In our interconnected world, the value of data is growing with cyber threats also on the rise. This causes the security and protection of data to become crucial. Organizations have become compelled to adopt strict measures to safeguard their data. Implementing security practices in data protection and encryption ensures the confidentiality, integrity, and availability of the data stored in the cloud.
Organizations, now more than ever, need to maintain control over cryptographic keys and secrets, manage access permissions effectively, and comply with industry standards and regulations.
Microsoft Azure, one of the leading cloud computing platforms, offers a range of tools and features that help reinforce data security in all of its states from data being at rest till use. Such Azure Data Security measures include key management, disk encryption, and secure data transit. After having read this article, your organization will be well equipped with the knowledge to strengthen its security position in Azure data security.
This article explores the best practices for ensuring Azure’s data security and encryption. It covers the following aspects:
- How to manage data states and controls?
- Microsoft Azure’s key management solutions
- How to effectively secure workstations?
- How can data encryption help?
How to Manage Data States and Controls?
When it comes to ensuring Azure cloud data security, understanding the states in which data can exist and the controls available for each state is important. By understanding this categorization we can implement security measures to protect our valuable information throughout its lifecycle.
Azure offers a variety of controls for each stage of data processing. These resources empower organizations to establish security measures. For instance, Azure Information Protection assists in classifying and safeguarding documents and emails. In Azure, data can typically be categorized into three states.
Data at Rest
This term refers to when data is stored in secondary memory like storage media, hard drives, optical storage, etc. It encompasses files, objects, containers, and any other static repositories of data. Azure Key Vault enables management while Azure Disk Encryption ensures the encryption of data when it’s at rest.
Data in Transit
Data is considered “in transit” when it is being transferred between modules, applications, or services. This includes scenarios like over-the-network transfers, communication across service bus (such as from on-premises to the cloud or vice versa, including hybrid connections such as ExpressRoute), and during an input/output process. Encrypting the data while it’s being transmitted ensures that it remains secure and unintelligible even if intercepted. To secure data during transit organizations can rely on Azure VPN Gateway.
Data in Use
Data in use refers to data that is currently being processed or accessed by applications and/or services. Many times, encrypted data is read from secondary memory, decrypted, and held in primary memory unencrypted. It is essential that this data remains encrypted even while in use to prevent unauthorized access. To ensure the security of data, in use, it is crucial to protect the applications, services, and systems that interact with and handle the data.
Furthermore, by employing Azure Role-Based Access Control (RBAC) organizations can effectively manage access permissions and controls for both the management plane and the data plane. Proper implementation of these tools and controls guarantees Azure data security.
Microsoft Azure’s Key Management Solution
Protecting keys and secrets is incredibly important when it comes to ensuring holistic Azure data security. These keys are used to access and encrypt data and their security plays a role, in ensuring the confidentiality and integrity of that data. Microsoft Azure offers a solution called Azure Key Vault, which serves as a platform for managing cryptographic keys and secrets utilized by cloud applications and services.
Understanding Azure Key Vault
Azure Key Vault is a cloud-based service designed to streamline the management of keys while allowing organizations to maintain control over them. This service provides a platform for managing application secrets, cryptographic keys, and certificates thereby minimizing the risk of loss of crucial security information. It is important to note that Key Vault primarily focuses on application keys and secrets rather than being a repository for user passwords.
Key Features
Key Vault empowers developers with the ability to swiftly create development and testing keys within minutes which can later be migrated to production-level keys. Security administrators have control over granting or revoking access permissions as needed ensuring management with robust logging capabilities. Moreover, it also facilitates requesting and renewing Transport Layer Security (TLS) certificates offering a solution for certificate lifecycle management.
Best Practices for Using Azure Key Vault to Ensure Azure Data Security
One recommended practice is granting access, at scopes based on your requirements.
To ensure access, to a vault it is essential to grant permissions at a specific level using Azure RBAC predefined roles. For instance, if you want to give a user the ability to manage vaults you can assign them the predefined role of ‘Key Vault Contributor’ at a scope like a subscription resource group or even a particular key vault. In case the existing predefined roles don’t meet your requirements you have the flexibility to create custom roles.
Managing user access involves two interfaces; the management plane and the data plane. These interfaces operate independently when it comes to access controls. To control what users can do on the management plane utilize Azure RBAC. For granting permissions on the data plane (such as accessing or managing data) leverage vault access policies.
When it comes to storing certificates in a vault it’s crucial because certificates hold value and their unauthorized access can jeopardize your application or even Azure’s advanced data security. Azure Resource Manager offers a way of deploying certificates stored in Azure Key Vault onto Azure VMs during deployment. By managing all your certificates in one location like Azure Key Vault and configuring access policies you can maintain control, over who can access them.
Inadvertent or malicious deletion of vaults or their objects can occur sometimes. Therefore it is essential to have mechanisms in place for recovering deleted vaults or objects securely. Make sure to activate the purge protection functionalities, in Key Vault especially for the keys used for encrypting data that is stored. This way if necessary you will be able to restore any deleted vaults or objects, within the vault.
How to effectively Secure Workstations
Using access workstations or privileged access workstations is extremely important, in safeguarding accounts, tasks, and data. The majority of cyber attacks tend to focus on targeting end users making the endpoint a prominent point of attack. When an attacker successfully compromises the endpoint they can exploit the users’ credentials to gain access to an organization’s data. Most endpoint attacks exploit the fact that users typically have privileges on their workstations.
Recommended Practices for Utilizing Secure Management Workstations
Utilize a Privileged Access Workstation
A privileged access workstation offers an operating system with security controls specifically designed for handling sensitive tasks. This effectively reduces the attack surface on workstations utilized for activities like administering cloud environments managing security measures or handling data.
Ensure Endpoint Protection
Implement security policies across all devices utilized for accessing data regardless of whether it’s stored in the cloud or on premises. Employ endpoint protection solutions that provide features such as antivirus programs, anti-malware tools, and other capabilities for enhanced threat detection.
Restrict Administrative Privileges
Limit user access, by restricting privileges on their workstations. Doing it mitigates the risk of an attacker gaining control over an organization’s network if a user’s workstation gets compromised.
Implementing Multi-Factor Authentication (MFA)
It is important to require forms of authentication before granting access, to systems or data. This additional layer of security helps enhance protection in situations where a user’s credentials may have been compromised.
How can Data Encryption help?
Ensuring the encryption of data both when it’s stored and during transmission is an element of any strategy to protect information. It does not help maintain the privacy and compliance of data. Also safeguards it against unauthorized access and breaches ensuring Azure data security.
Protecting Data, at Rest
Data at rest refers to all types of information that exist on media like optical disks in a static state. Encrypting data at rest is a measure for ensuring data privacy, compliance, and sovereignty.
Implement Disk Encryption
Utilize Azure Disk Encryption for Linux or Windows VMs. This feature incorporates industry encryption tools like Linux dm-crypt or Windows BitLocker to encrypt both the operating system and data disks.
Mitigate Risks with Encryption
Always encrypt your drives before storing information on them. Organizations that fail to enforce data encryption are more vulnerable to issues regarding the confidentiality of their data. Unauthorized individuals or malicious users may exploit compromised accounts. Gain access to unencrypted data.
Centralize Key Management
Employ Azure Key Vault as a centralized solution, for managing keys used in accessing and encrypting your data. By storing application secrets in vaults you reduce the risk of losing important security information.
Securing Data During Transfer
When we talk about data, in transit we’re referring to the data that is being transferred between components, locations, or programs. This could include transmission over a network through a service bus or during input/output processes. It’s crucial to protect this data while it’s in transit to prevent attacks like man-in-the-middle scenarios, eavesdropping, or session hijacking.
Utilize SSL/TLS Protocols
It is always recommended to use SSL/TLS protocols when exchanging data across locations. This ensures that the data is encrypted throughout its transmission improving Azure data security services.
Ensure Secure Access with a VPN
When transferring data between your on-premises infrastructure and Azure it’s important to implement security measures such as HTTPS or VPN. Azure VPN Gateway provides an option for establishing encrypted communication between an Azure network and an on-premises location using the internet.
Implement Application-Level Data Encryption
Even if you have a high-speed WAN link like ExpressRoute in place it’s still advisable to encrypt the data at the application level using SSL/TLS or other reliable protocols, for assuring Azure data security.
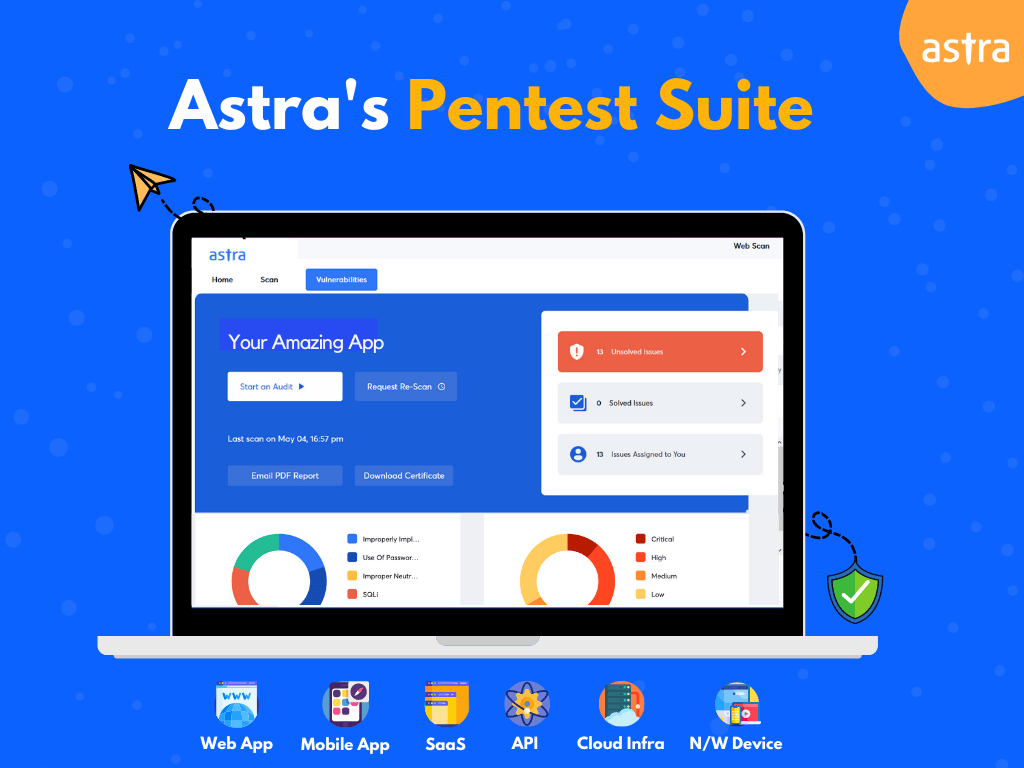
How can Astra Security help you improve your Azure data security?
Astra Security is a company dedicated to web security, offering continuous Azure data security services designed to swiftly and efficiently evaluate internet-facing assets to identify potential vulnerabilities.
Their extensive test cases, exhaustive reports, dynamic dashboard, and proactive approach to security with 24/7 human support make them a leading choice to help you secure your data.
Conclusion
Data breaches and cyberattacks have become quite common nowadays. Prioritizing data security at all stages is of utmost importance. We discussed some best practices, implementing which, organizations do not just secure their data but also meet compliance requirements and build trust with their customers and partners. Azure offers a variety of tools that can assist organizations in protecting their data in the cloud. One recommended approach, as discussed earlier, is using Key Vault to manage encryption keys. Another offering – Azure Information Protection can be utilized to safeguard emails and documents.
The responsibility for ensuring the security of your data ultimately lies with you. While Azure provides the tools it is up to each organization to put them into action. This includes updating security policies monitoring access and usage patterns and providing training on proper practices to employees. Always remember that, in the realm of Azure’s data security remaining vigilant is absolutely crucial.
FAQs
What security does Azure provide?
Azure provides a range of security options and tools, including web application firewalls, antimalware, and multi-factor authentication, to create secure solutions. Azure also offers built-in security controls and services, such as Azure Firewall and DDoS protection, to protect against evolving threats.