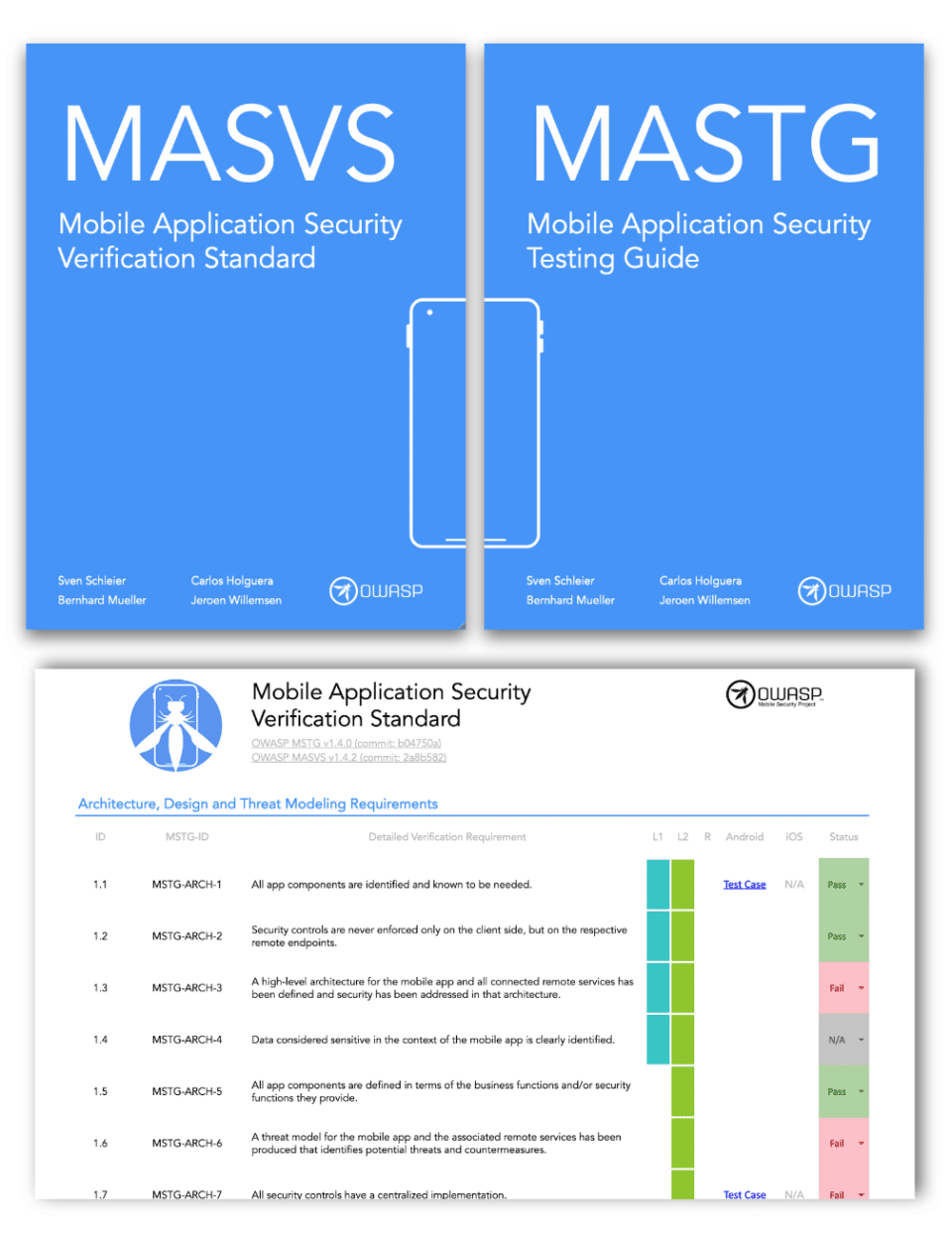
As mobile technology keeps expanding the security of mobile applications has become crucial. Mobile apps often manage sensitive data, ranging from personal details to financial transactions, making their protection from potential security threats vital. Among the most exhaustive and universally recognized guides for secure mobile application development are the Mobile Application Security Verification Standard (MASVS) and the Mobile Security Testing Guide (MSTG), both developed by the Open Web Application Security Project (OWASP).
The OWASP mobile app security checklist is an essential instrument for understanding, integrating, and verifying critical security controls during the development and testing stages of mobile applications.
In this article, we provide a 6-step OWASP mobile app security checklist, its features, and demonstrate how it can be efficiently embedded in your mobile app development workflow.
Understanding the OWASP Mobile Security Project
The Open Web Application Security Project (OWASP) is a globally recognized nonprofit organization with the prime objective of securing software applications. It offers an array of no-cost resources, such as tools, methodologies, and benchmarks. One of it’s initiatives is the OWASP Mobile Security Project which focuses on mobile application security. Its prime objective is to assist organizations in developing and deploying a uniform strategy for mobile application security.
The OWASP mobile app security checklist is an offshoot of this standard. The checklist is scalable and modifiable.
The OWASP mobile app security checklist includes data storage and privacy, authentication, cryptography, and network communication, along with platform-specific considerations, code quality, and build configuration. The comprehensive nature of the OWASP Mobile Security Project, together with the specific and practical points in the OWASP testing checklist, makes it a must-have tool for any developer or organization aiming to bolster the security of their mobile applications.
Deep Dive into the OWASP Mobile App Security Checklist
As we probe further into the OWASP mobile app security checklist, we’ll encounter a comprehensive and accurate blueprint for protecting a mobile application. This OWASP testing checklist is all-encompassing, addressing a plethora of security aspects crucial for constructing a robust application.
Platform-Level Requirements
The platform-centric requirements concentrate on bolstering the app’s functionalities on distinct mobile operating systems, predominantly Android and iOS. This segment tackles issues inherent to each operating system, possibly pertaining to the interaction between the app and the system’s features.
Taking Android as an example, it provides guidelines on the secure employment of Intents, inhibiting debuggable apps in the final version, and mandating secure interaction with Android’s IPC mechanisms. Conversely, for iOS, it offers suggestions for the secure utilization of Touch ID, Face ID, and Keychain and ensures that the app doesn’t inadvertently leak sensitive information while operating in the background.
Data Storage and Privacy Requirements
A significant portion of the OWASP mobile app security checklist is devoted to data retention and privacy. This segment addresses secure methods for storing sensitive information on a user’s gadget and transmitting this information to a remote server. It provides directives to abstain from unnecessary data storage, enforce suitable encryption methodologies, secure the storage of session tokens, and safeguard data contained in backups.
This section of the OWASP testing checklist is of paramount importance since improperly managed data or poorly secured storage frameworks can expose an application to unauthorized data retrieval or identity fraud. The checklist accentuates both the technical facets of secure data retention and the moral obligation to uphold user privacy.
Cryptography Requirements
Encryption plays a vital role in securely managing data in mobile applications. The encryption requirements section of the OWASP mobile app security checklist highlights the importance of correctly applying encryption methods to safeguard confidential information from unwarranted access. This comprises guidance on utilizing reputable cryptographic libraries, upholding robust key management practices, guaranteeing secure generation of random numbers, and evading common encryption missteps, like using hardcoded cryptographic keys or weak algorithms.
Improper encryption implementation can lead to deceptive security confidence – while it seems the data is secure, it might, in reality, be effortlessly decrypted by malicious entities.
Authentication and Session Management
Ensuring user validation and appropriate session control are key factors in upholding the security of user-profiles and their related data. In this portion of the checklist, the focus is on the secure management of user authentication data, endorsing multi-factor validation when feasible, and establishing secure session control.
Subjects addressed comprise obstructing username enumeration, securely preserving passwords (ideally using a ‘salted’ hash method), and securing session tokens during transmission and storage. These precautions assist in ensuring that even if a cyber attacker gets hold of a device, they won’t be able to take over a user’s session or misuse their login credentials.
Network Communication Requirements
The standards for secure communication in the OWASP mobile app security checklist put emphasis on guaranteeing that an app securely interacts with its backend infrastructure. This encapsulates mandating HTTPS connections, accurately validating SSL/TLS certificates to avoid man-in-the-middle intrusions, and securely managing data transmission.
Moreover, it includes the secure establishment of web services and the application of security headers to safeguard against prevalent web susceptibilities. A vulnerability in secure communication can reveal sensitive data during transit, thereby making it an essential domain to prioritize in mobile app security.
Code Quality and Build Setting Requirements
The section of the OWASP Mobile Security Checklist pertaining to code quality and build settings zeroes in on your app’s codebase and compilation configurations, forming the bedrock of your application’s security. It includes adhering to secure programming practices to ward off prevalent vulnerabilities like buffer overflows or injection attacks and ensuring that security measures are applied during the compilation process.
The OWASP testing checklist underscores the removal of debugging code or testing structures from production builds, as well as obfuscating or encrypting the code to raise the bar for potential attackers attempting to reverse-engineer your app. Secure programming practices combined with thoughtful attention to building configurations can help forestall the introduction of vulnerabilities into your app, substantially reducing the likelihood of it being compromised.
Tips for Effective Implementation of the OWASP Mobile App Security Checklist
Successfully integrating the OWASP mobile app security checklist into your operations requires more than just ticking off boxes. It necessitates a calculated, proactive approach to incorporating security protocols into every stage of your mobile application’s life cycle. Here are a few pointers to maximize the benefits of the checklist:
- Integrate with Your Development Process: Security should not be a footnote in your project. Instead, it needs to be integrated into the design and development stages. Infuse the checklist’s elements into your development and design dialogues. Doing so, you ensure security measures are organically part of your application’s architecture rather than appended later, which often turns out to be pricier and less effective.
- Prioritize Based on Your Application’s Needs: Not all apps call for the same security parameters. Reflect on the sensitivity of the data managed by your app, its exposure, and possible threat vectors when deciding the checklist elements’ precedence. For example, an app processing sensitive personal information may demand more rigorous data storage and encryption protocols compared to a basic app.
- Continuous Testing: Security is an ongoing commitment, not a one-off event. Constantly scrutinize your application against the checklist elements during its development, after every update, and periodically throughout its life cycle. Consistent testing will help you preempt potential security challenges as your application progresses and as fresh threats surface.
- Leverage Automated Solutions: There’s an array of automated security testing solutions at your disposal that can help enforce and validate many of the checklist elements. These solutions can assist in identifying common coding mishaps, insecure configurations, and other security challenges, allowing your developers to dedicate more time to crafting the app’s functionality.
- Remain Informed: The mobile security landscape is in constant flux, with fresh threats cropping up consistently. Regularly revisit updates to the OWASP Mobile Security Checklist and other security resources to ensure your app’s security measures stay current.
Structured and consistent application of the OWASP Mobile Security Checklist will help you notably improve the security of your mobile applications, safeguarding both your users and your organization from potential security risks.
Also Read: Mobile App Security Audit and Penetration Testing Checklist
Conclusion
To wrap up, security for mobile applications is no longer a luxury in our current digital era – it’s an essential requirement. The OWASP mobile app security checklist offers an all-inclusive, industry-endorsed blueprint to ensure your mobile applications’ resilience against potential security challenges. Ranging from platform-specific considerations to secure data management and network communications, this checklist is engineered to address every facet of your mobile app’s security necessities, thereby protecting both your users’ information and your company’s reputation.
With an array of security products and services, Astra Security can be your ally in implementing and sustaining top-tier security protocols. From vulnerability evaluations to security audits and more, let’s collaboratively create safer digital interactions. Get in touch with Astra Security today and accord your mobile applications the security they merit.








