A vulnerability report is a document provided by security testers after the assessment of a target’s security. It contains a detailed analysis of the vulnerabilities uncovered along with the test cases run during the assessment. The report also provides possible remedial steps.
One of the major criteria often looked for when choosing a security assessment service is a good vulnerability report. Well-written vulnerability reports are vital for vulnerability management, this article will tell you all about the components of a good report as well as provide you with a vulnerability report template.
Components of A Security Vulnerability Report
A well-structured vulnerability report gives the reader a thorough understanding of the shortcomings in their asset security by listing out the vulnerabilities in detail. This section explains the crucial components of a security vulnerability report that should not be overlooked.
Executive Summary
This section provides an overview of the vulnerability situation without going deep into the details. It establishes the purpose and scope of testing. The vulnerability report will also have graphical representations of the vulnerabilities found based on their nature and severity.
Scoping Overview
The scope refers to a broad description of what is included in a project or the scope of a contract. The scope given in the vulnerability report is based on the agreed-upon terms for scanning and the assets that needed to be scanned. Thorough scoping is crucial to avoid any legal trouble and also to ensure an exhaustive vulnerability assessment of the agreed-upon assets.
List of Vulnerabilities
The section is followed by a brief list of vulnerabilities where the CVSS score of each vulnerability along with their severity level categorization in terms of low, medium, high, and critical severity. It also shows their current remediation status.
Individual Vulnerability Information
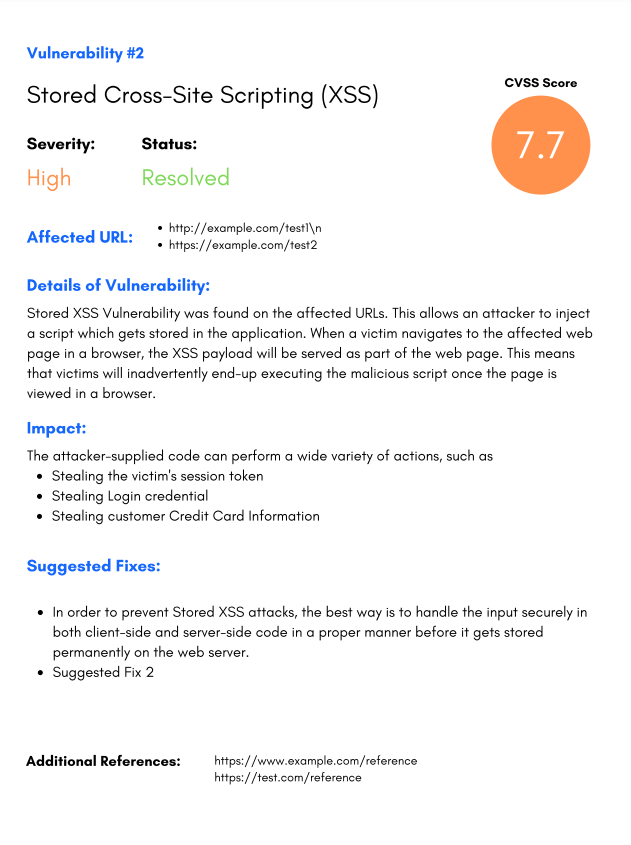
This is where things start getting pretty technical. In this part, each vulnerability is explained. Every specific vulnerability and its impact on their website and business, its status, and CVSS score should be mentioned. It should also include suggestions to fix the issue.
Remediation Measures
Individual vulnerability information is followed by recommendations for remediation. This may be just a one-line comment or a detailed step-by-step guide to reproduce and solve the issue.
POC videos can also be provided for more difficult vulnerabilities so that companies can reproduce and remediate the vulnerabilities with further ease.
Vulnerability Scan Test Cases
Hundreds of test cases are documented along with their category, typical severity, scan type, etc. The test cases are different for web apps, android apps, iOS apps, and blockchain-based apps.
Vulnerability Assessment Process in Brief
Vulnerability assessments or scanning are divided into the following steps:
1. Setting the Scope
The first step is to determine the scope of the vulnerability assessment which is based on the assets that the organization wants to scan for vulnerabilities. The scope of the scan helps you decide whether to use an application scanner, network scanner, or host-based scanner.
2. Vulnerability Scanning
The second step is carrying out a vulnerability scan. An automated scanner can be used to scan for common vulnerabilities based on a vulnerability database.
3. Vulnerability Analysis
The vulnerabilities found during the vulnerability scans are identified and analyzed based on their risk level for prioritization during remediation.
4. Vulnerability Report
Then comes the vulnerability report. It documents the vulnerabilities that were found during the scan along with their CVSS score. It also suggests necessary steps to fix a certain vulnerability.
5. Vulnerability Remediation
Once vulnerability reporting is complete and submitted, it is time for vulnerability remediation. Based on the vulnerability report given, companies assign the vulnerabilities to the developers in their company, who follow the suggestions in the report and consult security experts if need be, to fix the issues detected.
What To Look For In A Strong Security Vulnerability Report?
Here are some tips to strengthen one’s assessment vulnerability report.
Prioritization of Vulnerabilities
A hallmark of a good vulnerability report lies in whether it prioritizes the list of vulnerabilities based on how much risk they pose to the customer’s IT environment. This makes it easier for an organization to pick the vulnerabilities that are most critical to its cybersecurity and resolve them with ease.
Concise Writing
Another thing to make note of for a good vulnerability report is the writing style. Make sure the writing is concise, and well-explained but to the point. Reports that are drawn out and long make it tedious for organizations to follow and understand.
Clear Summary
The start of the report should have a brief summary that provides an overview of the vulnerability, including its severity and potential impact. This summary should not go into detail and or be too technical, rather it should be simple and easy for the reader to understand.
Solid Suggestions
Add recommendations for how the vulnerability can be mitigated or fixed, including any patches or updates that may be required.
Solid, actionable suggestions are often overlooked by most assessment service providers. But they are crucial and can define an organization’s outlook on security and shape its security strategies.
Vulnerability Report Example
This section comes with a prime vulnerability report example provided by Astra Security. This vulnerability report template can be followed by all professional security testers and also organizations looking for vulnerability reporting samples.
Importance Of Understanding The Customer
When generating a vulnerability report after an assessment, scan, or pentest, it is important to keep in mind that the report should be uniquely tailored for the customer’s ease of understanding.
For example, a report could have multiple audiences with different expertise. It is on the security testing provider to understand and customize the report accordingly. If the report is to be submitted to a CXO it would likely have to be non-technical and brief
If it’s for the IT team involved in fixing the vulnerabilities, explain the security strategies, and apt remediation measures that could be adopted to strengthen their cyber defenses.
Lastly, the report could be to meet compliance requirements during audits, in which case it is better for the report to be non-technical with the vulnerabilities listed down along with their severity level and remediation status.
Let us check out some of the other reasons why it is important to keep the reader in mind while creating the vulnerability report.
- For Efficient Vulnerability Prioritization
A vulnerability report can only be effective when vulnerabilities are listed down based on the severity of the threat it poses to the organization in question. Vulnerabilities that pose the highest risk should be mentioned first followed by those that range from medium to low in severity.
- To Act on Actionable Recommendations
The report provided to technical experts who are involved in vulnerability management and remediation should be given actionable recommendations to mitigate the vulnerabilities detected during the scans.
- For Effective Communication
Effective communication is only possible when one understands who they’re trying to reach with their information. In the case of a vulnerability report, it is important for you to analyze whether this is for CXO, the technical team, or auditors looking for documentation.
- To Nurture Trust
Understanding your customer’s vulnerability report requirements not only helps them but also helps you. A good vulnerability report that is customized according to the needs of the target boosts the reliability of your organization and the commitment to the security testing services provided by you.
Benefits of Vulnerability Reporting For Business
Vulnerability reporting aids an organization and its active endeavor to maintain proper security. Here are the ways vulnerability reports provide value to a company’s cyber security.
Helps Maintain Compliance
The country of operation of an organization decided the benchmarks you’d have to follow and adhere to. For instance, businesses operating in the European Union countries must abide by the GDPR or General Data Protection Regulations.
Similarly, businesses that collect and/or process payment card data must comply with the PCI-DSS regulations. A vulnerability report plays a significant part in making your compliance ready.
Build Trust
The vulnerability report has a vital relationship with trust. An actionable vulnerability report prompts you to action and helps you prioritize fixes and secure your website. Once you have done that, a rescan confirms that you are truly secure, and a certificate is assigned.
A thorough vulnerability report also showcases your steadfast and proactive nature in securing assets and data. Hence, it helps you boost trust and build a reputation.
Provides Comprehensive Evaluation
Vulnerability reports can provide you with a comprehensive evaluation profile of your network, applications, or website. For the higher management, a vulnerability report acts as a single piece of document that they need to act upon and tackle the business risks to manage cybersecurity, any inlying vulnerabilities, and the overall IT environment.
Proper Documentation
Vulnerability reports for websites, networks, cloud, APIs, or mobile applications all help with continuous monitoring and documentation of the security status of an organization’s assets. This in turn helps with compliance audits as well as developing and implementing better security strategies for your assets.
Challenges Of Vulnerability Reports
Creating vulnerability reports that are apt for the organizations comes with its own set of challenges which will be discussed below:
Identification of Vulnerabilities
Identification of vulnerabilities using automated scanners can result in false positives and false negatives, which if included in the report would bring down its quality. Therefore it is important to vet the findings and vulnerabilities thoroughly by a security expert before its put on the report.
Accurate Description of Vulnerability
Another challenging area in vulnerability reporting is getting the description and impact of the vulnerability accurately in the report. It is important to make sure that potential impact and mitigation strategies be well explained.
Communication with Stakeholders
Vulnerability reports often require communication with multiple stakeholders, such as developers, IT staff, and management. Effectively communicating the severity and urgency of the vulnerability to each stakeholder can be a challenge in this scenario.
Prioritization of vulnerabilities
Vulnerability reports identify numerous vulnerabilities thus making it a challenge to prioritize them according to which needs to be addressed first. This requires an understanding of the potential impact of each vulnerability on the organization.
Remediation Follow-up
Upon submission of the vulnerability report, it is vital to ensure that the listed vulnerabilities are addressed, resolved, and patched in a timely manner. Critical vulnerabilities need to be addressed immediately while flaws with low severity can be addressed with time. This requires ongoing communication with stakeholders and vendors to ensure that the necessary actions are taken.
Conclusion
Vulnerability reports are multi-faceted handy documents that help organizations understand the flaws and vulnerabilities in their security system. It also aids organizations in the documentation process for audits and maintaining compliance.
This article has discussed major aspects of vulnerability including components of one, tips on how to make your vulnerability stronger as well the benefits and challenges of providing a vulnerability report.
FAQs
Do I also get rescans after a vulnerability is fixed?
Based on the plan you get 1-3 rescans which can be availed within 30 days of the initial completion of the assessment.
How Astra helps you get a vulnerability report?
Astra Security has an interactive and collaborative reporting procedure. Not only do you get a detailed PDF report along with video POCs on how to reproduce vulnerabilities, but you also get expert assistance from security engineers at Astra while working on the issues.
















