated units of software – they do not give hackers a lot of opportunity to escalate an attack. However, issues regarding containment break out do come up quite frequently and things can go south really fast as we have already explained. A docker hub vulnerability scanning every now and then is highly recommended to save yourself from vulnerabilities such as the following.
3.1 runC Root Access Remote Execution
runC is an open-source project that powers runtime capabilities in almost all containers. A severe containment breakout vulnerability was found in runC with a risk of remote code execution. It was attributed a CVSS score of 8.6. A patch for this vulnerability was launched by Docker, but as we have already mentioned, docker vulnerability patches are ignored more often than not.
3.2 Docker Skeleton Run Time for Apache OpenWhisk
This docker specific vulnerability with a CVSS of 9.8 allows hackers to change user functions inside a container if the user’s code is exploitable.
3.3 util.c in runV
util.c in runV 1.0.0 for Docker allowed attackers to leverage an initial numeric value on an /etc/passwd line which they could use in the -u argument to issue a “docker exec” command to gain root access.
This vulnerability allows hackers to get privileged access and hence was assigned a CVSS of 7.8.
There have been other docker hub vulnerabilities with dire consequences and there will be more. The DevOps driven software development environment is highly dependent on docker images which makes regular Docker Hub vulnerability scanning all the more important.
4. Docker Hub Vulnerability Scanning
Docker Hub provides vulnerability scanning for docker images to its pro or business level subscribers. If you enable the Docker Hub vulnerability scanning feature, it will scan the container images that you push into it for security flaws. Any one with push access can start a vulnerability scan by pushing a container image into a specific repository when Docker Hub vulnerability scan is enabled.
Read also: What, Why, and How of Vulnerability Scanning
4.1 How do you enable vulnerability scanning on docker hub?
You can enable docker hub vulnerability scanning by following the steps below.
- Start by logging into your Docker Hub account.
- Then go to the main menu and click on Repositories to select a repository.
- Click on the Settings tab and from there click on Enable image scan.
The scanning feature is disabled on all repositories by default, you have to enable it manually for each repository.
5. Limitations of Docker Hub Vulnerability Scanning
The inbuilt docker image scanner is definitely your first line of defense against docker image vulnerabilities and security flaws. But the scanning feature has some limitations that may expose you to severe exploits.
5.1 Environment level threats
The docker hub vulnerability scanner cannot detect issues related to the container environment. For instance, it cannot tell if a container is running as root, or if there is an insecure Kubernetes configuration.
5.2 Vulnerabilities acquired by shared resources
Containers often share resources such as networking, or storage volume. Misconfigurations in these cases cannot be detected by the Docker hub image scanner.
5.3 Vulnerabilities in non-public packages
Let us say, you take an open source software package and then import code into it and redesign it in someway thus incurring a vulnerability, the Docker image scanner won’t detect it, as the custom package would not be enlisted in the public database.
There are several issues like these that necessitate the involvement of third party vulnerability scanning tools like Astra’s Pentest Suite, Clair, Anchore, Falco, etc.
How Should You Choose a Docker Hub Vulnerability Scanning Tool?
If you are looking for an efficient way of managing vulnerabilities and building a strong security posture, the idea should be to find a vulnerability scanner that is equally adept in detecting all sorts of vulnerabilities. You might not want to spend separately on a specific feature if you can get an all round vulnerability assessment tool.
These are some features you should be looking for
- Continuous scanning: Managing vulnerabilities become way simpler if you can integrate your vulnerability scanner with CI/CD platforms and automate continuous scanning whenever a code update takes place.
- Scan behind login: This feature too makes life easy for you since you do not have to authenticate the scanner every time a session runs out.
- Compliance reporting: The tool allows you to monitor your standing in terms of compliance regulations based on the vulnerabilities that are found during a test.
- Thorough remediation guidance: A tool that comes with human support and detailed POCs to reproduce and fix vulnerabilities can make life a lot easier for your developers.
Astra’s Pentest Suite for Your Vulnerability Scanning Needs
Scan behind logged in pages, CI/CD integration, Docker Hub vulnerability scanning, continuous scanning, video POCs for remediation with human support, you name a feature and Astra’s Pentest has it.
Astra Security has built comprehensive yet easy to use vulnerability assessment and penetration testing dashboard that allows you to access every cutting edge feature from one place. In fact, you do not even need to visit the dashboard to run continuous scans for product updates.
Researchers and engineers at Astra Security are not satisfied after building a pentest tool that trumps almost every competitor in the market. They want to take it further by paying minute attention to every minor need of a customer that can improve the user experience in any way. They are industry leaders in the most literal sense possible.
Conclusion
When it comes to securing your applications, no amount of caution is enough. Docker images are rarely thought of as a source of critical vulnerabilities. But now, you know better. You know how to enable docker hub vulnerability scanning, and why you should opt for third party help. If you have any more questions, feel free to drop them in the comments section.
What is vulnerability scanning?
Vulnerability scanning is the process of scanning computer systems for security flaws with the help of a vulnerability database and automated tools. Learn more
What is the cost of vulnerability scanning?
The cost of vulnerability scanning for web applications is between $99 & $399 per month.
Why is docker hub vulnerability scanning important?
Hackers can cause a lot of damage like data theft, denial of service, remote code execution by gaining access to docker containers through a vulnerability. That is why you want to conduct frequent vulnerability scans to avoid such situations.
Why should you choose Astra’s Pentest for vulnerability scanning?
With 8000+ tests, scan behind logged in pages, CI/CD integration for continuous scanning, and thorough remediation support, Astra’s Pentest is quite unbeatable in terms of features and support.