When it comes to cyberattacks, everyone believes it couldn’t happen to them until it does. This far-off concept became a real nightmare for LastPass, a password management software, in August 2022 and again in April 2024.
These attacks resulted in customer information, such as passwords to different platforms, being used to siphon over $4.4 million worth of cryptocurrency and sell the data on the dark web, compromising the privacy of a huge part of their customer base.
To stay ahead of cyber threats in a rapidly growing SaaS space, companies should employ cyber security auditors for regular testing to prevent considerable reputational, financial, and resource loss. A cyber security auditor or auditing company fulfills this role by identifying and resolving software vulnerabilities to prevent the risk of data breaches.
What is a Cybersecurity Audit?
A cybersecurity audit is a structured review of your systems, networks, and applications to identify vulnerabilities, misconfigurations, and compliance gaps. It provides an independent, end-to-end assessment of your security posture and documents how well your defenses align with industry standards.
Top 7 Cyber Security Auditors (2026)
- Astra
- Rapid7
- HackerOne
- Intruder
- Qualys
- IBM Security
- EY
Audit vs. Assessment vs. Penetration Test (Quick Comparison)
- Audit: Formal, compliance-driven review of policies, processes, and systems. Focuses on security controls and evidence.
- Assessment: Broader evaluation of overall security posture. Usually consultative, highlighting risks and improvements.
- Penetration Test: Attack simulation by ethical hackers to uncover exploitable weaknesses that automated tools may miss.
Who is a Cyber Security Auditor?
A cyber security auditor or auditing company conducts vulnerability assessments and penetration tests to find vulnerabilities in your network, systems, cloud, API, and applications that could lead to cyberattacks and data breaches.
A cybersecurity auditor helps:
- Complete Security Posture Evaluation by conducting custom audits covering the entire IT infrastructure, system configurations, access controls, and application security to find vulnerabilities.
- Penetration Testing and Threat Modeling Services use pentesting techniques to simulate real-world attack scenarios and identify weaknesses. They also utilize threat modeling to gauge potential threats and prioritize security controls based on the likelihood and impact of each threat.
- Detailed Reporting and Remediation Guidance is included in the report covering identified vulnerabilities, their severity levels, and remediation strategies.
How Audits Are Performed
- Planning & Scoping: In this phase, you define the systems, applications, and environments to be covered in the audit and scope out the different components of each system that need to be tested.
- Evaluation: Review the infrastructure, configurations, access controls, and development practices, including their current security standing and any identified weaknesses/open ports.
- Testing: Use a combination of automated scans, manual vetting of scan results, and expert-led penetration testing – all of which Astra Security can help you with.
- Reporting & Remediation: Finally, you can go through the findings, which should be given to you with severity ratings by the testing team, conduct compliance mapping to see what misses need to be fixed to achieve compliance, and take actionable steps to remediate the vulnerabilities.
SaaS-Specific Scope (What Gets Tested)
1. IT Infrastructure Assessment
Auditors assess the organization’s IT infrastructure, scrutinizing network architecture, system configurations, and access controls. This approach exposes potential firewall vulnerabilities, intrusion detection/prevention systems (IDS/IPS), and other network security mechanisms.
2. Security Protocol Review
Security protocols, encompassing authentication methods, authorization levels, and data encryption techniques, undergo rigorous scrutiny in a security audit. Auditors identify weaknesses attackers could exploit to gain unauthorized access or manipulate sensitive data.
3. Software Development Practices
The software development lifecycle (SDLC) is evaluated to identify potential security flaws that may have been introduced during development. Coding practices, adherence to secure coding standards, and vulnerability management procedures are assessed to ensure secure software development.
Need for Cyber Security Audits in SaaS Companies
1. Building Trust Among Clients
Trust is a key differentiator in the rapidly evolving SaaS industry that offers a competitive advantage. Customers trust your platform with their data and expect the best data safety practices.
You can strengthen this trust by regularly conducting cybersecurity audits that proactively identify and solve vulnerabilities. A solid security posture also increases investor confidence, creates brand credibility, and attracts security-conscious consumers to expand your clientele.
2. Continuous Testing for Emerging Threats
New vulnerabilities emerge daily, necessitating a security strategy based on continuous testing and consistent updating of the list of tests conducted.
Make it a top priority to find an auditor who combines automated vulnerability scanning, human penetration testing conducted by security experts, and regular updates to its tests. This ensures that you identify known vulnerabilities, zero-day exploits, and emerging threats before they can be exploited.
4. Being Compliance Ready
Security audits serve as a roadmap to achieving compliance with regulations such as HIPAA, GDPR, PCI DSS, and SOC 2, even though getting an audit does not automatically guarantee it.
Audits identify vulnerabilities that might prevent SaaS organizations from complying with regulations. By addressing these weaknesses, they can greatly increase their compliance rate.
5. Prevents Potential Losses
Data breaches continue to cause major financial and reputational damage: IBM’s Cost of a Data Breach Report 2024 found the global average breach cost reached a record $4.88 million per incident, underscoring why regular security audits are a strategic investment to reduce financial, operational, and trust-related risk.
How to Choose a Cybersecurity Auditor
1. Automated Scanning Combined With Pentesting
When we discuss combining manual and automated testing, we don’t necessarily recommend opting for the month-long manual tests. There is a better option.
You should look for companies with a solid automated vulnerability scanning tool and a team of security experts that can validate the results the scanner shows and also look for things it might have missed. By employing penetration testing conducted by security experts
2. Authenticated Scanning
A vulnerability scanner should be able to scan behind login pages and properly test every portion of the network, application, or system. However, most scanners must be authenticated manually whenever a session runs out and cannot scan behind login pages. Find a scanner that offers these features as well.
3. Comprehensive Dashboard
You need an interactive dashboard that lets you manage the vulnerabilities, assign them to team members, monitor and update their status, and even get help from security experts to resolve them. By prioritizing an auditing company that offers a dashboard that can be customized to your needs, you’re making vulnerability management a much simpler process.
4. Actionable Reports
A long and complicated vulnerability report that isn’t customized to the technical level its reader requires doesn’t serve its purpose of communicating details of the vulnerability effectively. A customizable report helps you decide the technical information you want to include to provide a bird’s eye view to a CTO or a detailed breakdown of each vulnerability to a security engineer.
The report’s structure should help you prioritize critical vulnerabilities and guide you in the right direction for remediation.
Top 3 Cybersecurity Auditors
| Feature | Astra Pentest | Qualys VMDR | Intruder |
|---|---|---|---|
| Platform | SaaS | Cloud-based | SaaS |
| Pentest Capabilities | Continuous scanning (9300+ tests), Manual pentesting | Continuous vulnerability scanning, Patching | Continuous vulnerability scanning, Manual pentesting (optional) |
| Accuracy | Zero false positives (with vetted scans) | Not specified | Reduced false positives |
| Compliance Scanning | OWASP, PCI-DSS, HIPAA, ISO27001, SOC2 | PCI-DSS, HIPAA, GDPR, SOC 2 | SOC2, PCI DSS, HIPAA, and ISO 27001 |
| Expert Remediation Assistance | Yes | Support included in some plans | Yes |
| Customizable Reports | Yes | Yes | Yes |
| Workflow Integration | Slack, JIRA, GitHub, GitLab, Jenkins etc. | Integrates with ticketing systems and security platforms | GitHub, JIRA, Azure DevOps, and more |
| Pricing | Starts at $1999/year | Starts at $2195/year | Starts at $1958/ year |
| Focus | Comprehensive pentesting with automation & manual testing | Vulnerability management, patching, and compliance | Vulnerability scanning, with optional manual pentesting add-on |
Top 7 Cybersecurity Auditors for SaaS (2026)
1. Astra Security [Get Started]
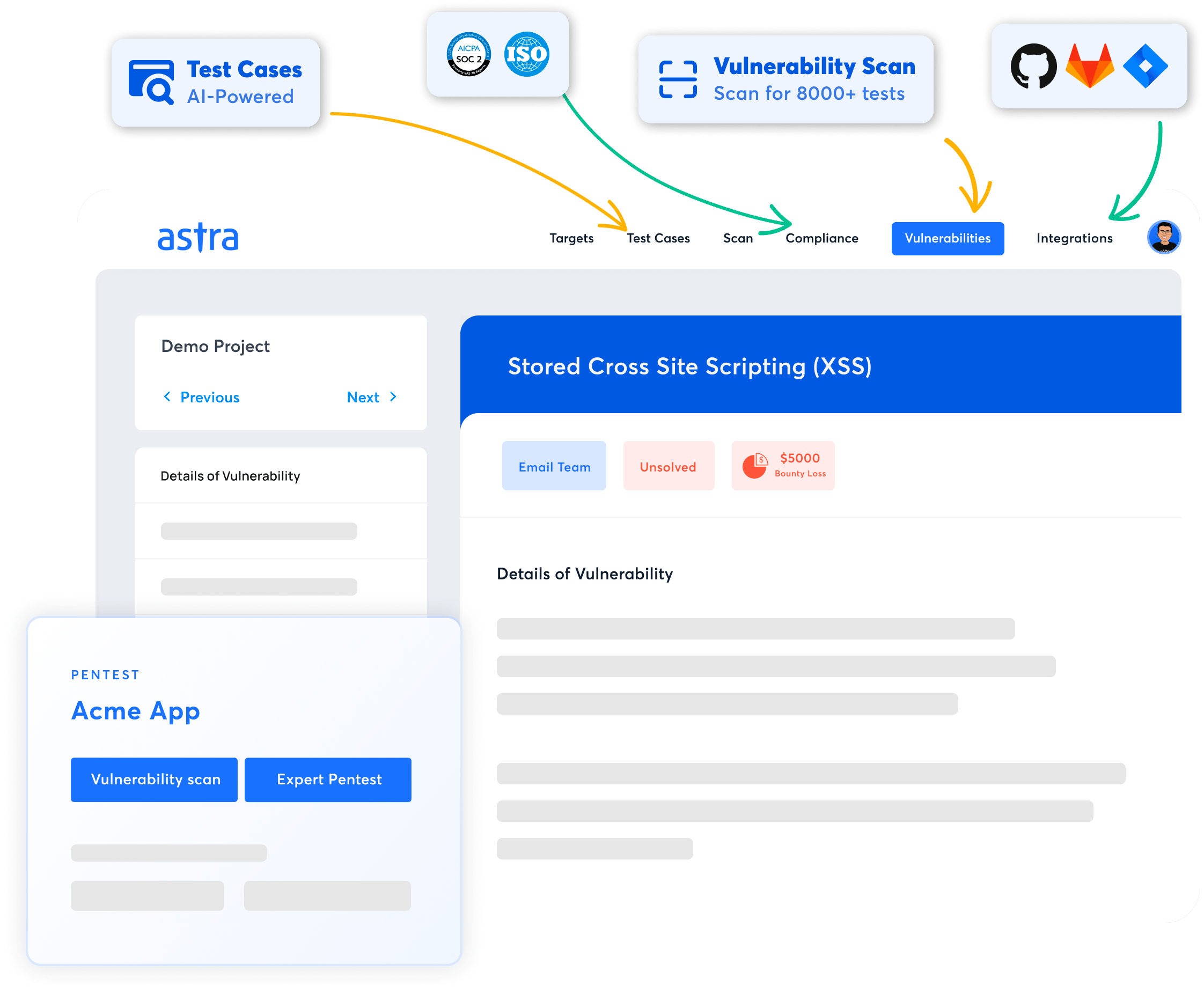
Key Features:
- Platform: SaaS
- Pentest Capabilities: Continuous automated scans with 9300+ tests and manual pentests
- Accuracy: Zero false positives (with vetted scans)
- Compliance Scanning: OWASP, PCI-DSS, HIPAA, ISO27001, and SOC2
- Expert Remediation Assistance: Yes
- Customizable Reports: Yes
- Publicly Verifiable Pentest Certification: Yes
- Workflow Integration: Slack, JIRA, GitHub, GitLab, Jenkins, and more
- Price: Starting at $1999/yr
Astra Security offers a comprehensive suite of security testing solutions to help businesses identify and resolve vulnerabilities in their networks, mobile applications, cloud infrastructure, APIs, and online applications. Our online vulnerability scanner continually scans systems for over 9,300 possible vulnerabilities, utilising industry standards such as OWASP and NIST.
Our platform automates scanning while combining it with manual penetration testing by security experts to achieve maximum coverage. We provide detailed reports that rank weaknesses by risk score, allowing development teams to work on them and create an effective security roadmap.
Astra’s easy-to-use dashboard provides real-time vulnerability data for enhanced security management. Our platform’s integration with popular CI/CD tools, such as GitHub, enables us to run continuous security testing throughout the development life cycle.
2. Rapid7
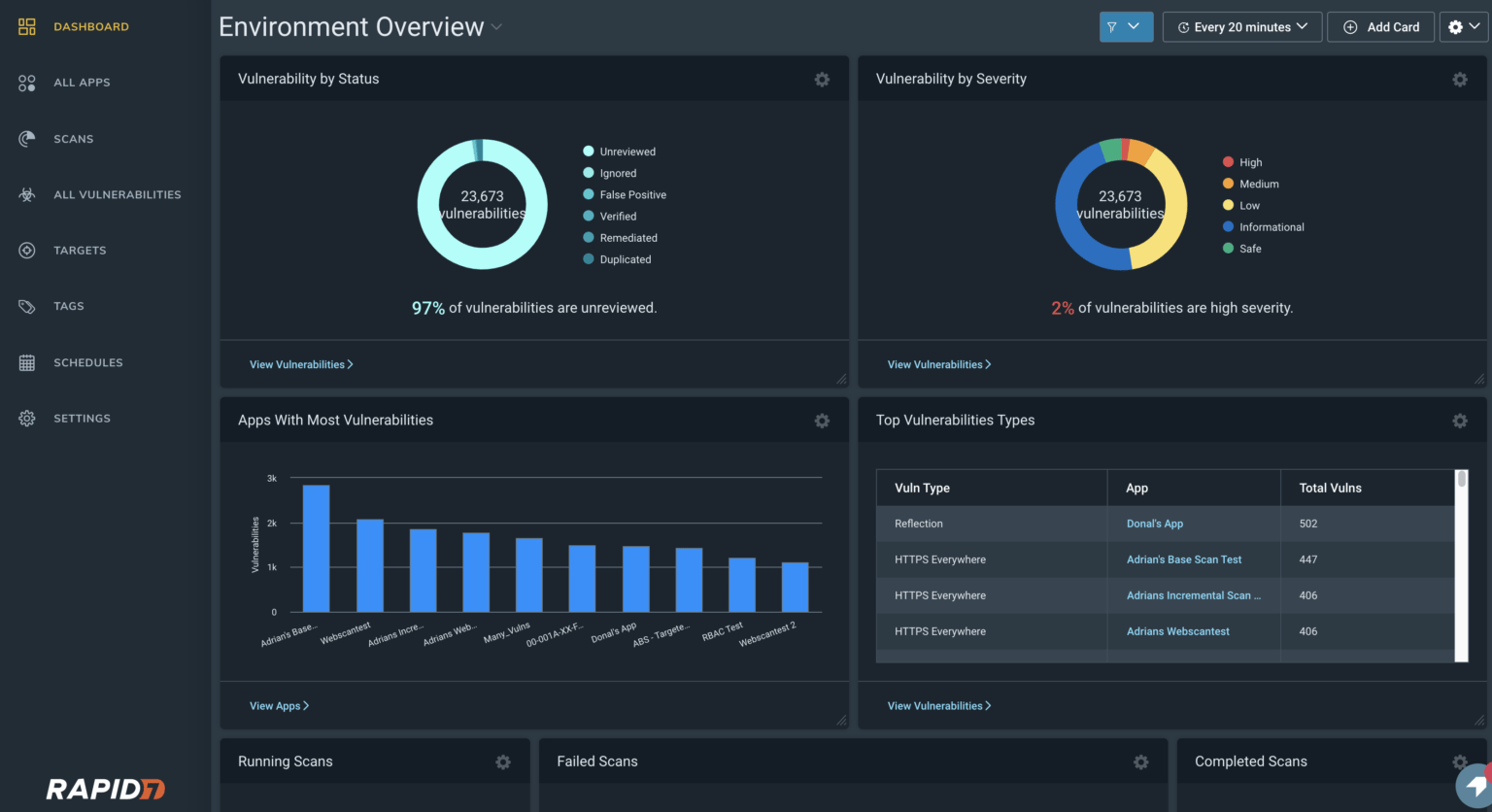
- Category: Managed cybersecurity detection and response with skill development for professionals
The powerful cloud-based platform from Rapid7 called the Insight Platform, provides continuous attack surface monitoring, real-time vulnerability assessment, and round-the-clock threat detection and response with MDR. This helps run end-to-end security audits for your SaaS platform and safeguard all your cloud data.
Their compliance tools help you achieve regulatory compliance, and their penetration testing services assist in locating CVEs. Supported by cutting-edge research initiatives, Rapid7 provides the automation, visibility, and analytics required for complete security.
3. HackerOne
- Category: Bug Bounty & Vulnerability Management Platform
HackerOne has a leading bug-bounty platform that brings the strengths of expert hackers to your company. You can incorporate insights from them to safeguard your systems against hackers.
They also offer a vulnerability management platform that helps businesses streamline managing and remediating vulnerabilities. The platform features application security, attack resistance management, and cloud security.
You can thoroughly audit your systems by combining their products – HackerOne Bounty and HackerOne Assessments.
4. Intruder
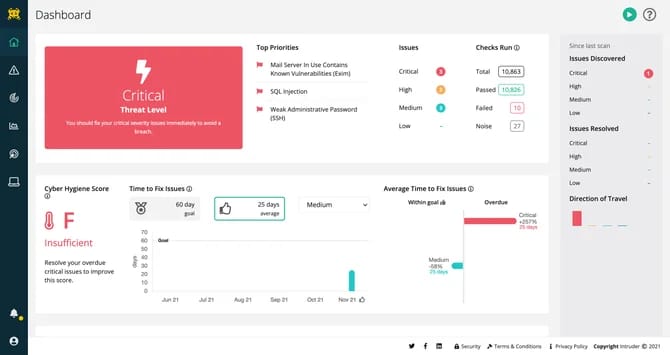
- Category: Vulnerability scanning, pentesting, and compliance reporting
Intruder is a dedicated application vulnerability scanning tool that offers attack surface monitoring, compliance reporting, and continuous vulnerability scanning features, which makes the security auditing process simple with automation.
They create detailed vulnerability scanning reports that help you fix security loopholes and prepare for compliance audits. Their features include internal and external vulnerability scanning, cloud security scanning, manual pentesting, and continuous scanning.
Evaluate trusted Intruder.io alternatives and competitors that balance automation with expert-driven validation and reporting.
5. Qualys
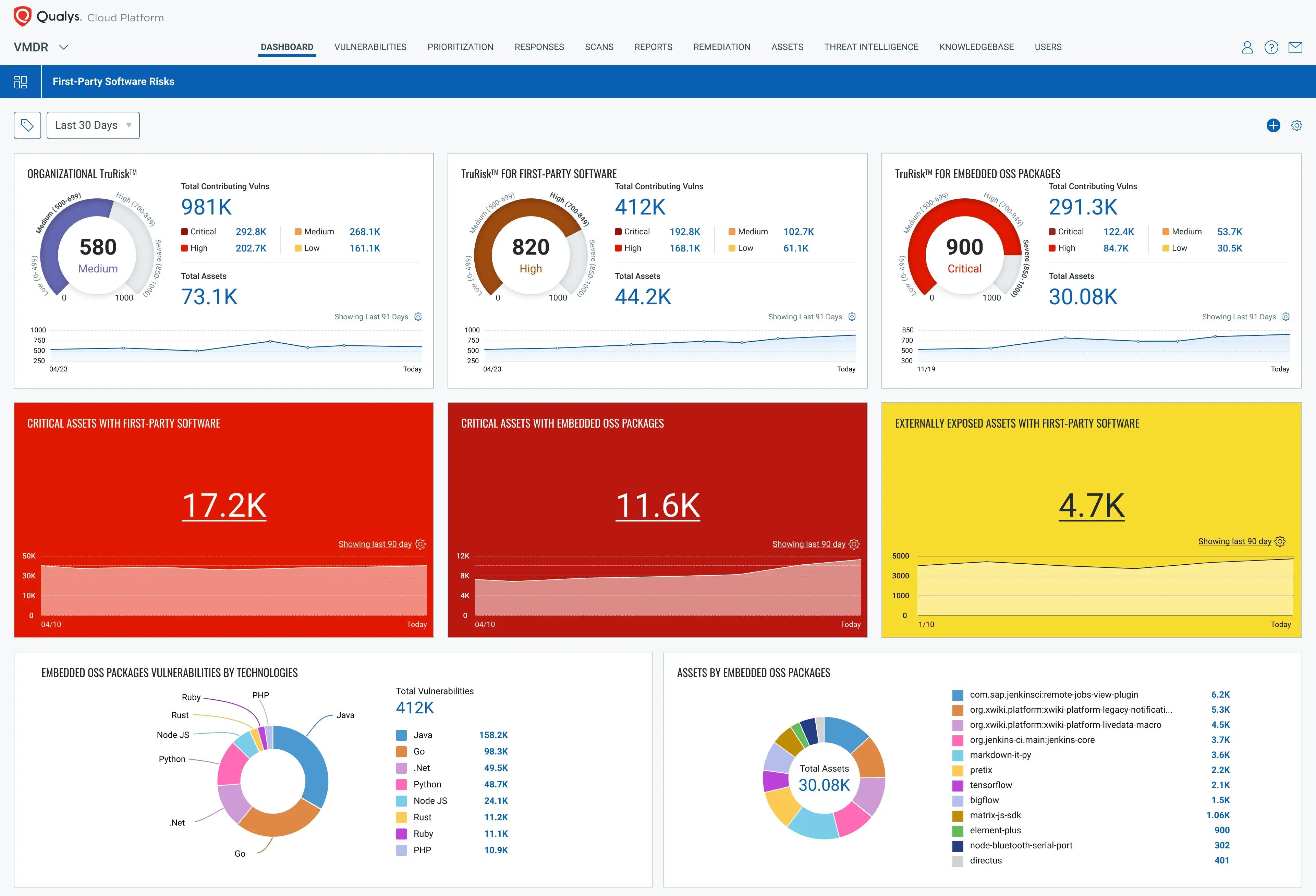
- Category: Managed vulnerability detection, compliance, and protection for IT systems
Qualys is a great tool for cloud security management and incident response. Its cloud platform is an asset monitoring tool that gives you 2-second visibility on all your IT assets deployed on the cloud. In addition, it has vulnerability management and surface monitoring programs.
Using VMDR and Threat Protection, Qualys continuously discovers and patches vulnerabilities. Their Cloud Inventory & Assessment platform handles misconfiguration detection, while the Cloud Agent handles real-time device protection.
6. IBM
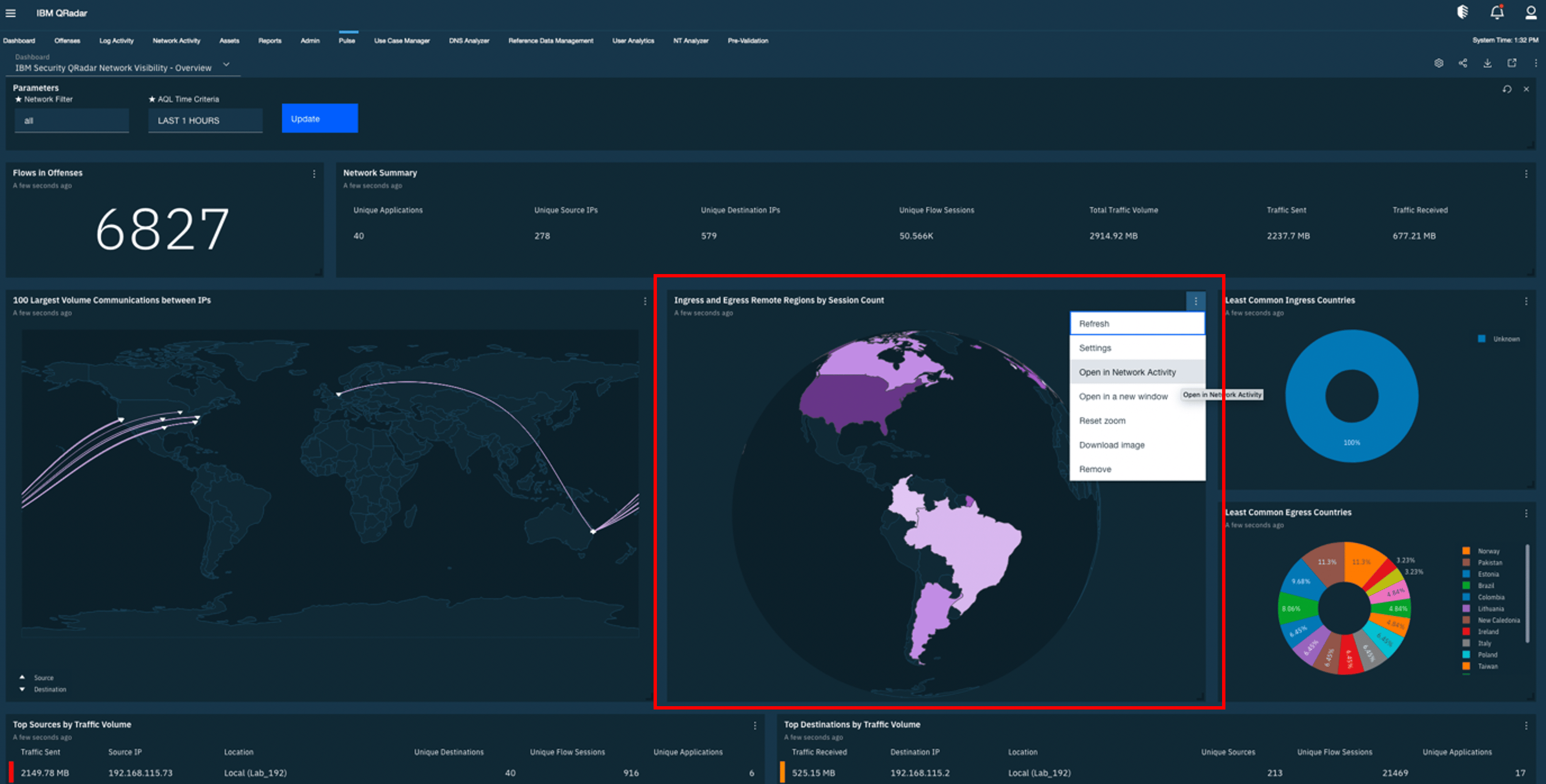
- Category: Comprehensive Cybersecurity Solutions with Industry-Leading Expertise
IBM Security offers vulnerability management, penetration testing, compliance assistance, and incident response. Their scanners use threat intelligence to identify known and emerging vulnerabilities.
At the same time, their security professionals conduct in-depth penetration testing to expose business logic vulnerabilities and find combinations of weaknesses that could be exploited when combined. IBM Security also helps you navigate the ever-evolving compliance landscape and offers expert guidance in the event of a security breach.
7. EY
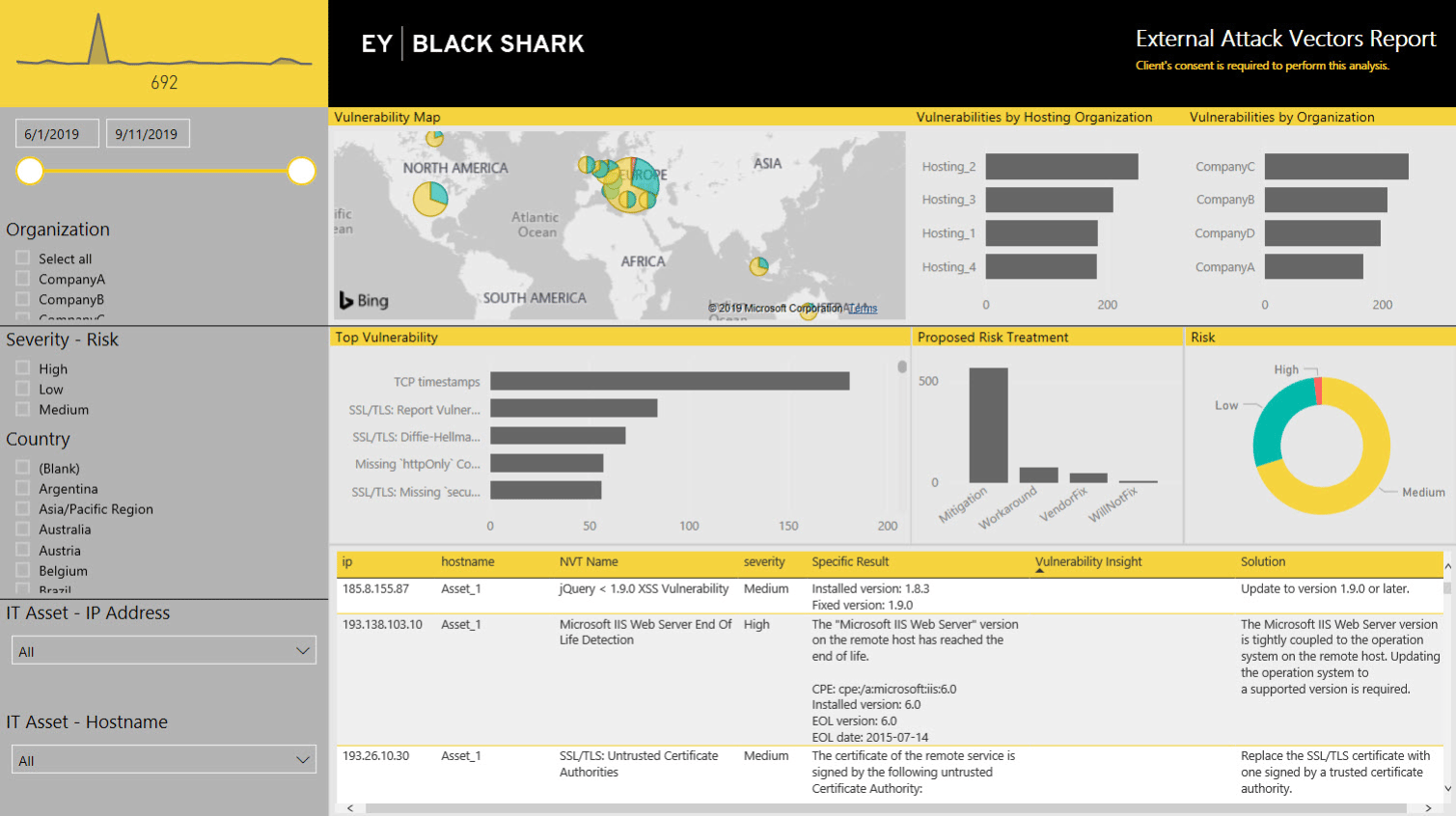
- Category: Strategic Security Consulting and Managed Services
EY Cybersecurity takes a strategic approach to securing your SaaS environment with its team of experts to help you develop a customized security plan. EY offers vulnerability management, penetration testing, compliance assistance, threat detection and response, and digital identity and access management.
EY specializes in providing personalized cybersecurity services – from safeguarding your supply chain and third-party lifecycle to data protection and privacy, they can transform your security posture.
Final Thoughts
As cyber threats evolve and become more prevalent, SaaS companies should prioritize regular cybersecurity audits to prevent them. These audits are essential for building trust with customers.
By demonstrating a commitment to data security through regular audits, SaaS companies attract and retain customers who entrust them with sensitive information. Audits are critical in proactively managing vulnerabilities and help create a roadmap to compliance with regulations.
Identifying weaknesses before attackers can exploit them can significantly reduce the risk of data breaches and financial losses, ultimately protecting a company’s success and security.
FAQs
1. Why do SaaS companies need regular cybersecurity audits?
SaaS companies manage sensitive customer data and run critical services in the cloud. Regular audits identify vulnerabilities, strengthen compliance readiness, and build customer trust. Without them, risks like breaches, downtime, and reputational loss increase significantly.
2. What is the difference between a cybersecurity audit and a cybersecurity assessment?
An audit is structured, compliance-focused, and evidence-based, while an assessment is consultative and broader. Audits check if controls meet standards, whereas assessments highlight risks, recommend improvements, and evaluate overall security posture beyond compliance.
3. When should we choose an audit, an assessment, or a pentest?
Choose an audit for compliance readiness, an assessment for strategic risk insights, and a pentest when simulating real-world attacks. SaaS companies often combine all three for complete visibility into compliance gaps, systemic weaknesses, and exploitable flaws.
4. How is a cybersecurity audit performed from start to finish?
Auditors define scope, review controls, and run automated and manual tests. Findings are compiled into a report with severity ratings and remediation steps. The process closes with follow-ups to verify fixes and align with compliance frameworks.
5. How long does a cybersecurity audit take for a SaaS company?
Depending on scope and systems, SaaS audits take one to four weeks. Smaller startups may complete audits in a week, while larger platforms with complex cloud, API, and app ecosystems require longer timelines for thorough evaluation.








