Safe to host certificate is an X.509 certificate that can be used to securely recognize servers and to establish encrypted communications between clients and services. To acquire a safe to host certificate, you must submit a formal request to the Certificate Authority (CA). It is worth mentioning here that a safe hosting certificate is of paramount importance to hosting companies.
These certificates build trust in your customers and establish you as a credible hosting company — providing a secure connection with added layers of encryption.
Trust and credibility should be good enough reasons to get the safe to host certificates. But, we have more. Find out below. Also, find information on where to get a safe to host certificates from and how much it costs.
Why do hosting companies need to prove their security?
Data breaches among hosting companies are becoming more and more common. It is important to note here that when a data breach occurs in a hosting provider’s set up, thousands of customers can be affected. Let’s take the instance of the recent data breach on the popular web host — GoDaddy. GoDaddy has a phenomenal customer base of 19 million people from across the world. However, recently, GoDaddy reported a data breach in its hosting setup that compromised more than 28,000 hosting accounts.
Later in a public appearance, the Vice President of GoDaddy said that the breach was not that severe and a timely intervention stopped the threat from accessing customer’s credentials.
As per security analysts, the attack may have emanated due to the re-use of stolen credentials by GoDaddy. There are recent reports that GoDaddy’s support employees being the victims of phishing attacks.
Sadly, this is the case with most hosting providers.
How ‘Safe to host certificate’ instills security & credibility?
1. Acts as a trust seal
There is no doubt that a Safe to host certificate signifies the credibility of the hosting provider. In other words, it acts as a seal of trust on which the customers rely when hosting their websites/business with a hosting provider.
Further, these certificates are usually granted after a deep security audit on the web application, which means the hosting provider has been deemed secure and without vulnerabilities. This, again, instills confidence among the prospects.
2. Surety of patched vulnerabilities
Well, hosting servers are the foothold of a website. So it becomes a nightmare for the administrator if the server gets infected.
To be frank, open vulnerable ports have been one of the major concerns for a plethora of web servers getting affected.
Moreover, outdated server software can also be the main reason behind the frequent occurrence of data breaches. When server software is not properly updated, it makes them prone to hackers.
These vulnerabilities and security gaps can be checked with a deep security audit, which is a pre-requisite to get this certificate.
In case of shared hosting arrangements, it is all the more necessary to plug all security gaps. Websites on shared hosts are always a hot target because one malicious website on the hosting server eventually compromises more websites, giving hackers more data, resources and campaign perpetrators.
A safe to host certificate for shared hosting plans would go a long way as this section of web hosting is at the receiving end of more brutal cyber attacks.
So far we learned that the ideal way to get a ‘Safe to host’ certificate is by opting for a thorough security audit. But where to get one? The following section answers.
Safe to host certificate by Astra
Astra offers one of the most reliable security audits and safe to host certificates to businesses and hosting companies. VAPT by Astra includes – static and dynamic code analysis, network configuration test, business logic error testing, payment security testing, and 1250 other tests.
The VAPT plan by Astra also comes with a collaborative security audit dashboard, where Astra security experts and developers of a company can communicate directly. Besides providing a detailed PDF report, Astra also provides a POC detailing the vulnerabilities in the system.
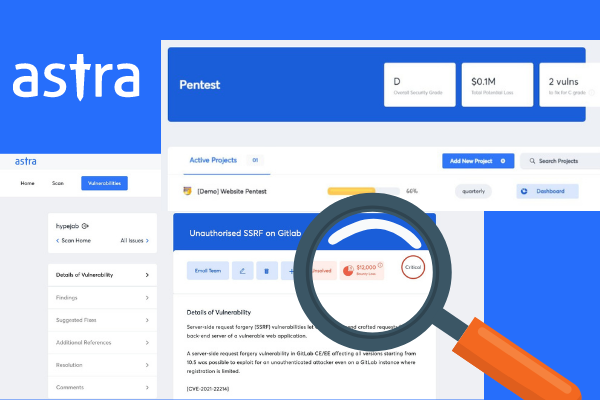
What’s more? Astra experts don’t just mention the recommendation steps, instead, they assist your developers with fixes and do a re-scan to ensure that all reported vulnerabilities are patched.
This is how the visual representation of VAPT process by Astra looks like:
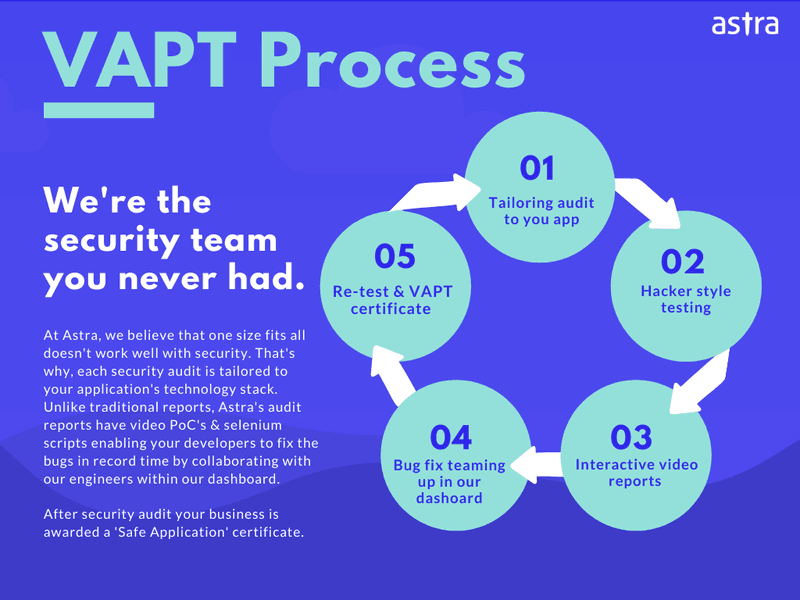
The VAPT services provided by Astra encompass all major security compliances like OWASP, PCI-DSS, etc which makes it a trusted name in the industry. This organization is empanelled by CERT-In for providing information security auditing services.
Astra’s comprehensive VAPT services – Pricing & Features
VAPT services offered by Astra come in three different plans – Basic, Expert, and Elite. Then there are Advanced and Business plans which offer yearly and monthly security audits respectively.
These plans differ in frequency, the number of tests done, security consultation, type of support, etc.
As a leading VAPT service provider, all these plans help your web applications and servers to address the latest security vulnerabilities.
From analyzing vulnerabilities to assisting in patching them, Astra security experts ensure that your servers are impermeable to malware attacks.
















