We often tend to think of the internet as a boundless space with unlimited capacity for any possible situation – but this isn’t true. Even your server has a certain limit before it cracks under the pressure of receiving multiple users and many visits at the same time. Definition wise, this is what a distributed denial of service (DDoS) situation looks like.
DDoS attacks are more common than you might think, so setting immediate WordPress DDoS protection is an ideal solution. For example, looking at 2019’s statistics, DDoS attacks have increased by 39% as compared to the situation in 2018.
It’s not just the quantity but the quality of attacks that have increased in seriousness – network attacks of over 500 gigabytes per second (Gbps) and low-and-slow application flooding are not so rare anymore.
The impact of these attacks is not weak either – the application or network unavailability or you can also expect a severe drop in legitimate website traffic, lose sales and revenue, high costs to deal with the compromised situation, and permanently suffer a hit to your website reputation.
What are the different types of DDoS attacks that one can expect?
There are two kinds of DDoS attacks one can expect under different layers of the Open Systems Interconnection (OSI) model – this model uses seven different layers within a communication system which is used by computers in the network for sending information back and forth.
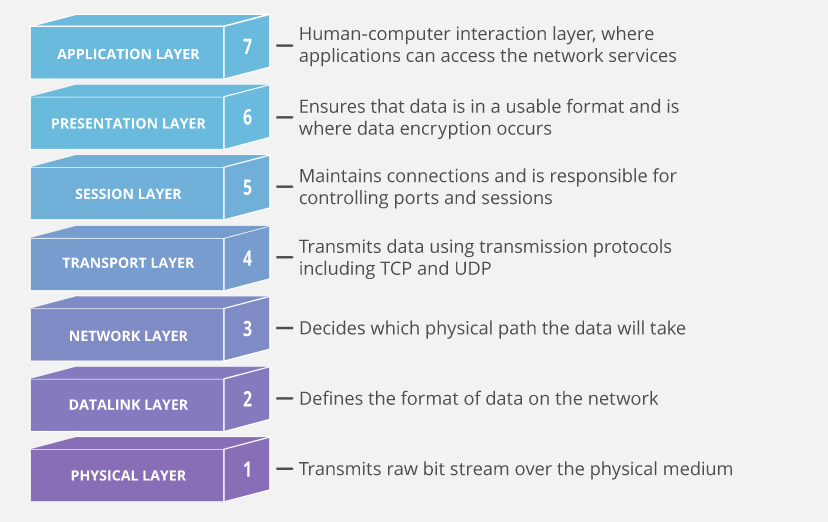
Layers 3 and 4 – The Network and Transport Level DDoS attack
As the name suggests, Layer 3 and 4 attacks target the network and transport level, which usually occur by overwhelming the target and brutally consuming the server resources till it’s unable to cater to actual traffic and malfunctions.
Usually, layers 3 and 4 are targeted in the form of DDoS attacks since it’s the most efficient way of disrupting a website’s traffic quickly and taking it down.
The good part is that these kinds of attacks are easier to resolve between the two mentioned here and contain no risk of permanent damage to the site.
Layer 7 – Application Level DDoS attack
Here, the DDoS attacks aim at the application layer of the OSI model, making them more complicated to deal with than layer 3 or 4 attacks. Here, their main target is the user interface of the website or the application, making it more human-based than a bot attack, like flooding the network or the transport layers.
One example of the execution of this kind of attack involves targeting specific elements on the server like form input submissions or downloading a resource.
This makes this form of DDoS attack a dangerous one for WordPress websites and in absolute need of WordPress DDoS protection software.
Steps for implementing WordPress DDoS protection
There are few measures you can take on your side to both prevent and detect DDoS attacks at an early stage, thus preventing the eventual website crash that compromises your users and legitimate website traffic.
1. Install the firewall
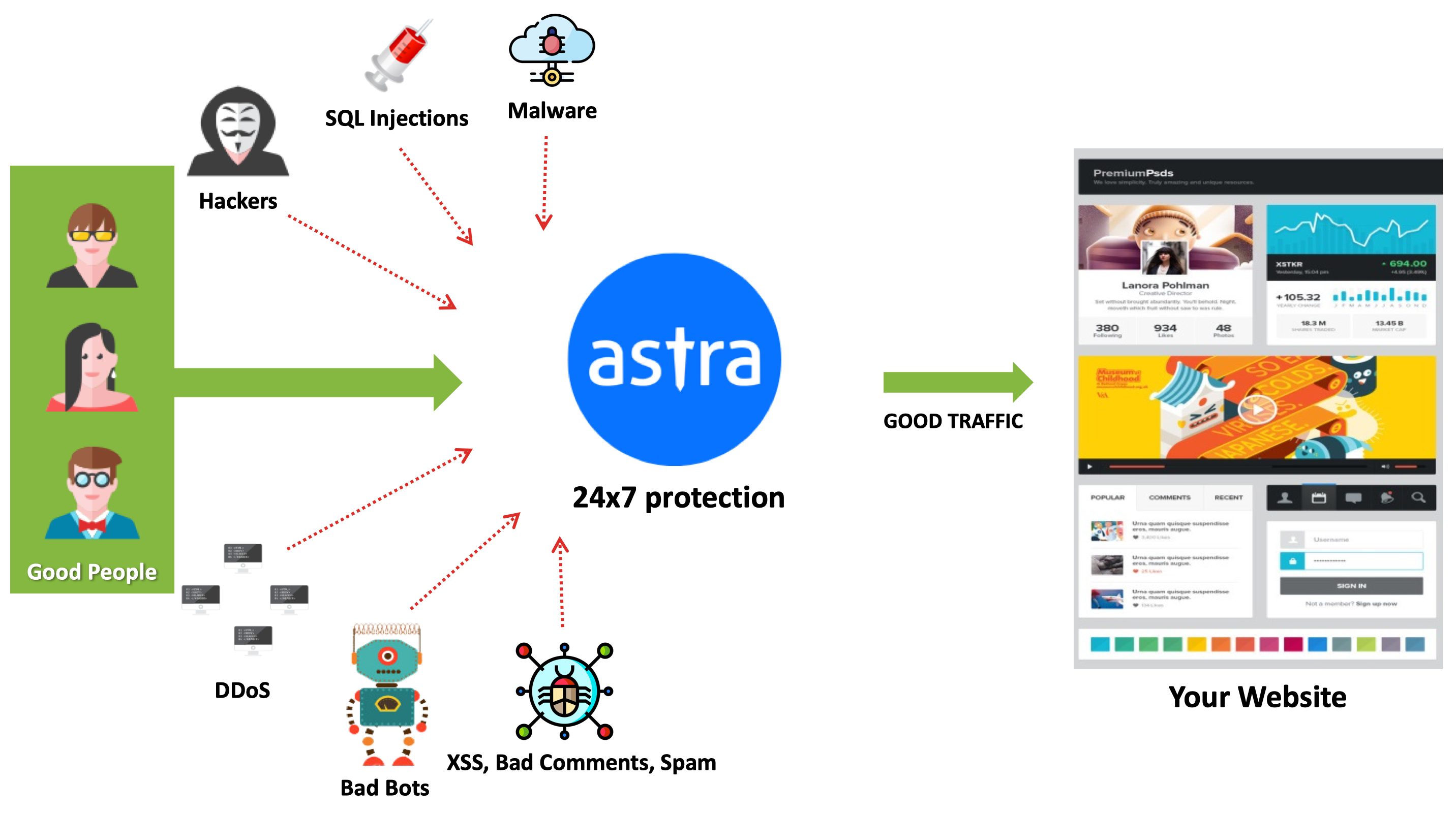
The intent of the web application firewall (WAF) plugin handles the responsibility of analyzing the requests that come to the WordPress site and categorize it as malicious or otherwise. If problematic, the plugin will block the flooding attempt, thus foiling the hacking attempt.
DDoS attacks can be very specific and require certain firewall plugins that are equipped to handle them specifically. There are two types of traffic requests, one that uses your WordPress installation and another that doesn’t require a WordPress site, but just your server. To block the second kind, you need plugins with specific technologies to work against DDoS attacks.
2. Use CDN
Content Delivery Networks (CDNs) offer cache copies of your site from the data centers, acting as a middleman between you and the site’s visitors. This allows CDN providers to act as a barrier to DDoS attacks by preventing any overwhelming amounts of website traffic from crashing the site.
Plus, they also help you to decrease the loading times of your site and detect uncommon website traffic activity which may signal DDoS attacks.
3. Supervising the traffic of your site
While DDoS attacks come with no warning label attached, but constant supervision of the website traffic log (in real-time) can prove quite useful.
Details such as time of access, location, or the page or file that was requested can be quite useful.
The traffic log should capture both kinds of requests that we covered above, and with this, you can have a better chance of detecting the issue rather than writing it off as a faulty plugin or site issues.
4. Monitor the site’s data usage
DDoS attacks intend for the website to be overwhelmed with all resources extensively exploited – this characteristic allows you to track the usage of the website’s resources and statistics of the WordPress site.
This option is usually available under the dashboard > ‘manage hosting’ which gives the usage statistics. Check that they are within mid-range limits (unless you run a large website on a low-end hosting plan) and move accordingly.
5. Utilize geo-blocking features
A majority of DDoS attacks tend to originate from one country, which works out in your favor as you can block IP addresses that specifically come from there. This is only a temporary solution (hackers can use proxy servers based in different countries and you can’t block everyone), but it’ll lessen the intensity of the attacks until you work out a more permanent answer.
Anti-DDoS plugins offered by WordPress
WordPress also offers certain security plugins that fix the vulnerabilities along with the offering of WordPress DDoS protection.
1. Protection against DDoS
This plugin helps in addressing the performance issues that arise out of brute attacks and DDoS attacks. It’s done through checking the ‘.htaccess’ file which can stop all malicious requests at the entry-level of the web server before actually reaching the WordPress site.
You can also use this plugin to fix the XML-RPC vulnerability with the configuration options providing the extra category of blocking users from specific countries.
2. Disable XML-RPC Pingback
This plugin targets all the exploitable methods of the XML-RPC interface, which explains its multiple installations and 4+ rating; the plugin also removes the X-Pingback from the HTTP headers which is a prime target for bots from the xmlrpc.php file.
3. Disable WP REST API
WordPress REST API is another vulnerability that your WordPress site needs protection from, the solution of which is this plugin. Very little code is used in an efficient process for protecting your users by disabling the WordPress REST API for those not logged into the WordPress platform.
After installation and activation of the plugin, if any logged-out visitors make JSON/Rest requests to your site, they get a notification stating that the REST API is only allowed for authenticated users.
Alternatively, you can also install our multi-purpose WP-hardening plugin and do all the above-mentioned tweaks and more with just a toggle of a button, within the same interface. It saves you the effort and time of installing and maintaining many different plugins. At the same time, it also reduces the risk of introducing more vulnerability points, which often comes as a part and parcel of installing a third-party plugin.
Your best solution at this point is to hire the services of professionals or all-comprehensive security suites that cover multiple security concerns including DDoS attacks with a website firewall, antivirus software, constant scanning, and monitoring provisions – check out Astra Security’s WordPress DDoS Protection today!
















