The importance of privacy was recognized from archaic times when in 300 B.C. when Aristotle differentiated the public and private sphere of one’s life. Fast forward to the current era of connected devices and internetworked technologies, making it difficult to keep the private information actually private. Most of the times we end up sharing crucial information on the internet, which rarely tends to restrict to one site only. Consequently, carelessness on the user end in information mishandling or a data breach led cyber attack results in information leakage, and thus privacy loss. The information stolen can be misused by hackers or people with malicious intent in a variety of ways.
Malicious use of personal information
An attacker is restricted by their imagination in using the personal information of a person to attack them. If they get hands on highly confidential information (Social Security Number, Aadhar Number, DOB, Mobile Numbers) many devastating situations may arise. A few of them are described below.
- Password Guessing: An attacker is capable of guessing the passwords of your application. For Example- If one uses digits of the mobile number in the password while performing a guessing attack, the attack tool would be able to use the digits from the mobile number and would skip on a large number of permutations.
- Identity Theft: This is one of the most dangerous consequences of a security breach. Anyone with sufficient amount of personal information can easily impersonate another person over the internet. This causes many problems such as:
- Credit Card Thefts: Hackers have been known to get a credit card issued in another person’s name, use it and embezzle money.
- Buying goods over the internet with someone else’s ID.
- Such information is sold in the black market.
- Financial Losses: If an attacker gets hold of credit card or debit card information, they are able to use the card for illegitimate purchases. Although all companies employ customer protection and refunds any fraudulent payments,
This explains why even the smallest businesses need to protect the user information. If there is a data breach in any organization, customers start to lose faith in it, which directly affects the business of the organization. Many safeguarding techniques can be employed by businesses to secure their applications such as Web Application Firewall, Regular Security Audits, and malware analysis.
Classification of data
Data is classified into three categories: Regulated, Confidential and Public.
| Data | Sensitivity | Example |
|---|---|---|
| Regulated Data | Highest | Social Security Number, Credit Card number, bank accounts, driver’s license,
bank accounts, driver’s license other information of such sort |
| Confidential Data | High | Research details, information covered by NDAs, contracts facilities, management information. |
| Public Data | Low | Public Directory information, maps and other information put for public use. |
People and Organizations need to understand the class of data they are dealing with. Exemplifying e-commerce businesses, consumers share their highly confidential data (Credit Card Number, CVV, house address) while ordering from reputed organizations only. To build a good reputation, it is essential to exhibit a trust factor amongst consumers, by assuring them that their credentials are safe on the organization server. To promote this ethic, we at Astra ensure the protection of applications from imminent cyber attacks by providing regular malware cleanups and business logic checks.
Protecting Personal Information
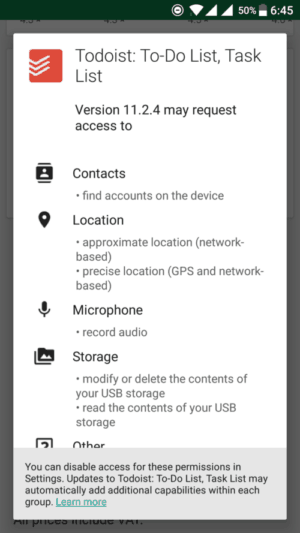
Since both customers and business owners need to secure private data, it is essential for consumers to filter the data they can trust a vendor with. Focusing on these aspects can ensure a high level of data security and build trust amongst each other.

- Web Application Firewall
Astra offers an intelligent state of the art firewall that protects your website in real-time. Apart from giving rock-solid security, it follows optimized security practices to defend against all forms of cyber-crimes.
To understand the working of the firewall, one is advised to visit here. - Regular Security Audits
Regular security audits ensure that the application is following best security policies out there in the market. Often new updates are required in an application in order to combat potential vulnerabilities. Missing out on security checks in such updates ultimately leads to undiagnosed vulnerability and susceptibility to attacks. It does not matter how small or big an application is, attackers, attack them all. - Malware Cleanups
One of the most devastating situations for any application is malware injection. This causes attackers to take control of your application and misuse it for their benefits which include sending financial transactions to dummy servers. We at Astra provides facilities for malware cleanups. - Business Logic Scans
Business logic defines the modulation of data i.e. how it is created, stored and extracted. Many applications are vulnerable to such attacks where an attacker can extract all the information required by simply extrapolating the functionalities provided by the application. To understand more about Business logic errors, users are advised to go here.















