NIST serves as an invaluable guide in cybersecurity’s dynamic landscape, offering guidelines and frameworks designed to protect institutions against cyber threats. As one of the foremost authorities on vulnerability management practices in existence today, this organization stands as a beacon of hope to IT professionals as well as business leaders alike seeking guidance for protecting information systems.
But what exactly is NIST vulnerability management, and why is it such an essential aspect of cybersecurity? At its core, vulnerability management entails the systematic process of identifying, assessing, prioritizing, and mitigating potential weaknesses within a system that may be exploited by attackers – an attempt at preemptively dealing with potential issues before they can become leveraged for cyber attacks.
In this blog, we will explore the following in more depth:
- Understanding NIST
- NIST Guidelines and Frameworks
- A detailed analysis of its process
- Common challenges faced and solutions
Why is Astra Vulnerability Scanner the Best Scanner?
- Runs 8000+ tests with weekly updated scanner rules
- Scans behind the login page
- Scan results are vetted by security experts to ensure zero false positives
- Integrates with your CI/CD tools to help you establish DevSecOps
- A dynamic vulnerability management dashboard to manage, monitor, assign, and update vulnerabilities from one place.
- Helps you stay compliant with SOC2, ISO27001, PCI-DSS, HIPAA, etc.
- Integrates with Slack and Jira for better workflow management
- Trusted by the brands you trust like Agora, Spicejet, Muthoot, Dream11, etc.

Understand NIST (National Institute of Standards and Technology)
The National Institute of Standards and Technology is commonly referred to by its acronym NIST. Founded with an eye toward increasing innovation and industrial competitiveness, this organization has quickly established itself within cybersecurity circles as an indispensable ally. NIST plays an instrumental role in championing robust security protocols not just within America but worldwide, serving government agencies, private enterprises, and academic institutions alike with trusted advisory roles across sectors and disciplines alike.
NIST goes far beyond mere guidelines and standards – it takes an active, adaptive, and proactive approach toward cybersecurity that adapts to the changing dynamics of the digital realm. Through careful preparation of frameworks, both comprehensive and flexible, NIST fosters an ecosystem that can withstand current threats while adapting to future ones. We will examine some specific frameworks curated by NIST that lead to effective vulnerability management strategies.
NIST Frameworks and Guidelines for Vulnerability Management
The NIST Cybersecurity Framework serves as a guide for entities toward creating an organized approach to managing cyber risks. Created as part of a collaboration between governments and industries, this voluntary framework offers organizations a universal language and set of NIST vulnerability management standards designed to assist with managing risk more easily across a broad spectrum of businesses and organizations – even those that specialize in it.
NIST SP 800-53: Security and Privacy Controls
NIST SP 800-53 is an indispensable guide outlining essential security and privacy controls to protect an organization’s information systems from security vulnerabilities and breaches. When seeking to maintain confidentiality, preserve integrity, and assure information availability, this NIST vulnerability management guideline can prove indispensable in maintaining these standards.
Providing tailored controls that meet individual organization requirements creates an imposing fortress of protection where vulnerabilities can be quickly identified and mitigated to unparalleled precision; additionally, privacy controls protect sensitive data against unapproved access or disclosure, ensuring all bases are covered for ultimate peace of mind.
NIST SP 800-37: Risk Management Framework
At the unprecedented speed of cyber threats, an effective risk management strategy is not simply essential but mandated. Here, the NIST 800-37 vulnerability management becomes indispensable: it offers an organized process that assists organizations in controlling risks associated with the integration of information systems while at the same time categorizing systems for segmentation purposes, selecting suitable security controls, and tracking their effectiveness on an ongoing basis – helping organizations foster a proactive risk culture ready to adapt and respond swiftly in light of ever-evolving cybersecurity threat landscape.
NIST Vulnerability Management Process
Identification: At the heart of NIST vulnerability management framework lies identification. This initial stage lays a map outlining possible cyber attack vectors by employing various tools like vulnerability scanning and asset inventories to make visible their cyber terrain – in turn helping expose potential weak points for further defense strategies to emerge and be developed against. NIST provides guidelines that guide this vigilant identification process in helping organizations create robust defensive plans against possible vulnerabilities within their information systems.
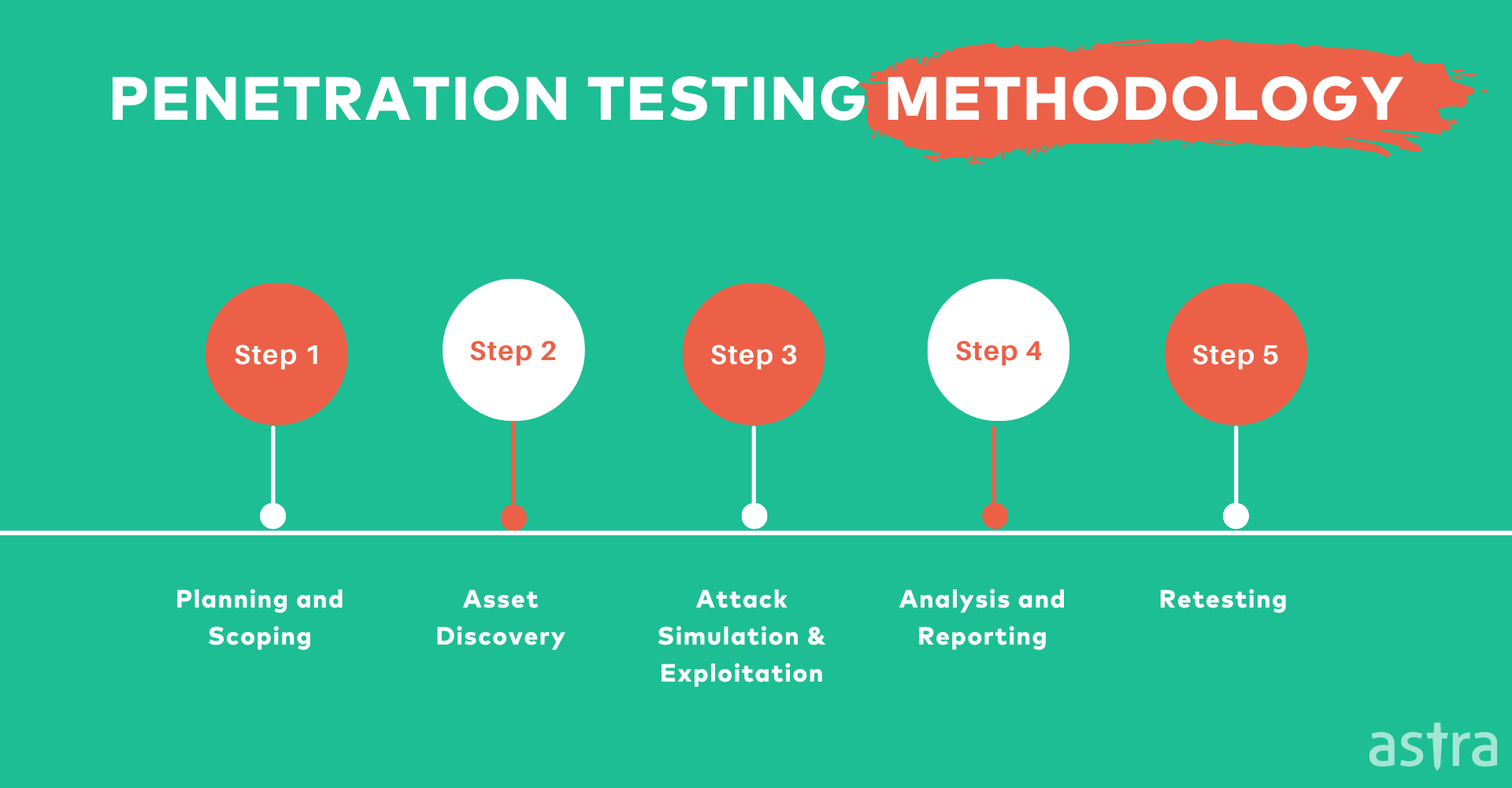
Analysis: Once vulnerabilities have been identified with NIST vulnerability scanning, analysis comes into play to investigate them more deeply and uncover any clues pointing towards potential impacts or likelihoods for each vulnerability. By drawing together information from various sources and applying risk evaluation techniques, organizations can develop comprehensive plans designed to effectively tackle their most pressing vulnerabilities with keen focus and accuracy.
Prioritization: After vulnerabilities have been assessed, the next logical step in the NIST vulnerability management process should be prioritizing them. Prioritization allows organizations to better allocate their resources by prioritizing mitigating vulnerabilities with the highest risk first and tackling those that pose the greatest danger first. NIST guidelines advocate using an organized, systematic process when prioritizing vulnerabilities to ensure efforts focus where they will have maximum effect and create hierarchies of response where efforts have the most noticeable impact.
Remediation: Moving along our journey, we reach the phase of remediation where plans become realities. Here, organizations put their plans into motion by patching identified vulnerabilities to provide protection of their system from cyber-attacks – such as by installing patches, reconfiguring system components, or strengthening security policies. NIST guidelines offer organizations a structured pathway through which to address vulnerabilities with accuracy and precision, thereby creating a secure cyber environment.
Verification: Once remediation steps have been implemented, it’s essential that organizations assess and verify the effectiveness of measures taken. Consider it quality assurance for cybersecurity initiatives: this phase includes closely monitoring systems to make sure vulnerabilities have been effectively addressed and no residual risks remain unaddressed; through continuous assessment, organizations can affirm a robust security posture ready to face an ever-evolving cyber threat landscape – this is where NIST vulnerability management guidelines prove invaluable, offering tools and techniques necessary to test resilience formed through the vulnerability management process.
Understanding Challenges and Solutions
At times in vulnerability management, organizations face unique hurdles that put their security infrastructures through rigorous trials.
A major challenge is cyber threats’ ever-evolving nature – just when organizations increase defenses against attacks from cybercriminals, new methods emerge for breaching them. In such an ever-evolving landscape, an agile yet proactive security measure update process must take place regularly so as to stay abreast with potential attackers and keep pace.
Organizations often face resource restrictions in terms of both technology and expertise; developing and implementing an extensive vulnerability management program requires significant investments as well as skilled teams navigating it successfully. But fear not! Solutions lie within NIST guidelines themselves. By adopting the systematic phased approach outlined by them, organizations can streamline processes while efficiently using resources. Furthermore, cultivating collaborations and partnerships will strengthen internal capabilities as well as bring in external expertise needed for the cybersecurity journey.
At its heart, resilience in cybersecurity begins with continuous learning and adaptation. NIST frameworks become most useful when organizations integrate them into daily operations – creating a culture of awareness and vigilance – creating an ideal defense against cyber threats by strengthening capacity-building efforts while developing security-centric organizational cultures that prioritize response agility over reactionary tendencies.
How can Astra help?
As a leading provider of penetration testing services, Astra’s Suite of security services aims to help you achieve compliance, optimize risk management, and protect your networks from internal and external threats.
With our unique combination of automated and manual pentests, accompanied by easy CI/CD integration, a CXO-friendly dashboard, and 24/7 support, we help you identify and manage vulnerabilities from start to finish.
Conclusion
As we reach the conclusion of understanding the NIST vulnerability management guidelines, it becomes evidently clear that adopting an organized and systematic approach to vulnerability management is no longer just a best practice but an absolute requirement in today’s digital era. Exploring NIST guidelines has provided us with greater appreciation and knowledge regarding all processes necessary for safeguarding an organization’s cyber borders – these adaptive structures stand as beacons pointing us toward a safer and resilient future for each entity they guide towards a secure existence.
As our expedition comes to an end, it is crucial to stress that vulnerability management is an ongoing journey that necessitates organizations adapting and evolving with changing cyber environments. NIST frameworks offer guidance that teaches organizations the art of staying ahead of threats; we should take advantage of them by adopting proactive cybersecurity approaches that prevent threats before they take root – This means being prepared is more than a good plan; it’s the only solution if cybersecurity threats emerge!
FAQs
What are NIST vulnerability management metrics?
NIST vulnerability management metrics are quantitative measures used to assess and track the effectiveness of an organization’s vulnerability management program. These metrics include factors like the number of vulnerabilities identified, their severity, the time taken to remediate them, and the overall risk reduction achieved, helping organizations prioritize and improve their security efforts.
















