Article Summary
Today every organization has a number of web applications that are insecure. In fact, they comprise of many vulnerabilities with little or no chance for immediate remediation. In such scenarios, virtual patching comes handy. Virtual patching protects applications from an exploit due to a vulnerability whose patch is yet to be applied.
Today every organization has a number of web applications that are insecure. In fact, th
ey contain many vulnerabilities with little or no chance for immediate remediation. In such scenarios, virtual patching comes handy. Virtual patching protects applications from an exploit due to a vulnerability whose patch is yet to be applied.
What is Virtual Patching?
Virtual patches are short-term, emergency implementations of security policies. They also enhance the existing patch management by providing remedies for lately discovered vulnerabilities on affected servers and endpoints. OWASP defines virtual patching as:
The security policy enforcement layer which prevents the exploitation of a known vulnerability.
According to OWASP’s Virtual Patching Best Practices, virtual patching does not involve modifying the actual source code. Instead, it protects an application by analyzing web application traffic. That is, it intercepts and blocks the attacks in transit, therefore shielding the application against malicious transactions.
How Can You Benefit From Virtual Patching?
Many organizations eagerly appify their businesses to speed up & automate its functions for employees and customers. In the process, they do not check the security of the apps properly. These applications come packed with vulnerabilities, regardless of the fact, if they are built in-house or purchased from a third-party vendor.
Web apps connected with the back-end systems contain valuable business data. Which makes it the main target for cyber attacks. The Verizon’s Data Breach Investigation report 2019 says,
Attacks on vulnerable web app are most likely to trigger data breach.
Therefore, patching web application vulnerabilities becomes crucial for organizations to mitigate such attacks. But fixing a vulnerability is no child’s play. It may take a lot of time and human effort. According to TrendMicro, on average a business takes over 30 days to patch standard operating systems and applications. It should be noted that complicated business applications can take months or years to install a fix. There are numerous reasons behind such behavior, including:
- The application may be critical for smooth business functioning. The organization can’t afford to risk taking the application offline.
- Migrating from legacy systems or upgrading apps may be time-consuming and costly.
- The official patch by application vendor may not be available after disclosure of a vulnerability.
- The application is complicated and expensive to fix.
- The IT team who is responsible for patching may be understaffed.
These challenges increase the company’s risk and ultimately lead to reputation damage and financial loss to the company.
How can an organization address such an issue? And protect itself during such a difficult period? Let’s find out.
Importance of Virtual Patching
Technologies like virtual patching come to rescue during such critical times. They help to mitigate the attacks against vulnerable web applications. They buy the organization enough time to test and install a stable & reliable patch for the existing vulnerability. A virtual patch has other benefits as well.
Here is the list of benefits of using virtual patches over traditional patching methods:
- Scalable Solution: Virtual patch is convenient to implement since it needs to be installed on fewer locations rather than on every host.
- Reduces Risk: It helps in reducing the risk until a vendor-supplied patch is released, tested and applied.
- Downtime Prevention: It protects the critical systems that require high availability and can’t be taken offline.
- Cost Reduction: It cuts down or eliminates the time and money spent on immediately patching the vulnerability.
- It helps in maintaining the organization’s regular patch cycles.
These benefits make Virtual Patching an attractive tool. It provides an additional security layer against threats.
Virtual Patching Tools
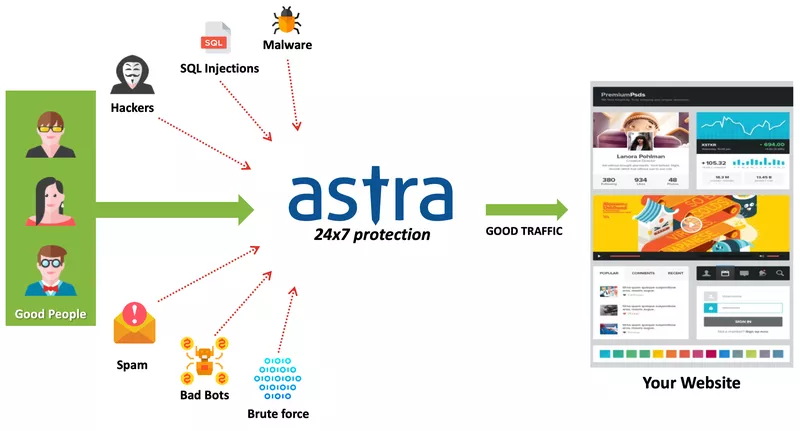
Virtual patching can be done by using several different tools. For instance, intermediary devices such as web application firewall (WAF), intrusion prevention system (IPS), web server plugin such as ModSecurity, and application layer filter such as ESAPI WAF.
While choosing the tool, one must take into consideration the following features:
- The tool must use HTML and HTTP parser, which can understand specific protocol features such as content-type, XML payload, and more.
- The tool must be able to break up the HTTP stream into headers, parameters and uploaded files, and should be able to inspect each element separately for its content, length and count.
- For a keep-alive HTTP connection, it should be able to match correctly request and replies.
- The tool must have anti-evasion capabilities, including techniques like character encoding and data sanitization.
- The tool should not wholly rely on signatures. It must provide the feature to implement robust rules with complex logic to define the tests.
By far, a web application firewall is the most viable tool for Virtual Patching. Moreover, a hacker tested firewall such as the Astra Firewall works wonders in securing your website. The Astra Firewall also satisfies all the above conditions and can be used to implement virtual patches in no time. It provides an end-to-end, easy to deploy, and highly scalable solution to protect against web application vulnerabilities and coming attacks.
Summing Up
In today’s ever-changing environment, keeping up pace with the security flaws in complex web apps & software can be taxing. Virtual patching proves to be a life-saver in these cases. It patches web app vulnerabilities and reduces risk.
Virtual patches have several benefits over traditional patching cycles, which can take a lot of time, effort, and money. Virtual patches can be put in places within minutes or hours with minimal cost. Moreover, they should be included in the security toolkit along with other security tools like firewalls, IPS, etc for better defense against evolving threat and attack techniques.
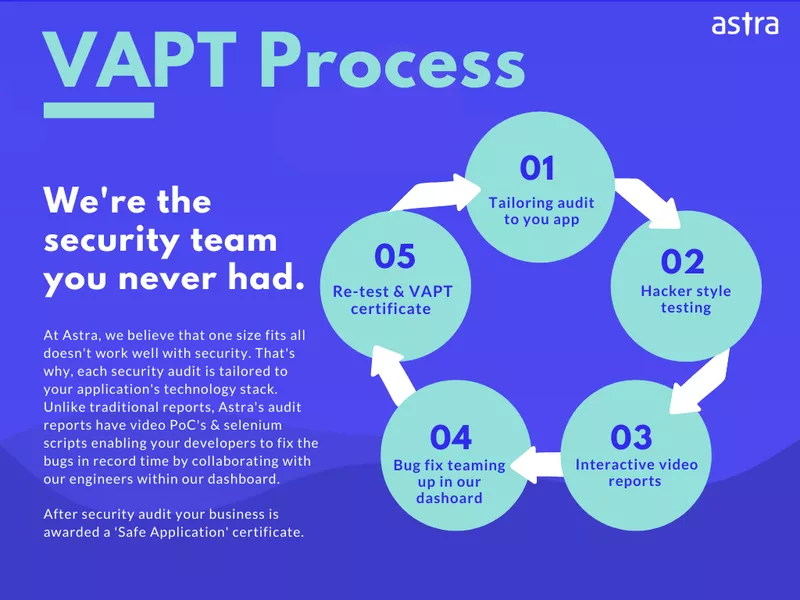
You must, however, remember that the virtual patch is just an emergency setup and not the actual solution. Deploying a virtual patch buys you time to fish for the long-term solution such as – finding & mending the vulnerability. A full website Security Audit is what you need at this time. Astra’s Website Security Audit (aka VAPT) offering has helped small & big businesses detect hidden exploitable vulnerabilities. Learn more about it here.
Found this post useful? Subscribe to our blog and get notified every time we post fresh content 🙂