In our increasingly digital world, applications and online services have become deeply woven into the fabric of our daily lives, creating a growing need for secure digital environments. Security is no longer a luxury or add-on; it’s a fundamental necessity for any application, particularly so for Android apps. Given Android’s status as the most widely with more than 3.3B billion devices used mobile operating system, it naturally draws the attention of cybercriminals. Consequently, Android app developers must embed rigorous security protocols from the design stage right up to deployment to maintain maximum android app security posture.
In this article, we’ll navigate through a thorough android app security checklist that every Android developer should follow to ensure their applications are unassailable and secure.
Why an Android App Security Checklist is Essential?
An Android app security checklist serves as a systematically arranged guide for developers, ensuring all critical security zones are addressed during the app’s development process. This android security checklist covers the finest security practices, helping you steer clear of typical security pitfalls and defend against possible vulnerabilities.
A properly crafted Android app security checklist is not merely a list of tasks to be ticked off during development. It’s a cornerstone of your app’s security lifecycle, guaranteeing adherence to secure coding standards, secure data management, utilization of secure communication pathways, and routine updates of your app’s security defenses.
6-Step Android Application Security Checklist
Secure Coding Guidelines
The foundation of crafting a secure and robust Android application lies in secure coding. This practice revolves around creating code in a manner that prevents the incorporation of security vulnerabilities. A critical notion in app development is that “the best defense is a good offense.” This means that being aware of the strategies employed by attackers can arm developers with the tools for better android app security.
Data Protection
Ensuring secure data handling and storage hinders unauthorized access and preserves user trust. Data protection goes beyond being a technical matter; it’s a matter of user trust. Insufficient data protection can lead to a decline in user trust, regulatory oversight, and potential legal ramifications. Therefore, the integration of sturdy data protection measures in your Android app development process is critical.
Here are a few methods to implement in your android application security checklist:
1. Upholding Data Privacy:
Data privacy concerns the appropriate management, processing, storage, and utilization of user data, respecting user rights. It’s crucial that your app only requests necessary permissions and handles data in a manner that honors user privacy. Transparency about how their data is used and stored is essential. Offer them the choice to opt out of non-essential data gathering.
2. Secure Data Storage:
Android presents various options for data storage, including SharedPreferences, SQLite databases, Files, and others. Nevertheless, they all demand cautious implementation to stay secure. When using these, consider applying encryption to sensitive data. Android’s Jetpack Security library assists in encrypting files and shared preferences data. Also, try to avoid storing sensitive information like passwords or credit card details unless absolutely required.
3. Secure Data Transmission:
When your app interacts with servers or other services, the transmitted data should be encrypted to avoid interception. Employ secure communication protocols like HTTPS, SSL, and TLS to safeguard data in transit. Also, confirm the server’s identity before data exchange to avoid man-in-the-middle assaults.
4. Encryption and Key Management:
Encryption of data converts understandable data into undecipherable ciphertext, which can only be reversed using a specific decryption key. It is a vital aspect of both data storage and transmission. Android provides the Android Keystore system to generate, store, and manage cryptographic keys safely. Ensure the use of robust encryption algorithms and the proper management of keys, as mishandled keys can render your encryption useless.
Securing Network Connections
In an age of apps brimming with network-dependent features and services, network security is an essential part of Android app security checklist. Making certain of secure network communication is key to avoiding data leakages and safeguarding user privacy.
Here are a few methods to implement in your android application security checklist:
1. Ensuring Safe Communication with Servers:
Apps frequently need to interact with servers to retrieve or deliver data. This interaction with servers has to be secure to avoid unauthorized data breaches. You should always opt for HTTPS (HTTP Secure) over HTTP for all network interactions.
Besides resorting to HTTPS, it’s crucial to verify the server’s certificate prior to data exchange. This procedure, often referred to as SSL/TLS certificate pinning, confirms that your app is engaging with a legitimate server and not a fraudulent one. Application of certificate pinning can avoid man-in-the-middle (MITM) attacks, in which the intruder intercepts the communication flowing between your app and the server.
2. Authenticating Server-side Certificates:
The process of certificate validation entails confirming if the server’s digital certificate is valid and can be trusted. While Android takes care of SSL certificate validation from a trusted Certificate Authority (CA), it does not perform hostname verification. Therefore, it’s also important to confirm that the server’s hostname aligns with the hostname presented in the server’s certificate to ensure your app communicates with the correct server.
3. Preventing Man-in-the-Middle Attacks:
As noted before, man-in-the-middle (MITM) attacks involve an intruder intercepting, and possibly altering, the communication between two parties unbeknownst to them. You can deter these attacks by employing secure and updated versions of SSL/TLS protocols, executing certificate pinning, and authenticating server-side certificates.
User Authentication and Session Management
Both user identification and session handling are key elements in ensuring android app security. Effective user identification makes sure that only authorized individuals can access your app, while well-managed sessions help to shield a user’s ongoing session from interception and various forms of attacks.
Here are a few methods to implement in your android application security checklist:
1. Implementing Strong User Authentication:
User authentication is the process of verifying the identity of a user. Implement strong authentication mechanisms to prevent unauthorized access. This can involve the use of passwords, biometric data, or multi-factor authentication. If passwords are used, encourage users to set strong, unique passwords and securely store hashed and salted password representations, never plaintext.
For biometric authentication, Android provides BiometricPrompt API, which provides a standardized dialog to guide users through the authentication process. Additionally, using multi-factor authentication adds an extra layer of security. It requires the user to provide at least two forms of evidence to authenticate their identity, such as something they know (a password) and something they have (a mobile device to receive a code).
2. Secure Session Management:
Post-identification, users are generally given a session ID, which helps maintain the session’s state amidst requests. Session handling must be securely managed to fend off session interception attacks. Make certain that session IDs are random, distinct, and encrypted. Implement a session timeout that strikes a balance – lengthy enough to not inconvenience users but short enough to restrict the duration an attacker can exploit a hijacked session.
Handling Sensitive Data
Confidential information in mobile apps may comprise personally identifiable information (PII), payment specifics, log in details, among others. It’s vital to securely handle such information to safeguard user privacy and comply with various data protection laws and regulations. This is an important step in the android app security checklist.
Here are a few methods to implement in your android application security checklist:
1. Masking Sensitive Fields:
Masking implies substituting confidential data with asterisks or other characters in input fields. Mask confidential fields like passwords or PINs during their entry to avert shoulder surfing attacks.
Moreover, ensure that confidential data doesn’t appear in screen captures or screen recordings. You can stop screenshots or screen captures of your app by setting the secure flag on your app’s window.
2. Secure Logging:
While logging is crucial for debugging, it can introduce security threats if not correctly managed. Confidential information should never be included in logs. An intruder with access to the logs could exploit this information for malicious purposes. Use the Android Debug Bridge (adb logcat) tool to scrutinize your app’s log output and confirm that no confidential information is being written to the logs.
3. Not Storing Sensitive Data Longer Than Necessary:
To minimize risk, avoid retaining confidential data beyond its necessity to maintain Android app security. When the data isn’t needed anymore, ensure it is securely deleted and can’t be restored. For example, don’t store authentication tokens or other confidential data in persistent storage if it’s only needed for a session’s duration.
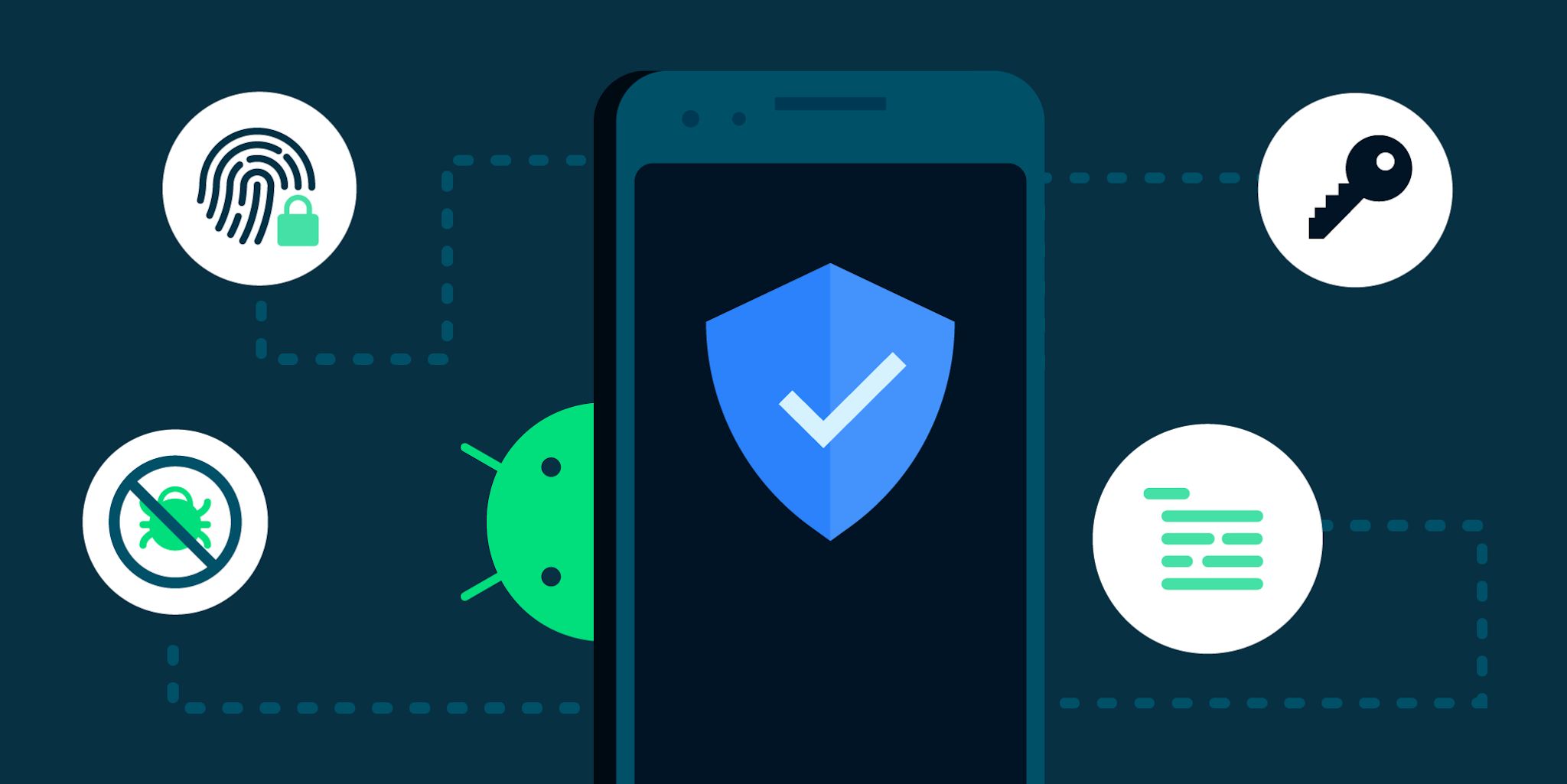
Using Android’s Built-In Security Features
Android, an extensively utilized mobile operating system, comes with a multitude of in-built android app security features that you can employ to bolster android application security checklist. Such features range from data encryption and secure user authentication to app integrity checks.
Here are a few methods to implement in your android application security checklist:
1. Android Keystore System:
Android’s Keystore System provides an encrypted container for storing cryptographic keys. Storing these keys in such a secure container makes it notably difficult for anyone to extract them from the device. You can utilize these encrypted keys for diverse purposes, including data encryption, user authentication, and data signing.
2. Biometric Authentication:
Android’s Biometric API offers an avenue for applications to request users for biometric authentication. Such authentication may involve fingerprint scanning, facial recognition, or iris scanning. Biometric authentication stands superior to traditional authentication methods like passwords or PINs and provides a user-friendly approach.
To implement biometric authentication, you need to verify the device’s hardware capabilities, display a biometric authentication prompt to the user, and manage the authentication response. Android ensures secure storage and non-exposure of biometric data to applications, thus improving the security of user data.
3. SafetyNet Attestation API:
Android’s SafetyNet Attestation API is a beneficial tool that lets you gauge the Android app security and compatibility of the Android environments where your application operates. It provides a cryptographically signed attestation, which helps you ascertain whether the device has been tampered with, contains potentially harmful applications, or exhibits any other Android app security risks.
Conclusion
Navigating through the constantly shifting cyber threat environment, we find it non-negotiable to have a solid Android app security checklist in place. Remember, your Android app security isn’t a one-and-done deal, rather it’s a commitment to persistent monitoring, timely updates, and applying patches to handle ever-emerging threats. An astute and forward-thinking approach to security comprises a good and unique understanding of Android app security infrastructure, a dedication to following the principles of secure coding and making good use of tools like Astra Security Scanner that efficiently spots and addresses familiar security issues.
Frequently Asked Questions (FAQs)
What is the OWASP 10?
The OWASP Top 10 is a list of the most critical web application security risks, updated every one to two years by a non-profit community of experts. It aims to raise awareness among developers and web application security professionals about the common threats and best practices to prevent them. The OWASP Top 10 covers various categories of risks, such as injection, broken access control, cryptographic failures, and more.
What are the most common mobile application threats in Android?
The most common mobile application threats in Android applications is insecure data storage which can expose sensitive information to unauthorized parties. Other mobile app vulnerabilities include malware attacks, insecure inter process communication, unsecure API, vishing, phishing attacks, etc.
What are common mobile app vulnerabilities in iOS?
Some of the common mobile app vulnerabilities in iOS are:
1. Broken cryptography: This occurs when an app uses weak or outdated encryption algorithms, or implements them incorrectly. An attacker can exploit this mobile application threats to decrypt sensitive data or tamper with the app’s functionality..
2. Improper platform usage: This happens when an app does not follow the security best practices or guidelines provided by the platform vendor, such as Apple. For example, an app may fail to use the Keychain API for storing credentials, or misuse the Touch ID or Face ID features.
3. Insecure communication: This refers to the lack of protection for data in transit between the app and the server, or between the app and other apps. An attacker can intercept, modify, or redirect the network traffic using techniques such as man-in-the-middle attacks, SSL stripping, or DNS spoofing.
4. Lack of binary protections: This means that the app does not implement sufficient measures to prevent reverse engineering, tampering, or debugging by unauthorized parties. An attacker can use tools such as ClutchMod, xcon, or class-dump-z to extract information, bypass security checks, or modify the app’s behavior.