In 2021, unauthorized access was responsible for 43% of data breaches. Among the data breaches that did not involve an error, misuse of privilege, or physical action, 62% were a result of stolen credentials.
Passwords are important – they differentiate an authorized user from an unauthorized user during an authentication process. The strength of your password represents your authority over an account. The weaker the password, the easier it is to breach your data privacy.
This article will provide weak password statistics, password theft statistics, and reuse and sharing statistics to keep you updated on the weakest links in cybersecurity.
Password Security Statistics
The following is a list of the 10 most used passwords in 2023
- 123456
- 123456789
- qwerty
- password
- 12345
- qwerty123
- 1q2w3e
- 12345678
- 111111
- 1234567890
Notice how some of the passwords do not even maintain the 8-character length. You’d see a general disdain toward the importance of setting a hard-to-guess password.
Nevertheless, there is a tendency of setting slightly harder passwords for accounts that we consider important.
Then again, a lot of us have a very vague concept of what consists of a strong password. What’s even more interesting is the propensity toward using the same password for multiple accounts.

Password Reuse Statistics
More than 60% of Americans use the same password for more than one account
13% use the same password for virtually all accounts. A whopping 59% of adults in the USA use birthdays and names as passwords.
The general logic behind using predictable passwords and the same password across multiple accounts is a simple one. They are easier to remember.
When it comes to keeping track of passwords, 36% wrote down passwords on a paper and only 15% used a password manager to keep track of passwords.
44% of internet users almost never change or reset their passwords
Only 34% updated their passwords regularly. 44 million Microsoft users were found to have reused passwords.
The habit of not updating passwords regularly has awkward consequences.
6% of US adults say they still have access to accounts belonging to their former romantic partner, colleagues, or roommates.
On the bright side –
34% of users change their passwords once per month while 15% reset their passwords multiple times every week. And a rare 6% of users change their passwords every day.
One should not, under any circumstances, retain the same password for more than 3 months. But the reality of password resetting is quite upsetting, as you can see from the password statistics.
Password Sharing Statistics
Sharing passwords through emails, messages, or even verbally, goes against the basic password-security protocol. However, there are situations where password sharing becomes necessary. For instance, if a team is collaborating on a password-protected platform, they might all need access to the password.
Now, what’s wrong with sharing a password through email?
Well, when you type your password into an email it goes as plain text – unencrypted. Hence, if someone gets access to your email, they automatically get access to the password.
Moreover, your email is stored in multiple servers – it’s in the sent box of the sender, inbox of the recipient, and a bunch of other places in between. Hence, unsafe.
Other popular methods of password sharing include online document sharing (43%), sharing through messages (41%), verbally (31%), and paper (21%). 24% of respondents never share passwords.
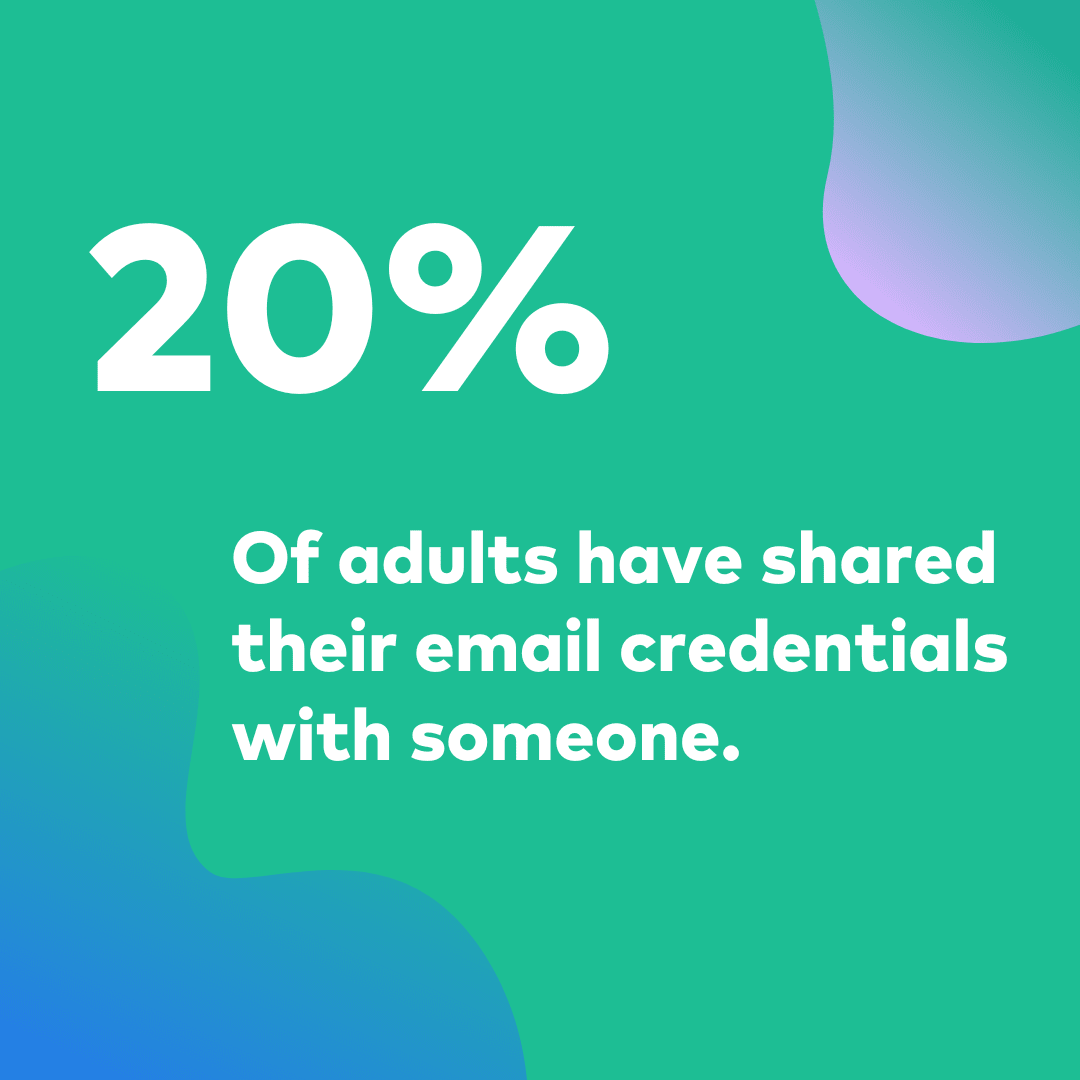
20% of adults have shared the credentials for their email accounts with someone. 22% of them have shared the password for a streaming platform. 17% have shared social media passwords and 17% share online shopping account passwords.
This shows a general trend of password sharing that very easily escalates from the personal circle to the professional milieu and creates vulnerabilities. This is exactly what makes two-factor and multi-factor authentication so important. 2FA and MFA add a protective layer between the account and its password.
The abundance of online accounts has also added to the breadth of attack surfaces.
The average adult has created 15 new online accounts during the pandemic
44% of these people plan to retain all new accounts. The prime concern is that 82% of them use the same password in more than one of these new accounts and 21% use the same password for all accounts.
This situation begs the question, what should a person do to remember and comfortably use passwords across 10-25 accounts? What is the safe way of dealing with so many passwords? The answer is password management.
Password Management Statistics
Password managers are tools that you can use to store, generate, encrypt, and access your passwords across platforms. When you store all your passwords in the password manager, all you need to do is remember your master key which will give you access to all the passwords.
20% of US respondents in a survey said they are not familiar with the concept of password managers
A survey by bitwarden showed, 59% of the respondents from the UK use their memory to manage passwords.
65% of US respondents said they do not trust password managers. 32% do not want to pay for a password manager.
Only 27% of US adults use random password generators while creating new passwords
You can use password managers (at least some) to generate random passwords for your accounts.
Randomly generated passwords have better entropy and increase the difficulty of a brute force attack.
But there’s a general nonacceptance towards password generators too. 38% think their current system is sufficient.
38% of IT organizations do not use password managers. 30% of IT professionals think a password manager has a negative effect on their productivity.
Yes, password managers too can be hacked, and they have been hacked in the past. Despite that, a combination of password managers, randomly generated strong passwords, and MFA is your best bet against password theft and brute force attacks.
The password management market is set to grow from $2.35 billion in 2023 to $7.13 billion in 2030 with a CAGR of over 17%.
Password Breach Statistics
In December 2022, LastPass, America’s most popular password management tool experienced a data breach. A single compromised credential caused exposure of its development environment to unauthorized actors.
The breach affected 30 million users. No wonder, a large portion of the American population does not trust password managers.
Between 2017 and 2020, hackers published 555 million stolen passwords on the dark web.
That’s why we stress on the importance of combining password managers with 2FA and MFA.
These stolen passwords are bought, sold, and later used in credential-stuffing attacks. Stolen credentials account for 80% of password-hacking incidents
Again, the propensity towards creating easy-to-guess passwords and then using them across platforms is to blame.
Poor passwords contributed to 81% of corporate data breaches
In 2019, 27% of hackers tried to guess other people’s passwords, and 17% made accurate guesses. Brute force hacking attempts as such occur every 39 seconds
62% of organizations think they have failed to take adequate steps toward securing data on mobile devices.
Multi-factor authentication can stop 96% of bulk phishing attacks and 76% of targeted attacks.
What is a strong password?
There has been a lot of debate around the topic of password strength. The general consensus is that the longer the password, the better. A Microsoft TechNet blog explained the formula for measuring password entropy (you can think of it as the difficulty quotient of a password).
The formula is log(C) / log(2) x L where C is the size of the character set and L is the length of the password. You can see from a mathematical standpoint the length of a password carries maximum weight in this equation.
“…if you’re using passwords with a character set of 10 (only numbers), in order to achieve the same amount of entropy as a character set of 94 (all possible ASCII characters), you only have the double the password’s length. To say it another way, a password that is 16 characters long and made up of only numbers provides the same level of difficultly-to-crack as an 8-character password made up of the possible 94 possible characters.”
A 2019 report by Scientific American said it is 62 trillion times harder to crack a password with 12 characters than a password with 6 characters.
Conclusion
So, from what we’ve seen so far, there are two keys to achieving stronger password security
- Longer passwords
Longer passwords mean better password entropy. The password length is directly proportional to the difficulty of brute forcing.
- Multi-factor authentication
With MFA enabled, just the password is not enough to log into an account. The added layer of security helps thwart most credential theft attacks.
A discussion about passwordless authentication has been making the rounds of industries. 87% of IT professionals think a passwordless environment using security appliances like hardware tokens, key pairs, and certificate-based authentication, could contribute towards more secure infrastructure. But that’s a story for another time.
FAQs
How can a password be stolen?
The two popular ways of stealing credentials is A) hacking into the active directory of websites that store customer credentials. B) stealing passwords directly from users using phishing and social engineering attacks.
What should I do if my password manager is hacked?
Once the breach is identified, your password manager will share instructions with you. You can do three things to add safety. 1. Reset the passwords stored in the vault regularly. 2. Never store your master password on an online medium. 3. Go for tools that support MFA.
What is the ideal length of a strong password?
While most sites prompt you to create an 8-character long password with different character types, it’s not long enough. Try to use at least 12 characters. Longer the better.
















