For as long as we can remember, the cyber defense has been an important issue in the digital age.
It’s not that there’s a shortage of security solutions that help businesses and consumers fend off today’s threats. Hackers are just getting smarter and craftier in exploiting software vulnerabilities.
The bad news is, security companies seem to be at a disadvantage against cyber criminals when looking at the overall cost of breaches. According to statistics, the costs of cybercrime is expected to reach $6 trillion annually by the year 2021.
For individual cases, the average cost of data breaches for every record lost or stolen is $148. Remember, this doesn’t include the soft losses incurred due to downtime — not to mention the loss of your customers’ trust, which can be harder to recover than lost revenue.
When it comes to cybersecurity, prevention is always better than cure. What you need to do is implement a proactive web security that can stop breaches before they do damage.
Here are top 7 strategies you need to adopt for the proactive cyber defense of your website:
1. Keep your CMS Updated
If you use a CMS or Content Management System like WordPress, make it a habit to update your entire website ecosystem whenever possible. This includes your plugins, themes, and the CMS itself.
Fortunately, most website platforms consolidate all updates into one page. WordPress, for example, has a designated page for all available updates for your plugins, themes, and CMS version.
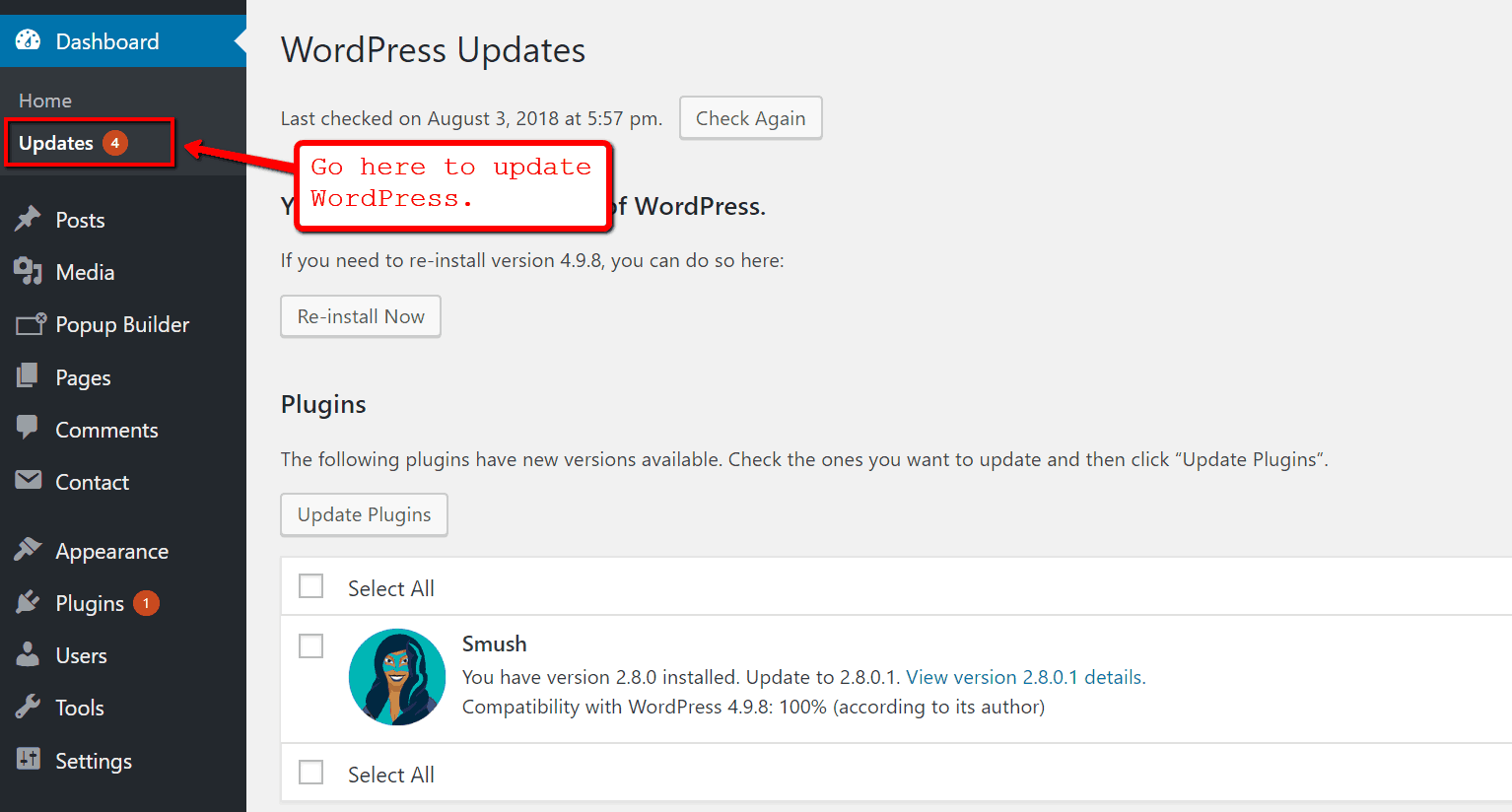
Keep in mind that software updates are rolled out to patch potential vulnerabilities found in previous versions as well as improve the overall performance of the CMS. The more your forego updates for your website’s components, the more vulnerable you become to cyber-attacks.
To have a better grasp of which CMS is more secure, we’ve put together a security comparison article for WordPress, Drupal, and Joomla.
2. Invest in Employee Training
For companies, cybersecurity is a team effort that requires everyone’s involvement.
Small startups, for instance, tend to have a BYOD or Bring Your Own Device policy that allows employees to use their own gadgets for everyday tasks. As cost-efficient as it may, it exposes your organization to a number of security vulnerabilities — from malware infections to device theft.
That’s why a proactive cyber defense strategy should always have an employee training aspect. For this, some points you can cover include:
- Password Safety Awareness
Believe it or not, some people still use weak passwords such as “123456,” “password,” and “admin.” This will put your entire website platform or cloud storage at risk of unauthorized access if an employee’s login credentials get compromised.
- Avoiding Suspicious Links
Apart from using terrible passwords, there are also gullible users who haphazardly click links even if they’re from suspicious sources. The same goes for malware-carrying email attachments that irresponsible individuals tend to download without a second thought.
- Staying Away from Removable Storage
Even if you put your online connections on lockdown, malware can still get to your network via removable storage devices. Flash drives, memory cards, external drives — consider banning the use of these devices and stick to secure cloud storage solutions, like Dropbox or Google Drive.
- Use Encrypted Messaging Apps
If members of your team are allowed to work remotely, use encrypted messaging apps like Telegram to protect your communications against digital eavesdropping. Also, discourage your employees from connecting to public Wifi networks without identifying its source first.
3. Leverage a Web Application Firewall
A DDoS or Distributed Denial of Service is one of the most common forms of cyber-attacks that hackers use to put websites down. It occurs when hackers use a large network of infected computers — also known as botnet — to flood a website’s servers and block access to human users. To have a better understanding of how hacking works, you can read our article about the 20 must-know hacking terminologies.
In addition to costly downtimes, DDoS attacks are often precursors to even bigger, more elaborate hacks, particularly ransomware incursions.
To defend against DDoS attacks, a timeless approach is to use a WAF or web application firewall to automatically detect and filter malicious HTTP traffic. While businesses should definitely consider premium services, CMS users can utilize free plugins.
4. Outsource a Data Protection Officer
For businesses that collect and manage customer data in the EU region, the GDPR or General Data Protection Regulation law requires you to appoint a DPO or Data Protection Officer to help you with compliance.
Put simply, a DPO is a professional with expertise in global data privacy regulations and other GDPR-related rules. Since they are in charge of conducting risk assessments in your organization, they must also have a high level of understanding of cybersecurity, potential online threats, and prevention strategies.
You are required to hire a DPO if your business falls under any of the following categories:
- Your core activities require the large-scale, systematic processing of data on a regular basis.
- Your core activities include categories of data that relates to criminal convictions and offenses.
- You collect and process personal information as a public authority.
To comply with the GDPR, the fastest course of action you can take is to get an outsourced DPO for your business. Not only is it more affordable than hiring a full-time staff, data protection agencies can also do the heavy lifting for you in terms of screening a candidate’s qualifications.
5. Create Regular Backups
If you built your own website from scratch, chances are you encountered the option to create backups for your content on multiple occasions.
Major web hosting service providers offer tools that can help their clients schedule automatic backups.
In cybersecurity, a backup can be considered as a last line of defense in case all the other security measures failed in preventing a breach. The good news is, backups are extremely effective in minimizing the effects of a cyber-attack.
If you constantly create backups of your website, you can always restore its normal operation within a few hours without any lasting repercussions.
Aside from the automatic backup tools you can find in most web hosting services, you can also leverage third-party software.
6. Use a Virtual Private Network
A VPN or Virtual Private Network is a service that keeps your data private and protected by routing your connection through a secure server. It follows different protocols that manage your connection between the VPN server and the site or web service you’re trying to access.
The most common use case of VPNs is to secure the connection of a remote employee who’s trying to access important data while connected to a public network, such as Wi-Fi hotspots in a coffee shop, mall, or restaurant.
With a VPN, your connection is encrypted through a tunnel where you’re protected against digital eavesdropping. Not even your internet service provider should be able to monitor your online activities.
7. Leverage a Content Delivery Network
Lastly, website owners can use a CDN or Content Delivery Network to protect their online assets from traffic-based attacks. What it does is cache your website’s data into multiple proxy servers — offering mitigation against application layer and DDoS attacks.
Some CDN services also feature security add-ons that can help protect your online assets from hackers, including but not limited to IP masking, traffic monitoring, and an integrated WAF.
On top of its security benefits, a CDN can give any website a significant boost in performance. It reduces latency for users by utilizing the nearest available proxy server, which is why you need to review a CDN company’s coverage to make sure your target audience can reap the performance benefits.
Conclusion
In a hyper-connected world, having a proactive approach to cybersecurity is no longer an option.
You need to act now and protect your assets from security threats that can compromise the stability and integrity of your business. With the tips above, you should be well on your way to a more secure, successful future. Cheers!