What is Magento Hacked Redirect?
Magento hacked redirect in simple terms is a small code added to a Magento website in order to redirect the users to one or more target websites. This is usually done for the purpose of generating advertising impressions. But, it can also result in losing financial details, personal information and so on.
You might find if your website is hacked with the help of symptoms such as the presence of malicious code in header or footer of the website, a sudden decrease in traffic as Google might be displaying a warning message to visitors, warning message in Google Search Console and many more.
It is not uncommon for a hacked Magento website to redirect its users to spam or adult sites. These hacks can result in losing your customers, cause a lot of damage to brand identity, and affect your site’s SEO rankings.
Magento Hacked Redirect? Drop us a message on the chat widget and we’d be happy to help you. Fix my Magento website now.
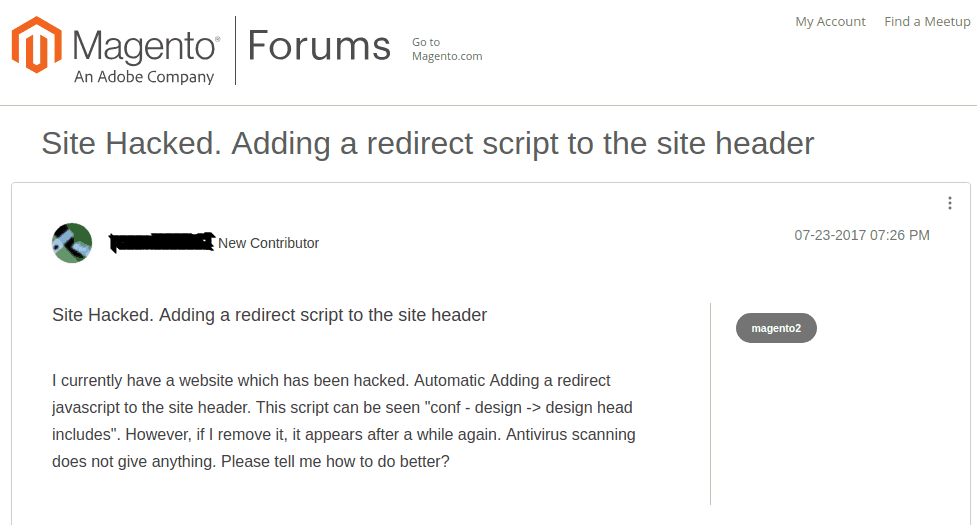
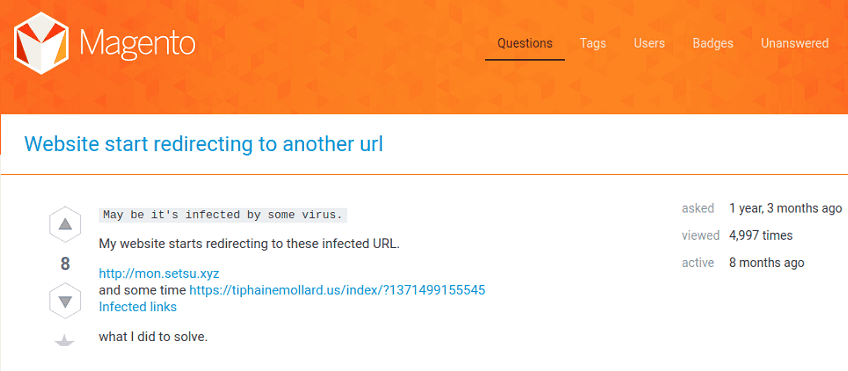
Magento Malware Redirect Examples
We wanted to see how many people are troubled by this Magento hacked redirect problem, we searched the popular forums. Here are a few examples that we found on Magento Forums and StackExchange.
Effect of Magento Redirection Spam
- Redirecting to spam websites like porn, advertisement or fake customer care support.
- Magento’s store getting redirect from Google search. Hackers do this to make search bots seeing spam sites from the search results. This can result in affecting your store SEO & getting blacklisted
- Sometimes hackers limit the redirection effect to mobile or laptop devices or to certain geographies so that people don’t recognize any malware attack or hack symptoms easily
- More infected files in the server which can give the control to add or delete user data, stealing of financial information and so on.
- Error messages in webmaster tools. Webmaster tools never lie and it will show problems such as 404 errors, crawl errors, log file crashes, server errors, malware infection errors and many more.
- Negative impact on SEO. The main causes of this are – increase in bounce rate due to redirecting to spam websites, decrease in average time spent on the website.
- Loss of customers and sales. Redirection to spam websites will eventually make customers leave thereby impacting sales.
- Ads Suspended by Adwords.
How to Fix Magento store redirecting
- Check Core File Integrity
Recently modified files could also come under the hack. Therefore the whole Magento file system should be examined for malware.
Magento Hacked Redirect? Drop us a message on the chat widget and we’d be happy to help you. Fix my Magento website now.
All Magento 1.x and 2.x versions are available on GitHub. Magento can be downloaded locally using SSH terminal. The following example uses Magento 2.1.3 for uncontaminated files and public_html for the location of Magento installation on the server.
Use the following SSH commands to check the integrity of the core files.
$ mkdir magento-2.1.3
$ cd magento-2.1.3
$ wget https://github.com/magento/magento2/archive/2.1.3.tar.gz
$ tar -zxvf 2.1.3.tar.gz
$ diff -r 2.1.3 ./public_html
The comparison between the clean Magento files and your installation will be done by final diff command. Added additional modules will also be included in the output and comparison with already known uncontaminated files in the same method is possible.
You have to check the integrity of the Magento core files. But, be cautious not to remove modules or patches that are false positive flagged. Make a note that most online free tool only checks the important folders. To have a thorough check, continue the below-mentioned steps.
To manually check the files that are recently modified.
- First, log into your Magento web server.
- If you are using SSH, you can get the list of all the modified files in the last 15 days using the following command.
$ find ./ -type f -mtime -15
- If you are using SFTP, check the last modified date column for files on the server.
- Make a note of all the files that are recently modified.
Check the recent files that are modified in the past 7 to 30 days, that you find suspicious.
Note: It is highly recommended to use SFTP/SSH/FTPS instead of unencrypted FTP when accessing the server, to keep it more secure.
Also, malware can hide by changing the file modification date. Therefore, it is recommended to use online scanners or Magento extensions to find suspicious activities, malicious payloads and so on.
- Audit user logs
Most hackers aim to create user accounts on the hacked Magento sites. So, check all Magento user accounts and give more importance to administrators.
Steps to check malicious users in Magento
- Log in to your Magento admin panel.
- Click System on the menu item and select Users or All Users under Permissions.
- Check the whole list and double check any abnormal or recent ID number.
- Delete any suspicious user accounts which you think have been created by hackers.
Magento website facing malicious redirects? Drop us a message on the chat widget and we’d be happy to help you. Fix my Magento website now.
If you can handle parsing your server logs, then you can try searching for requests to the administrator area. If you find any account which has logged in from different time zones and geographic areas, chances are higher for them to be hacked accounts. Astra provide admin login notification
-
Check for reports
You can check if Google or other security authorities have blacklisted your website by using the respective diagnostic tools.
Steps to check Google Transparency Report for your website
- Go to the Safe Browsing Site Status website
- Enter the URL of your site and click the search button
- You can check
- Site Safety details – information related to spam, malicious redirects, and downloads.
- Testing Details – details of the recent Google scan date along with detected malware.
It is recommended to check if your customers have reported any fraudulent activities after purchasing from your website. It can be useful in indicating if your site has malware that steals credit card data.
How to Keep your Magento Store Secure from Hacks in the Future?
Fixing an infected site does not make it secure from future attacks. The vulnerabilities that the hacker used to inject malware into your site has to be found and fixed. Go to this blog post to learn how to prevent Magento malware injection. Here are some steps that you have to follow to shield your site from future hacks.
- Install a Web Application Firewall(WAF): WAF will filter out hackers, malware and bots. A WAF works like a gatekeeper and checks all the incoming traffic to the website and takes the required action if the necessity arises. There are plenty of advantages of using WAF, important ones are:
Request filtering – It monitors all incoming and outgoing HTTP requests and makes sure that only the “good traffic” reaches the server.
Malware scanning for uploads – Most e-commerce websites allow customers to upload bills and other images for various purposes. Hackers see this as an opportunity to upload malicious scripts and files. This WAF shields the website from these attacks.
Blocking harmful bots – Harmful bots infiltrate website and cause huge damage through content scraping, spamming forums with ads and so on. This can be put to an end by using a powerful WAF.
- Performing a Magento security audit is crucial as it may reveal potential dangers that you had no clue in the first place. Security audits should be carried out at regular intervals or when suspicious activities are noted, to ensure that your site is safe. At any given point, It is a wise decision to stay protected with the right tools than taking measures once the damage is done.
Keeping all this in mind, Astra has developed advanced security audit systems that will protect you from all security-related problems.
Other
- Remove all unused admin accounts
- Change all admin account passwords and make sure you use strong passwords only.
- Enable two-factor authentication using Google Authenticator to have an additional layer of security.
- Install all required patches and update your Magento to the latest version. Not a developer? Get help from Codilar.
- Use Magento cybersecurity tools to keep your online store secure.
- Finally, configure your site with brute force protection.
Astra Security Suite is highly tailored for Magento stores and gives you a 360-degree protection for attacks like SQL Injection, Credit Card hack, Malware Injection, XSS, CSRF, LFI, RFI, Bad Bots, and 100+ attacks.
Take an Astra DEMO now!
















