Penetration testing is important in avoiding data breaches and keeping data secure. It’s not just about knowing if an attacker can get into your system, but having a clear plan on how to stop them. Penetration testing, or pen testing as it is called, is a technique used to test a computer system, network, or web application to find security-related defects.
Penetration testing is done by a person called (a pen-tester) or using an automated penetration testing tool. In this blog, we will put together a list of top pentest tools in US that are widely used.
Understanding Manual and Automated Pentest
Penetration testing is also known as pen testing, is a process of identifying, analyzing, and exploiting insecure vulnerabilities in an application. It is performed to verify the level of security of an application.
Penetration testing is not a one-time event but rather a continuous process. Penetration testers launch an attack to find vulnerabilities that a hacker can exploit. These vulnerabilities may be a logic flaw in the code, a flaw in the database configuration, or even a misconfiguration in the firewall. Penetration testing is limited to finding vulnerabilities and includes taking steps to exploit the vulnerability to gain access to the system.
Penetration Testing is done in 2 different ways:
1. Manual Penetration Testing
Manual penetration testing is an activity that is often carried out by a penetration testing team. The team of penetration testers is an expert in different fields. They can identify and exploit vulnerabilities in various systems.
Manual penetration testing is used to determine the security posture of the target environment and is used to identify vulnerabilities that require more in-depth testing. It is also used to verify the results of automated vulnerability scanning. It is a very important activity, and the findings are documented in a report at the end of the testing.
2. Automated Penetration Testing
Automated Penetration Testing is a process in which automated penetration testing tools are used to identify vulnerabilities in a target application. The automated penetration testing tools carry out the penetration testing by performing a series of automated attacks on the target application. The automated penetration testing tools can carry out the penetration testing activity using predefined commands.
Automated penetration testing is a method of testing the security of a system without any human interaction. For instance, if a website is being tested, the penetration testing software will browse the website, interact with it, and search for vulnerabilities.
What is Automated Penetration Testing Tools?
Penetration testing attempts to gain access to a system, network, or application to test their security. Penetration testing is a manual process, but this can be aided with automated penetration testing tools.
Automated penetration testing tools can be used to test any application (including website) for security vulnerabilities. Automated penetration testing tools can scan for vulnerable ports, test for weak passwords, brute force, and much more. Most penetration testing tools perform a wide range of tasks and can perform thorough penetration testing.
Automated penetration testing tools are used to detect any security risk or vulnerability in the applications. Both experienced, and novice security testers can use these tools.
Also Read: Continuous Penetration Testing: The Best Tool You’ll Find in 2022
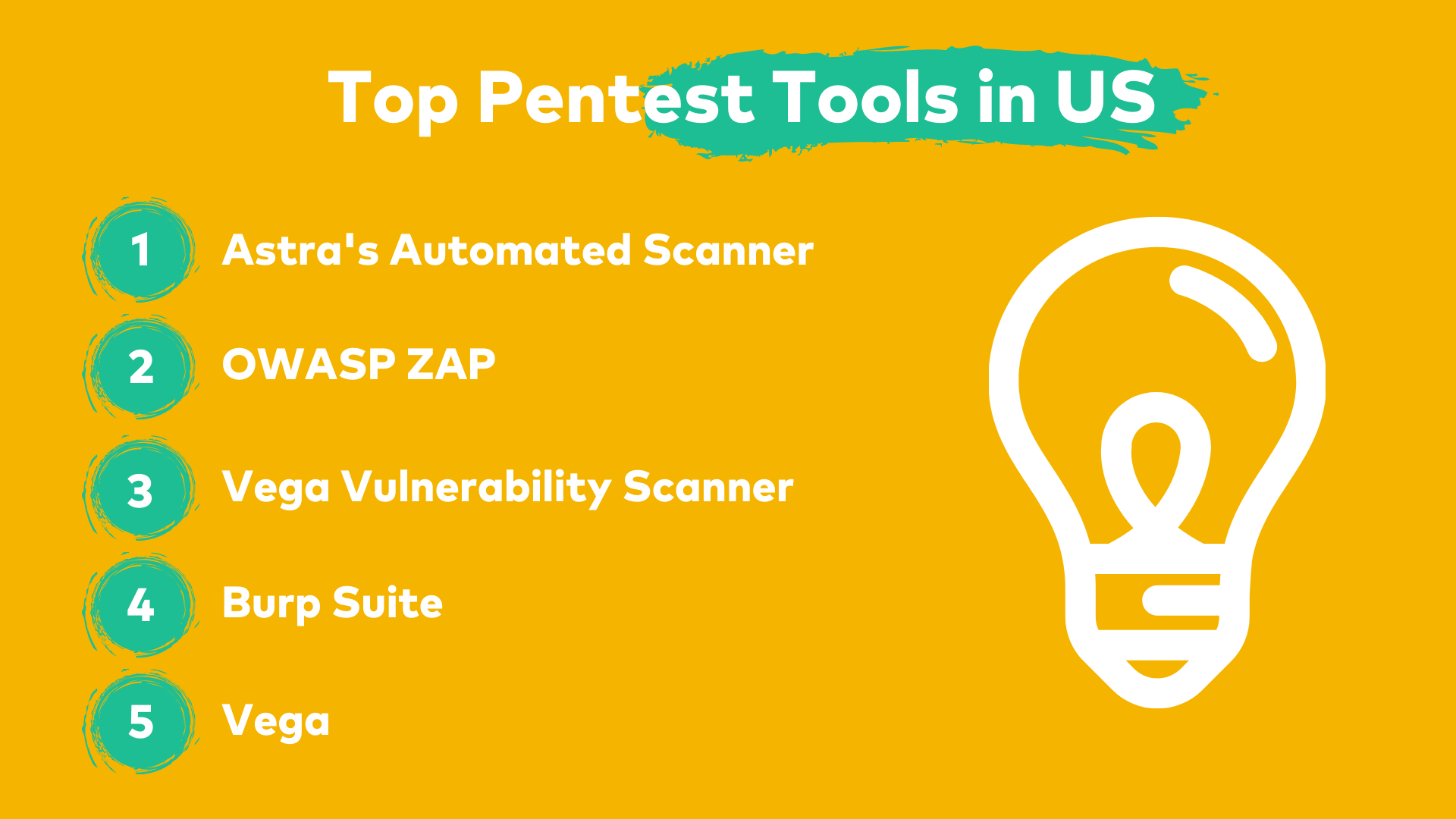
Now that we have understood what automated pentest tools are. Let’s check out a list of top pentest tools in US.
List of Top Pentest Tools in US
While manual testing is very time-consuming and requires several resources, an automated tool can save you a lot of time and effort in the long run. It is one of the most effective ways to find vulnerabilities on a website or a product. Now, we will explore some of the best pentest tools that you can use for your application.
1. Astra’s Pentest Suite
Astra’s Pentest Suite is a comprehensive solution for all your security needs. It was developed to help organizations of any size assess their security risk level, identify vulnerabilities, and implement the most appropriate security measures.
Whether you are a large security company with countless assets or a small business with limited IT resources, Astra’s Pentest Suite can help you protect your data and minimize your security risks. The solution is available for all the latest technologies such as:
- Web Application Penetration Testing
- Cloud Penetration Testing
- Mobile App Penetration Testing
- Blockchain Penetration Testing
- Network Penetration Testing
Astra’s automated pentest tool is used by organizations worldwide to keep their sensitive data secure from hackers. Astra’s automated scanner is used to automate security tests. The suite is based on more than 8000 automated scan rules, and it covers OWASP Top 10 vulnerabilities and other security testing methodologies.
Also Read: Why Firewall Penetration Testing is Essential to Your Security Strategy
Some more common features of Astra’s pentest suite:
1. Comprehensive penetration testing report
2. Pocket-friendly pricing
3. Compliance friendly (NIST, SOC2, GDPR, etc.)
4. Quick human support available
Also Read: 7 Best API Penetration Testing Tools And Everything Related
2. OWASP ZAP
The OWASP Zed Attack Proxy (ZAP) is an easy-to-use integrated penetration testing tool for finding vulnerabilities in applications. It is designed to be used by people with a wide range of security experience. It is ideal for developers and functional testers who are new to penetration testing.
ZAP provides automated scanners and a set of tools that allow you to find security vulnerabilities manually. ZAP has been actively developed and maintained since 2005 and is a mature piece of software that is battle-hardened. ZAP has also been ported to work on various platforms, including Windows, Linux, and macOS X.
3. Burp Suite
Burp Suite is an integrated platform for performing security testing of web applications. It is a collection of tools distributed in a client-server architecture. The Burp Suite client is installed on the user’s computer and communicates with the Burp Suite server to perform tasks such as scanning web applications for security vulnerabilities, attacking web applications through integrated penetration testing tools, and scanning the results of web application attacks to detect vulnerabilities.
Burp Suite is developed to support manual testing techniques and automate repetitive tasks, allowing the security auditor to complete a wider range of tests in less time.
Also Read: Top 5 Software Security Testing Tools in 2022 [Reviewed] | API Penetration Testing: What You Need to Know
4. Vega
Vega is a free and open-source automated security scanner and web security testing platform to test the security of web applications. Vega is a cross-platform, easy-to-use tool that runs as a web application within a browser. Vega was made to be a lightweight and user-friendly tool to allow non-security experts to scan the security of web applications.
5. Nessus
Nessus is one of the most popular vulnerability scanners, trusted by a lot of organizations worldwide. Nessus vulnerability scanner is used in vulnerability management, compliance and deployment, and security operations.
Developed by Tenable, the Nessus vulnerability scanner is the most popular vulnerability scanner on the market. Tenable also offers Nessus Network Monitor, the only network monitoring solution that natively integrates with Nessus vulnerability scanner. Tenable also offers Tenable. Sc, is a powerful web application for managing your vulnerability scans and reporting.
Also Read- Best Tenable Alternative and Competitor
Three things to know before buying a Pentest Tool
Security is a huge concern for businesses, and with good reason. A broken security system can cost a company millions of dollars in a single hack. That’s why so many companies are investing in security tools. Of course, not all security tools are created equal. Before you spend your hard-earned money on a new tool, you should keep in mind a few important factors.
Here’s a list of four things you should keep in mind before buying a pentest tool:
1. Extend of Testing: If you need to test the security of your application, you need to know the extent of testing it can provide. Is it only capable of testing a single page? Or can it test the entire system?
2. Cost of use: A good tool is expensive, but that doesn’t mean you need to spend a lot of money. It would be best if you chose a tool that fits your budget. Be sure to check the different plans and determine how many tests you can perform with each before you commit.
3. Easy to Use: You shouldn’t have to waste a lot of time learning how to use your security tool. It should be simple to use and easy to navigate.
4. Comprehensive Pentest Report: The penetration testing report you get from a pentest tool can greatly impact your business. It can offer you the opportunity to fix problems before they affect your business. Or, it can give you a false sense of security, leaving your business open to attack.
How much does a pentest tool cost?
There is no fixed price for pentest tools. The costs vary from a simple website audit to a complex website or network penetration test.
The price of a pentest tool is dependent on several factors, including the
- Type of test,
- Scope of the target
- Amount of expertise required
- Number of scans
While a low-end price for a pentest tool may be around $2,000, an average price of a professional pentest could be between $1,000 and $5,000.

We at Astra Security offer three website security audit pricing as follows:
| Package | Pricing | Features |
|---|---|---|
| Scanner Plan | $199/monthly or $1,999 yearly | 1. Unlimited vulnerability scans 2. Expert vetted scans 3. Compliance reporting |
| Pentest Plan | $5,999 per year | 1. All Scanner Plan features 2. Manual penetration test 3. Cloud security review |
| Enterprise Plan | $ 7,999 per year | 1. All features of Pentest Plan 2. Verifiable pentest certificate 3. Multiple targets across assets. |
Why is Astra a Top Pentest Tool in US?
Unsettling security threats and the need to defend applications and systems against attacks have become a major concern for businesses and government agencies. This is why companies that store and manage user data use Astra’s Automated Pentest to keep them away from hackers.
Astra is a top pentest tool in US and worldwide that the world’s best companies and security engineers use. Astra’s Automated Scanner is a powerful tool used by thousands of companies.
Here are some amazing features of Astra’s Automated Pentest Tool:
- 8000+ tests to keep your infrastructure secure from hackers.
- Easy, accessible reports that you can interpret at a glance with the dashboard.
- Collaborate with developers from within the dashboard.
- Get detailed steps on bug fixing tailored to your issues and know exactly how to reproduce vulnerabilities with video Proof of Concepts (PoCs).
- Why keep your security status private? Showcase Astra’s Publicly verifiable certificate.
- Post pentest, Astra shows a potential loss in $$$ for each vulnerability, making it easier for everyone to understand the impact.
- For each vulnerability, Astra gives an intelligently calculated risk score.
- Pocket-friendly pricing.
Astra is the Security Team you never had. Learn WHY?

Conclusion
Security is a need nowadays as hackers are getting strong day by day. Automated pentest tools are one of the ways to keep your data secure from hackers. To ensure the safety of your data and information, you surely have to have a good security system in place. Some of these security systems can protect your data, but they can’t protect the data on a large scale, which is where Astra’s Automated Scanner comes in. Using Astra’s automated scanner, you can manage and secure your assets in a better way.
FAQs
1. What should you know before buying a pentest tool?
You should know:
a) whether the pentest tool comes with human support,
b) if it can run scans behind logged-in pages,
c) if it gives you a publicly verifiable certificate,
d) read their sample pentest report and see if it’s thorough enough.
2. How much does a pentest tool cost?
A pentest tool costs between $99 and $399 per month. Read about penetration testing costs.
3. Why choose Astra for Pentesting?
8000+ tests, adherence to global security standards, intuitive dashboard with dynamic visualization of vulnerabilities and their severity, security audit with simultaneous remediation assistance, CI/CD integration, continuous scans, these are the features that give Astra an edge over all competitors.
4. Do I also get rescans after a vulnerability is fixed?
Yes, depending on the plan, you get 1-3 rescans after the vulnerabilities are fixed.
















