Malware attacks are bad! They bring your business to a stand still and cause a loss money, reputation and even customers. Usually business owners only start caring about malware after they get infected with it. As they say everyone feels secure until they get hacked, and they haven’t got hacked until now because a hacker didn’t try. Once infected, it becomes imperative to understand the causes, consequences and steps to fix this mess called malware. Here’s a write-up that will help you understand the causes and guide you to fight malware and clear up the mess caused by it.
Malware is a malicious piece of code written to steal information and disrupt systems. In website security, hackers are able to execute this malicious code on your website by exploiting an already existing vulnerability in your code or infrastructure.
The Top 5 Causes of Malware Attacks:
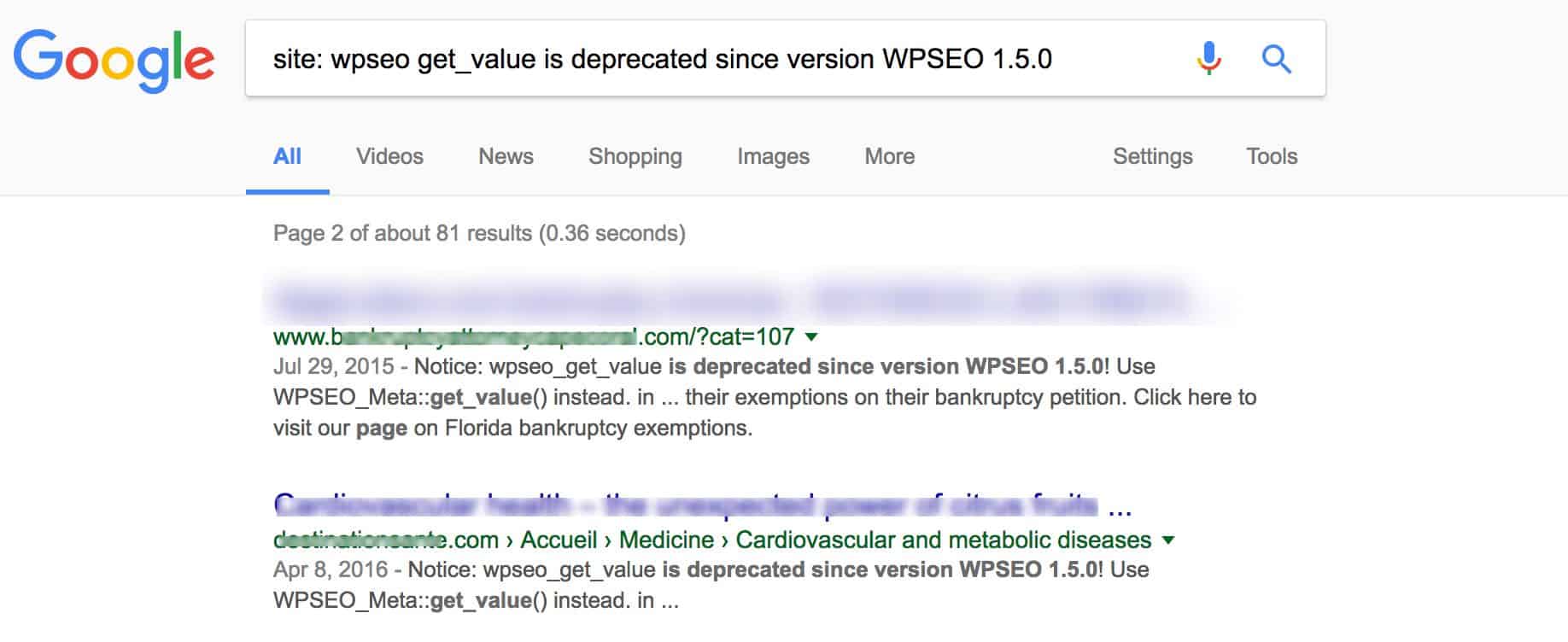
- Vulnerable Website Code: Just like good products attract visitors to your website, bad code attracts hackers. A lot of times your website code contains deprecated functions which are known to be vulnerable to some attack. Hackers often search for such functions around the web and since your website contains them, it automatically falls under the radar of hackers. Here’s an example of a deprecated function that hackers search:
[code inline=”true” scrollable=”true”]site: wpseo get_value is deprecated since version WPSEO 1.5.0[/code]And as a result, you see all the websites using this deprecated function:
- Un-patched Vulnerabilities: CMS’s like WordPress, OpenCart, Magento, Drupal, Joomla etc. all have had critical vulnerabilities discovered in them. These vulnerabilities leave millions of websites using these CMSs vulnerable to attacks. With time as these CMSs have evolved, the level of security has become better too. But then there are thousands of plug-ins/extensions these CMSs use which prove to be an easy entry point for hackers. The controversial Panama Papers Leak of 2016 was because of a vulnerability in the famous Revolution Slider plug-in used by millions of WordPress websites.
- Lack of Input Sanitization: A website has multiple forms like the search bar, login area, registration form etc. If the inputs taken by the user in these forms aren’t sanitize, they often allow a hacker to add evil code. This is an easy way to get entry inside the website without doing much. Attacks like XSS and SQL injection are direct consequences of the lack of input sanitization. Recently, Joomla patched an either year old LDAP vulnerability! The vulnerability was being exploited by hackers for 8 long years and cause of this vulnerability was lack of sanitization in input fields.
- Server Level Security Leaks: Less often than leaks in CMSs or code of the website, but servers also often become the reason for malware attacks. And when servers are attacked the number of websites infected usually runs in a few thousand with just one attack. Apache, Nginx, Azure, Tomcat all have been known to have vulnerabilities. Recently Equifax, an aggregator of that aggregates information of more than 800 million consumers was hacked. The cause of hack was said to be a vulnerability in web server.
- No Firewall on Website: Websites get infected by malware even after having all security best practices in place. It’s important to have an additional layer of protection that is looking our for your website 24×7. A website firewall assures only legit traffic reaches your website and malicious bots/hackers are stopped at the door itself. Here’s how relieved Astra’s customers feel on seeing the screen below:
While the above mentioned are the most common causes for malware attacks on websites, the causes are not limited to the above ones. Here’s a quick checklist which you can follow to assure that your website doesn’t attract malware:
The Website Malware Protection Checklist |
|
No Deprecated Functions in Code |
|
All Inputs Sanitized |
|
No FTP but SFTP |
|
Vulnerable SSH Version not in Use |
|
Website Firewall in Place |
|
All Plug-in Update |
|
Latest CMS Version Running |
|
Strong cPanel Credentials |
|
No Warnings in Google Webmasters |
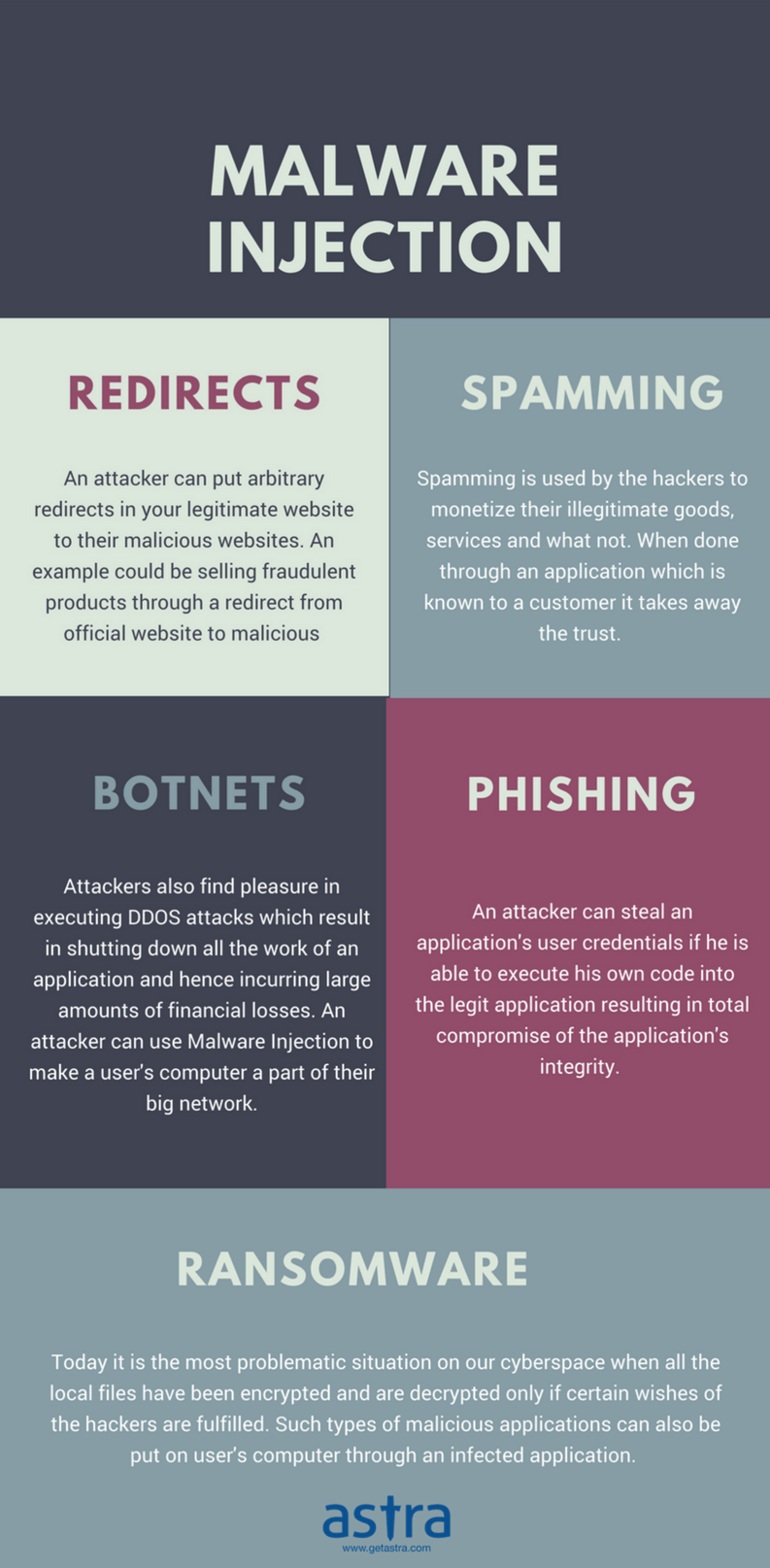
Hackers can have different motivations behind a malware attack. Depending on their motivation, the type of attack and consequences to your website differ. Sometimes hackers are in it for money or sometime they have greater agendas like utilizing web server resources to launch a bigger attack. A few consequences of malware attacks have been listed below
Consequences of Malware Attacks [Infograph]
- Loss of Sensitive Data
- Disruption of Services
- Malicious Use of Server Resources
- SEO Poisoning
- Launching Targeted Attacks on End-users
More consequences of malware attacks have been described in the infograph below:
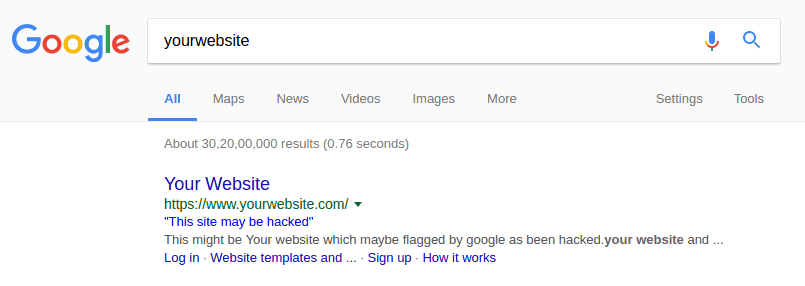
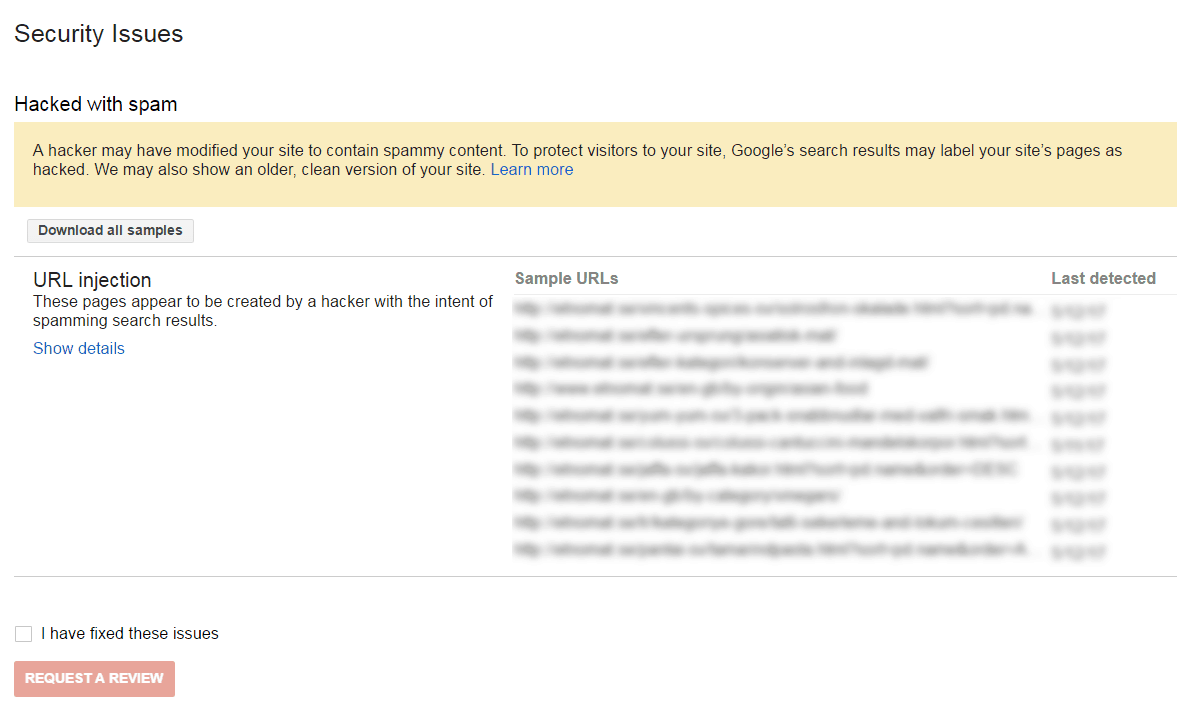
Sometimes malware still makes way into your website even though you’ve taken care of all the security best practices. Thanks to zero-days! If your website gets infected with malware, a few things done right and quick just after the attack can help you keep the impact minimal. After the malware attack as the time ticks, the size of repercussions also increases. You don’t want more customers to get infected or google to index your website with infected code. If google indexes a website while the website has malware, it flags the website and there is a significant decrease in SEO efforts.
Steps to Fix a Website Infected with Malware
- Check Your Search Results: Search results help you determine the magnitude of infection and also the type of malware that might have been the cause. There are some known malwares which create links of pharmacy products on your website, or the famous Japanese spam trying to capitalize on your SEO efforts. Entering the following code in google often helps determining these types of attacks:
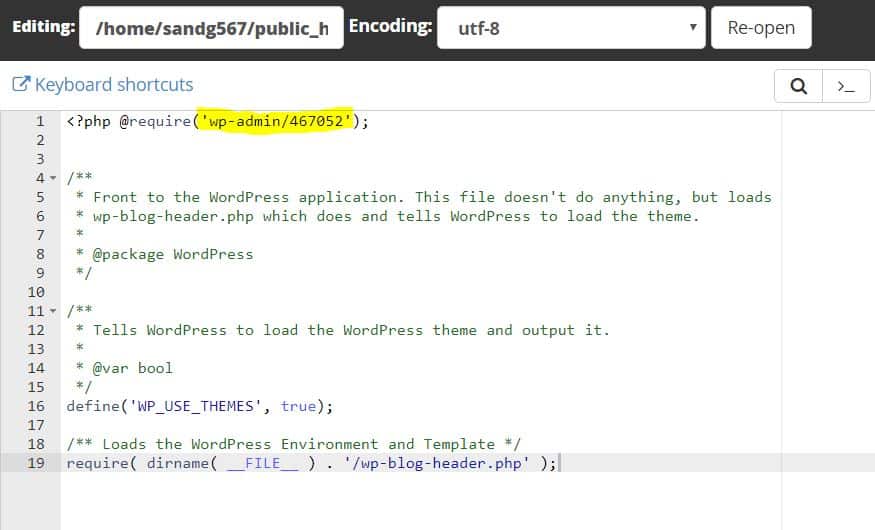
[code inline=”true” scrollable=”true”]site:YourWebsite.com[/code]If your website is infected with something like a Japanese spam, you’ll see the following page: - Examine .htaccess: Hackers usually add URL redirect codes in htaccess file of server. These codes are typical in SEO spam infections where hackers. Additionally, they hijack your website on Google Webmasters and for that they usually add some code in the htaccess file. If you find any malicious code, it should be removed immediately. Here’s how a malicious .htaccess file looks like:
RewriteEngine On ErrorDocument 404 http://some-maliciousSite.com/yyy.php[*] * Note. The file name/type could be anything RewriteCond %{HTTP_REFERER} .google. [OR] RewriteCond %{HTTP_REFERER} .ask. [OR] RewriteCond %{HTTP_REFERER} .yahoo. [OR] RewriteCond %{HTTP_REFERER} .bing. [OR] RewriteCond %{HTTP_REFERER} .dogpile. [OR] RewriteCond %{HTTP_REFERER} .facebook. [OR] RewriteCond %{HTTP_REFERER} .twitter. [OR] RewriteCond %{HTTP_REFERER} .blog. [OR] RewriteCond %{HTTP_COOKIE} !^._yyyy=yyyyy.$ (*** Present in some hacks) RewriteCond %{HTTP_USER_AGENT} .Windows.$ [NC] (*** Present in some hacks) RewriteRule ^(.*)$ http://some-maliciousSite.com/yyy.php [R=301,L] - Verify Authenticity of Index File: Hackers often include path to their malicious files in the index file. This way their malicious file is included throughout the website. Often it is difficult to identify malicious code in index file because it looks very legit, as if your developer as included another file in the index file. But on a detailed inspection one would see that the files included in index are malicious code.
Japanese SEO Spam: Steps to Find & Fix
If searching for your website on Google throws Japanese characters, then chances are that you’ve been infected with Japanese SEO spam. The interesting thing about this spam is that after you’ve taken care of bad code in index.php or htaccess, still the infection persists. This is because there are no specific traits of this malware. For every CMS, this malware is injected in a different way.
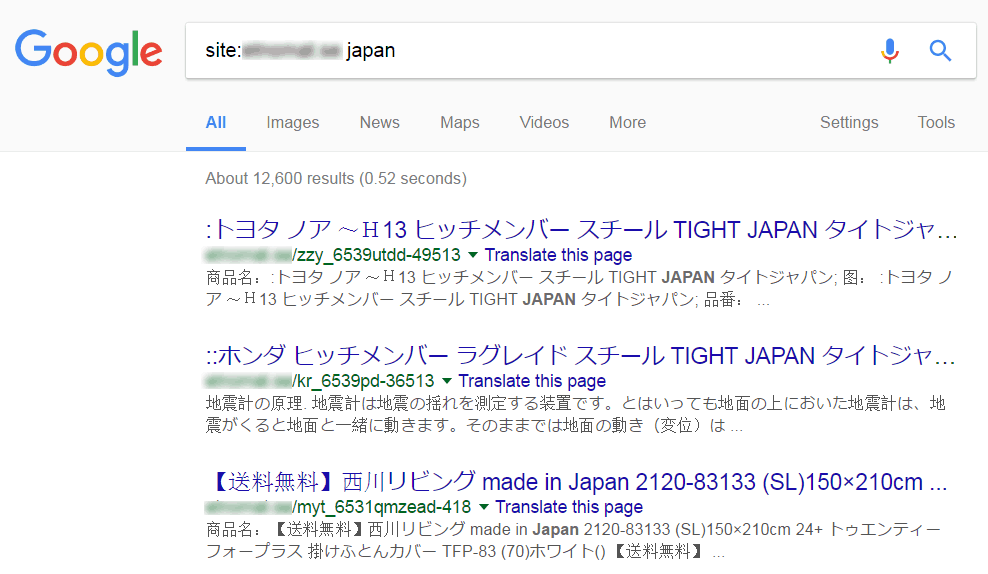
The interesting part is that is you go to the URLs indexed by Google, you’ll find that those pages do not exist on your website. A 404 error would be thrown to anyone who goes to those pages. But when a search engine indexes these pages, Japanese characters would shown up. This is a classic example of cloaking attacking aimed at capitalizing on your SEO rankings.
Find more about steps to fix this spam in a detailed guide on fixing Japanese spam or you could always contact us if you want our experts to help you here.

How to Remove Pub2srv & Mobisla Website Infection
We’ve been watching a specific malware infection targeting OpenCart & WordPress websites for several months. It’s commonly referred to as the pub2srv malware infection which redirects your website visitors to other malicious domains like go.pub2srv.com, go.mobisla.com and go.oclaserver.com.
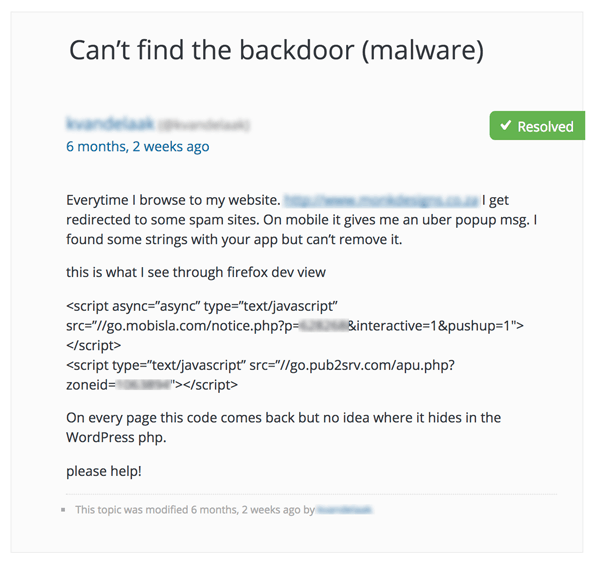
If you use WordPress, the key areas to look for Pub2srv, Mobisls & Oclaserver malware are:
- index.php
- functions.php
- Database tables
- Read about detailed steps here
If you use OpenCart, then be sure to check:
- oc_product_description table
- oc_category_description table
- A step by step procedure can be found in this guide
Here is a detailed step by step guide to fix Pub2srv, Mobisla and Oclaserver malware.
Website Links Redirecting to Spammy Websites
This is the most disturbing of all the infections. Depending on the extend till your website is infected this one gets bad if not taken care of early. Any visitor entering your website is redirected to a malicious website or phishing page. Here’s an example video:
Looking for malicious code in your index.php, searching for unwanted php files in core CMS files and checking your webmasters search console are the key things here. A more elaborate guide on how to deal with redirection issue can be found here.
3 Most Common Malware Infections in OpenCart & Magento
- Base64 Encoded Malicious Code: If you see files containing cryptic pieces of code which look something like the image below, chances are you’ve been infected with this malware. We usually encounter this infection which hackers are trying to target payment gateways of a Magento, OpenCart of WordPress store.
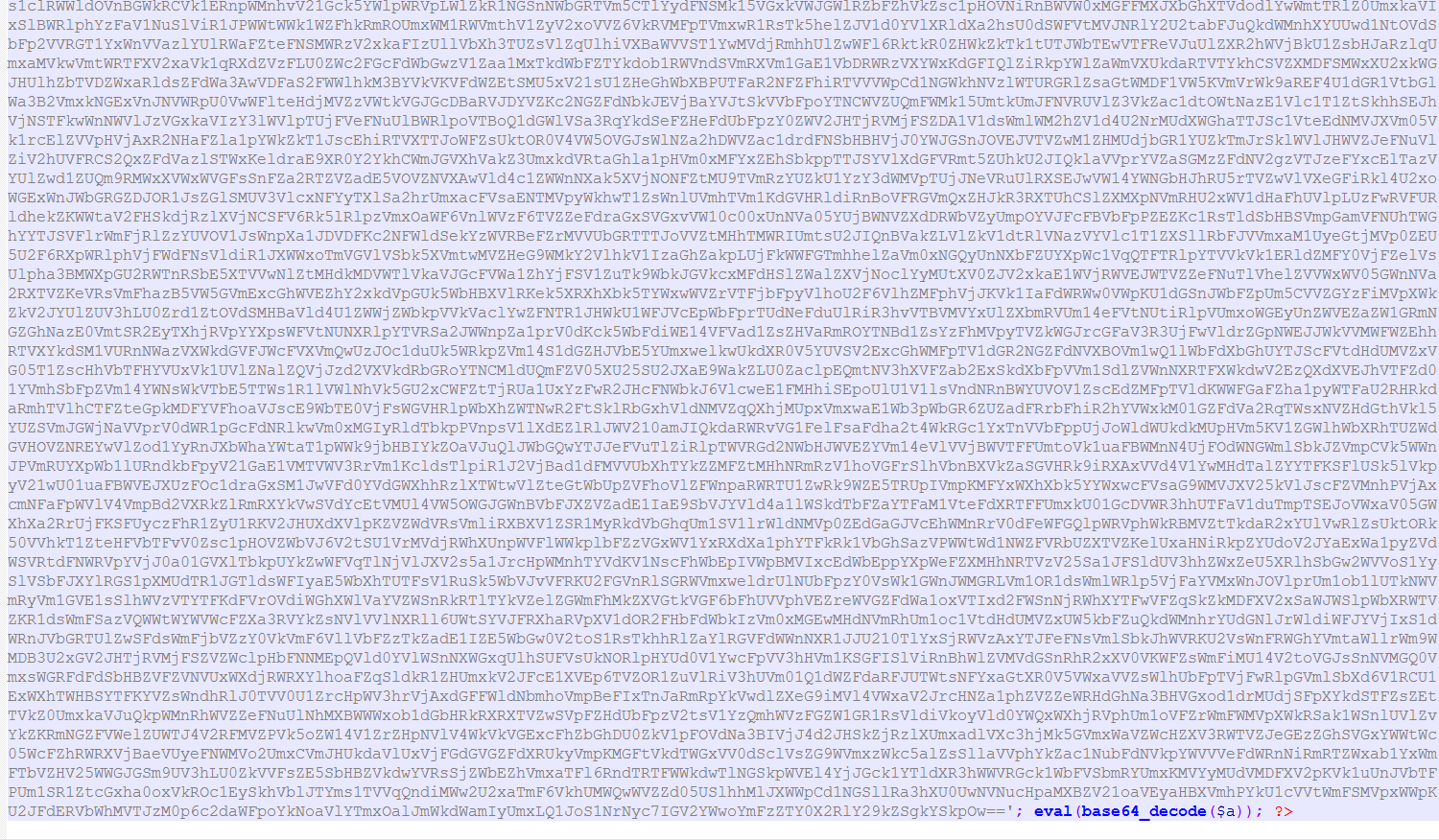
More about all these infections and how to fix them can be found at our detailed guide here
How to Prevent OpenCart Malware Injection
OpenCart being the popular e-commerce CMS is often targeted by hackers, bots and scammers. Usually the aim is to steal end customers’ credit card information. We’ve seen multiple reasons for OpenCart infections depending on the version you are using. A few top reasons include:
- OpenCart Version Has Never Been Updated
- Plugins With Weak Security Practices
- No Website Firewall or Bad Bot Protection
- Unrestricted File Uploads & Unsanitized User Inputs
We’ve made a detailed guide which explains how OpenCart malware be prevented.
Tackling Magento & OpenCart Credit Card Malware
Credit Card malware or Credit Card Hijack is when malicious PHP/JavaScript code is injected into Magento and OpenCart shops which allows hackers to intercept credit card data. This new way of credit card fraud has been undetected for 6 months.
With the increasing popularity of e-commerce platforms like Magento and OpenCart, the cases of malware infections have also risen. Hackers and cyber criminals have been modifying the core files of these CMSs to steal the credit card information of store customers. Here’s a detailed guide on how to locate this malware and fix it.
How to Fix Google Cross Site Malware Warnings?
Google often flags websites marking them with a ‘Cross Site Malware’ warning. Usually this warning is caused when your website is linking content or loading libraries from a another domain that has malware or is malicious in nature. Google usually tells the domain from where the questionable content might be getting linked.

The immediate steps to fix this should be to search your website’s entire code for the domain/URL which is causing cross site malware warning. You can do that by running this command in your SSH console:
Here /var/www should be the path of the home directory of your website. And URL should be replaced with the domain that is causing the cross site malware problem according to Google.
More details about the fix can be found here.
How to Remove Crypto Mining Malware Infecting WordPress, OpenCart, Magento Websites?
With the rise of crypto currencies & their power of making people rich within days – hackers have now started to target websites to infect them with crypto mining malware. Hackers use CoinHive, a service that is used as an alternative for advertisements by website owners to monetize traffic on their website.
CoinHive installs as javascript on the website and mines crypto currencies using Monero blockchain. While if a website owner is knowingly using CoinHive as a mean to monetize their traffic it’s not a problem. But hackers use CoinHive to illegally install the mining Javascript on hacked websites and use their resources to mine coins. A few domains which are usually used include:
- ads.locationforexpert[.]com
- camillesanz[.]com/lib/status.js
- security.fblaster[.]com
- fricangrey[.]top/redirect_base/redirect.js
- alemoney[.]xyz/js/stat.js
- africangirl[.]top/redirect_base/redirect.js
More details on finding this malware & fixing it can be found in our detailed guide here.
WordPress & Joomla Websites Slow Down – Cloki Malware Could be the Cause
Cloki malware is quite a dangerous malware that has been causing a havoc among various PHP based websites. The top CMSs infected are WordPress & Joomla. A few symptoms of Cloki malware are:
- Slowing down of the website
- Message from hosting provider about website utilizing too many resourcers
- Presence of unidentified cron jobs on the server
- Mail servers not working properly
Cloke malware is able to execute core server commands without having access to cPanel or SSH. A malware scan followed by carefully reviewing of all the cron jobs is recommended.
Details on how to fix the Cloki malware can be found in our detailed guide to remove the Cloki malware.
Conclusion
We clean hundreds of website from malware every month. In all these websites 80% of the times the malware has infected the website atleast 2-months before the owner comes to us. Imagine since when the vulnerabilities causing the attack would have been around, all unpatched. It is important to make sure you update all your plug-ins, stay updated with security trends around your website’s tech stack and be proactive in implementing the patches just as they are released.
After working with a number of website owners, we have realized that a business owner has so much to take care of right from sales, SEO, marketing, inventory etc. that often security takes a back seat. And then security looks like this elephant in the room that you do not want to address.
Our website firewall takes the headache of security away from the business owners, giving them a plug-n-play solution which comes pre-configured according to the CMS they are using. Astra requires no coding or IT knowledge and takes 5-minutes to install. Making security that simple and giving you time to concentrate on sales, marketing and other things.


















[…] today’s times, an online presence makes one vulnerable to unprecedented cyber attacks and a variety of malicious attacks on both small and large scales. On a daily basis, we encounter […]
[…] multiple reasons for this cross site malware warning. The first one being – your website is infected with malware & the second one being that your website is loading content from a website that is hacked or […]
[…] 700 WordPress and Joomla Websites have been infected with the ionCube malware that disguises as legitimate ionCube-encoded […]