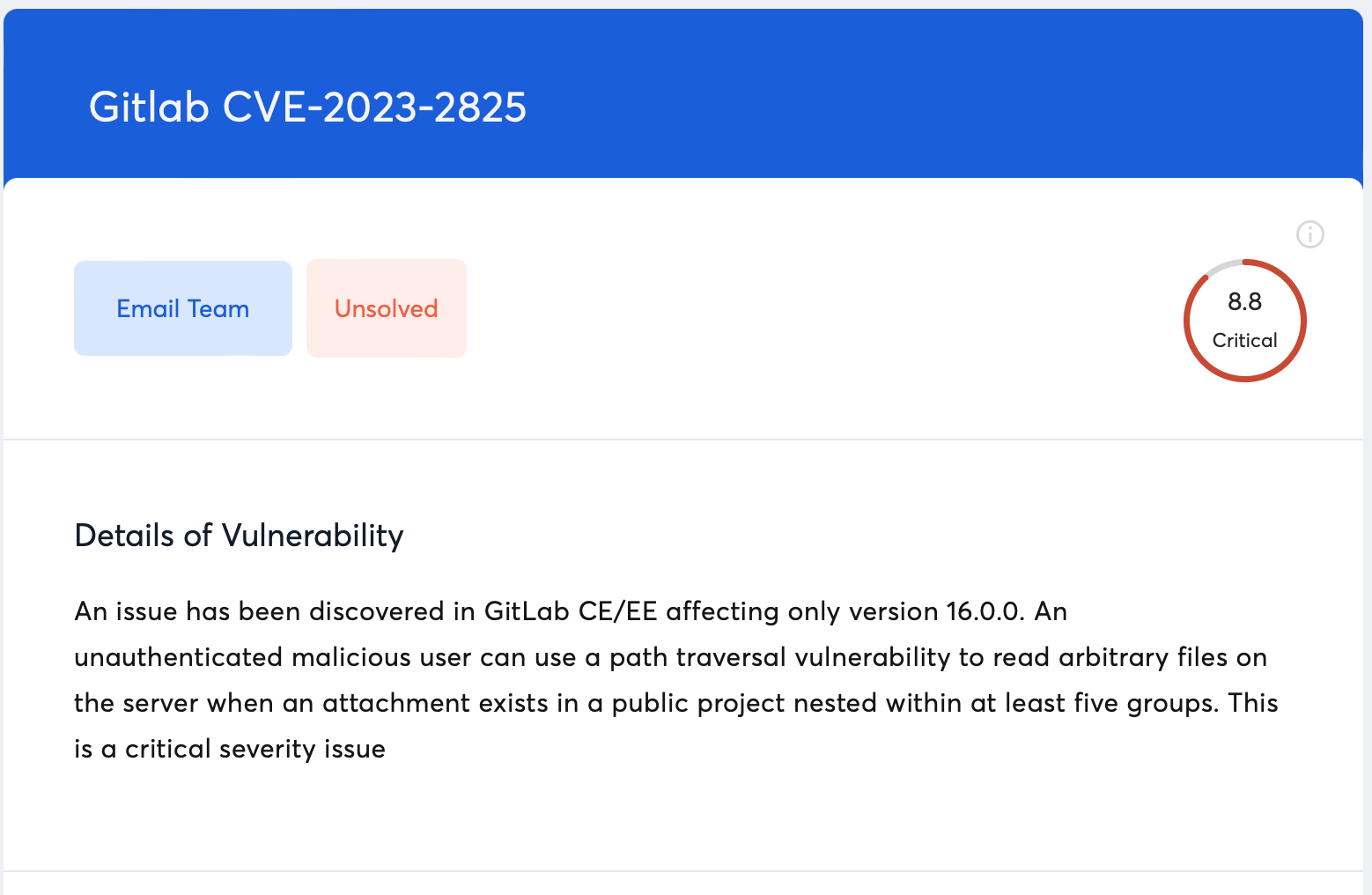
CVE-2023-2825 vulnerability is a recently discovered vulnerability in GitLab. It allows unauthorized access to GitLab repositories to read arbitrary files. This post will discuss further details of the vulnerability, its location, discovery, and how the Astra scanner scans for it.
About CVE-2023-2825
CVE-2023-2825 is a path-traversal vulnerability newly discovered in GitLab v16.0.0. The vulnerability has a maximum severity with a CVSS score of 10. Its impact is limited to GitLab’s Community and Enterprise Edition version 16.0.0 with no impact on previous versions.
More information about the vulnerability was not disclosed owing to the newness of the discovery and the severity of the problem. Upon discovery, GitLab immediately stressed the importance of applying the ad-hoc released security version 16.0.1 for GitLab Community Edition and Enterprise Edition.
Possible Impact From Exploiting CVE-2023-2825
The exploitation of the vulnerability could lead to the exposure of sensitive data, and proprietary codes for software, among other private information. The issue arose due to the way GitLab manages the paths for attachments stored within several levels.
What Is A Path Traversal Vulnerability?
A path traversal vulnerability is a flaw that allows malicious attackers to access files that they have no authorization to access. It allows attackers to trick the system and move to other files within the repository that should be off-limits for them.
With such a vulnerability, attackers can use manipulate the file path by using special sequences to jump out of their intended destination within the repository to areas that are unauthorized.
When Was CVE-2023-2825 Discovered?
The vulnerability was reported on 24th May 2023 to the project’s bug bounty program by a security researcher known as “pwnie”. Based on this GitLab released an emergency security update for the affected version 16.0.0. as 16.0.1.
Astra Scanner Scans For GitHub CVE-2023-2825
Steps To Take To Mitigate CVE-2023-2825
- Use vulnerability scanners such as the Astra vulnerability scanner to detect the usage of the affected version 16.0.0.
- Update the affected version to the latest ad-hoc security version released by GitLab 16.0.1.
Bottom Line
GitLab, being a code repository for more than 30 million registered and 1 million paying users, a vulnerability such as the one CVE-2023-2825 can prove to be fatal in its exploitation since attackers would be able to steal everything from software code to user creds, tokens, files and more. Therefore swift action must be taken in the detection and appropriate resolution by applying the update released by GtiLab.