With the rapid adoption of cloud computing, a monumental shift towards a complete cloud infrastructure was observed amongst the organizations. According to a study, 81% of these organizations face cloud-related issues like misconfigurations and unauthorized access in the past year.
Trends like these have made standardized guidelines for operations and security a necessity. Enter the NIST cloud security standards designed to identify threats, mitigate them, stay compliant, and guarantee overall security for cloud environments.
What is The NIST Cyber Security Framework?
The NIST (National Institute of Standards and Technology) Cyber Security Framework was introduced to help organizations manage and reduce cybersecurity risks. It does not provide specific security controls; however, they are done through special publications. It enables easy customization of cybersecurity practices based on individual company requirements.
It is designed to provide a high-level, strategic view of an organization’s cyber security posture. The NIST 800-53 is one of the most crucial and widely adapted standards of security that provides security controls with three main components:
- Core: High-level cybersecurity functions, i.e., identify, protect, detect, respond, recover.
- Implementation Tiers: Various degrees to which NIST CSF has been implemented, partial, risk-informed, repeatable, and adaptive.
- Profiles: Refers to each organization’s unique security requirements.
What Is NIST Cloud Security?
NIST establishes cloud security standards, guidelines, and best practices to secure cloud environments and manage cybersecurity risks. NIST defines cloud security as practices to protect data and the applications and infrastructure hosted in the cloud environment.
NIST standards concerning cloud security include:
- NIST SP 800 – 144: Key guidelines for maintaining security & privacy in public clouds.
- NIST SP 800 – 145: Defines cloud computing, its characteristics, and its service & deployment models.
- NIST SP 800 – 146: Cloud systems, along with when & how to use them, are explained.
- NIST SP 800 – 210: Provides access control guidance for different cloud delivery models.
Who Does NIST Cloud Security Apply To?
NIST’s frameworks, guidelines, and security controls are ideal for all companies with cloud assets. Most companies today have multiple cloud assets, such as data, applications, or both; therefore, implementing the best cloud security measures is integral.
Following NIST security controls such as NIST SP 800-53, NIST SP 800 -145, and others ensures that security measures appropriate for your cloud assets are applied for optimal protection. This usually includes risk assessments, data encryption, firewall installation, and more.
NIST Cloud Security Standards
NIST SP 800-144
Title – Guidelines on Security and Privacy in Public Cloud Computing
Purpose: This set of guidelines provides recommendations for security and privacy in public cloud environments.
NIST SP 800-144 is mainly geared toward decision-making executives, information officers, and system managers. It also includes an exhaustive list of other SP NIST publications that directly relate to cloud computing and can be used in conjunction with NIST SP 800-144.
Key Highlights:
- Planning of security and privacy components of cloud computing solutions carefully before implementation.
- Detailed knowledge and understanding of the public cloud computing platform offered by the provider.
- The public cloud computing solution should satisfy the organizational security and privacy criteria.
- Accountability over the privacy and security of applications and data in the public cloud platform should be maintained.
NIST SP 800 – 145
Title – The NIST Definition Of Cloud Computing
Purpose: This set of guidelines emphasizes a standard definition of cloud computing across industries.
NIST SP 800-145 defines cloud computing as an on-demand network that provides shared access to computing resources such as networks and applications.
Key Highlights:
- It defines five characteristics of cloud computing: on-demand, resource pooling, broad network access, rapid elasticity, and measured service.
- It defines three cloud service models: Infrastructure-as-a-Service (IaaS), Platforms-as-a-Service (PaaS) and Software-as-a-Service (SaaS)
- It defines four deployment methods: Private cloud, Public cloud, Hybrid cloud, and Community cloud.
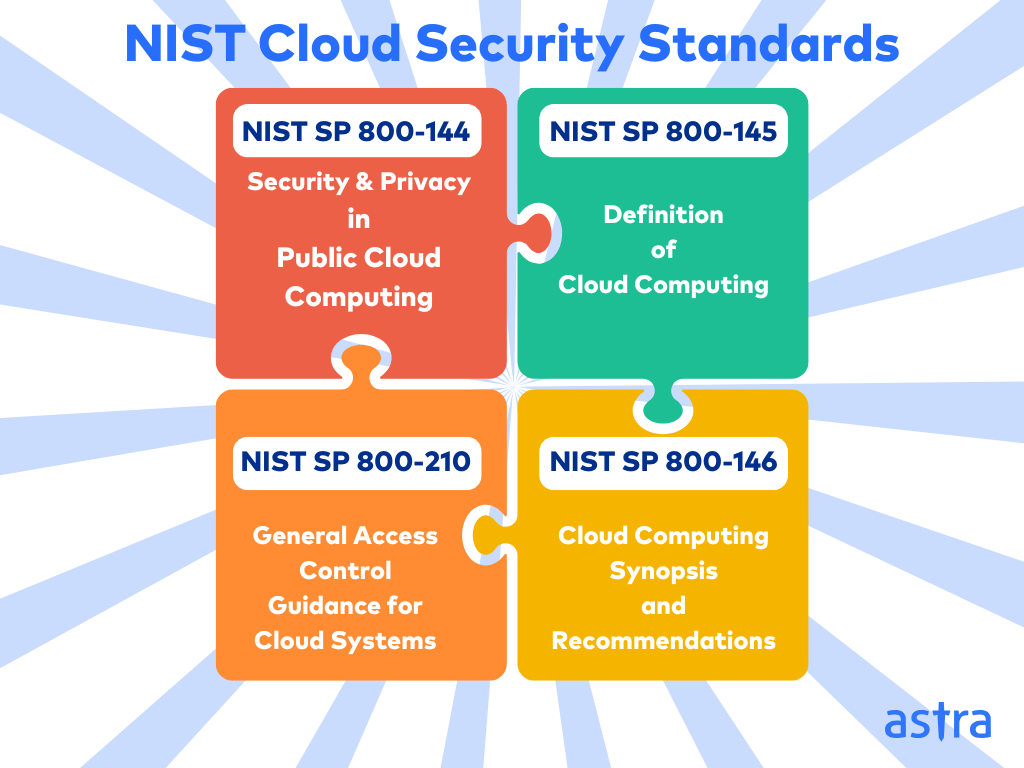
NIST SP 800 – 146
Title – Cloud Computing Synopsis and Recommendations
Purpose: This set of guidelines provides an overview of cloud computing with risks and benefits at the center.
NIST SP 800-146 explains different cloud deployments & technical characteristics like cloud performance, reliability, and security concerns. The standard mentions how and when cloud computing is ideal for an organization.
Key Highlights:
- It discusses operational and compliance challenges for an organization.
- It lays the ground for and suggests various security management practices based on cloud models.
- It discusses the need for and recommends data localization for compliance and performance of the organization’s assets.
NIST SP 800 – 210
Title – General Access Control Guidance for Cloud Systems
Purpose: This set of guidelines focuses on implementing secure access controls for cloud environments.
NIST SP 800-210 focuses on the technical features of access control without considering the cloud deployment model (hybrid, private, public). It provides access control guidance for various cloud components, such as network, data, APIs, and privilege management.
Key Highlights:
- It emphasizes the use of role-based access controls (RBAC) and attribute-based access controls (ABAC)
- It highlights a Zero-Trust Architecture setup for dynamic access
- It provides recommendations for API and session management.
Benefits of NIST Cloud Security
Key benefits of following NIST’s cloud security guidelines and standards include:
- Robust security posture in their cloud environments.
- Availability of tools and practices provided by NIST to identify and mitigate risks associated with cloud adoption.
- Aids with regulatory compliance requirements in the cloud for various compliances like SOC2, ISO 27001, PCI-DSS, and more.
- Provides best practices for increased cloud security and trust in its services.
- Emphasis on continuous monitoring for prompt detection and response to security threats.
- NIST is adaptable to various types of cloud deployment, whether public, private, community, or hybrid.
- Optimizes resource usage and cost-effectiveness in securing the cloud.
NIST Cloud Security Best Practices
Regular VAPT Activities
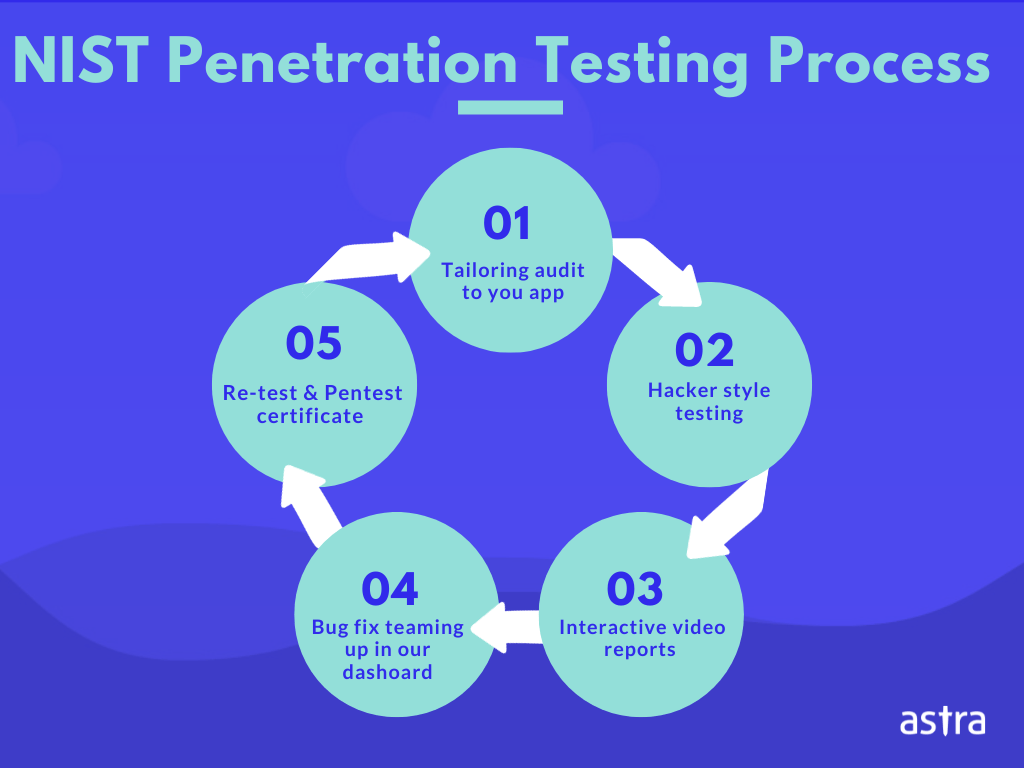
Perform regular vulnerability assessments and penetration testing on cloud environments to adopt a proactive approach to security. Along with identification and exploitation, prioritize mitigation strategies for the uncovered vulnerabilities.
Astra Security offers NIST vulnerability scanning, vulnerability assessments, and penetration tests based on NIST methodologies. It provides manual and automated testing, helping detect over 8,000 vulnerabilities across the cloud, networks, mobile apps, and websites.
Enhanced Data Encryption
Data encryption is one of the crucial practices that protects sensitive user and organizational data. Encrypting the data at rest while stored in a database is equally essential to encrypting data in transit.
Implement Access Controls
NIST recommends employing multi-factor authentication (MFA), & role-based access control to minimize potential security breaches.
Leverage Zero-Trust Architecture
To avoid exposing sensitive information to unauthorized users, always approach overall security with a zero-trust policy and implement continuous user verification and least privilege policies.
Final Thoughts
Although cloud infrastructures offer organizations many benefits, they also present security challenges. The NIST cloud security standards provide a roadmap for navigating these complexities and establishing a strong security posture. By adopting NIST guidelines and best practices, businesses can enhance compliance and ensure resilient operations in the cloud.
What is NIST SP 800 – 53 in cloud security?
NIST SP 800 – 500 is a special publication document released by NIST that provides security controls for the successful implementation of cloud security measures based on the NIST cyber security framework. Relevant controls for organizations in the cloud include risk assessments, access control & configuration management.
What are NIST’s five essential cloud computing characteristics?
The five essential NIST cloud characteristics are on-demand self-service, broad network access, resource pooling, rapid elasticity, and measured service, i.e. pay per use. It enables users to provision the cloud based on their needs through devices such as laptops and mobile devices. Services can be controlled, scaled, and dynamically allocated.
What are the core NIST functions?
NIST’s core functions include identification, protection, detection, response, and recovery. NIST provides measures on listing assets, and security measures to protect them such as encryption, access control, logging & monitoring, and vulnerability scanning for detection, remediation, and recovery from vulnerabilities.