You are Here: Vulnerability Scanning >> NIST 800-171 Vulnerability Scanning
NIST vulnerability scanning is a procedure that involves a methodical examination of an organization’s IT infrastructure, applications, and devices. It utilizes specialized software tools to find security risks and incorrect setups that attackers could use. It is an overarching cybersecurity strategy that identifies, protects, detects, responds, and recovers your digital infrastructure.
Vulnerability Scanning vs Penetration Testing
Vulnerability scanning and penetration testing are similar but have minor differences. Penetration testing simulates actual attacks to evaluate the efficiency of security controls and identify exploitable vulnerabilities, while vulnerability scanning uses non-invasive methods to identify flaws.
Benefits of NIST Vulnerability Scanning for Organizations
Vulnerability scanning offers various benefits if conducted properly. Let’s discuss some of them.
- Early detection: Vulnerability scanning finds possible security gaps before malicious entities take advantage of them.
- Cost-Effectiveness: Compared to manual assessments, automated vulnerability scanning technologies are more affordable and considerably cut down review time.
- Compliance: Vulnerability assessments are necessary to maintain compliance with industry rules and regulations, such as PCI DSS, HIPAA, and many more.
NIST Control Vulnerability Scanning Guidelines
The NIST has issued an extensive set of principles and guidelines designed to aid organizations in managing cybersecurity vulnerabilities effectively, which is summarized within their Cybersecurity Framework publication series as well as two special publications from NIST.
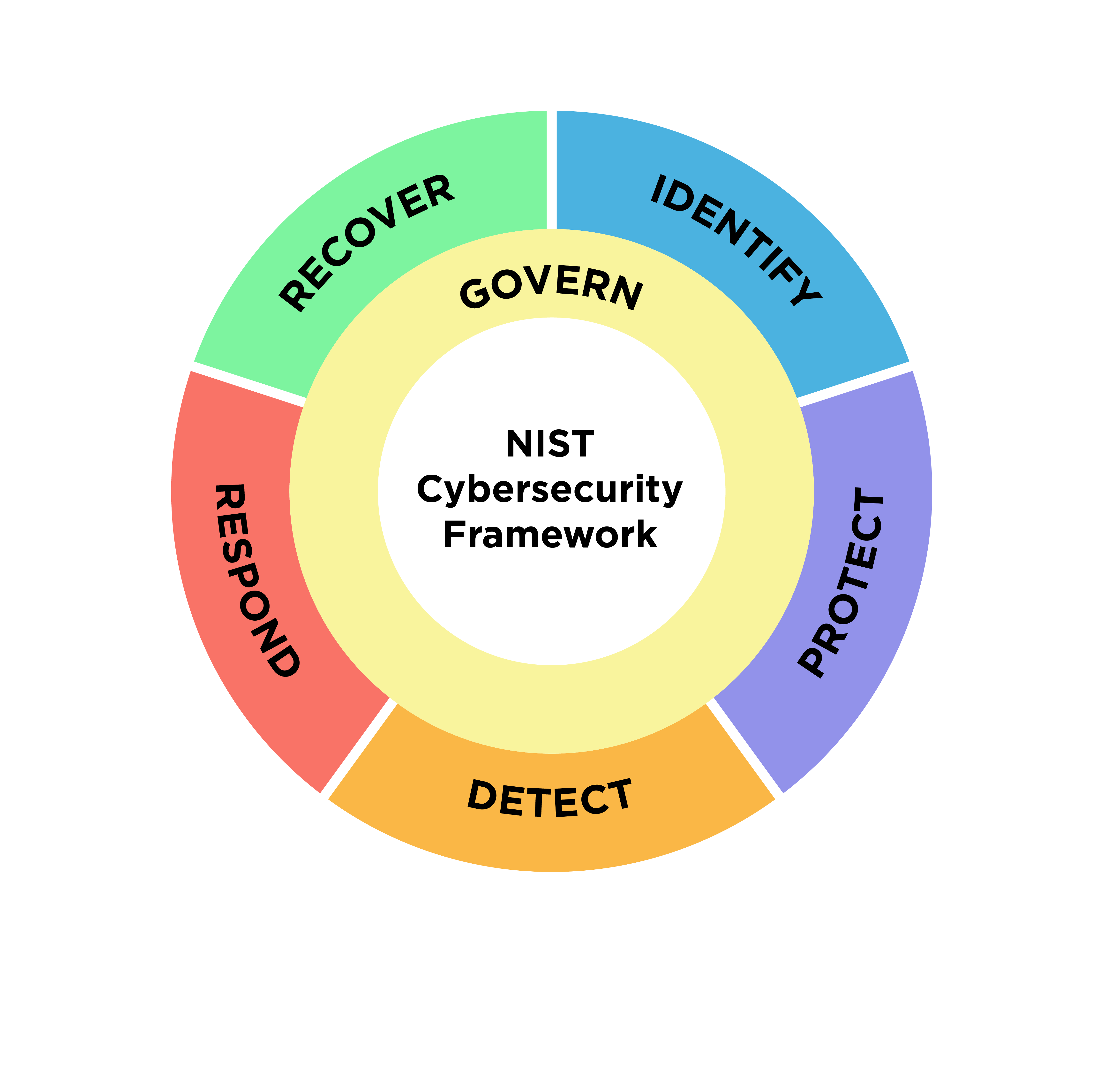
- NIST Cybersecurity Framework: Focuses on five core functions – Identity, Protect, Detect, Respond, and Recover. Vulnerability scanning plays an integral part in both of these areas of cyber security – it identifies weaknesses quickly so fixes can be implemented immediately.
- NIST Special Publication 800-40: A Guide to Enterprise Patch Management is an indispensable resource for developing an effective patch management plan and keeping systems current with security updates, thus decreasing vulnerabilities.
- NIST SP 800-115: Technical Guide for Information Security Testing and Assessment provides in-depth technical insights into testing and assessment practices and best practices for vulnerability scanning.
By including these guidelines in their risk management strategies, organizations can gain a comprehensive view of their security posture, identify threats effectively and allocate sufficient resources toward mitigating risks.
Implementing NIST 800-53 Vulnerability Scanning Best Practices
Let’s delve deeper into these vital components to building a strong cybersecurity defense.
Identifying Assets and Critical Systems
Prioritizing essential assets like databases, servers, and network devices is necessary for organizations before they start NIST vulnerability scan. This makes sure that scanning efforts are concentrated on the most crucial infrastructure components.
Choosing the Right NIST Vulnerability Scanning Tools
For accurate and thorough evaluations, it’s crucial to use the right NIST vulnerability scanning tools. NIST advises assessing tools according to their capabilities, coverage, and suitability for the company’s IT infrastructure.
Configuring Scans and Setting Scanning Parameters
To achieve accurate results, scan configuration and definition must be done correctly. Organizations should customize scans depending on their own requirements, including the frequency of scans, operating hours, and level of evaluation.
Scanning Frequency and Timing Considerations
The organization’s risk appetite, the number of system updates, and the threat landscape all have a role in determining how frequently vulnerabilities are scanned. Ad-hoc scans performed after substantial changes, together with routine scans, help maintain a strong security posture.
Interpreting NIST 800-171 Vulnerability Scanning Control Results
Understanding NIST vulnerability scanning results is vital in recognizing risks in your system. Here’s an introduction to its core components.
- Severity Levels: Vulnerabilities are typically graded on their severity levels from low to critical; understanding this helps prioritize fixes.
- Type of Vulnerabilities: Assigning vulnerabilities such as unauthorized access or data leakage into categories helps organizations determine an efficient strategy to combat them.
- Identification of Affected Components: Determining which systems, applications, or files have been affected is helpful when taking further actions to address them.
- Recommendations for Actions: Many scanners provide guidance for remediation or mitigation, which is key for quick resolution, so adhering to those instructions could ensure prompt results and resolution.
- False Positives: Scanners may falsely identify vulnerabilities as risks; careful evaluation will allow us to accurately detect and assess each one appropriately.
- Compliance Considerations: Depending on regulatory requirements, specific vulnerabilities may require immediate actions in order to stay compliant and ensure continued compliance.
Deciphering vulnerability scanning results is more than simply fixing immediate issues; it also serves to deepen comprehension of the larger security landscape so as to enable informed decisions, prioritize activities, and develop comprehensive cybersecurity policy.
Best Practices for NIST Vulnerability Scanning
Patch Management Strategies
Patch management strategies refer to the approach taken by organizations for overseeing updates and fixes for software applications and technologies.
Reducing the attack surface and eliminating known vulnerabilities need an efficient patch management technique. Establishing a procedure for quickly updating security updates on all pertinent systems and applications is important for organizations.
As part of its patch management strategy, an enterprise might conduct regular automated checks for available updates, prioritize patches based on severity, and schedule timely implementation across devices and platforms.
System Hardening and Configuration Management
System hardening involves securing device and application configuration to reduce attack vectors. Organizations can decrease the possibility of vulnerabilities arising from misconfigurations by placing strong configuration management practices in place.
Network Segmentation and Access Controls
Attackers’ ability to travel laterally is restricted by network segmentation and access constraints. To manage possible dangers and limit unauthorized access, NIST advises creating robust network segmentation.
Employee Training and Awareness Programs
Human mistake continues to be a major contributor to security issues. Employee training on potential threats, safe conduct, and the significance of reporting security events may greatly improve an organization’s security posture.
Continuous Monitoring and Improvement: Key Aspects and Enhancements of NIST Vulnerability Scanning
In the dynamic landscape of cybersecurity, continuous monitoring is important. This process not only helps detect vulnerabilities promptly but also offers real-time insights about the security health of an organization’s IT infrastructure.
Due to the constant evolution of cyber threats, NIST vulnerability scanning should involve tracking irregularities, inspecting intrusion detection systems, and routinely checking firewall logs. These actions can help organizations respond swiftly to potential threats, thereby limiting the potential damage.
Tracking and Managing Changes in the IT Environment
Active management of changes in the IT environment is critical to ensuring an up-to-date asset inventory and understanding the impact of such altercations in the organization’s security posture. These changes could range from deploying new software applications and altering network configurations to adding new hardware devices.
Regular documentation and evaluation of these changes are essential. This practice aids in the accurate mapping of digital assets, understanding the overall system’s interdependencies, and anticipating potential security implications.
Regular Vulnerability Assessments and Updates
With cyber threats constantly emerging, organizations should conduct regular vulnerability assessments. This requires reviewing their procedures and tools as well as updating them when necessary in order to detect and mitigate new NIST vulnerability scanning types efficiently.
- Approach Security Proactively: Adopting a proactive cybersecurity approach means taking measures to anticipate and respond to threats before they cause harm, using threat intelligence and predictive analyses for prevention measures that increase the resilience of security infrastructures.
- Establish Adequate Incident Response Mechanisms: Even after stringent security measures have been put into effect, incidents still arise that require rapid responses. Therefore, having well-delineated incident response mechanisms in place is paramount – having a protocol in place must outline all steps taken to identify, contain, eradicate, and recover from security incidents as soon as they emerge – regular testing and updating ensure this protocol stays efficient in dealing with potential incidents quickly and swiftly.
- Integrating Security Tools and Practices: Integrating various security tools and practices can significantly strengthen an organization’s security posture by unifying various security systems, streamlining information flow, increasing threat detection/mitigation efforts more accurately, mitigating potential breaches more swiftly, as well as regular audits that assess their effectiveness as well as uncover any opportunities for improvement.
NIST’s Role in Enhancing Cybersecurity Through NIST Vulnerability Scanning
NIST provides organizations with recommendations and publications designed to facilitate vulnerability assessments and risk mitigation – essential tools in improving cybersecurity posture and protecting critical assets.
- Security Resilience Improvement: Regular vulnerability scanning increases an organization’s capacity to detect and respond quickly to potential threats, providing them with a more robust cyber defense posture by anticipating cyber risks.
- Compliance Requirements: Cybersecurity laws and compliance requirements vary across various sectors. Adherence to NIST recommendations for vulnerability scanning can assist businesses with adhering to regulations, avoiding penalties, and protecting their reputations.
- Cost-Effectiveness: NIST reduces IT professionals’ workload while making efficient use of resources; its automated vulnerability scanning procedures reduce labor costs by saving both time and effort for businesses.
- Data Security and Customer Trust: By actively addressing vulnerabilities, organizations demonstrate their dedication to safeguarding sensitive data while upholding stakeholder and customer confidence.
- Incident Prevention: Vulnerability scanning helps avoid potential security incidents before they take place, helping avoid downtime, data breaches, and attendant costs in terms of time lost as well as reputational harm.
- Align With Cybersecurity Best Practices: NIST has long been recognized for its knowledge of cybersecurity norms. By following NIST recommendations, organizations are aligning themselves with industry best practices and guaranteeing that their cyber defenses meet global standards.
Automated Tools for NIST Vulnerability Scanning: A Spotlight on Astra Security
The continuous evolution of cyber threats necessitates advanced automated tools for conducting thorough vulnerability scanning. In a world where digital assets are more vulnerable than ever, businesses need a reliable solution to discover and mitigate potential security weaknesses.
Astra Security’s automated NIST vulnerability scanning tool stands out as a remarkable solution in this arena. With a database of over 5000 tests, Astra Security ensures an all-encompassing examination of an organization’s digital infrastructure, ranging from the software level to the network level.
Further, Astra Security is known for its automated scans that save time, effort, and cost, allowing organizations to allocate these resources more effectively. Advanced scanning technology can examine different components of an organization’s digital infrastructure in a thorough and efficient manner.

Why is Astra Vulnerability Scanner the Best Scanner?
- We’re the only company that combines automated & manual pentest to create a one-of-a-kind pentest platform.
- Vetted scans ensure zero false positives.
- Our intelligent vulnerability scanner emulates hacker behavior & evolves with every pentest.
- Astra’s scanner helps you shift left by integrating with your CI/CD.
- Our platform helps you uncover, manage & fix vulnerabilities in one place.
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Compliance-Friendly Pentest Certificate with Astra Security
Ensuring regulatory compliance is a significant part of vulnerability scanning, and Astra Security caters to this need in a noteworthy manner. Post-scan, Astra Security provides a comprehensive pentest certificate that is compliance-friendly, catering to standards such as the NIST, Payment Card Industry Data Security Standard (PCI DSS), and the Health Insurance Portability and Accountability Act (HIPAA).
This pentest certificate serves as a testament to an organization’s robust vulnerability scanning practices, thereby boosting stakeholder confidence. The certificate further enhances transparency and demonstrates the organization’s commitment to maintaining a strong security posture.
Conclusion
As cyber risks increase in today’s increasingly unsafe digital environment, NIST vulnerability scanning becomes essential in maintaining digital safety. NIST guidance on vulnerability scanning offer organizations a comprehensive framework that aids them in identifying, prioritizing, and mitigating vulnerabilities; by employing best practices like patch management, system hardening and network segmentation alongside NIST standards they can foster a robust security posture that not only ensures data protection and regulatory compliance but also builds trust, reduces costs and increases resilience against evolving cyber threats.
Frequently Asked Questions
What are the types of vulnerability scanners?
The three common types of vulnerability scanners: Network-based, application, and cloud vulnerability scanners. Vulnerability scanners — also known as vulnerability assessments — are automated, digital solutions specifically designed to identify vulnerabilities and gaps in an organization’s website, application, and network security systems.
What are the two main types of vulnerability scans?
The two main types of vulnerability scans are: Credentialed and non-Credentialed scans (also respectively referred to as authenticated and non-authenticated scans). Non-credentialed scans, as the name suggests, do not require credentials and do not get trusted access to the systems they are scanning.