Recently, we published an update on a severe Magento vulnerability which was released by the DefenceCode team. Soon after Bosko Stankovic (the Defensecode researcher who discovered this Magento vulnerability) released a follow-up article. Bosko confirms that Magento would be patching these in the upcoming updates.
Through this article, Astra aims to explain the severity of these vulnerabilities, and how one needs to prepare themselves for mitigating against the associated attacks and save their important business infrastructure.
The Solution
A solution proposed to combat these vulnerabilities was a Secret Key via which we were able to mitigate against the CSRF attack vector. However, further investigation reveals how this solution is still incompetent when it comes to more sophisticated attacks. Primarily because the derivation of secret keys is a weak mechanism.
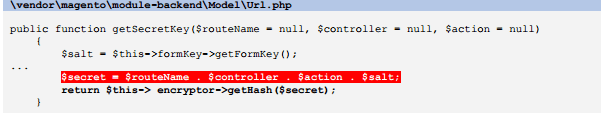
Secret key is a concatenation of three different parameters: controller, action and salt. Salt is a 16 bit randomly generated key which is equal to the form key and can easily be obtained by just a simple HTTP request in light of a XSS vulnerability. Thus, resulting in complete compromise of the account.
Mr Stankovic authored a technical report in which he shed some light on how well the vulnerability can be exploited to hijack the admin sessions successfully resulting in a full compromise. It is advised to read about the technical section of the vulnerability here.
Planning an attack on an application based on this vulnerability requires very detailed analysis and complete knowledge about admin URLs and existence of XSS vulnerabilities, but these are no big hurdles to cross. In case of targeted attacks, finding such information is not a very difficult task for the attacker.
Mr Stankovic reveals the solution to this Magento Vulnerability. “Direct requests to all URL paths without a secret key inside the Magento administrative panel should result in an error or log out the user instead of redirecting to the administrative dashboard. There should be no paths that can be requested without a secret key”, he believes.















